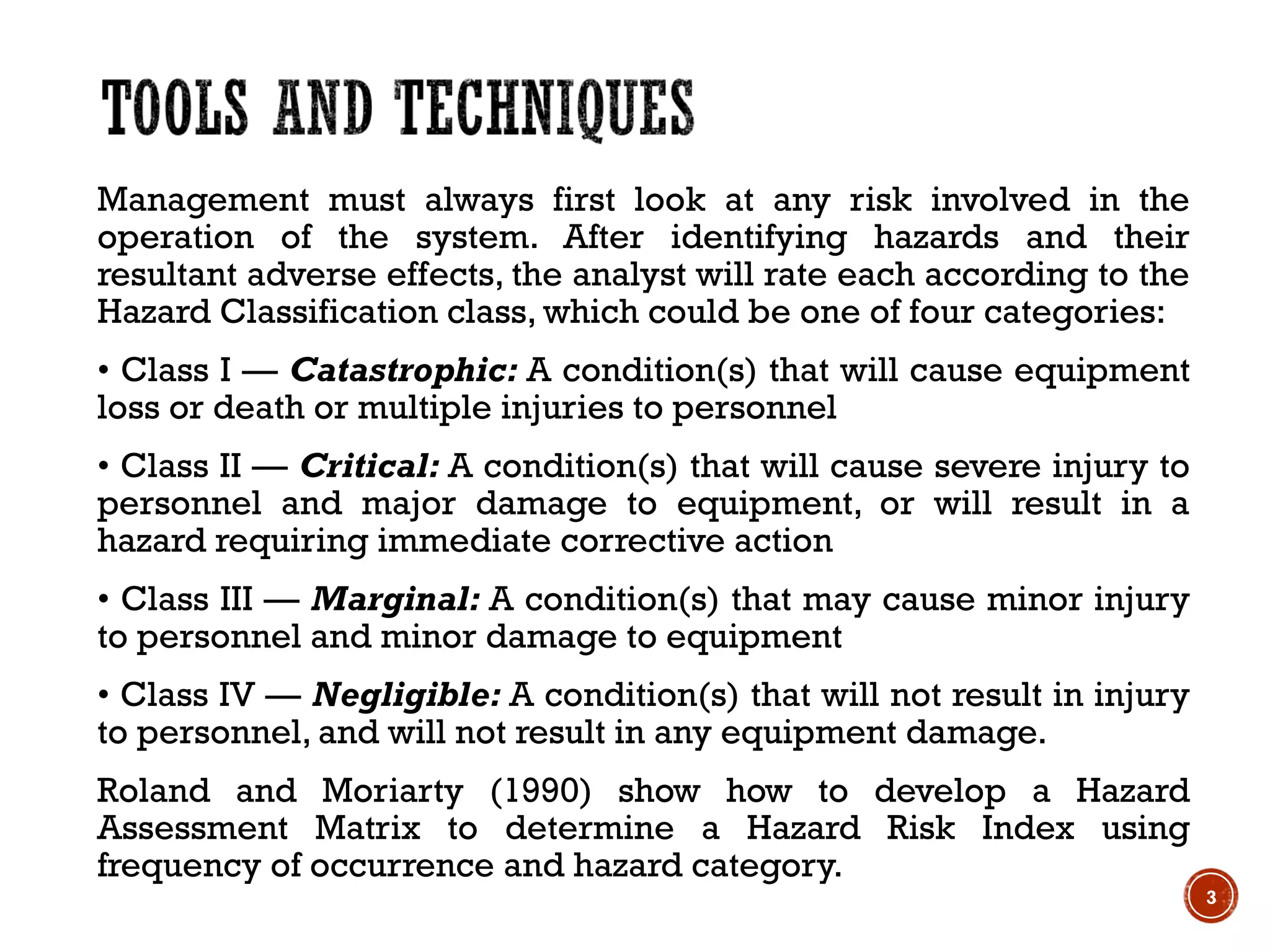
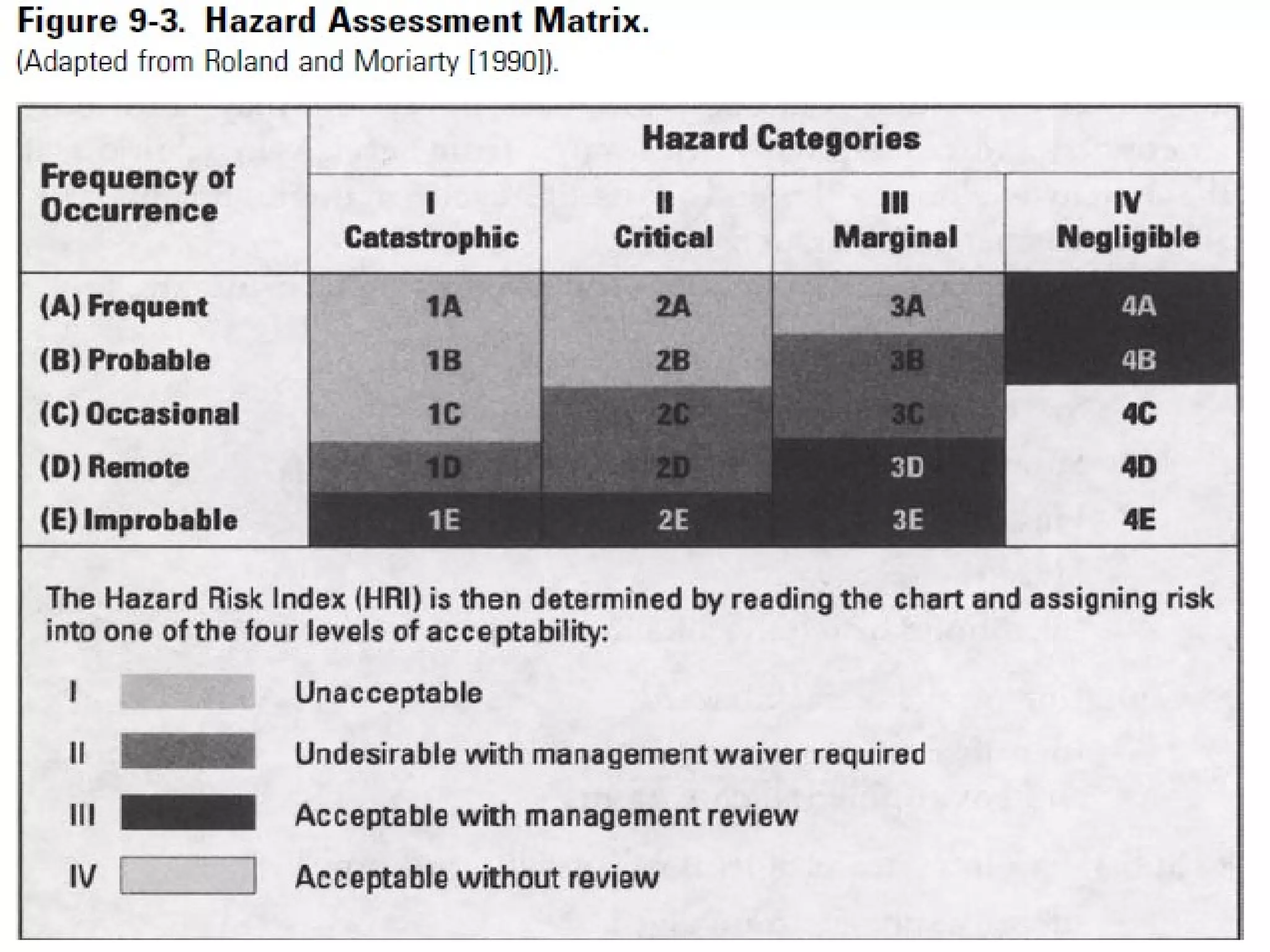
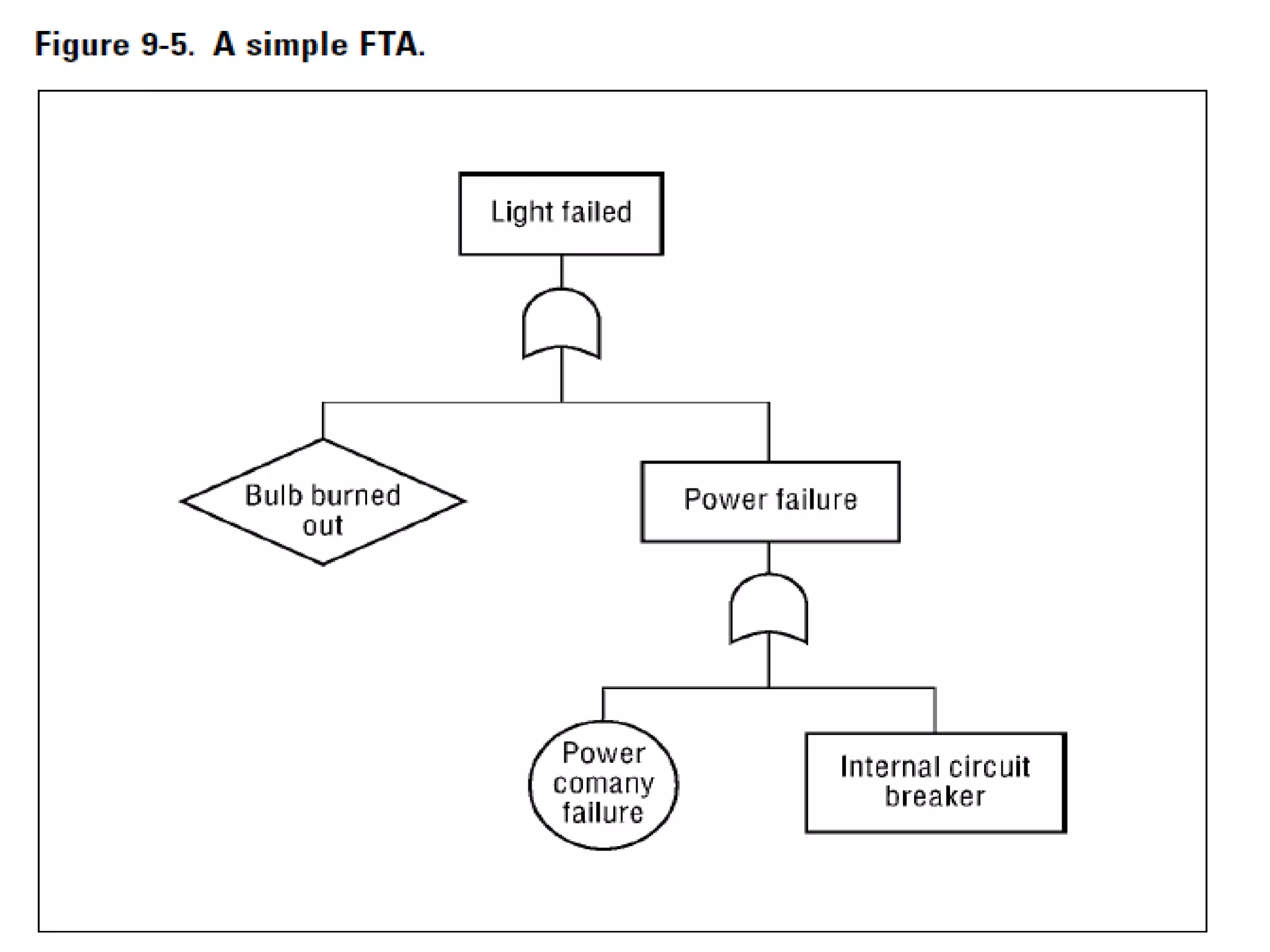
1. The document discusses various tools and techniques used in systems safety analysis, including preliminary hazard analysis, hazard classification, fault hazard analysis, fault tree analysis, failure mode and effects analysis, and technique for human error rate prediction.
2. Key tools covered are preliminary hazard analysis, used to identify hazard sources and potential accidents, and failure mode and effects analysis, which involves analyzing how components could malfunction and their downstream effects.
3. The document provides details on each tool, including how they are used to identify hazards, assess risk, and determine ways to eliminate or reduce risks in a system.