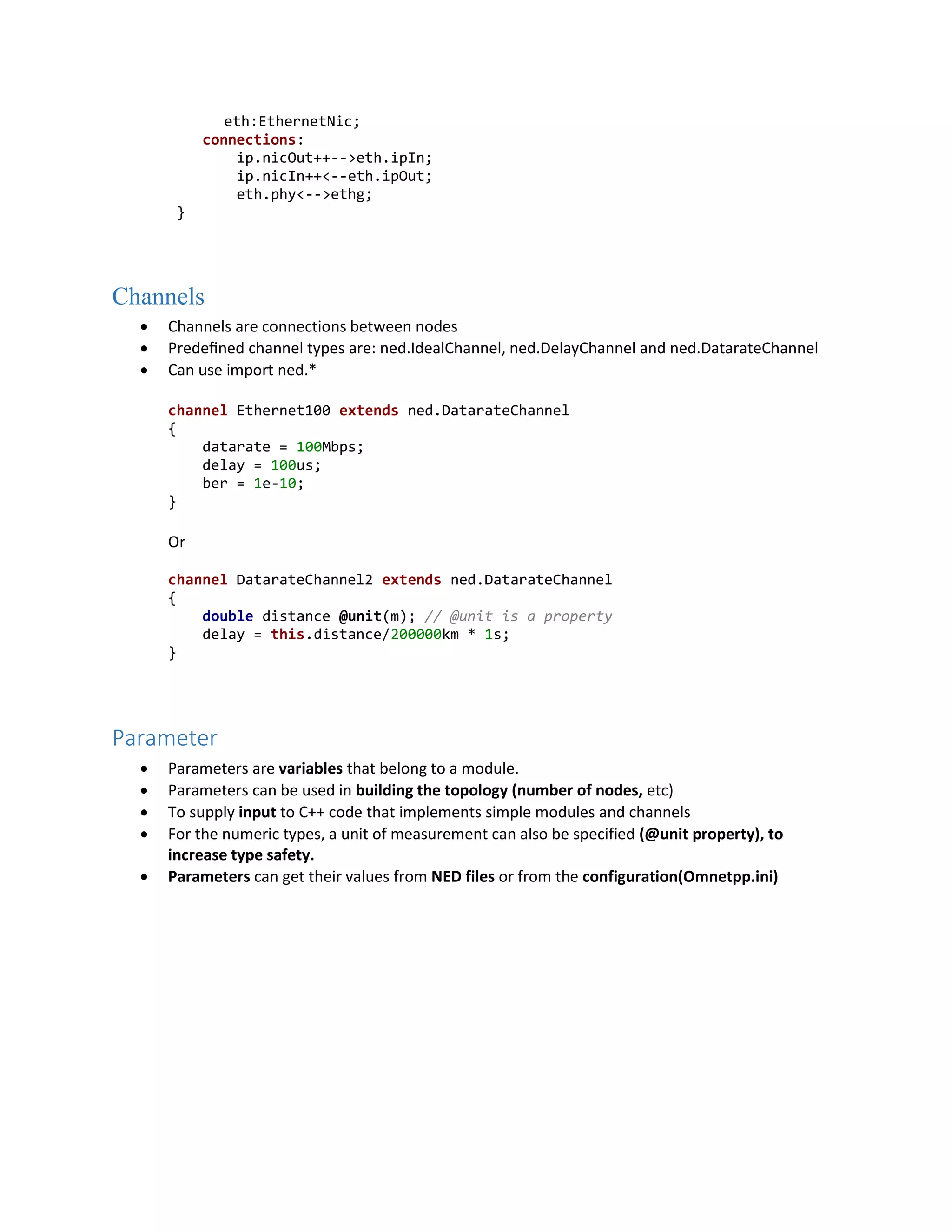
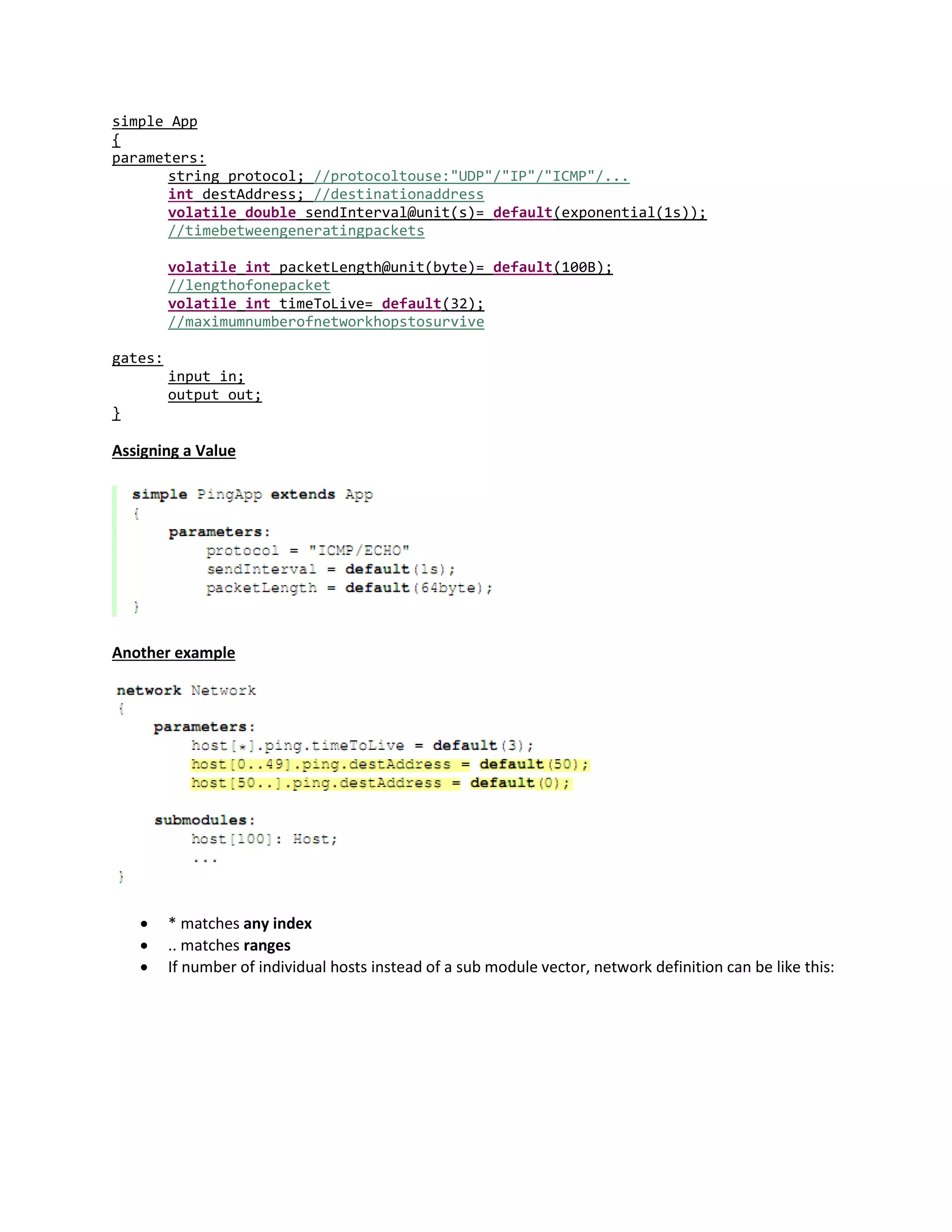
OMNeT++ is a simulator for modeling communication networks. It uses an object-oriented modular architecture where modules communicate by passing messages. Modules can be simple or compound, with compound modules made up of interconnected simple modules. The network topology is defined using the NED language. When a simulation starts, OMNeT++ loads the NED files defining the network structure and connects simple modules implemented in C++ code. Parameters can be assigned to modules, connections, and channels to configure the simulation.
