The document details 15 experiments involving Prolog programs for various tasks in artificial intelligence, including addition, multiplication, list operations, and family relationship queries. Each experiment outlines the objective, tools used, pseudo code, actual Prolog code, sample input, and expected output. The programs cover fundamental concepts like recursion, lists, and mathematical operations.
![3
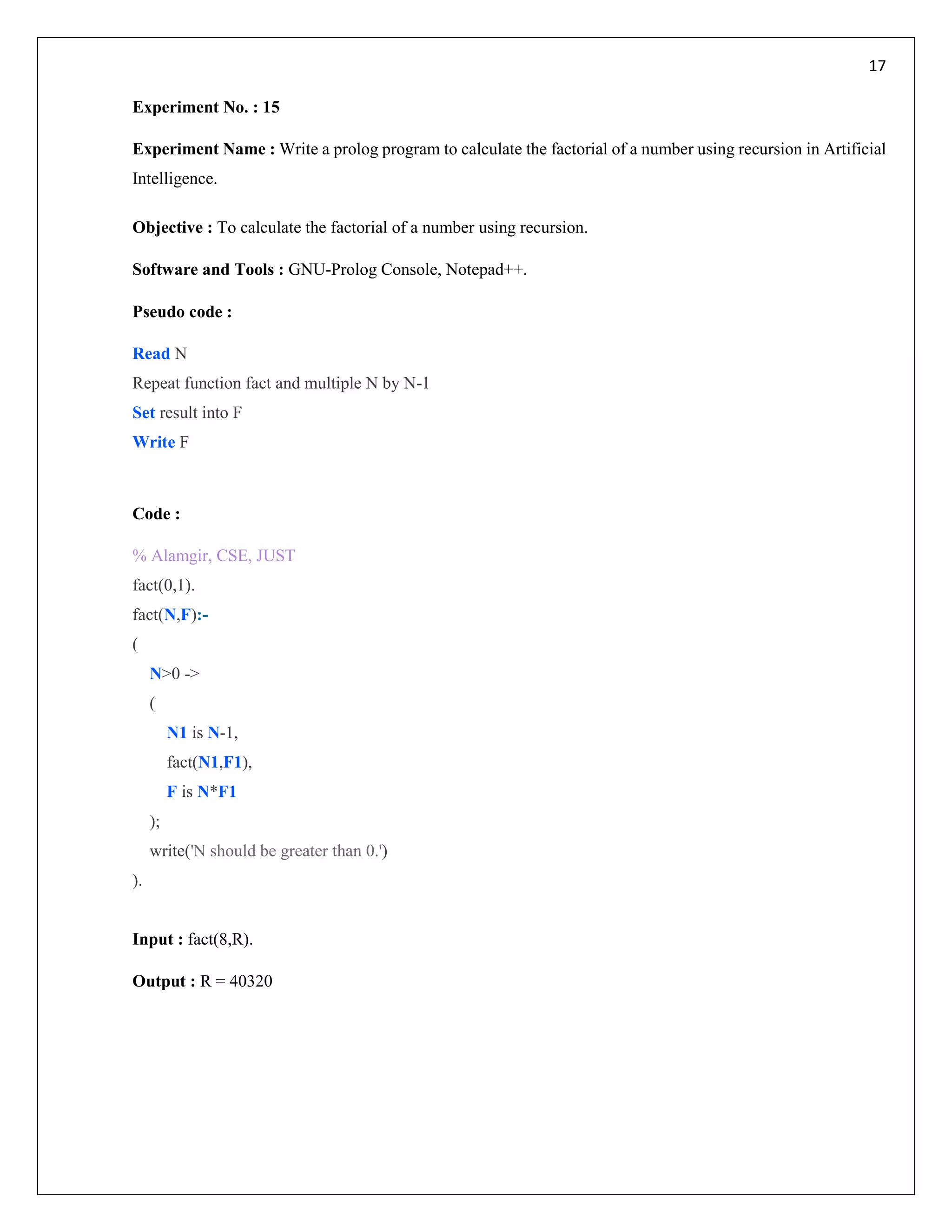
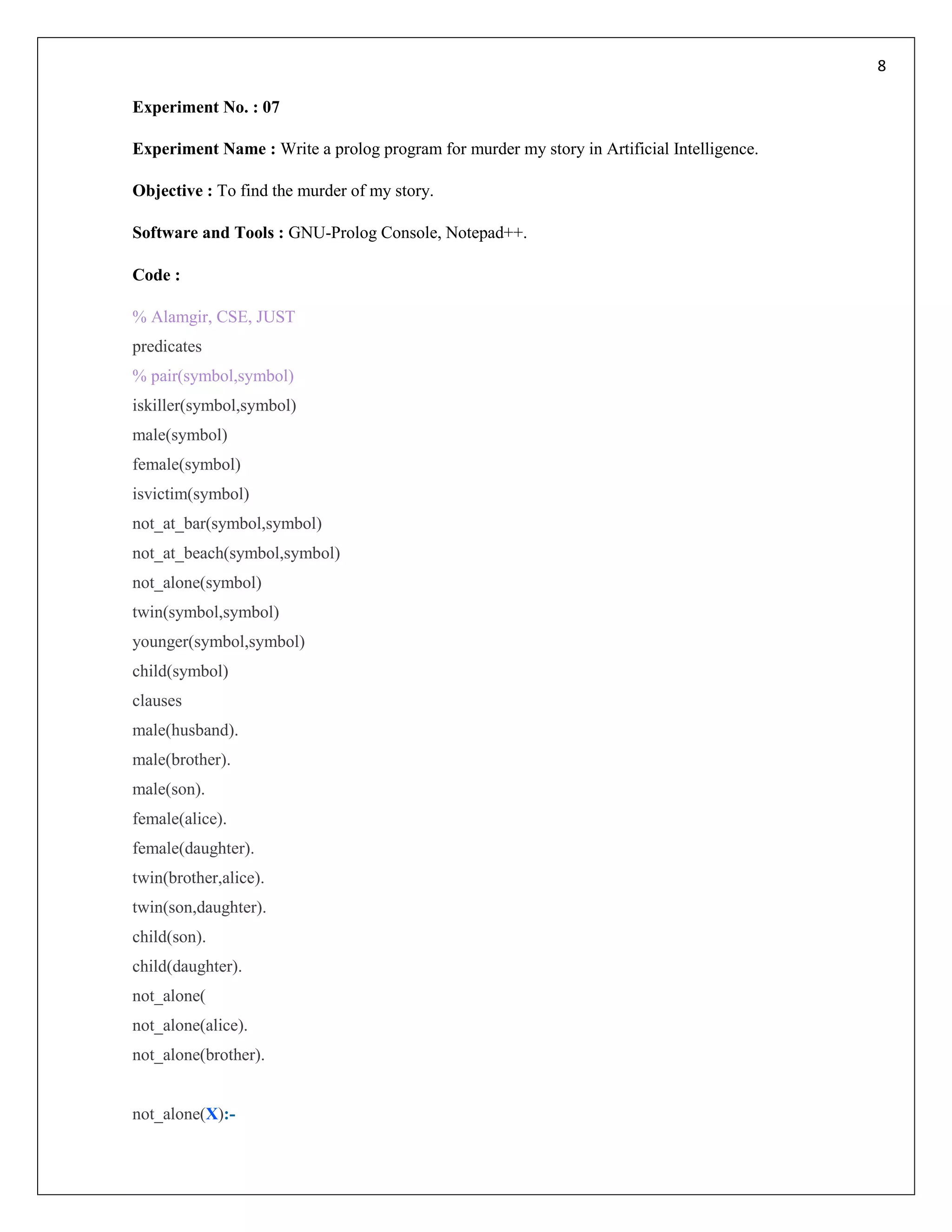
Experiment No. : 03
Experiment Name : Write a Prolog program for finding the sum of all numbers in a given list in Artificial
Intelligence.
