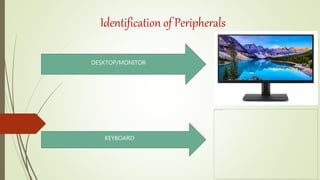
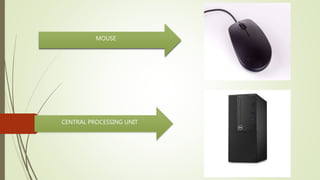
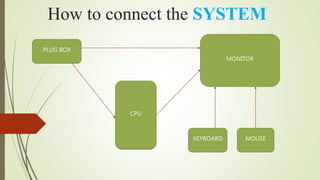
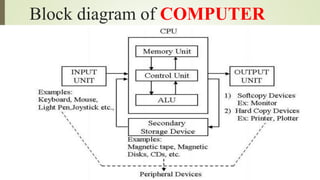
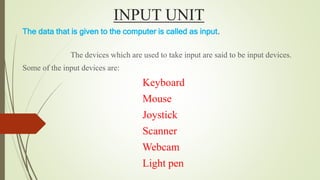
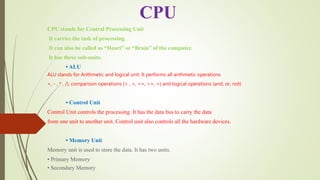
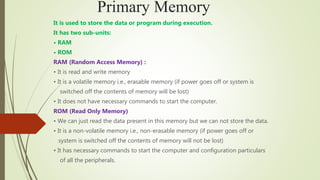
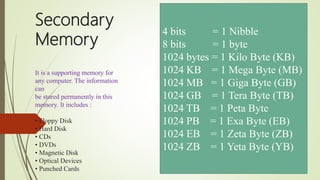
Computer is an electronic device that takes user input, processes it, and produces output. It has a central processing unit (CPU) that includes an arithmetic logic unit (ALU) for calculations, a control unit to direct operations, and memory. Common computer components include a monitor, keyboard, mouse, and peripherals like printers and speakers. The CPU contains the primary memory of RAM for temporary storage and ROM for startup instructions. Secondary memory like hard disks allow for permanent storage of large amounts of data and programs. Input devices provide data to the computer while output devices display or communicate the processed results.