More Related Content
PDF
Cisco Connect Japan 2014: 実践 Cisco ACI (Application Centric Infrastructure) PDF
【Interop Tokyo 2015】 L 03: シスコ技術者認定 CCIE Routing and Switching 取得への道 PDF
【Cisco Data Center Forum 2015】 Cisco ACI 活用例 PDF
データセンター向け高機能スイッチ Cisco Nexus スイッチ ガイド PDF
Cisco Connect Japan 2014: サービス プロバイダー向け SDN/NFV 戦略 PDF
[G-Tech2014講演資料] シスコのSDN最新動向とITインフラエンジニアに求められるスキル - シスコシステムズ合同会社 PDF
Netapp_innovation_2015_Cisco_抜粋修正版 PDF
[G-Tech2015]シスコのデーターセンター向けSDN最前線_シスコシステムズ様[講演資料] What's hot
PDF
ITpro EXPO 2014: Cisco ACI ~データセンター運用の効率化と迅速なアプリケーション展開~ PDF
【Interop tokyo 2014】 Cisco ShowNet Tour 2014 PDF
Cisco Connect Japan 2014:シスコ技術者認定エキスパートレベル CCIE PDF
【Interop tokyo 2014】 IoE 時代を支えるシスコ最新ネットワーク技術とクラウド プラットフォーム PDF
Cisco Connect Japan 2014:企業向け無線 LAN インフラの最新動向と最新ソリューションのご紹介 PDF
PDF
【Interop Tokyo 2016】 SDN/Cloud 仮想環境に、この二つさえあれば、他のファイアウォールはもういらない! PDF
【Interop Tokyo 2015】 DC 5: Cisco ACI とエンタープライズ アプリケーション PDF
Cisco ACI and OpenStack - Group-based Policy (GBP) & OpFlex PDF
Cisco ACI と 仮想化連携 (vSphere / Hyepr-V) PPTX
Cisco Modeling Labs (CML)を使ってネットワークを学ぼう!(基礎編)配布用 PDF
高速で安定した通信を提供するシスコ ワイヤレス LAN ソリューション PDF
PDF
Cisco Connect Japan 2014:高密度環境におけるシスコ無線デザイン ケース スタディ PDF
【Interop Tokyo 2015】 EN_S1: Cisco Catalyst による 無線/有線LANの高速化と管理 PDF
【Interop tokyo 2014】 ShowNetを支えるCiscoのキーテクノロジー PDF
【Interop tokyo 2014】 Cisco SDNの進化とアプリケーションモデル標準化への取り組み PDF
【Interop tokyo 2014】 Cisco SDNの進化とアプリケーション モデル標準化への取り組み PDF
Microsoft tech fielders_cisco_20150126_配布版 PDF
Cisco Connect Japan 2014:シスコ有線 無線統合型アクセス ファースト ステップ ガイド Viewers also liked
PPT
CCNA Security 011- implementing ios-based ips PPT
CCNA Security 010-configuring cisco asa PDF
