The document is an Ansible workshop presentation led by Arie Bregman, aiming to introduce participants to Ansible as an IT automation tool that emphasizes simplicity and ease of use. It covers installation, basic commands, inventory management, writing playbooks, using modules, and executing tasks, culminating in hands-on exercises to reinforce learning. Additionally, it highlights features such as conditionals, loops, ad-hoc commands, and encourages further exploration of advanced topics like Ansible roles and error handling.

![Let’s install a package with a shell script
6
YUM_CMD=$(which yum) # or dnf
APT_GET_CMD=$(which apt-get)
...
if [[ ! -z $YUM_CMD ]]; then
dnf install ntpdate
elif [[ ! -z $APT_GET_CMD ]]; then
apt-get install ntpdate
elif ...
...
else
echo "error can't install package ntpdate"
exit 1;
fi](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-6-2048.jpg)
![Update you inventory
12
[remote]
x.x.x.x
$ sudo vi /etc/ansible/hosts
Let’s test it! :)
ansible remote -m ping
remote | SUCCESS => {
"changed": false,
"ping": "pong"
}
x.x.x.x [remote]
X.x.x.x ansible_user=vagrant
Or Or
Using this, you can
later reference in
Ansible multiple
servers with one
name](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-12-2048.jpg)
![Run your first Playbook
14
PLAY [remote] **************************************************
TASK [Gathering Facts] *****************************************
ok: [remote]
TASK [Create the file /tmp/x] **********************************
changed: [remote]
PLAY RECAP *****************************************************
remote : ok=2 changed=1 unreachable=0 failed=0 skipped=0 rescued=0
$ ansible-playbook first_playbook.yml](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-14-2048.jpg)
![Exercise #1
16
● Write a playbook which will:
○ Create the file /tmp/x
○ Create the file /tmp/y
○ Create the file /tmp/z
- hosts: [host or hosts group name]
tasks:
- name: [task name]
[module name]:
path: ...
state: ...
# Commands
ansible-playbook](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-16-2048.jpg)
![22
PLAY [remote]
********************************************************************************************************
TASK [Gathering Facts]
************************************************************************************************
ok: [192.168.33.10]
TASK [add several users]
**************************************************************************************************
changed: [192.168.33.10] => (item=/tmp/a)
changed: [192.168.33.10] => (item=/tmp/b)
changed: [192.168.33.10] => (item=/tmp/c)
PLAY RECAP
************************************************************************************************************
192.168.33.10 : ok=2 changed=1 unreachable=0 failed=0 skipped=0 rescued=0](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-22-2048.jpg)
![Conditionals
26
● Run task only when certain condition is met
- hosts: remote
tasks:
- name: Install apache httpd
become: yes
apt:
name: apache2
state: present
when: ansible_facts['distribution'] == "Ubuntu"](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-26-2048.jpg)
![Conditionals: AND
27
- hosts: remote
tasks:
- name: Install apache httpd
become: yes
apt:
name: apache2
state: present
when:
- ansible_facts['distribution'] in ['CentOS', 'RedHat']
- my_var < 6
- install_apache](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-27-2048.jpg)
![Conditionals: OR
28
- hosts: remote
tasks:
- name: Install apache httpd
become: yes
apt:
name: apache2
state: present
when: ansible_facts['distribution'] == "Ubuntu" or ansible_facts['distribution'] == "Suse"](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-28-2048.jpg)
![29
{{ [32, 3, 5, 121, 6, 7] | max }}
Filters
● Transformation of data
{{ [32, 3, 5, 121, 6, 7] | min }}
{{ [32, 3, 5, 121, 6, 7] | random }}
{{ some_path | dirname }}
{{ some_string | quote }}](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-29-2048.jpg)
![30
- hosts: remote
tasks:
- name: Create multiple files
file:
name: "{{ item }}"
state: touch
loop: “{{ files_list | default([]) }}” What is the result of
the task?
OK? Changed?
Skipped?
