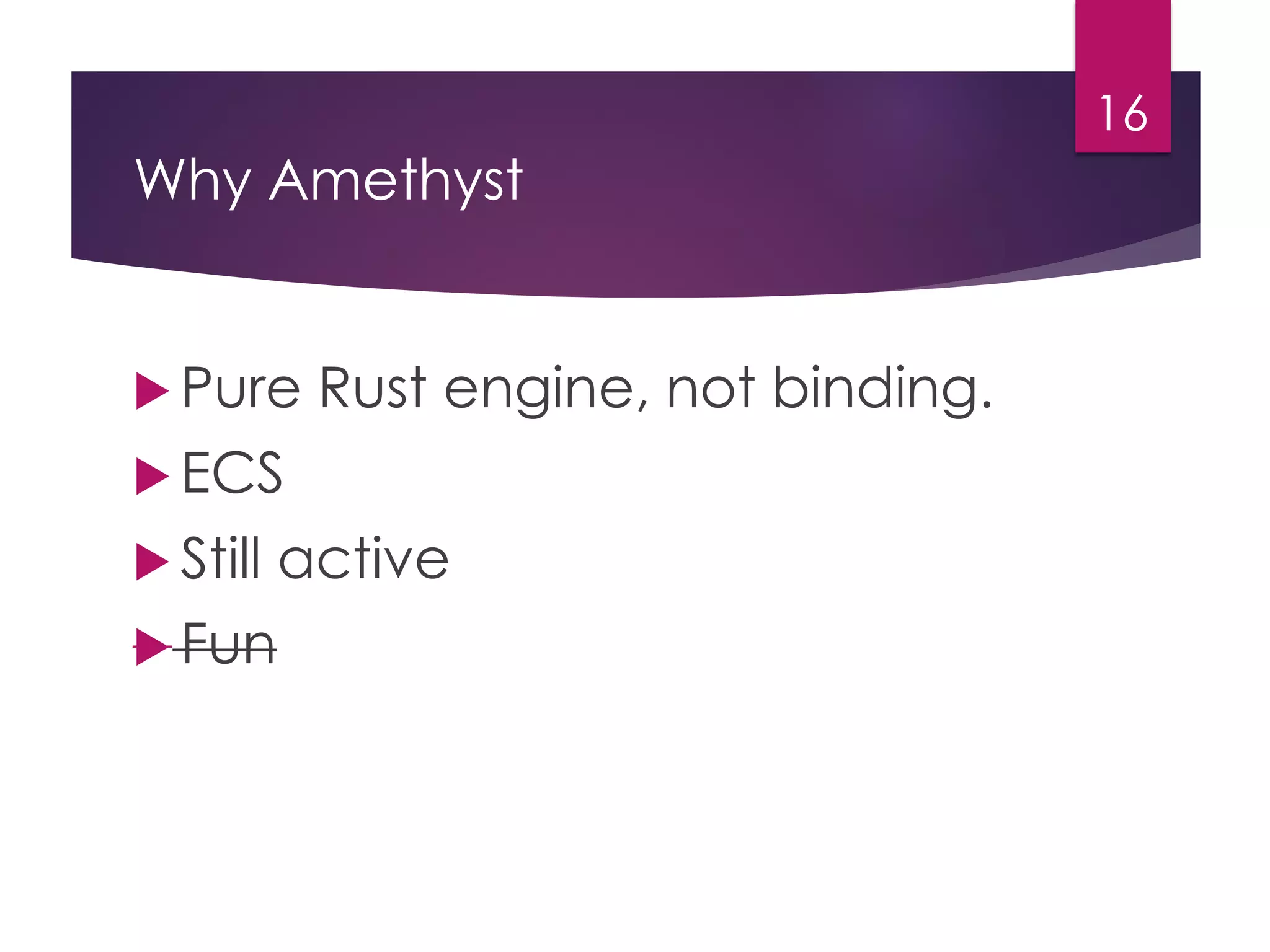
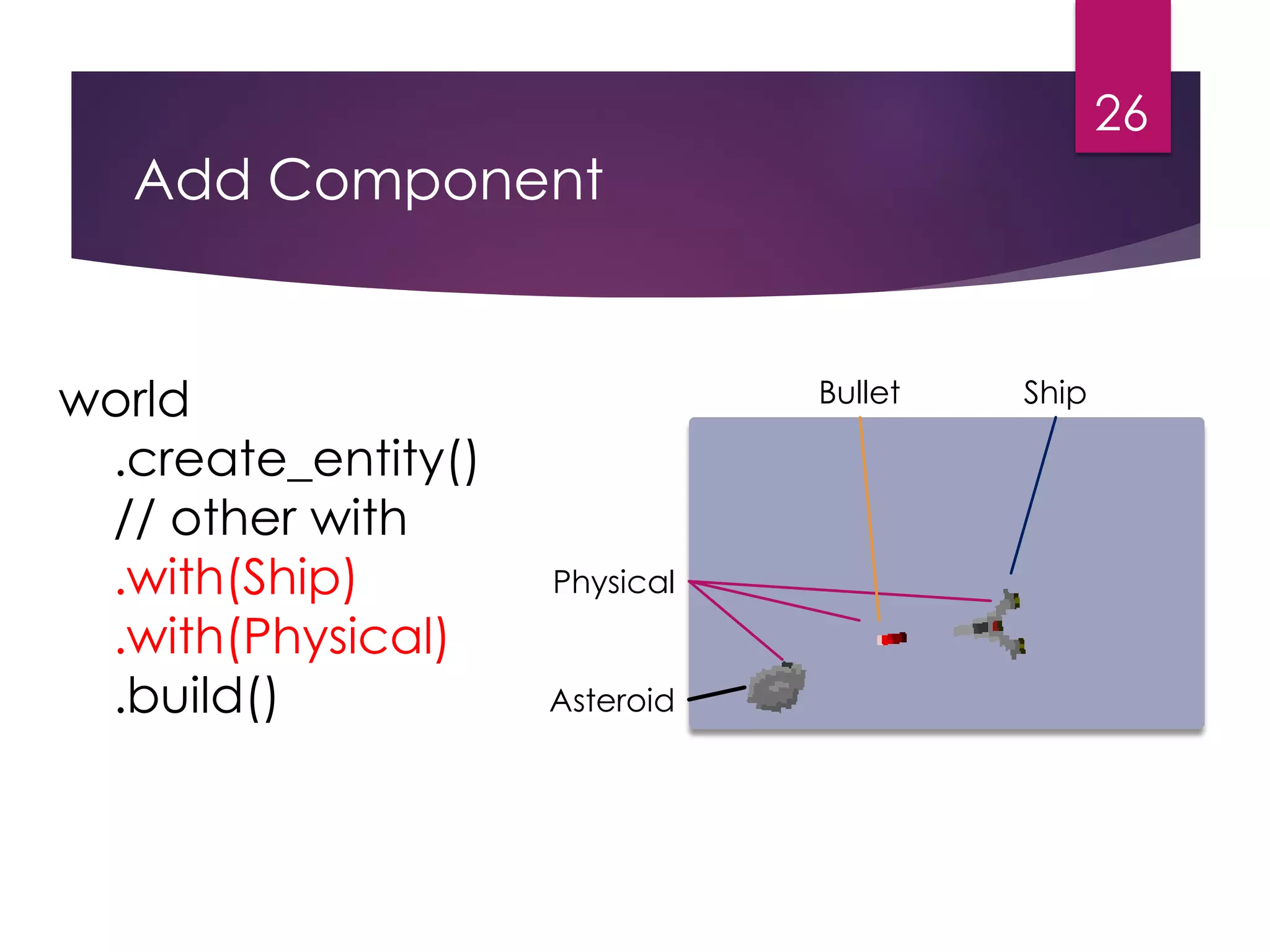
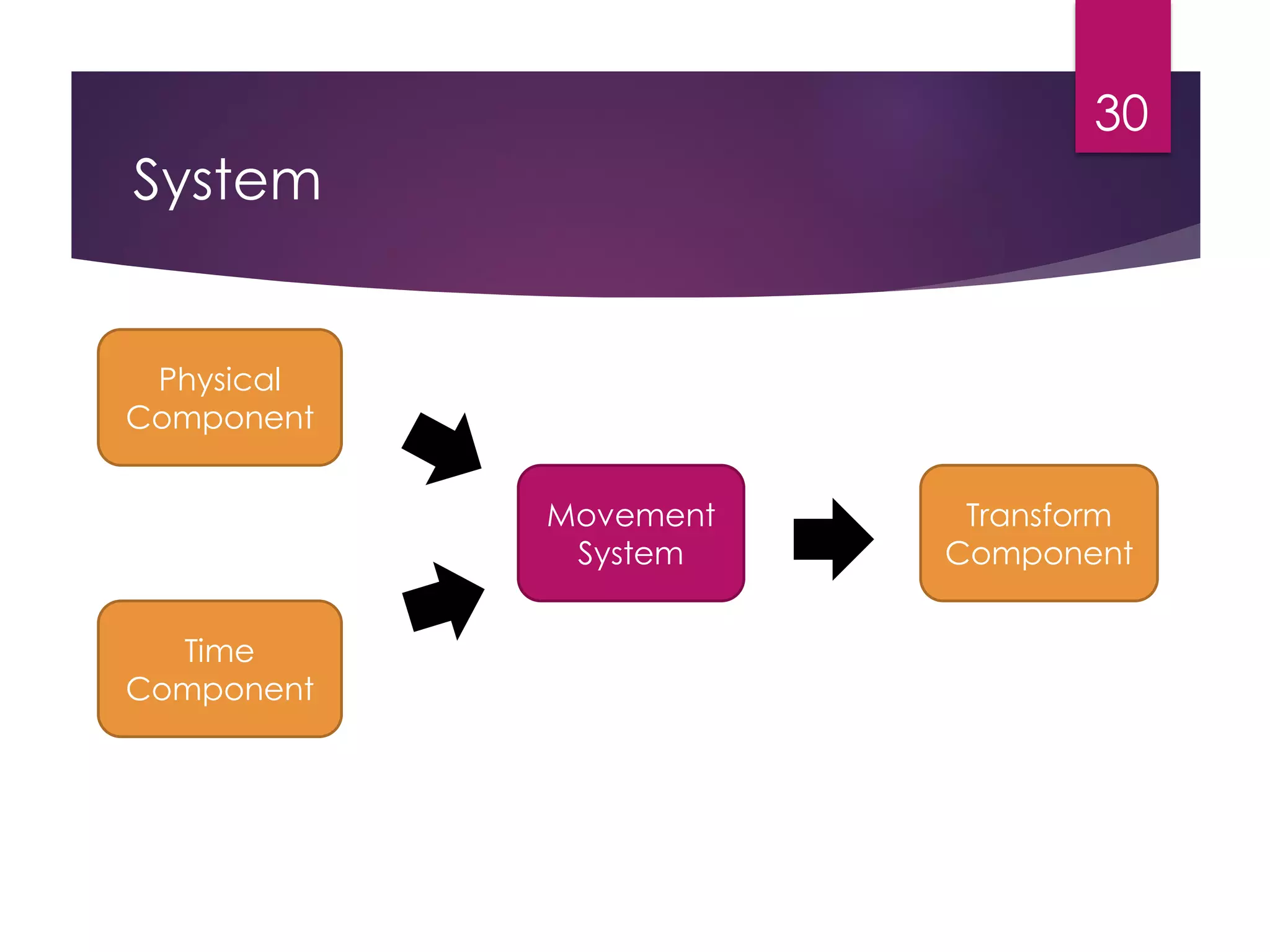
The document presents a tutorial on building a shoot 'em up game using the Amethyst game framework in Rust, covering Rust programming principles, Amethyst's entity-component-system (ECS) architecture, and integrating WebAssembly. It emphasizes Rust's safety features, the ECS model for game development, and provides insights into setting up systems and managing game states. Additionally, it discusses the performance advantages of using WebAssembly alongside Rust for game development.




![Ownership
10
let v = vec![1, 2, 3];
let v2 = v;