【Interop Tokyo 2015】 SP 04: シスコ サービス プロバイダー アクセス ポートフォリオ PPTX
PPT
CCNA Security 012- cryptographic systems PPT
CCNA Security 07-Securing the local area network PDF
PDF
PDF
PDF
PDF
PDF
PDF
DOCX
DOCX
PDF
The itil foundation_certificate_syllabus (2) (1) PDF
TXT
PDF
PDF
Similar to 【Interop tokyo 2014】 シスコ技術者認定 プロフェッショナル レベル CCNP Security
PDF
Mk data intensive-onic2021 PDF
PDF
Cisco Connect Japan 2014:Cisco ASA 5500-X 次世代ファイアウォールの機能と、安定導入・運用方法 PDF
【Interop tokyo 2014】 ビッグデータを活用し、被害を予見! シスコの新たなセキュリティ運用モデル KEY
PDF
Cisco E メール セキュリティ アプライアンス(ESA) PDF
PDF
【Cisco Data Center Forum 2015】 データ センター ネットワークの動向と Cisco ACI の戦略 PDF
ITpro EXPO 2014: Wi-Fi位置情報と超高速データベースSAP HANA連携ソリューション PDF
Cisco Connect Japan 2014: シスコ ビデオ テクノロジー最前線 PDF
Cisco Connect Japan 2014: シスコ ビデオ テクノロジー最前線 PDF
【Interop tokyo 2014】 “FlexPod” Cisco ACIとUCS Directorにより実現される自動化 クラウド基盤 PDF
【Interop tokyo 2014】 “FlexPod” Cisco ACI とUCS Director により 実現される自動化 クラウド基盤 PDF
Mk application aware-hicn PDF
Mk onic data-intensive-public PDF
Mk onic data-intensive-public PDF
CSCJ_Webcast_20180626_ACI.pdf PDF
Segment Routing @ SDN Japan 2013 PDF
Mk state in-programming-01 PDF
Network Programmability and the statefulness/transactionality More from シスコシステムズ合同会社
PDF
シスコ装置を使い倒す!組込み機能による可視化からセキュリティ強化 PDF
【Interop Tokyo 2016】 CCNA RS 改訂ポイントと BOOTCAMP トレーニング PDF
【Interop Tokyo 2016】 Seminar - EA-08 : シスコ データセンターSDN戦略、3本の矢 PDF
【Interop Tokyo 2016】 Seminar - EA-05 : 「Cisco の先進コア ネットワーク ソリューション」 Shownet 2... PPTX
Cisco Modeling Labs (CML)を使ってネットワークを学ぼう!(応用編) PPTX
Cisco Modeling Labs (CML)を使ってネットワークを学ぼう!(DevNet編) PDF
【Interop Tokyo 2016】 Seminar - EA-18 : 「Cisco の先進セキュリティ ソリューション」 Shownet 2016... PDF
