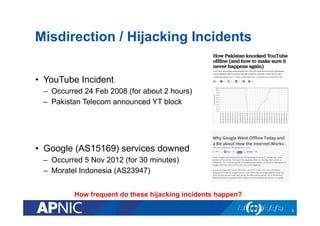
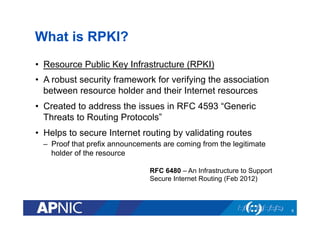
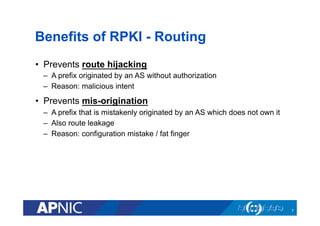
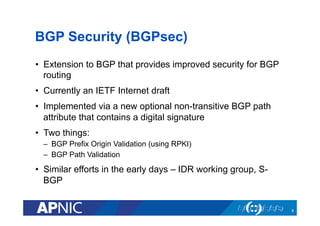
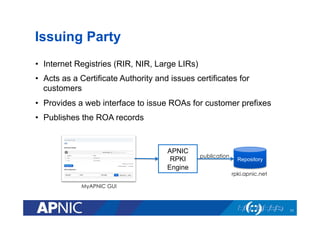
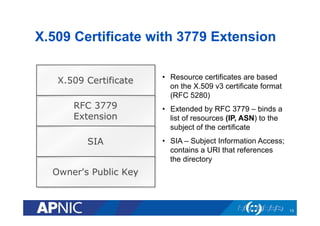
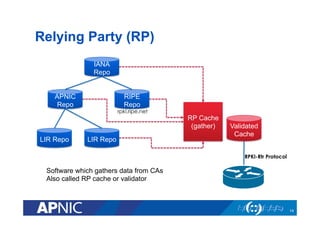
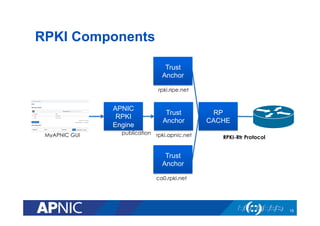
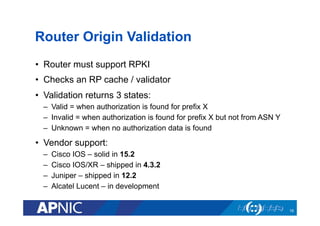
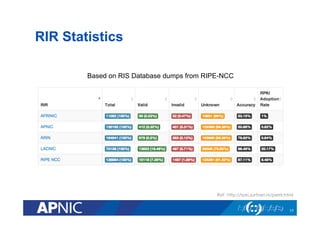
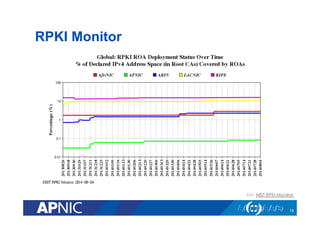
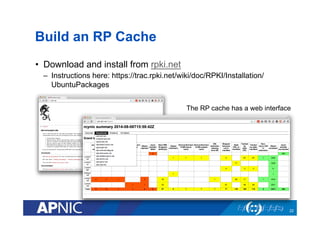
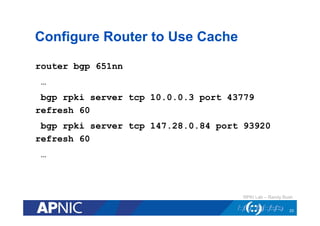
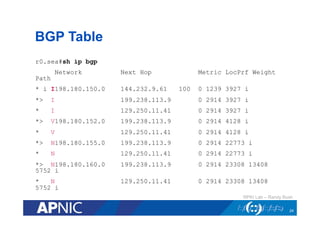
The document discusses the Resource Public Key Infrastructure (RPKI) which aims to address routing incidents caused by IP prefix hijacking and misorigination. It provides an overview of RPKI technical details, components, and deployment status. RPKI uses digital certificates and Route Origin Authorizations (ROAs) to validate that IP prefixes are announced by their legitimate holders and prevent unauthorized route announcements. Major RPKI components include Certificate Authorities (CAs), Relying Parties (RPs), and routers configured to use RPKI data to validate BGP routes.