v.push(4) // compile error !](https://image.slidesharecdn.com/amethyst-201025135240/75/Make-A-Shoot-Em-Up-Game-with-Amethyst-Framework-10-2048.jpg)
![Borrow Checker
11
fn foo(v: &Vec<i32>) {
v.push(5);
}
let v = vec![];
foo(&v); // compile Error
v.push(10);](https://image.slidesharecdn.com/amethyst-201025135240/75/Make-A-Shoot-Em-Up-Game-with-Amethyst-Framework-11-2048.jpg)










![Systems
32
Movement
System
Boundary
System
State Play
Control
System
Collision
System
let gamedata = GameDataBuilder::default()
.with(ControlSystem, "control", &[])
.with(MovementSystem, "movement", &["control"])
.with(BoundarySystem, "boundary", &["movement"])
.with(CollisionSystem, "collision", &["boundary"])](https://image.slidesharecdn.com/amethyst-201025135240/75/Make-A-Shoot-Em-Up-Game-with-Amethyst-Framework-32-2048.jpg)






![Rust with WebAssembly
40
Hello World in Rust for WASM
#[wasm_bindgen]
extern {
fn alert(s: &str);
}
#[wasm_bindgen]
pub fn greet() {
alert("Hello, wasm from Rust!");
}](https://image.slidesharecdn.com/amethyst-201025135240/75/Make-A-Shoot-Em-Up-Game-with-Amethyst-Framework-40-2048.jpg)
![Rust with WebAssembly
41
#[wasm_bindgen]
#[repr(u8)]
pub enum Cell { Dead = 0, Alive = 1, }
#[wasm_bindgen]
pub struct Universe {
width: u32, height: u32, cells: Vec<Cell>
}
// javascript
import { Universe } from "wasm-game-of-life";
const universe = Universe.new();](https://image.slidesharecdn.com/amethyst-201025135240/75/Make-A-Shoot-Em-Up-Game-with-Amethyst-Framework-41-2048.jpg)