【Interop Tokyo 2016】 次世代サービス チェイニング NSH (Network Service Header) PDF
【Interop Tokyo 2016】 LAN/WAN向けSDNコントローラ APIC-EMのご紹介 PDF
【Interop Tokyo 2016】 Cisco Advanced Malware Protection(AMP)/ レトロ スペクティブで見えてくる... PDF
【Interop Tokyo 2016】 ネットワーク モデリングと自動制御 PDF
【Interop Tokyo 2016】 初心者でもわかるCisco SDNの概要 PDF
【Interop Tokyo 2016】 世界最大級の脅威情報と自社ネットワークの脅威可視化 PDF
【Interop Tokyo 2016】 Cisco Jasper Control Center PDF
【Interop Tokyo 2016】 ShowNet - SSS-17 : ShowNet 2016 を支える�シスコの最新テクノロジー PDF
【Interop Tokyo 2016】 SP ネットワークの変革を支える技術イノベーション PDF
【Interop Tokyo 2016】 Seminar - EA-09 : エンタープライズ ワイヤレス:デジタル世界のための信頼性と汎用性に優れたアクセス PDF
【Interop Tokyo 2016】 新たなルーティング パラダイム セグメントルーティング PDF
【Interop Tokyo 2016】 Seminar - EA-14 : シスコ スイッチが標的型攻撃を食い止める ~新しい内部対策ソリューション「C... PDF
【Interop Tokyo 2016】 ビッグデータ解析手法による脅威分析サービス 【Interop tokyo 2014】 シスコ技術者認定 プロフェッショナル レベル CCNP Security
- 1.
- 2.
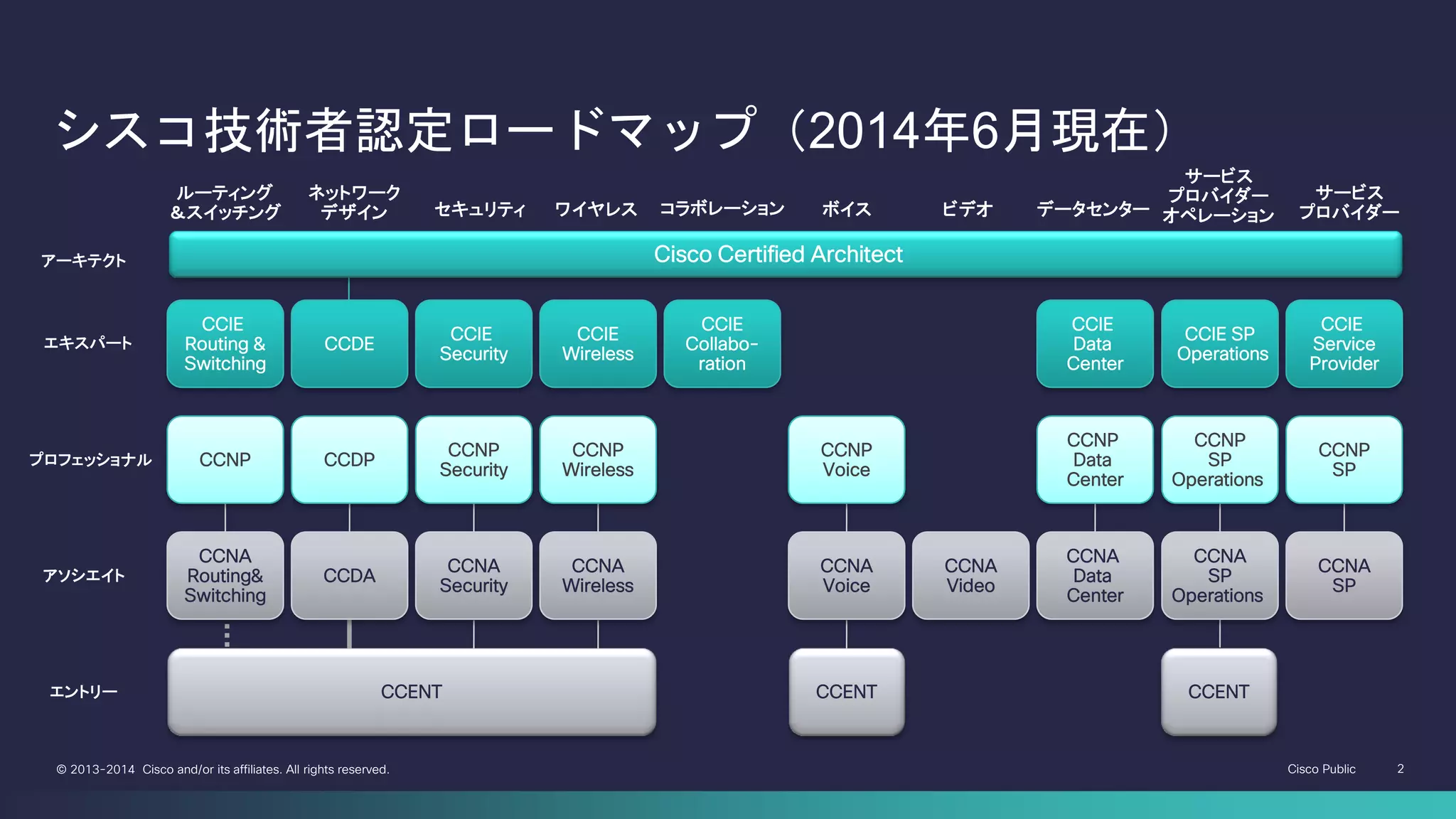
Cisco Public 2©2013-2014 Cisco and/or its affiliates. All rights reserved.
ルーティング
&スイッチング
Cisco Certified Architect
CCIE
Routing &
Switching
CCNP
セキュリティ
CCIE
Security
CCNP
Security
CCNA
Security
ボイス
CCNP
Voice
CCNA
Voice
ワイヤレス
CCIE
Wireless
CCNP
Wireless
CCNA
Wireless
サービス
プロバイダー
CCIE
Service
Provider
CCNP
SP
CCIE SP
Operations
CCNP
SP
Operations
サービス
プロバイダー
オペレーション
CCNA
SP
Operations
CCNA
SP
CCIE
Data
Center
ネットワーク
デザイン
CCDE
CCDP
CCENT
データセンター
CCDA
エキスパート
アーキテクト
アソシエイト
プロフェッショナル
エントリー
CCNP
Data
Center
CCNA
Data
Center
ビデオ
CCNA
Video
CCENT
CCIE
Collabo-
ration
CCNA
Routing&
Switching
コラボレーション
CCENT
シスコ技術者認定ロードマップ(2014年6月現在)
- 3.
Cisco Public 3©2013-2014 Cisco and/or its affiliates. All rights reserved.