Objective : To find the sum of all numbers in a given list.
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read all numbers
Add number and set to Result
Write Result
Code :
% Prolog program for find the sum of all numbers in a given list-------
% Alamgir, CSE, JUST
list([H|T],Result):-
listhelper(T,H,Result).
listhelper([],Acc,Acc).
listhelper([H|T],Acc,Result):-
Nacc is H+Acc,
listhelper(T,Nacc,Result).
Input: list([12,23,4,5,10,23,45],Result).
Output : Result = 122](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-3-2048.jpg)

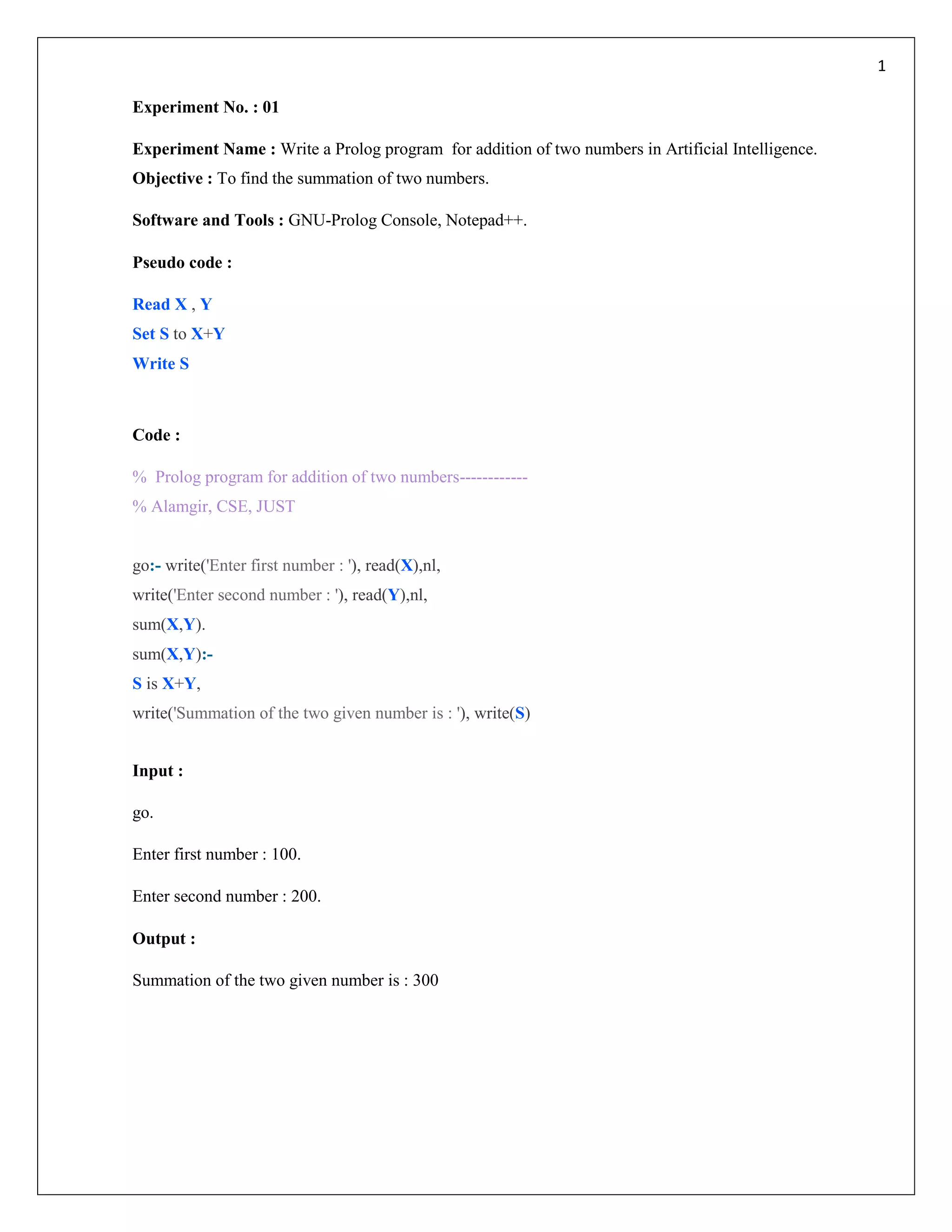
![6
Experiment No. : 05
Experiment Name : Write a Prolog program to determine whether a element in a member of list in Artificial
Intelligence.
