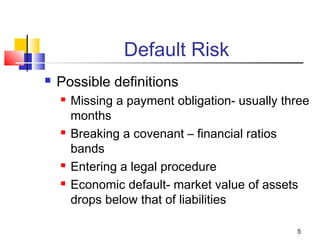
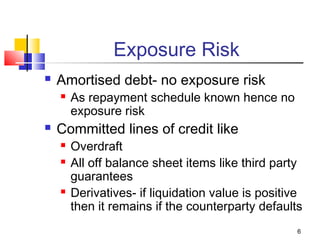
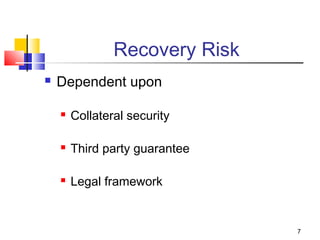
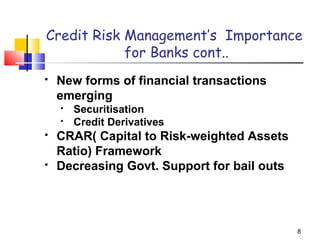
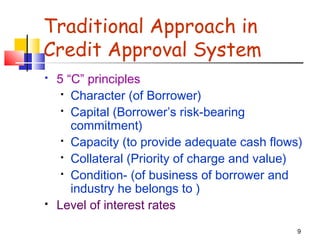
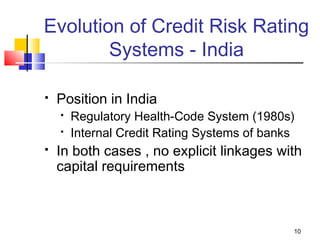
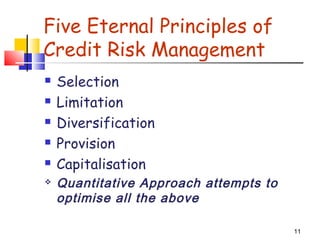
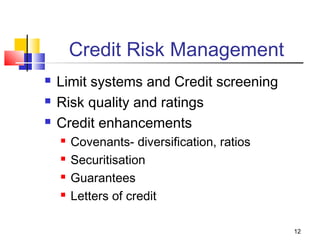
Credit risk refers to the risk of a counterparty defaulting on their obligations. It is defined as the possibility that a borrower may fail to meet their obligations in accordance with the agreed terms. There are several components of credit risk, including the amount of the loan, quality of the loan, default risk, exposure risk, and recovery risk. Credit risk management is important for banks due to new financial transactions, decreasing government support, and regulatory capital requirements. Banks traditionally evaluated credit risk using the 5 C's of credit analysis and now also utilize internal credit rating systems.