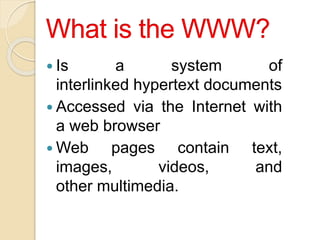
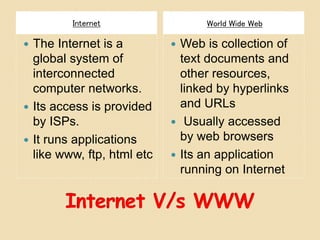
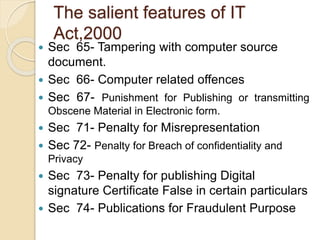
This document provides an introduction to cyber law and intellectual property rights. It defines key terms related to the internet and world wide web such as how the web was invented by Tim Berners-Lee. It also summarizes provisions of the Indian IT Act 2000 related to email validity, e-commerce, and digital signatures. The document further discusses cyber crimes, cyber squatting, and features of the IT Act related to tampering and publishing obscene content. It provides an overview of how digital signatures are used and authenticated under the IT Act.