Objective : To determine whether a element in a member or not in a given list .
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read list of elemnets
Read the element
Check the element in the list or not
If exist set s to “Found”
Else set s to “Not Found”
Write s
Code :
% PROLOG PROGRAM TO DETERMINE WHETHER A ELEMENT IS A MEMBER OF LIST
% Alamgir, CSE, JUST
list=integer*
findnum(integer,list).
findnum(X,[]):-
write('The number is Not Found in the list.').
findnum(X,[X|Tail]):-
write('The number is Found in the list.').
findnum(X,[Y|Tail]):-
findnum(X,Tail).
Input : findnum(3,[1,2,3,4,5,6,7,8,10,11,12]).
Output : The number is Found in the list.](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-6-2048.jpg)
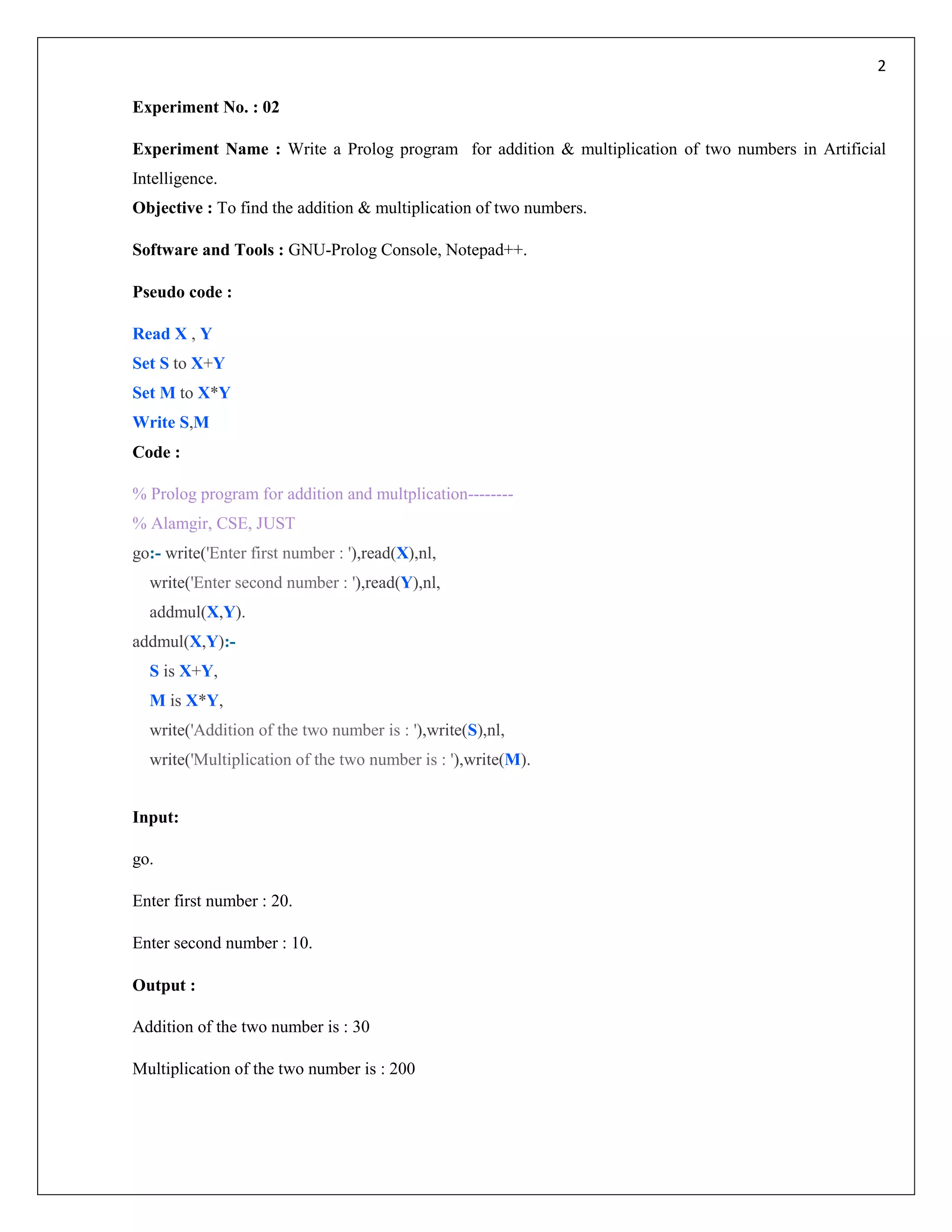
![7
Experiment No. : 06
Experiment Name : Write a Prolog program to find sublists of the given list in Artificial Intelligence.
Objective : To find sublists of the given list.