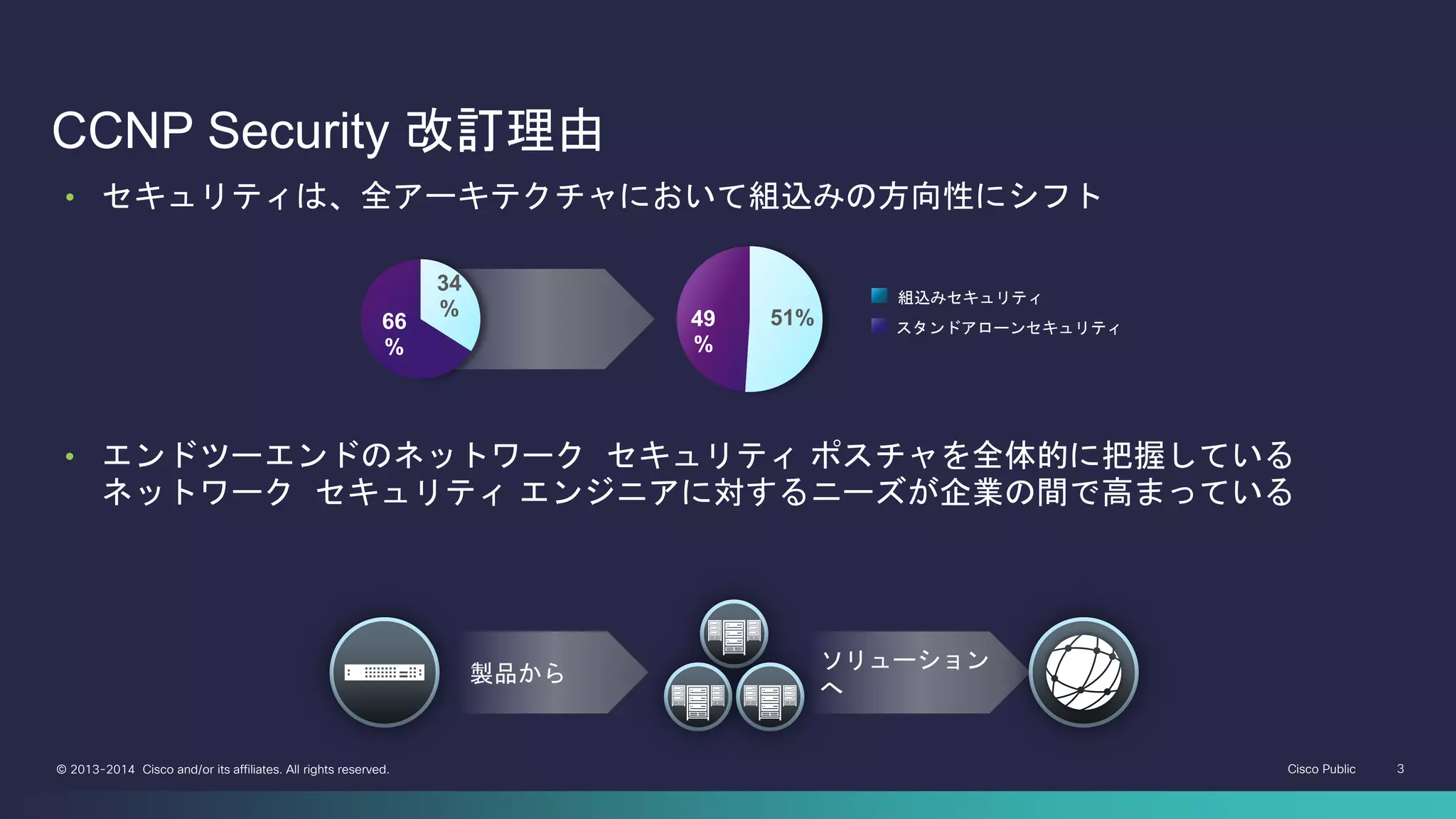
CCNP Security 改訂理由
製品から
ソリューション
へ
• セキュリティは、全アーキテクチャにおいて組込みの方向性にシフト
組込みセキュリティ
スタンドアローンセキュリティ
34
%
66
%
51%49
%
• エンドツーエンドのネットワーク セキュリティ ポスチャを全体的に把握している
ネットワーク セキュリティ エンジニアに対するニーズが企業の間で高まっている
- 4.
Cisco Public 4©2013-2014 Cisco and/or its affiliates. All rights reserved.