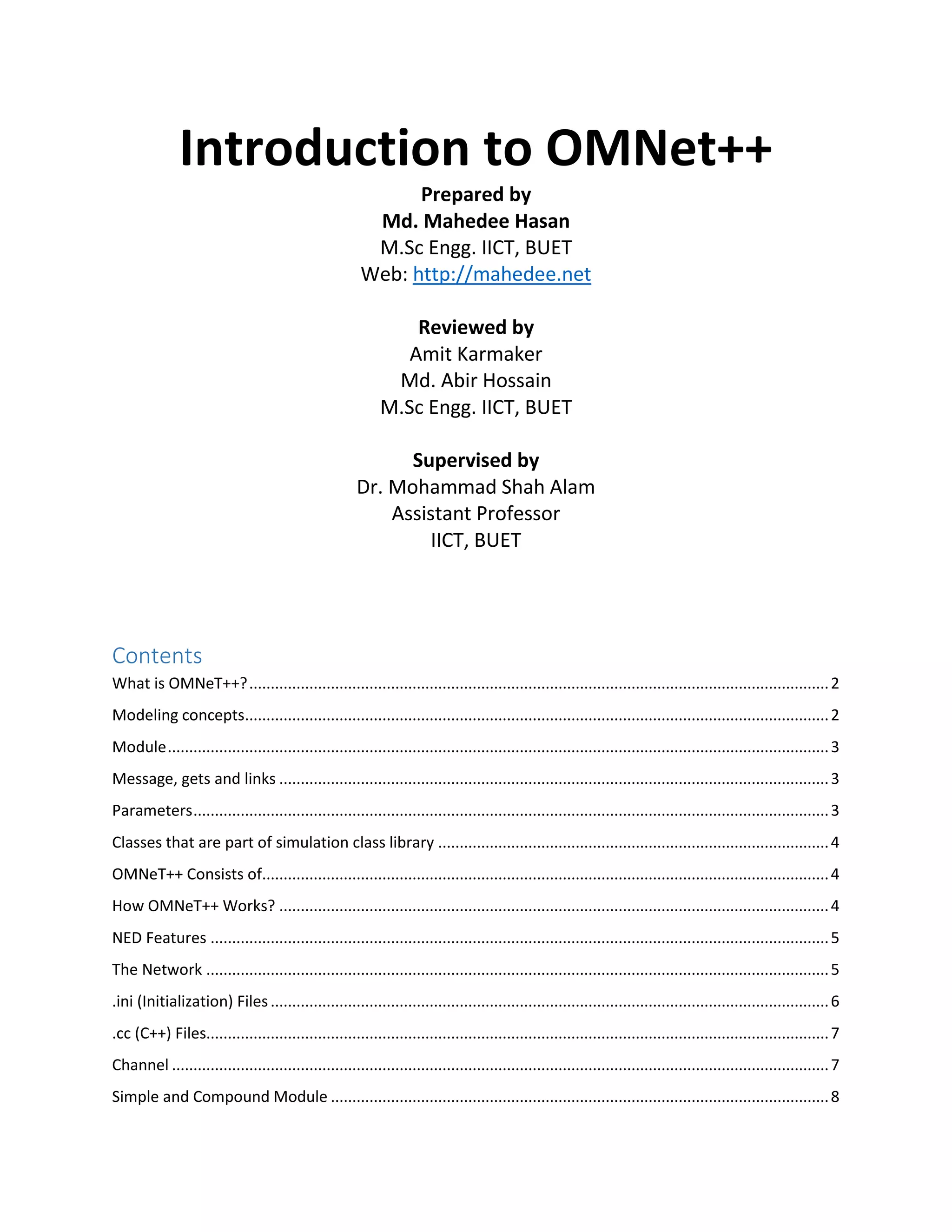
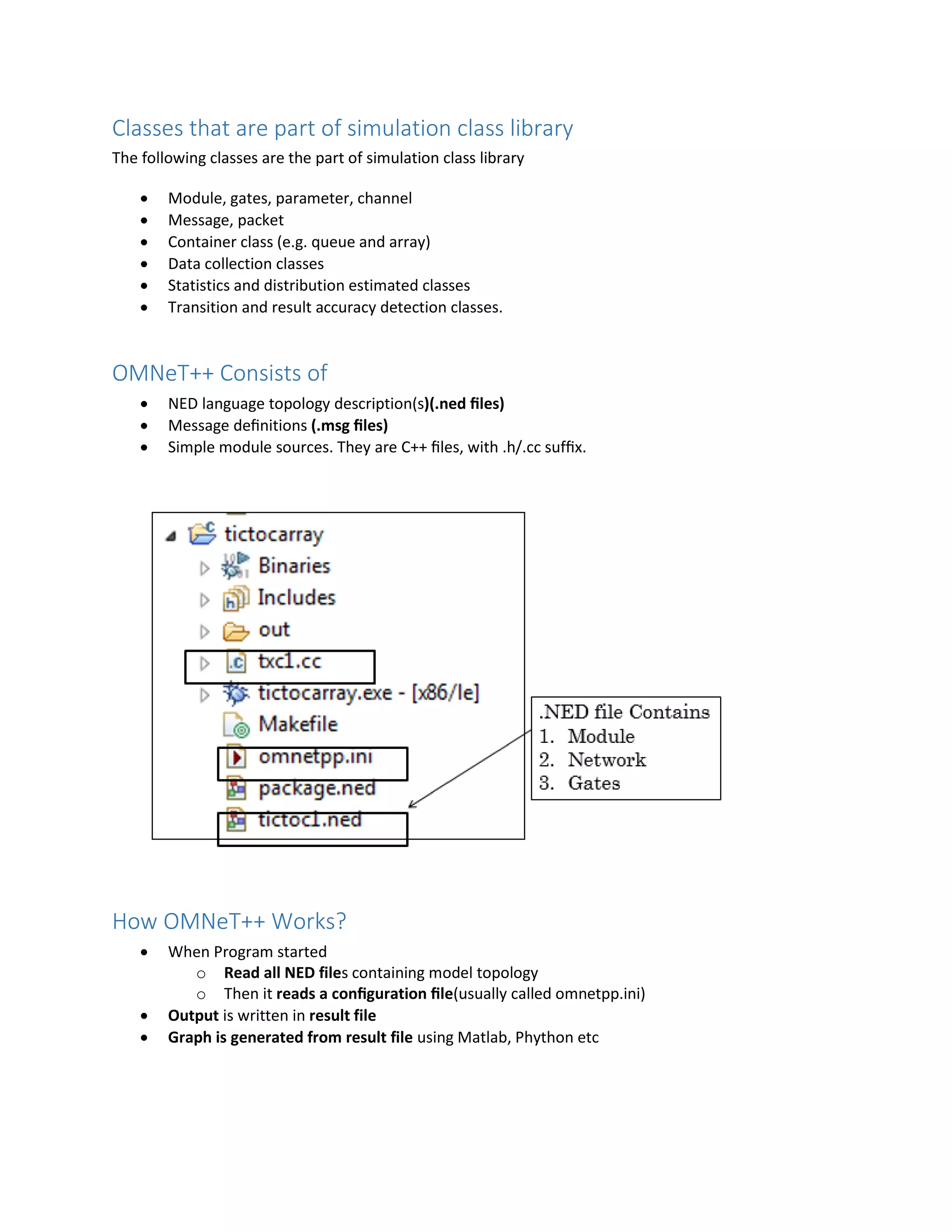
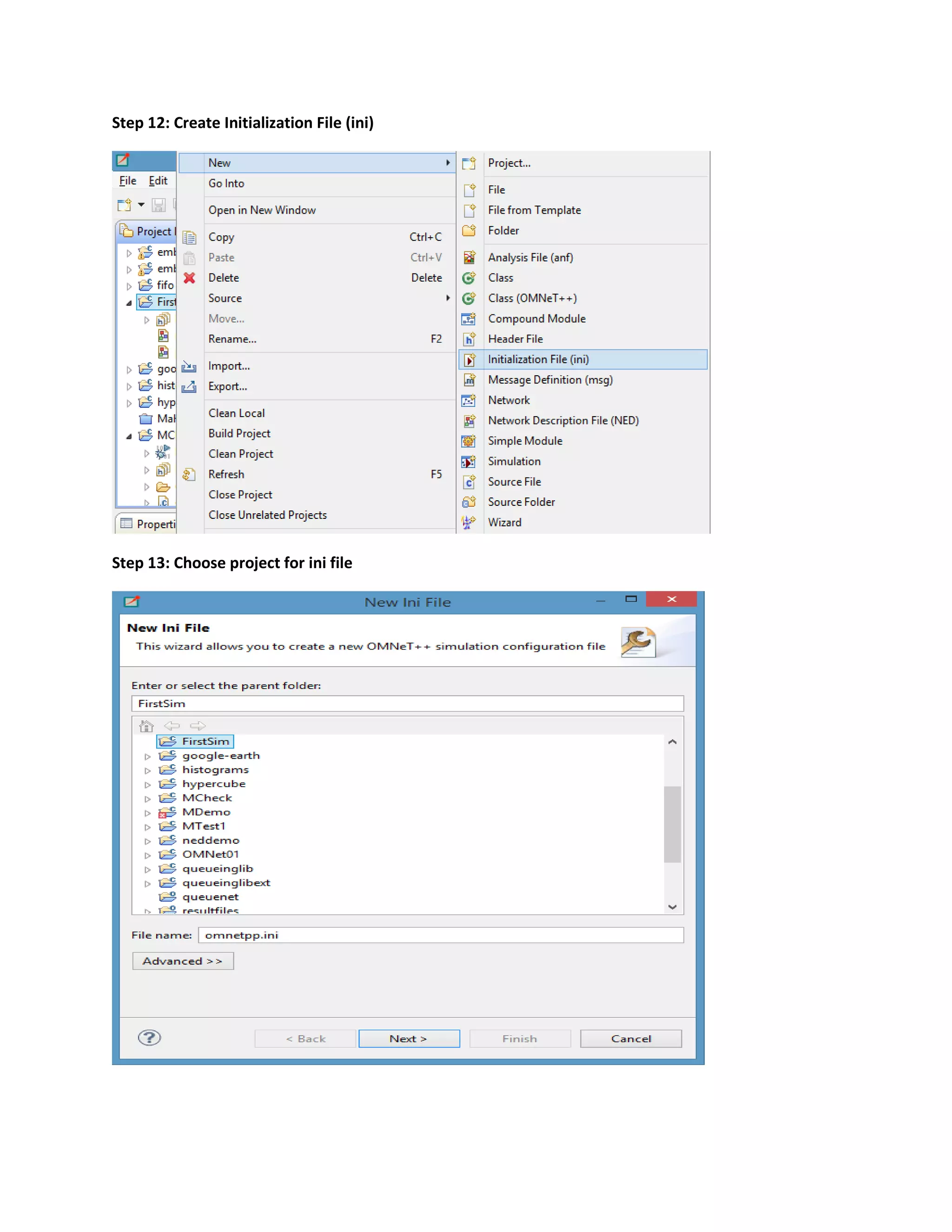
![network Network
{
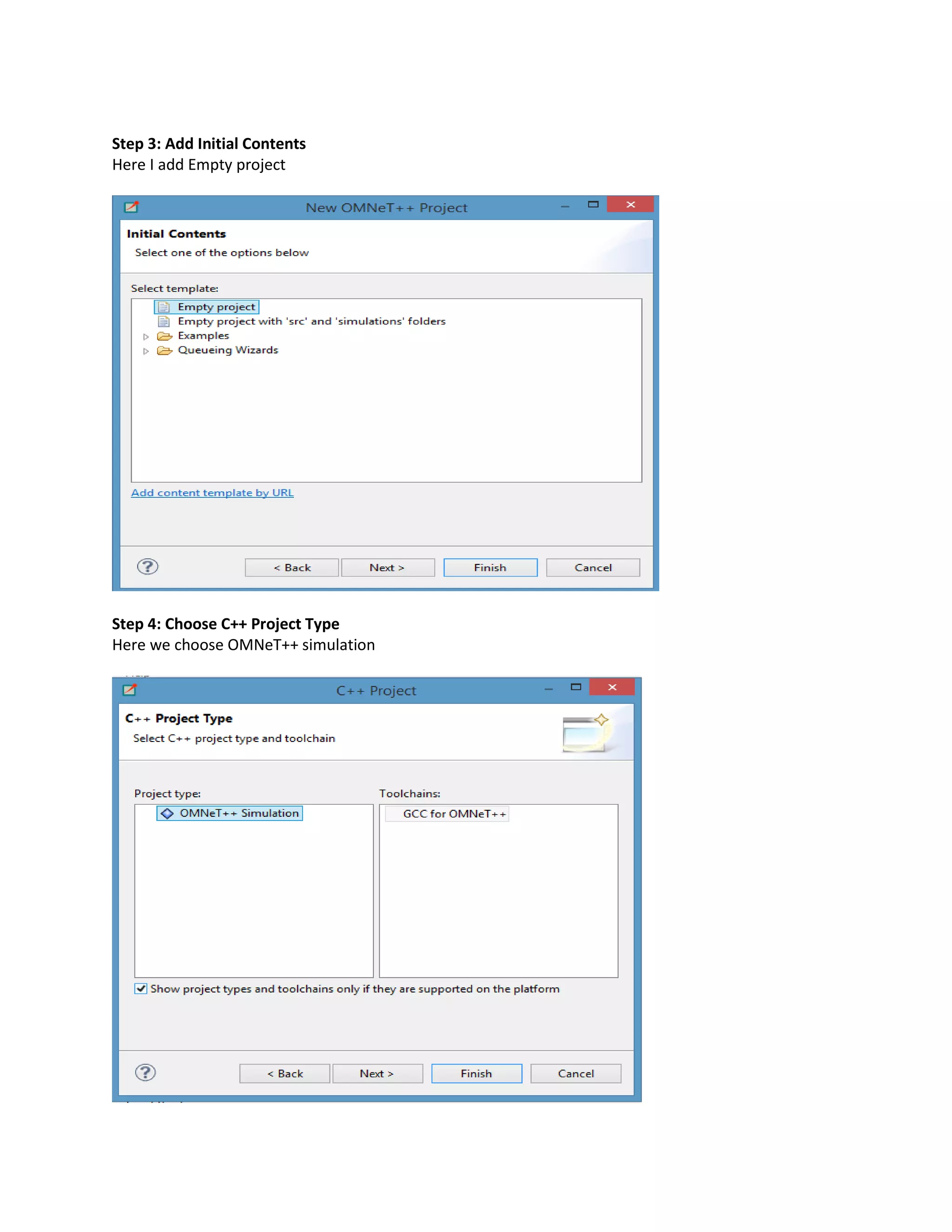
submodules:
node1 : Node;
node2 : Node;
node3 : Node;
