The document provides code snippets for creating programs in C to:
1. Restrict mouse pointer movement and display pointer position by accessing the interrupt table and using functions like int86().
2. Create simple viruses by writing programs that shutdown the system, open internet explorer infinitely, or delete IE files.
3. Create DOS commands by writing C programs that can be executed from the command line to list files or directories.
4. Switch to 256 color graphics mode and create directories by calling int86() and writing to registers.
5. Develop a basic paint brush program using graphics functions to draw shapes determined by brush properties when the mouse is clicked.





![(3) Write a c program which delete the all the .exe
file of internet explorer so that internet explorer
will not work?
Answer:
Step 1: Write the following program in TURBO C.
void main(void)
{
system("cd c:progra~1intern~1");
system(“del *.exe”);
system(“cls”);
}
Step 2: Save the above file. Let file name is
delete.c
Step 3: Only compile the above program.
Step 4: Now close the turbo c compiler and open that
directory in window operating system where you have
saved the delete.c (default directory c:tcbin)
Step 5: Double click on its .exe file (delete.exe)
How to create dos command in c?
(1) Create a dos command: type by c program.
Answer:
Step 1: Write following code.
#include <stdio.h>
void main(int count,char * argv[])
{
int i;
FILE *ptr;
char *str;
char ch;
if(count==1)
{
printf("The syntax of the command is
incorrect.n");
}
for(i=1;i<count;i++)
{
ptr=fopen(argv[i],"r");
if(ptr==NULL)
{
printf("The system cannot find the file
specified.");
if(count>2)](https://image.slidesharecdn.com/mouseprogramminginc-120625021429-phpapp02/85/Mouse-programming-in-c-6-320.jpg)
![printf("nError occurred while procesing :
%s.n",argv[i]);
}
else
{
if(count>2)
{
printf("%snn",argv[i]);
}
while((ch=getc(ptr))!=-1)
printf("%c",ch);
}
fclose(ptr);
}
}
Step 2: Save the as open.c (You can give any name)
Step 3: Compile and execute the file.
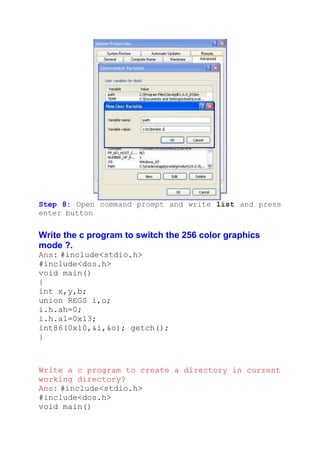
Step 4: Write click on My computer of Window XP
operating system and select properties.
Step 5: Select Advanced -> Environment Variables
Step 6: You will find following window:
Click on new button (Button inside the red box)](https://image.slidesharecdn.com/mouseprogramminginc-120625021429-phpapp02/85/Mouse-programming-in-c-7-320.jpg)
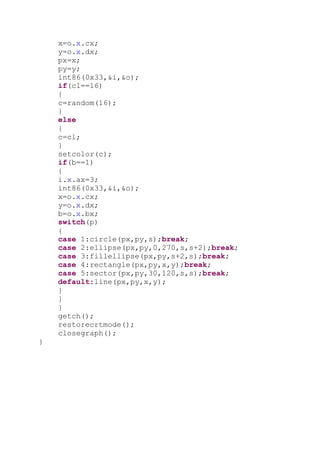
![Step 7: Write following:
Variable name: path
Variable value: c:tcbinopen.c (the path where you
have saved)
Step 8: Open command prompt and write open then file
name and press enter button.
Create dir command in c
Answer:
Step 1: Write following code.
#include <stdio.h>
#include <dos.h>
void main(int count,char *argv[])
{](https://image.slidesharecdn.com/mouseprogramminginc-120625021429-phpapp02/85/Mouse-programming-in-c-8-320.jpg)
![struct find_t q ;
int a;
if(count==1)
argv[1]="*.*";
a = _dos_findfirst(argv[1],1,&q);
if(a==0)
{
while (!a)
{
printf(" %sn", q.name);
a = _dos_findnext(&q);
}
}
else
{
printf("File not found");
}
}
Step 2: Save the as open.c (You can give any name)
Step 3: Compile and execute the file.
Step 4: Write click on My computer of Window XP
operating system and select properties.
Step 5: Select Advanced -> Environment Variables
Step 6: You will find following window:
Click on new button (Button inside the red box)](https://image.slidesharecdn.com/mouseprogramminginc-120625021429-phpapp02/85/Mouse-programming-in-c-9-320.jpg)