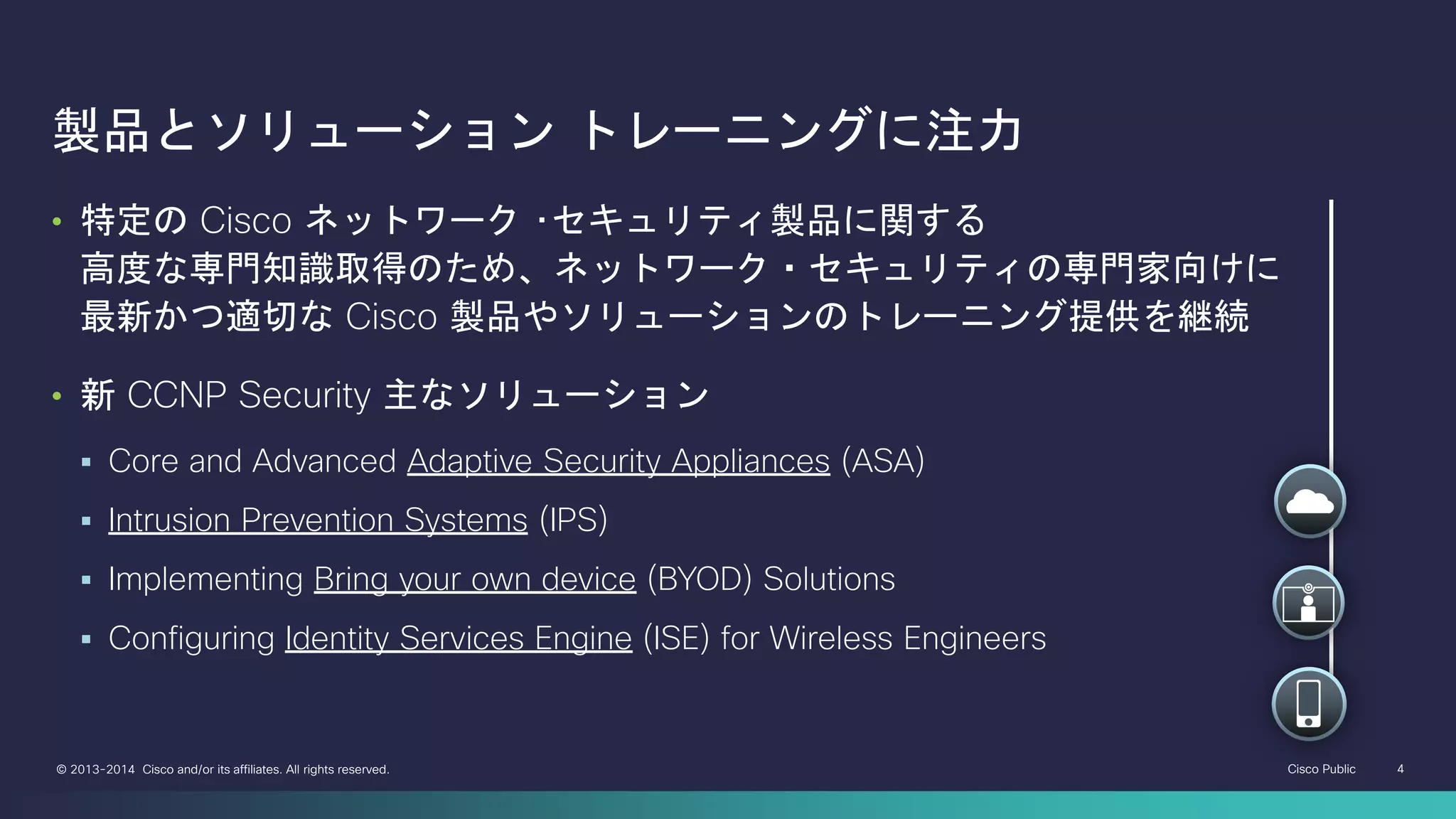
製品とソリューション トレーニングに注力
• 特定の Cisco ネットワーク ・セキュリティ製品に関する
高度な専門知識取得のため、ネットワーク・セキュリティの専門家向けに
最新かつ適切な Cisco 製品やソリューションのトレーニング提供を継続
• 新 CCNP Security 主なソリューション
Core and Advanced Adaptive Security Appliances (ASA)
Intrusion Prevention Systems (IPS)
Implementing Bring your own device (BYOD) Solutions
Configuring Identity Services Engine (ISE) for Wireless Engineers
- 5.
Cisco Public 5©2013-2014 Cisco and/or its affiliates. All rights reserved.
Implementing Cisco Edge Network Security
Solutions
Implementing Cisco Threat Control Solutions
Implementing Cisco Secure Access Solutions
Implementing Cisco Secure Mobility
Solutions
CCNP Security 関連4 試験
CCNP Security
マイグレーション ツール
http://cs.co/9004i4BQ
- 6.