………………………
connections:
node1.port++<-->{datarate=100Mbps;}<-->node2.port++;
node2.port++<-->{datarate=100Mbps;}<-->node3.port++;
node3.port++<-->{datarate=100Mbps;}<-->node1.port++;
………………………
}
The double arrow means bi-directional connection
The connection points of the modules are called gates
The port++ notation adds a new gate to the port[] gate vector
Nodes are connected with a channel
Specify the network option in to the configuration like below
[General]
network = Network
.ini (Initialization) Files
Defines the network initialization point with/without some parameters
[General]
network = TicToc1](https://image.slidesharecdn.com/introductiontoomnet-part-1-150907145749-lva1-app6892/75/Introduction-to-OMNeT-6-2048.jpg)
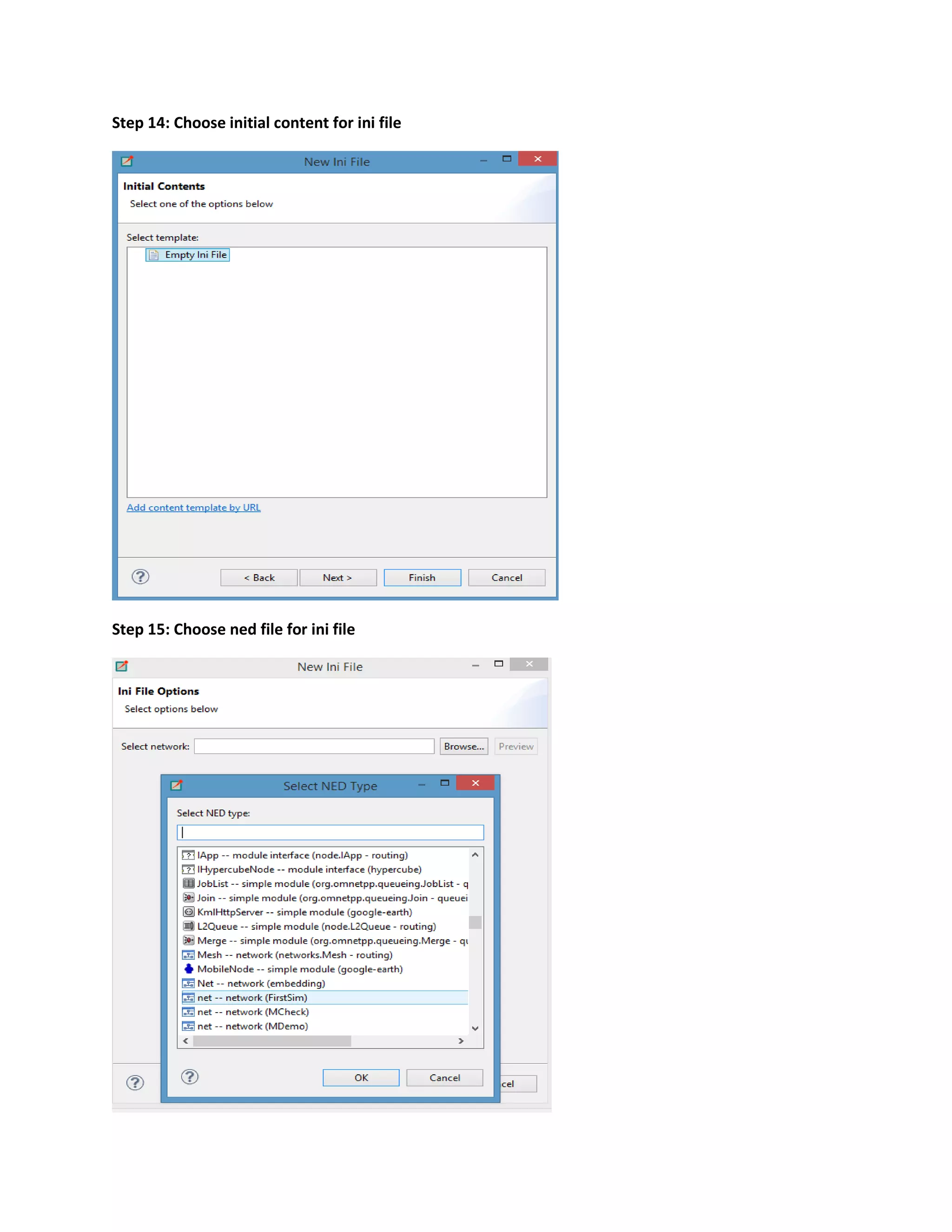
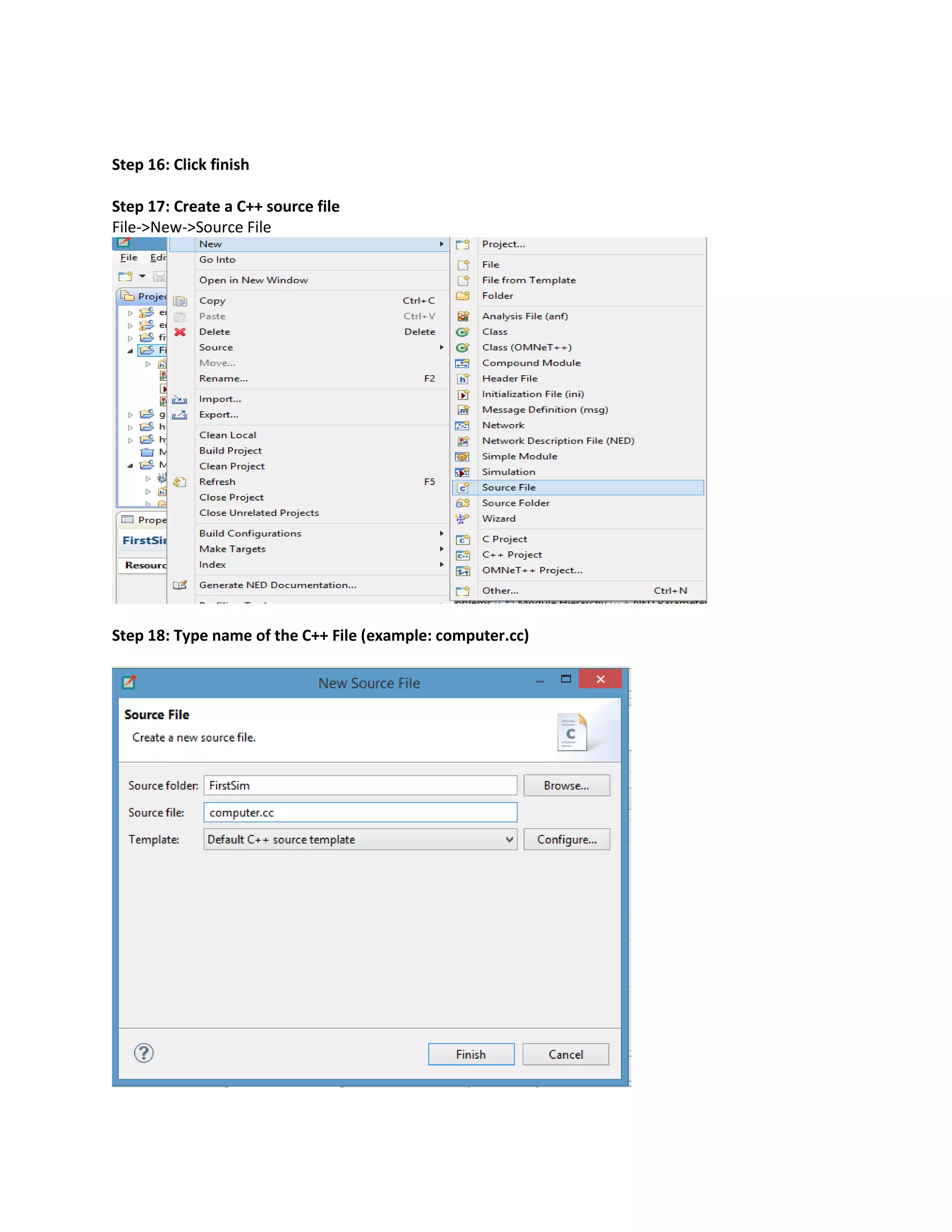
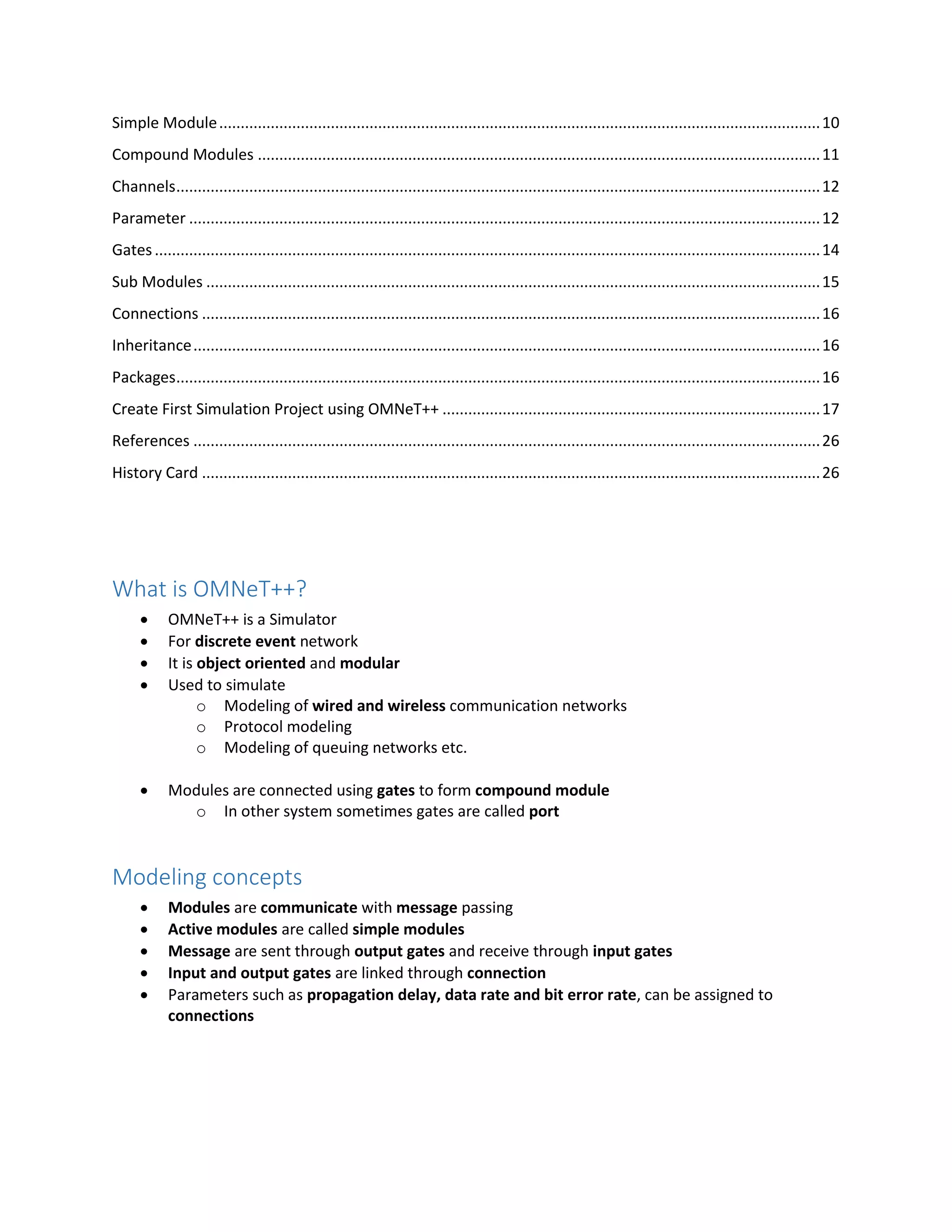
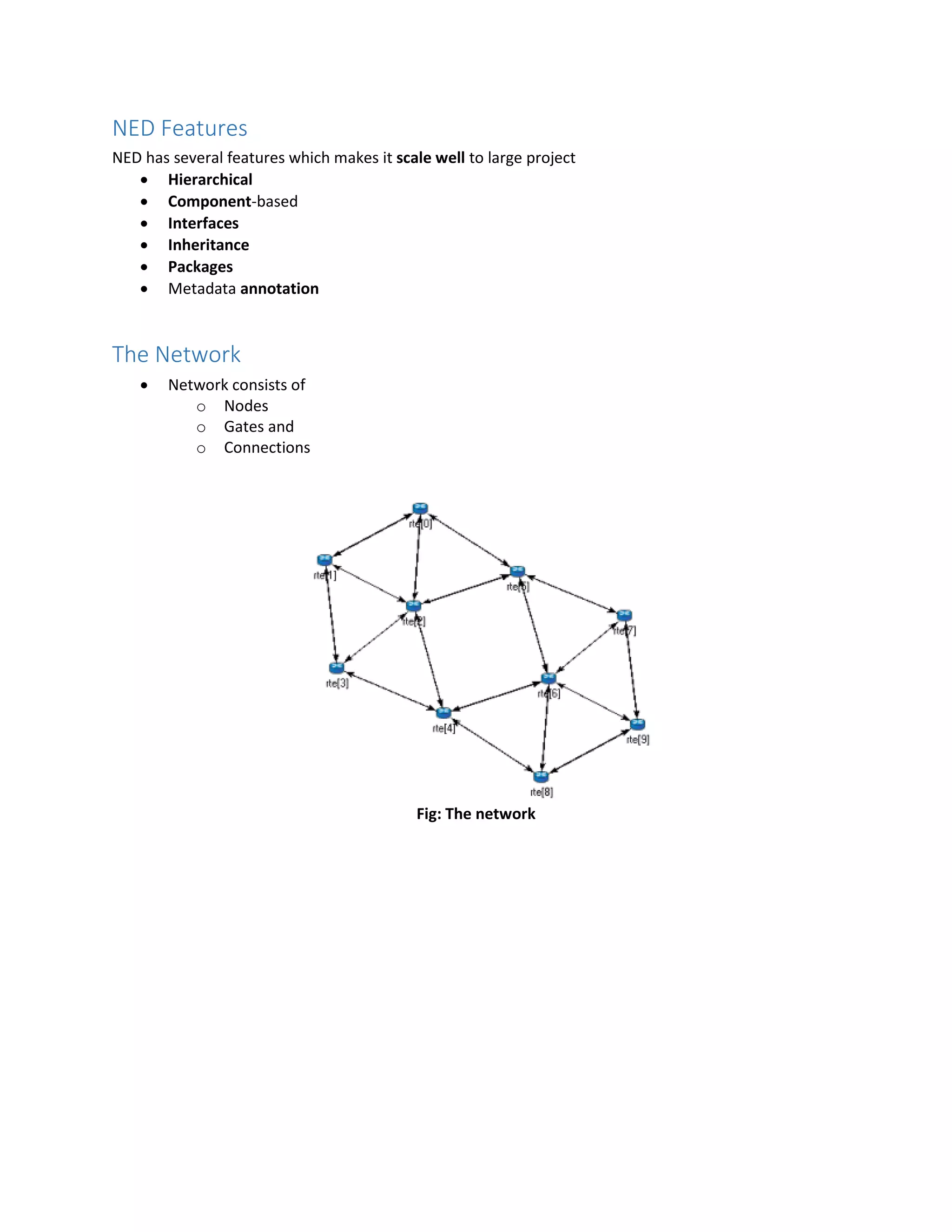
![.cc (C++) Files
Contains class definition and function for modules.