● Also useful for dealing with undefined variables](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-30-2048.jpg)
![Exercise #3
31
● Write a playbook which will:
○ Install the package htop only if the major version of the
operating system is 14
○ Install the package netcat only if the major version of the
operating system is 16
○ Add one random user of the following
■ [‘ed’, ‘eddy’, ‘eddie’]
# Commands
ansible-playbook
ansible-doc -l
ansible-doc <module_name>
ansible remote -m setup | less](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-31-2048.jpg)
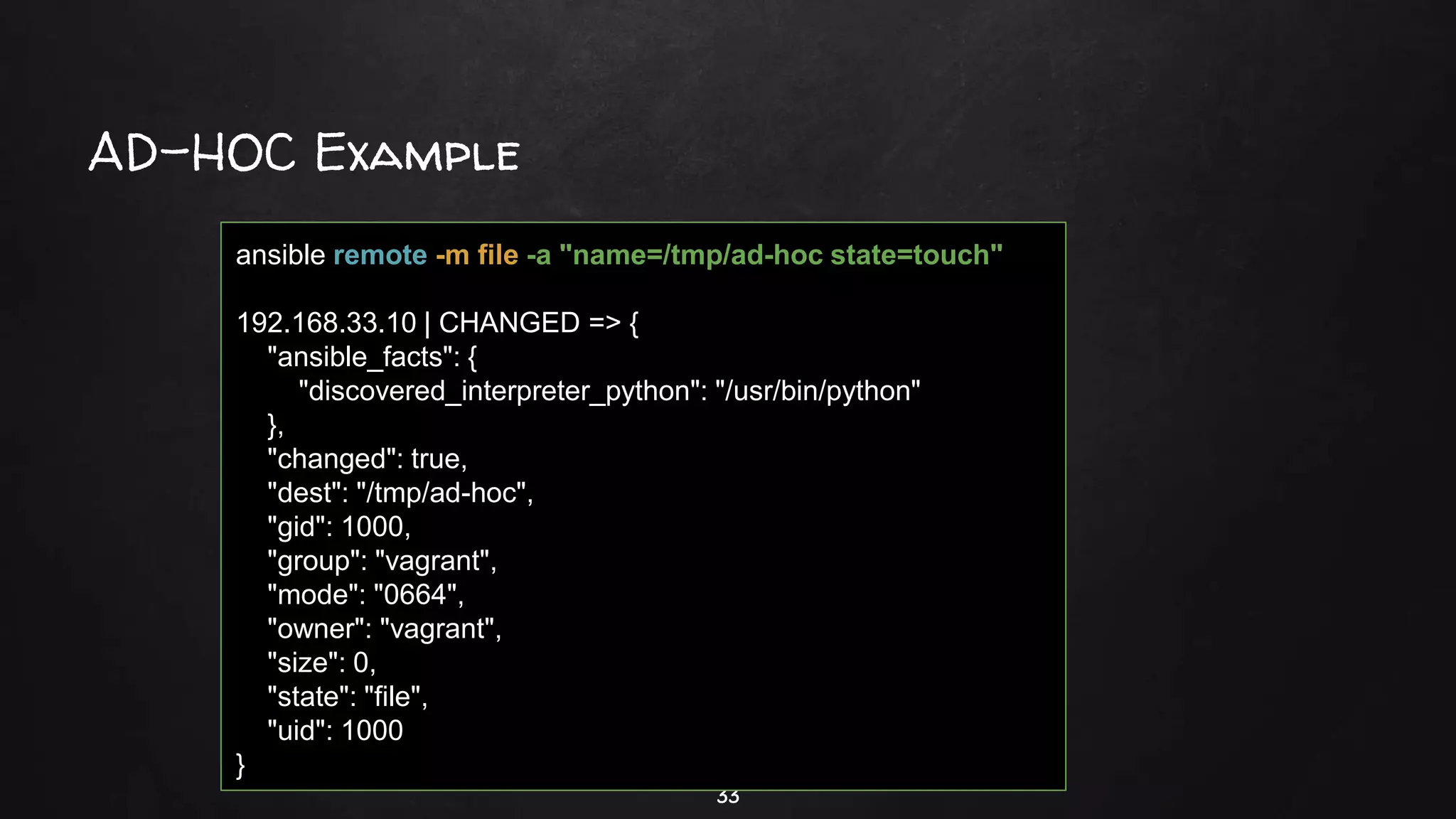
![AD-HOC
32
● Run tasks without writing playbooks
● For quick and non-repeating changes
ansible [hosts_pattern] -m [module_name] -a “[module options]”](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-32-2048.jpg)
![Exercise #4
34
● Create locally a file with the content
○ “I came here from a far far server”
● Using ad-hoc commands:
○ Add a user called “mario”
○ Run the service “cron” (Ubuntu) or “crond” (RHEL, Fedora)
○ Copy the file you create to the remote server
# Commands
ansible-playbook
ansible-doc -l
ansible-doc <module_name>
ansible remote -m setup | less
ansible remote -m module -a “...”
ansible [hosts_pattern] -m [module_name] -a “[module options]”](https://image.slidesharecdn.com/ansibleworkshop1011-200123195708/75/Ansible-for-Beginners-34-2048.jpg)