This document provides a summary of basic Linux commands including:
- ls to list files and directories
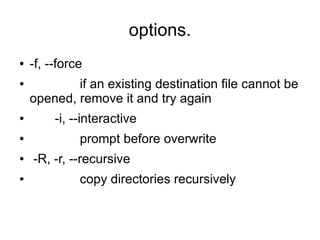
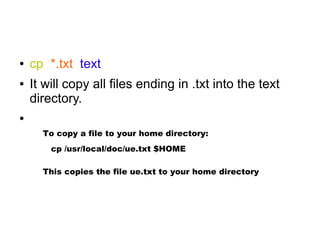
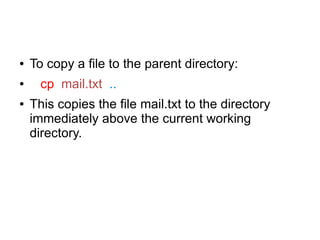
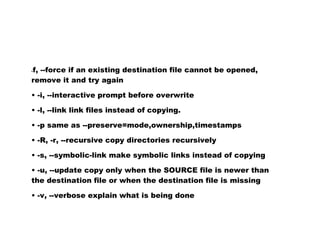
- cp to copy files
- mv to move files
- rm to remove files
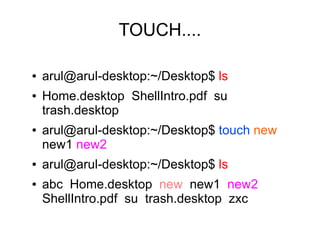
- touch to create empty files
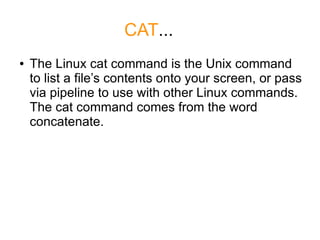
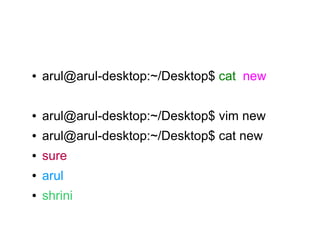
- cat to output a file's contents
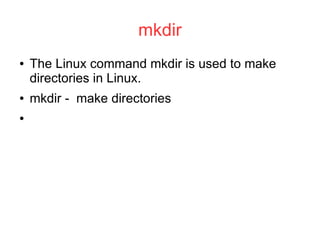
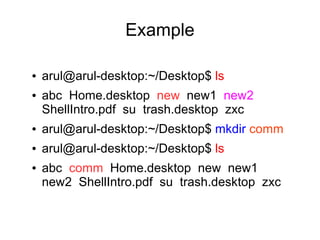
- mkdir to create directories
- grep to search for patterns in files
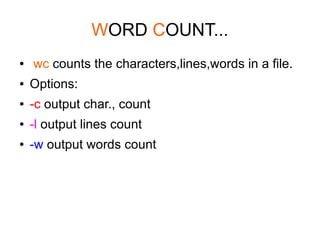
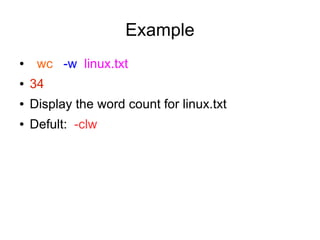
- wc to count lines, words, and characters
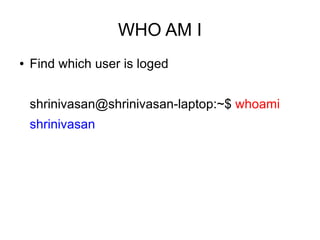
- whoami to print the current user
![LIST...
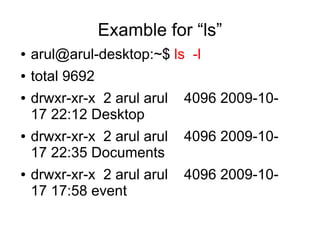
● ls [options] [file|directory]
●
-l
● will output the files and directories in long list
format.
-s, --size
print the size of each file, in blocks
-S sort by file size
-a, --all
do not ignore entries starting with .](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-2-320.jpg)

![COPY...
● cp [OPTION]... SOURCE DEST
● cp
is the Linux copy command, this shell
command is used to copy files|directories from
one location on the filesystem to another.](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-5-320.jpg)
![MOVE....
● mv [OPTION]... [-T] SOURCE DEST
● the Linux terminal command to move files|
directories. Like the cp command, but deletes
the original source.](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-10-320.jpg)
![REMOVE...