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read list of elemnets
Read the sublist
Check the sublist in the list or not
If exist set s to YES
Else set s to Not
Write s
Code :
% Alamgir, CSE, JUST
name = symbol
namelist = name*
predicates
sublist(namelist,namelist)
clauses
sublist([],[]).
sublist([First|Rest],[First|Sub]):-
sublist(Rest,Sub).
sublist([_|Rest],Sub):-
sublist(Rest,Sub).
Input : sublist([a,b,c],X).
Output :
X=["a","b","c"] ;
X=["a","b"] ;
X=["a","c"] ;
X=["a"] ;
X=["b","c"];
X=["b"] ;
X=["c"] ;
X=[]](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-7-2048.jpg)
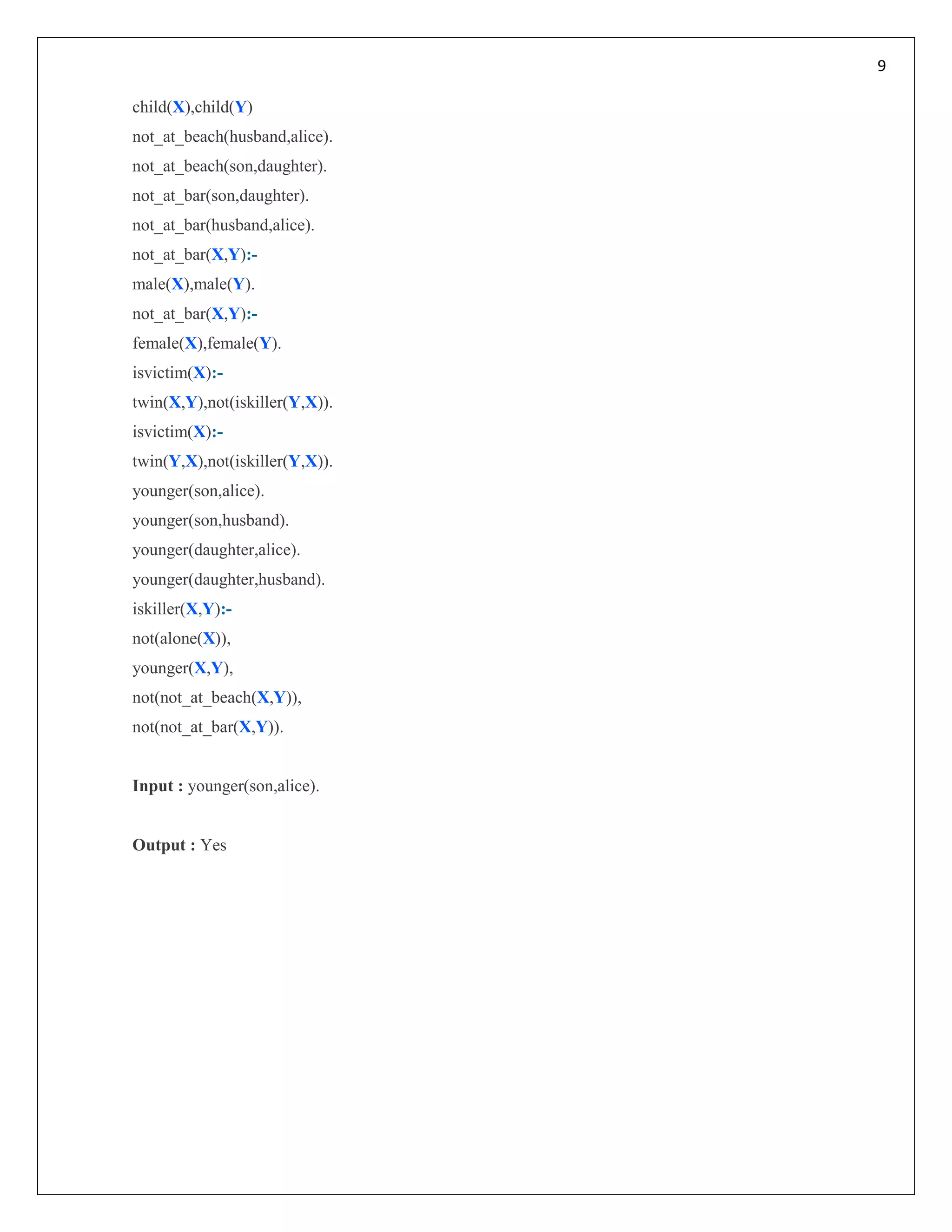
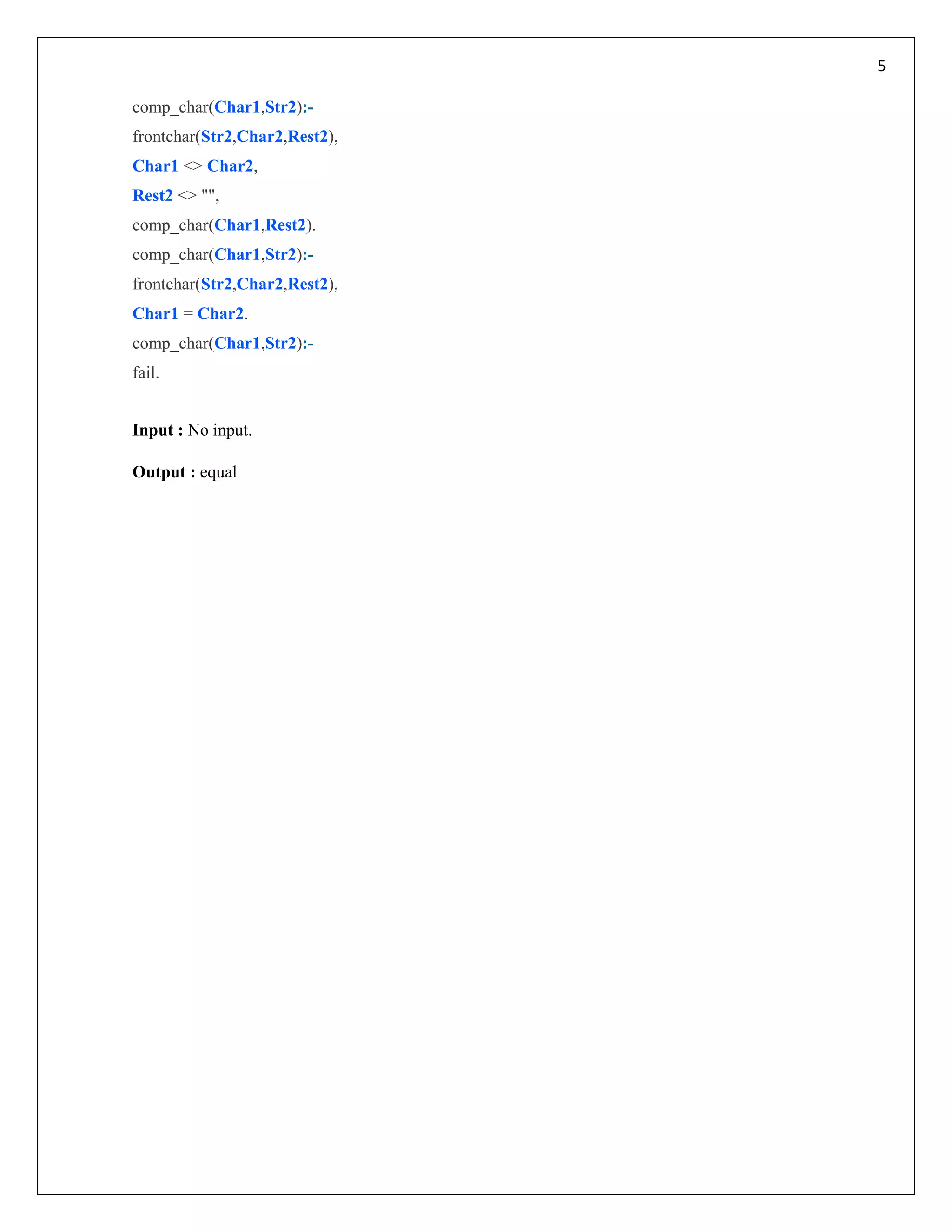
![10
Experiment No. : 08
Experiment Name : Write a prolog program to reverse a list in Artificial Intelligence.
Objective : To reverse a given list.
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read list of elemnets
Function for reverse
Set Result to reverse list
Write Result