#include <string.h>
#include <omnetpp.h>
class Txc1 : public cSimpleModule
{
protected:
virtual void initialize();
virtual void handleMessage(cMessage *msg);
};
Define_Module(Txc1);
void Txc1::initialize()
{
// Am I Tic or Toc?
if (strcmp("tic", getName()) == 0)
{
cMessage *msg = new cMessage("tictocMsg");
send(msg, "out");
}
}
void Txc1::handleMessage(cMessage *msg)
{
send(msg, "out");
}
Channel
Predefined Channel type
o IdealChannel
o DelayChannel
delay (double with s, ms, us)
diabled (boolean)
o DatarateChannel
delay (double with s, ms, us)
disabled (boolean)
datarate (double with unit as bps, kbps, Mbps, Gbps)
ber (double bit error rate [0,1])
per (double packet error rate [0,1])
One can create new channel type](https://image.slidesharecdn.com/introductiontoomnet-part-1-150907145749-lva1-app6892/75/Introduction-to-OMNeT-7-2048.jpg)
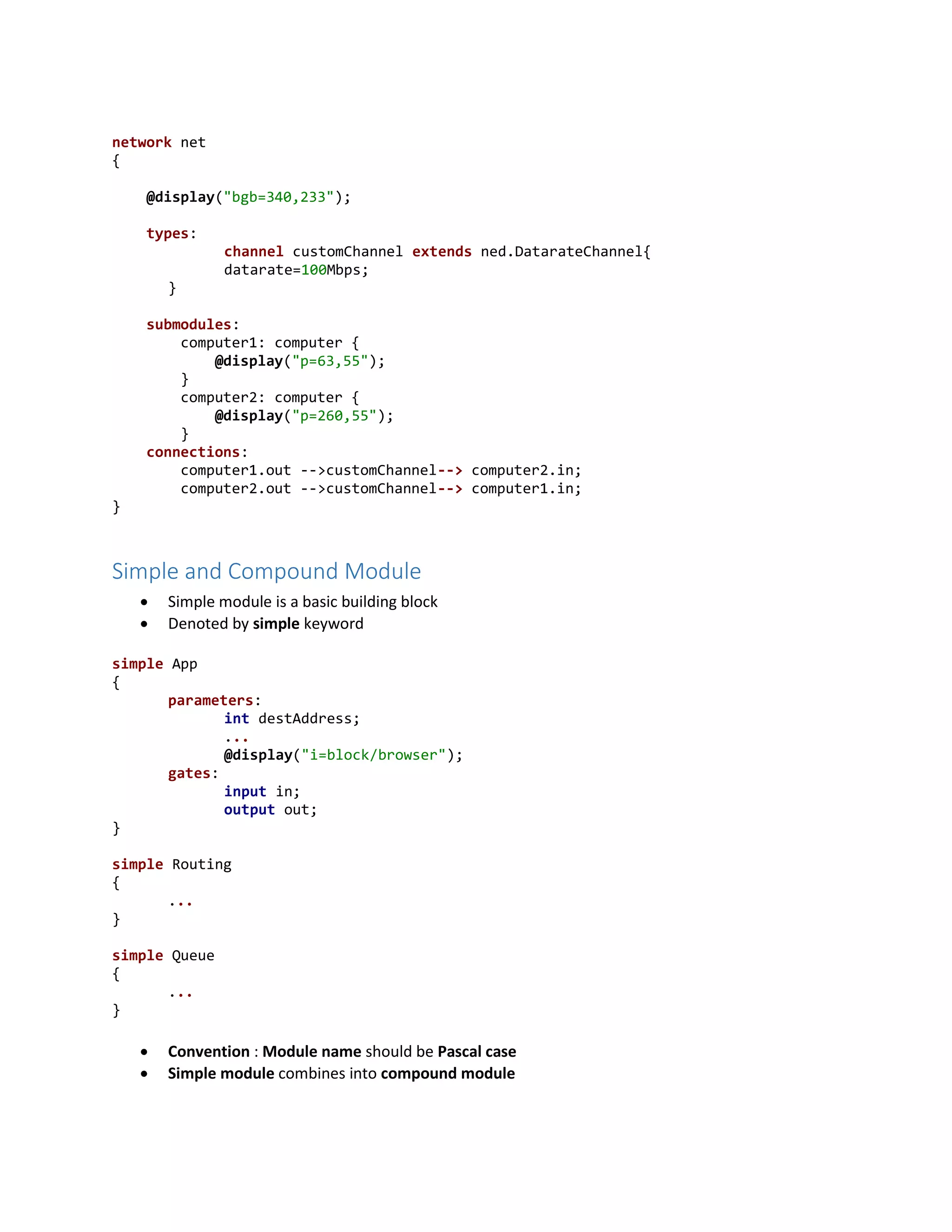
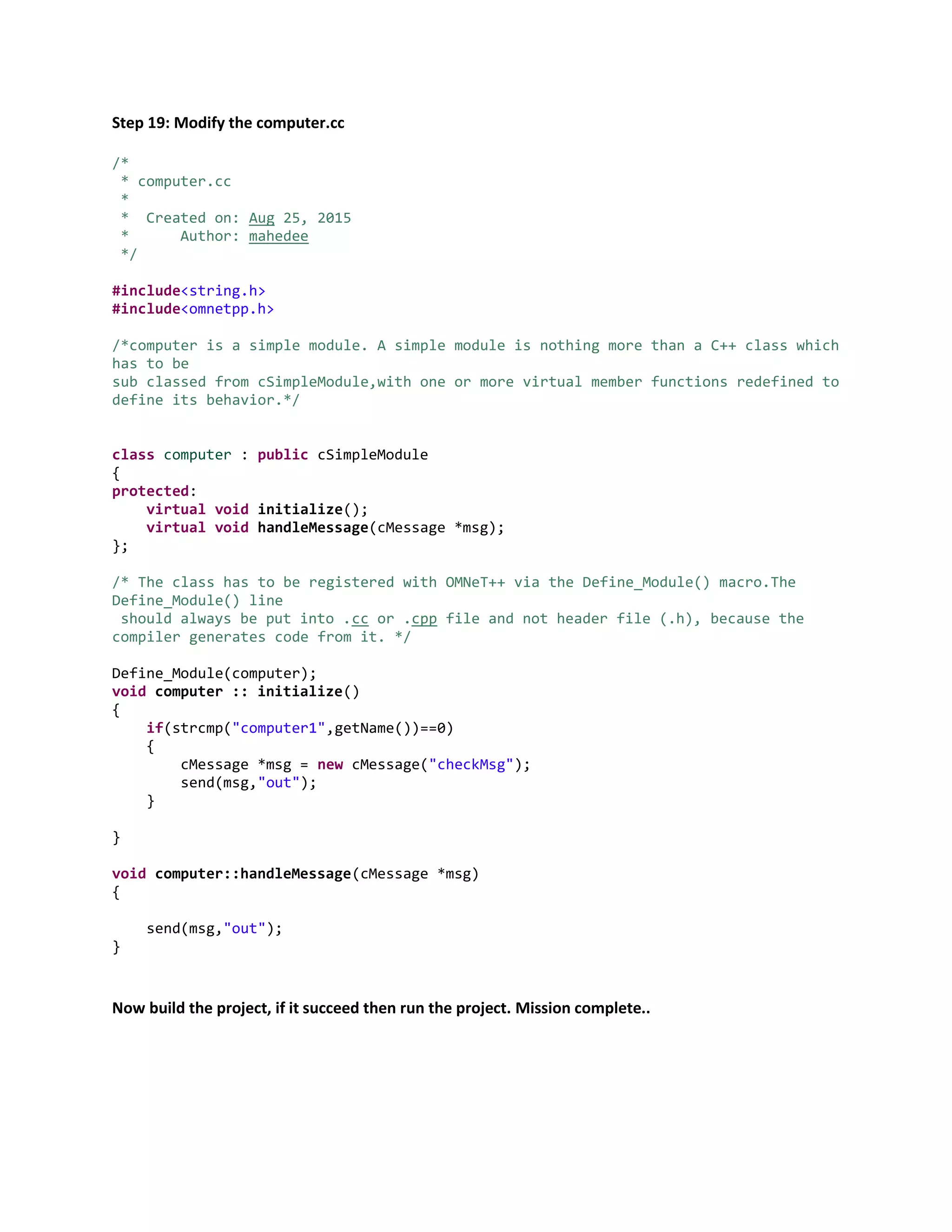
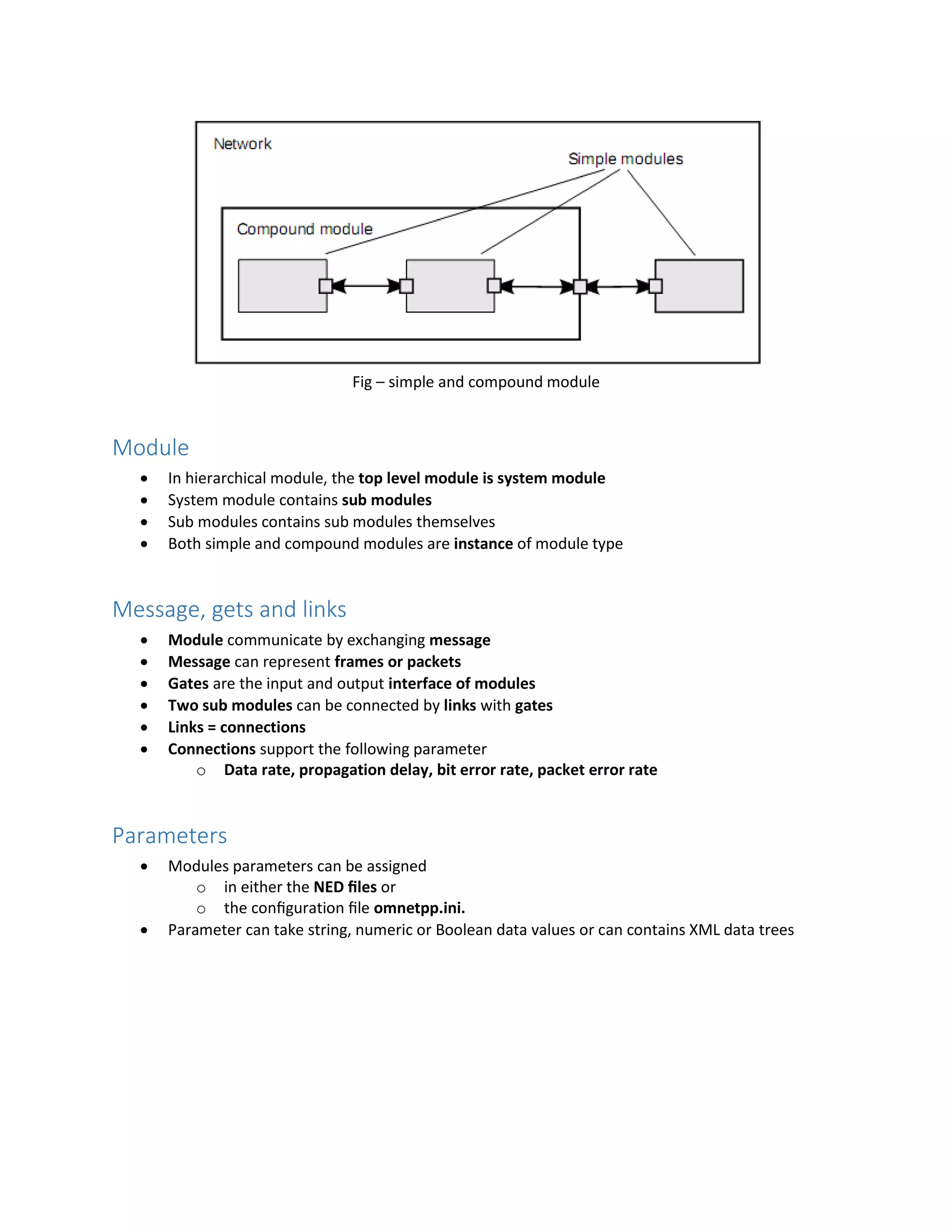
![simple App
{
parameters:
int destAddress;
@display("i=block/browser");
gates:
input in;
output out;
}
simple Routing
{
gates:
input localIn;
output localOut;
}
simple Queue
{
gates:
input in;
output out;
}
module Node
{
parameters:
int address;
@display("i=misc/node_vs,gold");
gates:
inout port[];
submodules:
app: App;
routing: Routing;
queue[sizeof(port)]: Queue;
connections:
routing.localOut --> app.in;
routing.localIn <-- app.out;
for i=0..sizeof(port)-1 {
routing.out[i] --> queue[i].in;
routing.in[i] <-- queue[i].out;
queue[i].line <--> port[i];
}
}](https://image.slidesharecdn.com/introductiontoomnet-part-1-150907145749-lva1-app6892/75/Introduction-to-OMNeT-9-2048.jpg)