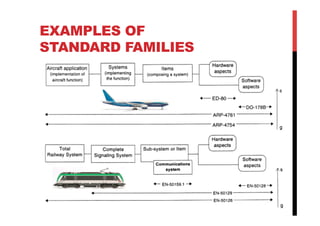
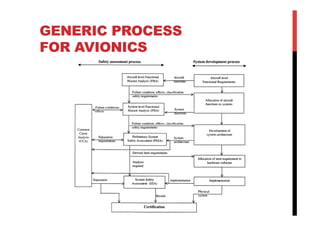
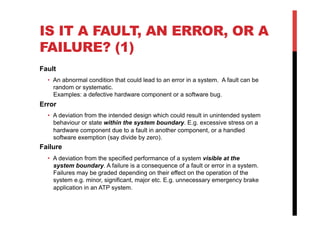
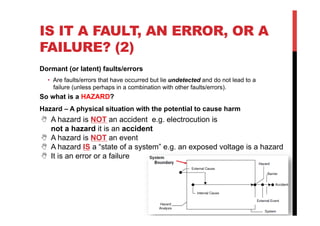
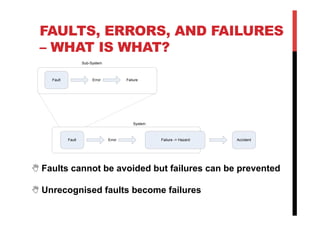
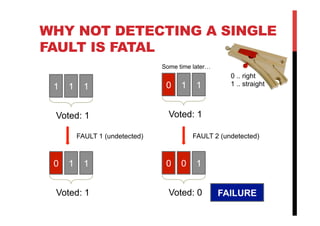
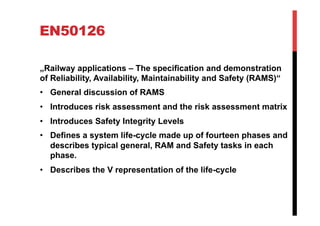
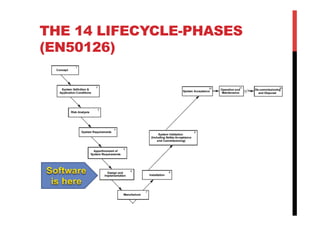
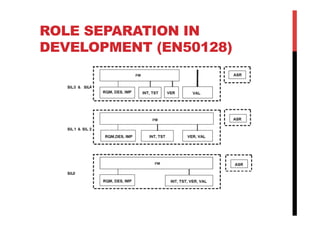
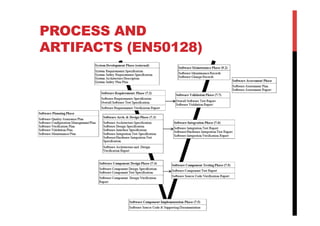
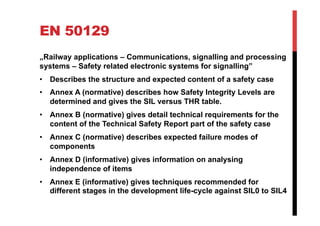
The document discusses various reliability, availability, maintainability and safety (RAMS) concepts for avionics systems. It defines key terms like reliability, availability and maintainability. It also discusses faults, errors and failures, and distinguishes between them. Finally, it provides an overview of RAMS standards like EN50126, EN50128 and EN50129 that define processes for safety-critical systems development.