● rm -f [file]
● option is if you are wanting to force a file to
be removed
● rm -r files
● (recursive remove) Remove files,
directories, and their subdirectories](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-11-320.jpg)
![grep
grep [OPTIONS] PATTERN [FILE...]
● The Linux grep command is used to extract
lines of data from files
●
arul@arul-desktop:~/Desktop$ grep sure new
sure
arul@arul-desktop:~/Desktop$ grep s new
sure
shrini](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-17-320.jpg)
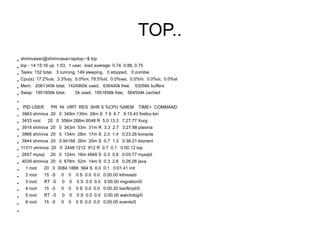
![EXAMPLE
● shrinivasan@shrinivasan-laptop:~$ ps -axu
●
Warning: bad ps syntax, perhaps a bogus '-'? See http://procps.sf.net/faq.html
●
USER PID %CPU %MEM VSZ RSS TTY STAT START TIME COMMAND
●
root 1 0.0 0.0 3084 1888 ? Ss 12:21 0:01 /sbin/init
●
root 2 0.0 0.0 0 0? S< 12:21 0:00 [kthreadd]
●
root 3 0.0 0.0 0 0? S< 12:21 0:00 [migration/0]
●
root 4 0.0 0.0 0 0? S< 12:21 0:00 [ksoftirqd/0]
●
root 5 0.0 0.0 0 0? S< 12:21 0:00 [watchdog/0]
●
root 6 0.0 0.0 0 0? S< 12:21 0:00 [events/0]
●
root 7 0.0 0.0 0 0? S< 12:21 0:00 [khelper]
●
root 8 0.0 0.0 0 0? S< 12:21 0:00 [kstop/0]
●
root 9 0.0 0.0 0 0? S< 12:21 0:00 [kintegrityd/0]
●
root 10 0.0 0.0 0 0? S< 12:21 0:00 [kblockd/0]
●
1000 6967 0.0 0.1 8332 3124 ? S 12:55 0:00 /usr/lib/gvfs/gvfs-gphoto2-volume-monitor
●
1000 7253 1.7 2.0 125404 42836 ? S 13:03 1:02 /usr/bin/okular /home/shrini/Desktop/nice_linux_guide.pdf -icon okular -
●
1000 7343 4.2 5.8 246512 120996 ? Sl 13:04 2:30 /usr/lib/openoffice/program/soffice.bin -impress /home/shrini/Desktop/li
●
postfix 10471 0.0 0.0 5792 1684 ? S 13:59 0:00 pickup -l -t fifo -u -c
●
1000 10698 0.0 0.0 2768 1032 pts/1 R+ 14:03 0:00 ps -axu
●](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-26-320.jpg)
![Kill the opretion
●
Kill -9 6967
●
Warning: bad ps syntax, perhaps a bogus '-'? See http://procps.sf.net/faq.html
●
USER PID %CPU %MEM VSZ RSS TTY STAT START TIME COMMAND
●
root 1 0.0 0.0 3084 1888 ? Ss 12:21 0:01 /sbin/init
●
root 2 0.0 0.0 0 0? S< 12:21 0:00 [kthreadd]
●
root 3 0.0 0.0 0 0? S< 12:21 0:00 [migration/0]
●
root 4 0.0 0.0 0 0? S< 12:21 0:00 [ksoftirqd/0]
●
root 5 0.0 0.0 0 0? S< 12:21 0:00 [watchdog/0]
●
root 6 0.0 0.0 0 0? S< 12:21 0:00 [events/0]
●
root 7 0.0 0.0 0 0? S< 12:21 0:00 [khelper]
●
root 8 0.0 0.0 0 0? S< 12:21 0:00 [kstop/0]
●
root 9 0.0 0.0 0 0? S< 12:21 0:00 [kintegrityd/0]
●
root 10 0.0 0.0 0 0? S< 12:21 0:00 [kblockd/0]
●
1000 7253 1.7 2.0 125404 42836 ? S 13:03 1:02 /usr/bin/okular /home/shrini/Desktop/nice_linux_guide.pdf -icon
okular -
●
1000 7343 4.2 5.8 246512 120996 ? Sl 13:04 2:30 /usr/lib/openoffice/program/soffice.bin -impress
/home/shrini/Desktop/li
●
postfix 10471 0.0 0.0 5792 1684 ? S 13:59 0:00 pickup -l -t fifo -u -c
●
1000 10698 0.0 0.0 2768 1032 pts/1 R+ 14:03 0:00 ps -axu
●](https://image.slidesharecdn.com/linuxcommands-091018105536-phpapp01-110920104535-phpapp01/85/Linuxcommands-091018105536-phpapp01-27-320.jpg)