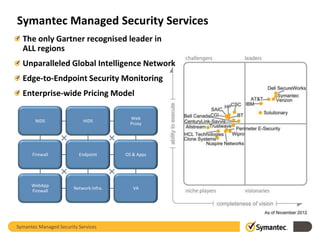
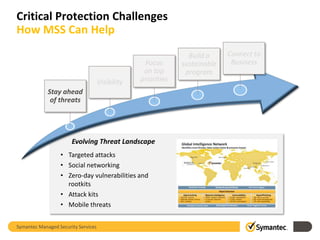
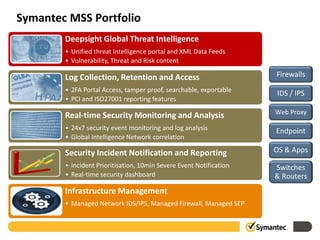
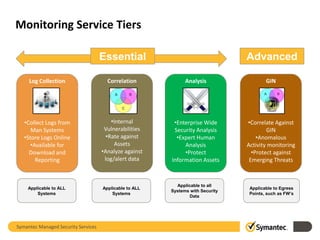
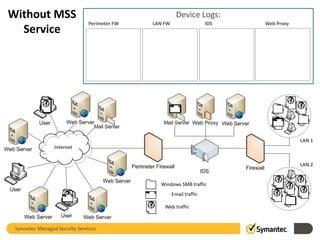
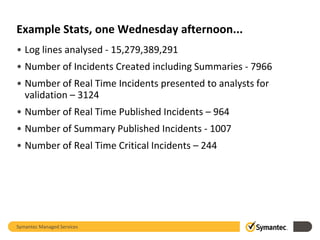
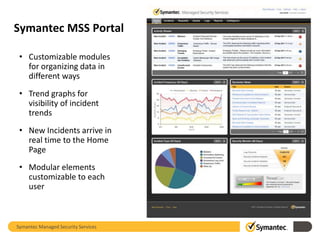
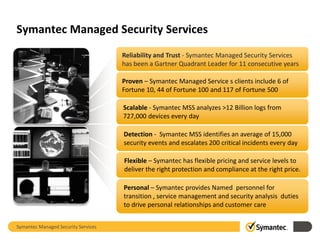
Symantec's Managed Security Services (MSS) provide organizations with global threat visibility and 24/7 access to security specialists to combat evolving cyber threats. The service encompasses security monitoring, infrastructure management, and threat intelligence, analyzing over 12 billion logs daily and identifying thousands of security events. Symantec is recognized for its scalable solutions and has maintained Gartner's leader status in the MSS market for 11 consecutive years.