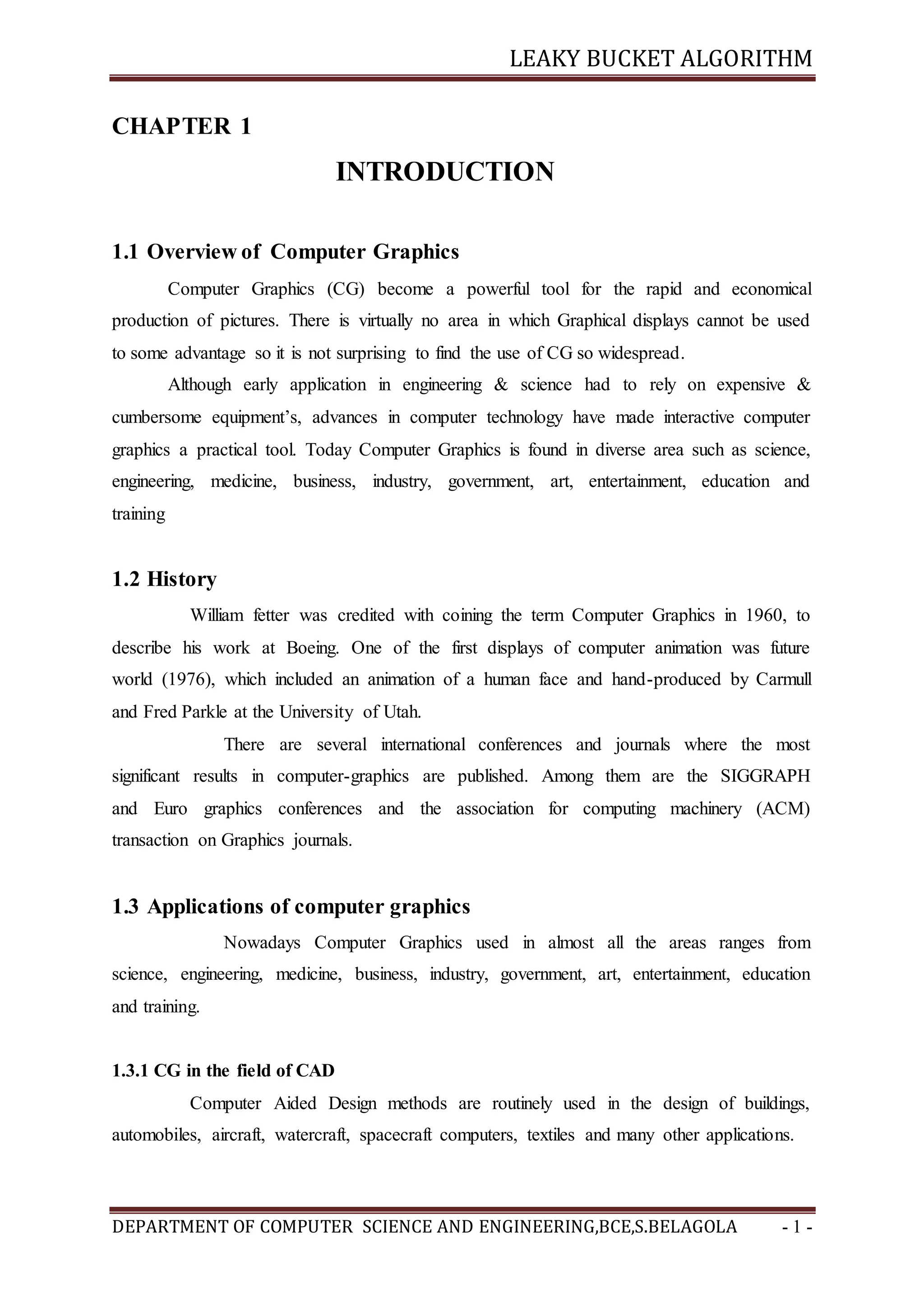
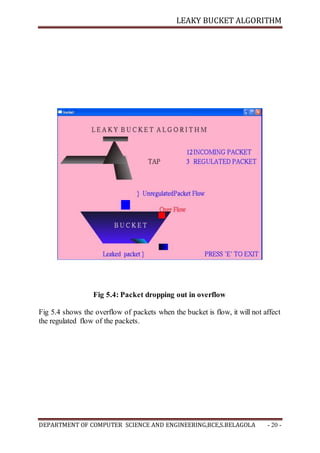
The document provides an overview of computer graphics, its history, and applications across various fields such as engineering, medicine, and entertainment. It introduces the leaky bucket algorithm for traffic shaping, explaining its function to convert turbulent incoming data into a smooth stream while adhering to specified constraints. The project aims to graphically illustrate the leaky bucket algorithm using OpenGL, detailing the objectives and structure of the report.











![LEAKY BUCKET ALGORITHM
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING,BCE,S.BELAGOLA - 14 -
4.2 IMPLEMENTATION
glutInit
Syntax: glutInit( int *argc, char ** argv);
Purpose: Initializes GLUT. The arguments from main are passed
In and can be used by the application.
glVertex
Syntax: a)glVertex[234][sifd]( TYPE xcoordinate, TYPE ycoordinate, …);
b) glVertex[234][sifd]v(TYPE *coordinate);
Purpose: Specifies the position of a vertex in 2,3,or 4 dimensions. The coordinates can
be specified as short s, int i, float f or double d. If the v is present, the argument is a
pointer to an array containing the coordinates.
glutCreateWindow
Syntax: glutCreateWindow(char * title);
Purpose: It creates a window on the display. The string title can be used to label the
window.
glutInitDisplayMode
Syntax: glutInitDisplayMode( unsigned int mode);
Purpose: It requests a display with the properties in mode. The value of mode is
determined by the logical OR of options including the color model(GLUT_RGB) and for
buffering(GLUT_SINGLE, GLUT_DOUBLE).
glutMainLoop
Syntax: glutMainLoop();
Purpose: It causes the program to enter an event processing loop. It should be the last
statement in main.
glutKeyboardFunc
Syntax: glutKeyboardFunc(void *f(char key, int width, int height)
Purpose: Registers the keyboard callback function f. The callback function returns the
ASCII code of the key pressed and the position of the mouse.](https://image.slidesharecdn.com/6-170424065632/85/Mini-Project-final-report-on-LEAKY-BUCKET-ALGORITHM-14-320.jpg)




![LEAKY BUCKET ALGORITHM
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING,BCE,S.BELAGOLA - 22 -
REFERENCES
[1]. Communication Networks – Fundamental Concepts & key architectures, Alberto Leon
Garcia & Indra Widjaja, 2nd Edition, Tata McGraw-Hill, India.
[2]. William Stallings: Data and Computer Communication, 8th Edition, Pearson Education,
2007.
[3]. Leaky Bucket Algorithm, www.slideshare.net
[4]. Edward Angel: Interactive Computer Graphics A Top-Down Approach with OpenGL, 5th
edition, Pearson Education, 2008.](https://image.slidesharecdn.com/6-170424065632/85/Mini-Project-final-report-on-LEAKY-BUCKET-ALGORITHM-22-320.jpg)