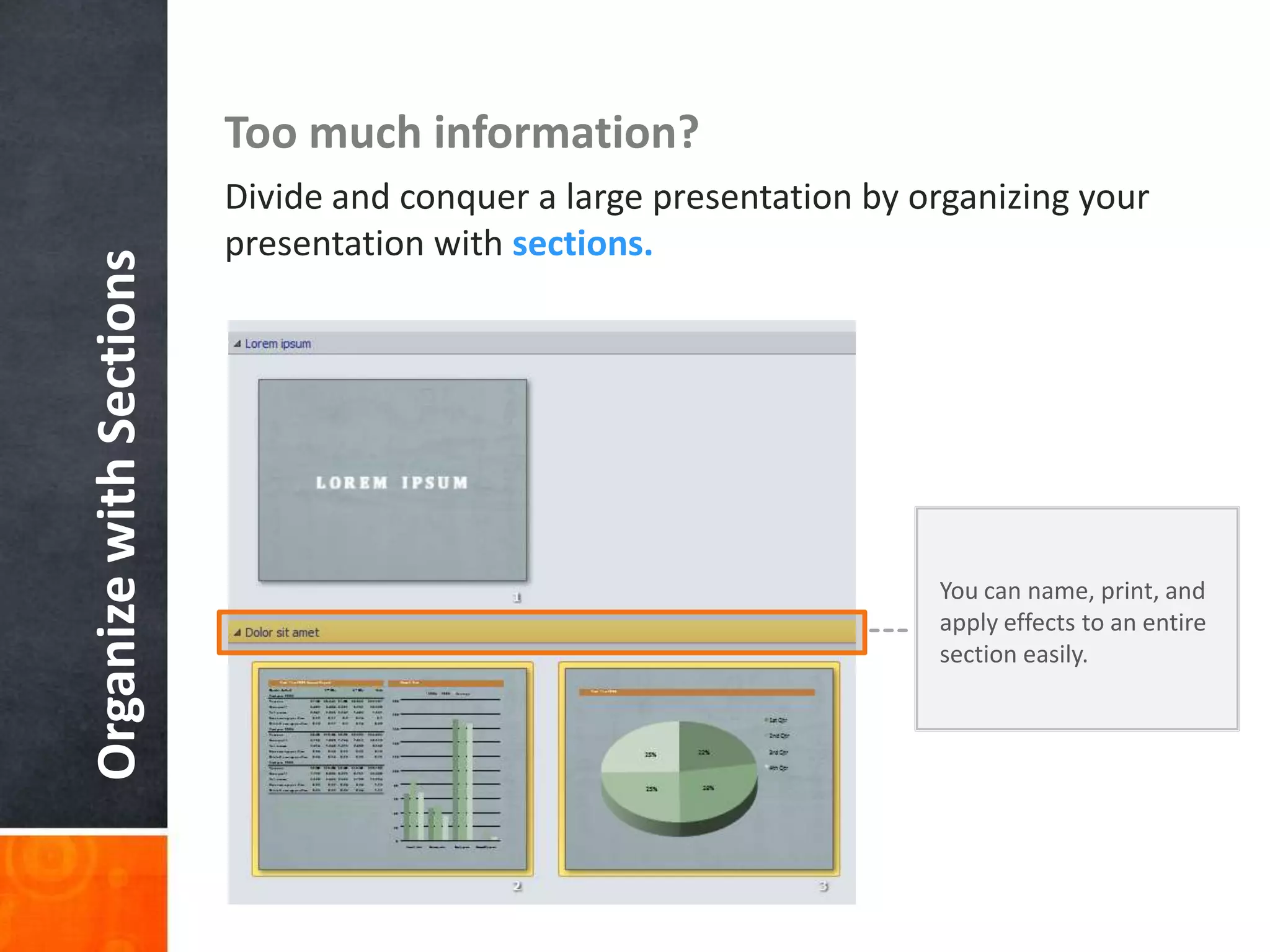
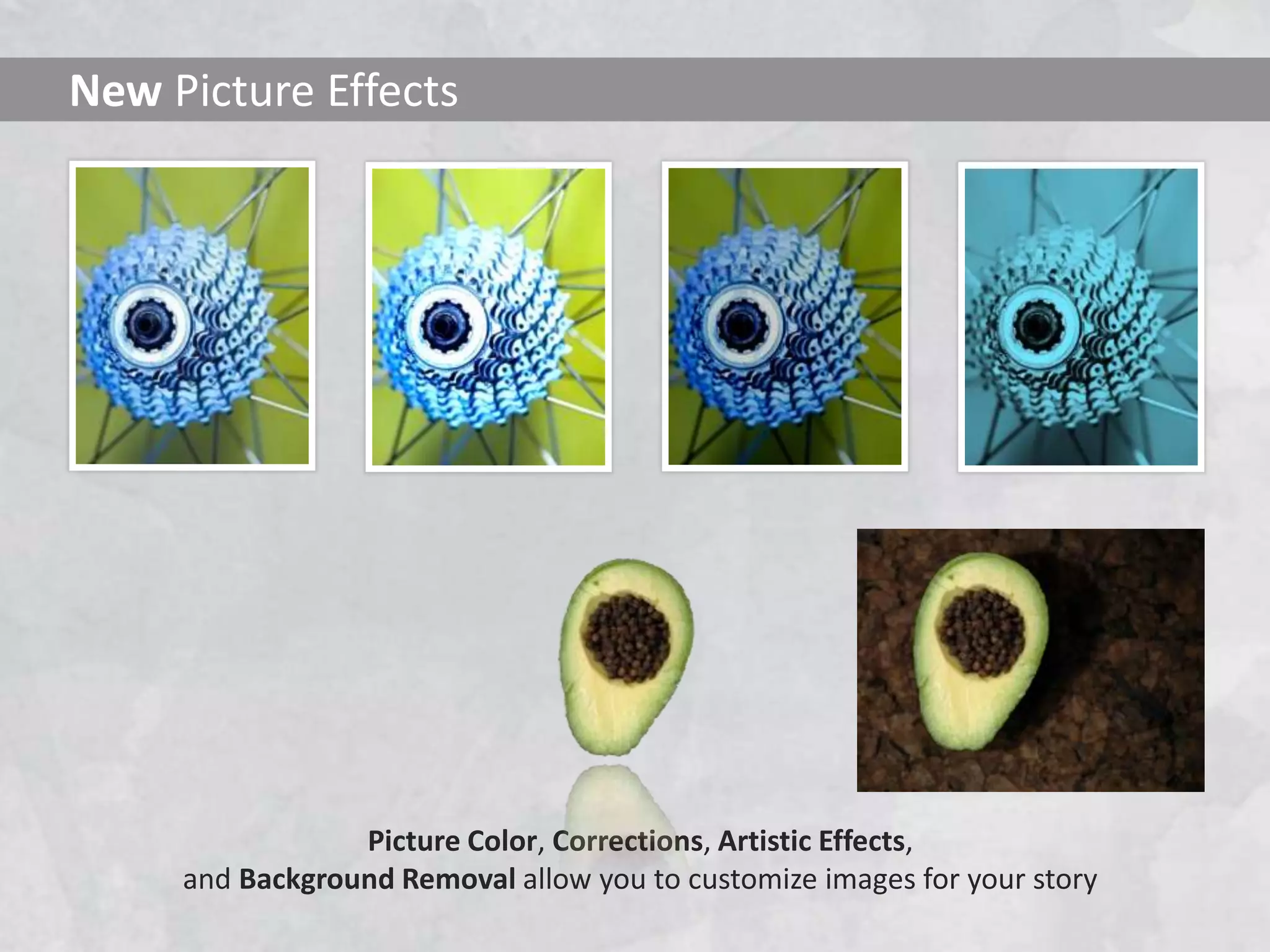
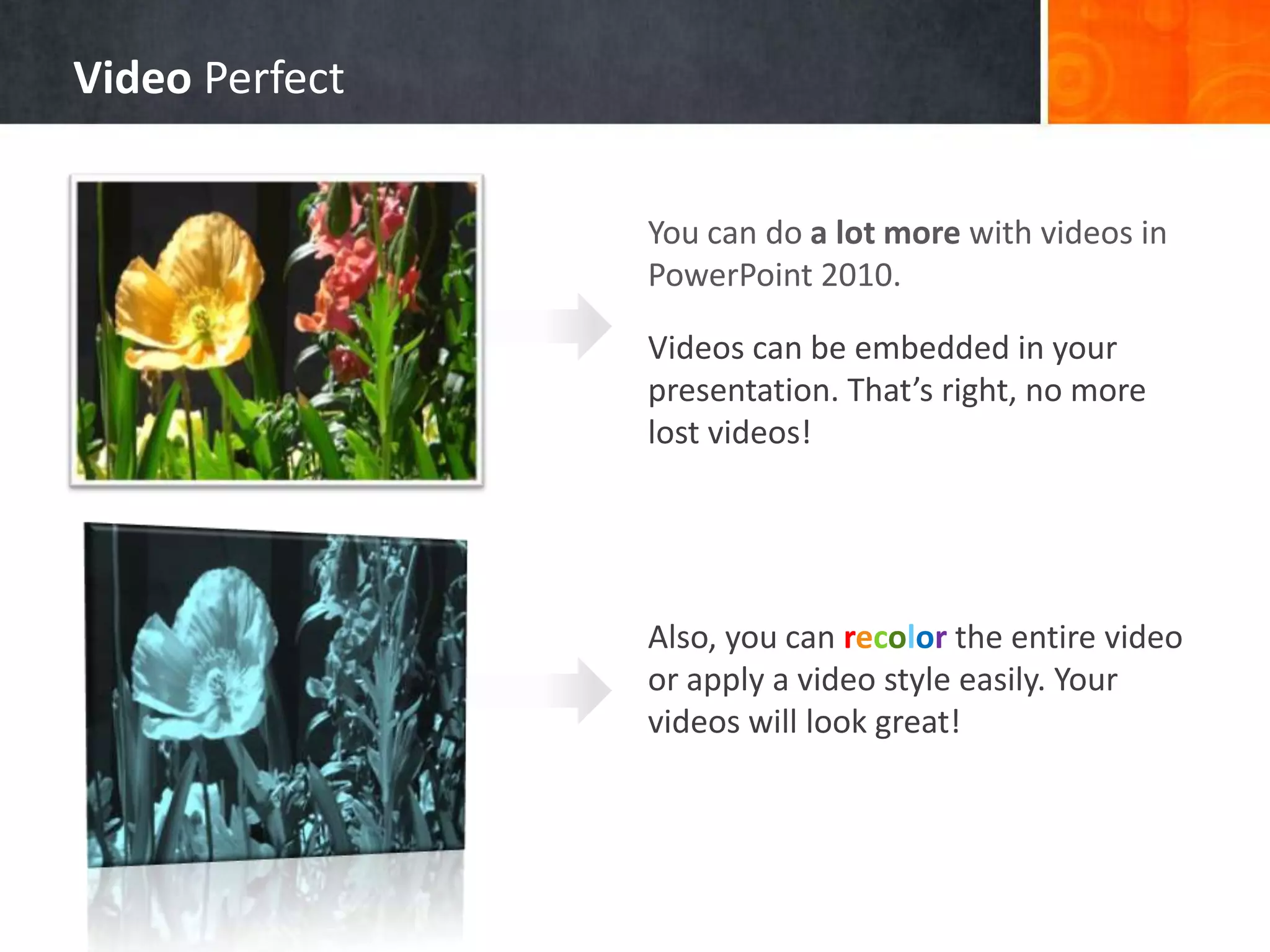
PowerPoint 2010 introduces new features to help users at every stage of creating and delivering a presentation. It provides templates to help users start presentations, allows simultaneous collaboration on a single document, includes new options for styling and animating pictures and videos, and enables users to broadcast or record presentations and share them online through tools for optimizing file size and embedding media.