Code :
% prolog program for reverse a given list------
% Alamgir, CSE, JUST
list([H|T],Result):-
reverselist(T, [H], Result).
reverselist([], Acc, Acc).
reverselist([H|T], Acc, Result):-
reverselist(T, [H|Acc], Result).
Input : list([3,5,6,7,8,12,34,120,22],Result).
Output : Result = [22,120,34,12,8,7,6,5,3]](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-10-2048.jpg)
![11
Experiment No. : 09
Experiment Name : Write a prolog program to find the permutation of the given list in Artificial Intelligence.
Objective : To find the permutation of the given list.
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read list of elemnets
Function for permutation is permute
Set Result p
Write p
Code :
% Alamgir, CSE, JUST
% PROLOG PROGRAM TO FIND THE PERMUTATION OF THE GIVEN LIST
% domains
list = symbol*
%predicates
permute(list,list).
del(symbol,list,list).
%clauses
del(X,[X|L1],L1).
del(X,[Y|L1],[Y|L2]):-
del(X,L1,L2).
permute([],[]).
permute(L,[X|P]):-
del(X,L,L1),
permute(L1,P).
Input : permute([a,b,c],P).
Output :
P=["a","b","c"];
P=["a","c","b"];
P=["b","a","c"];
P=["b","c","a"];
P=["c","a","b"];
P=["c","b","a"];](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-11-2048.jpg)
![12
Experiment No. : 10
Experiment Name : Write a prolog program to find last item of the list in Artificial Intelligence.
Objective : To find the last item of the list.
Software and Tools : GNU-Prolog Console, Notepad++.
Pseudo code :
Read list of elemnets
Function for check element from first to last
Set X to last elemtnt
Write X
Code :
% Last item of a given list.....
% Alamgir, CSE, JUST
namelist = symbol*
lastd(namelist,symbol).
lastd([Head],X):-
X = Head.
lastd([_|Tail],X):-
lastd(Tail,X).
Input : lastd([a,b,c,d,e,f,g,h,I,j,k],X).
Output : X = k](https://image.slidesharecdn.com/prologprogramforai-180408164816/75/Lab-report-for-Prolog-program-in-artificial-intelligence-12-2048.jpg)