Cisco Public 6©2013-2014 Cisco and/or its affiliates. All rights reserved.
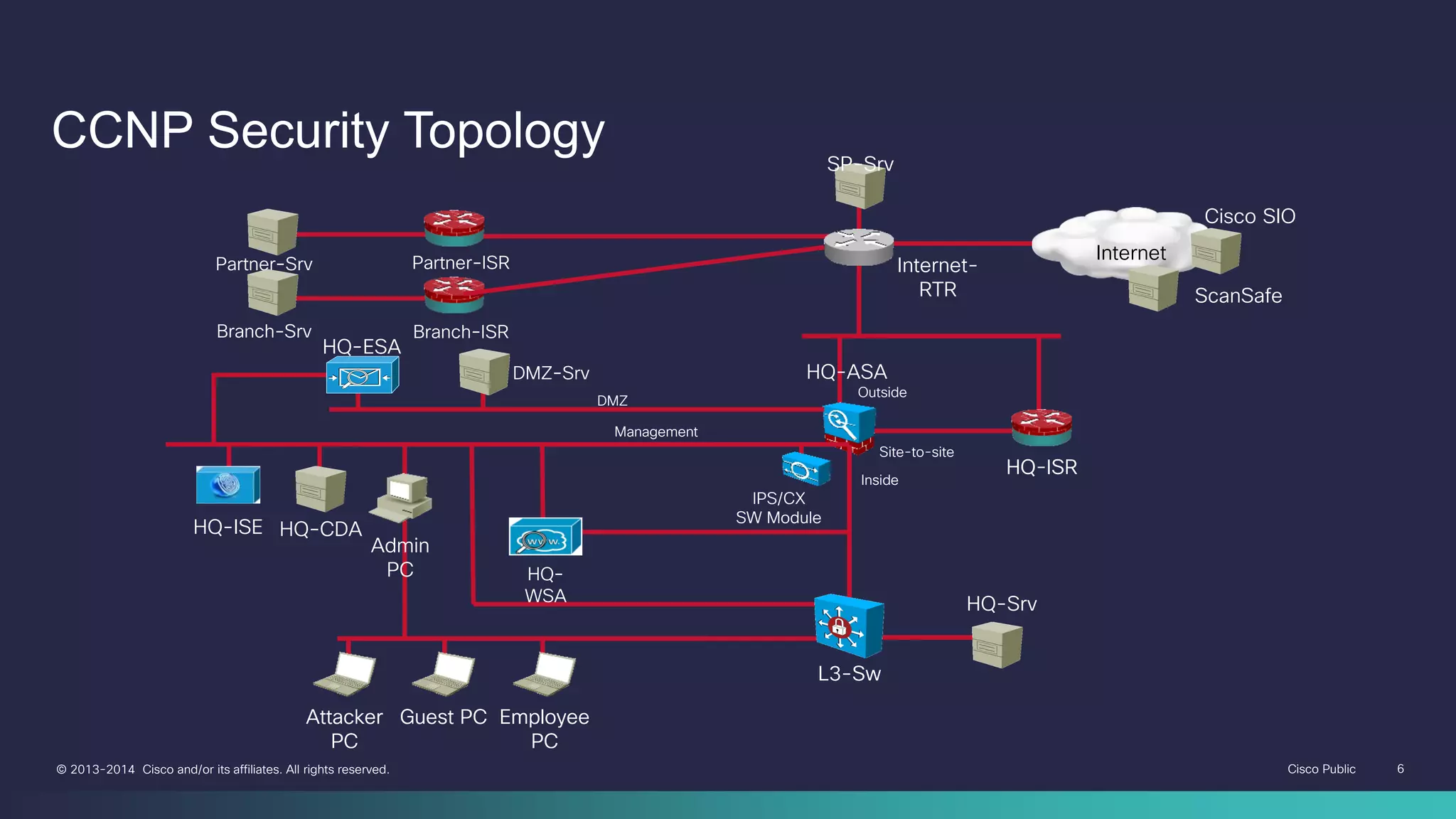
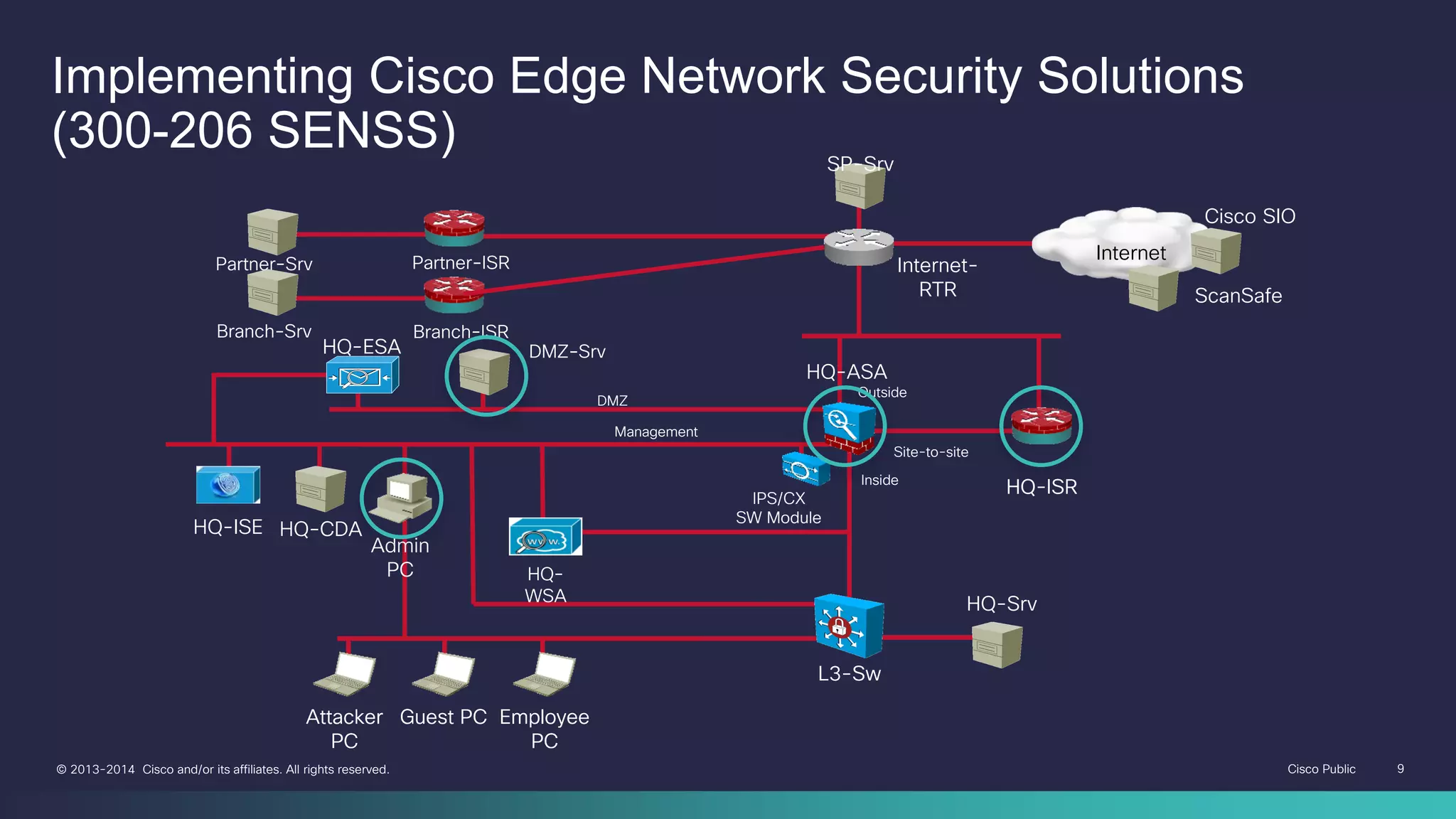
CCNP Security Topology
HQ-ASA
HQ-ISR
L3-Sw
HQ-Srv
Attacker
PC
Guest PC Employee
PC
DMZ
Management
Outside
Inside
Site-to-site
Partner-ISR
Branch-ISR
Partner-Srv
Branch-Srv
HQ-ISE
Admin
PC
HQ-CDA
HQ-ESA
HQ-
WSA
DMZ-Srv
HQ-ISR
IPS/CX
SW Module
L3-Sw
Attacker
PC
Guest PC Employee
PC
SP-Srv
Internet-
RTR
Internet
Cisco SIO
ScanSafe
- 7.
Cisco Public 7©2013-2014 Cisco and/or its affiliates. All rights reserved.
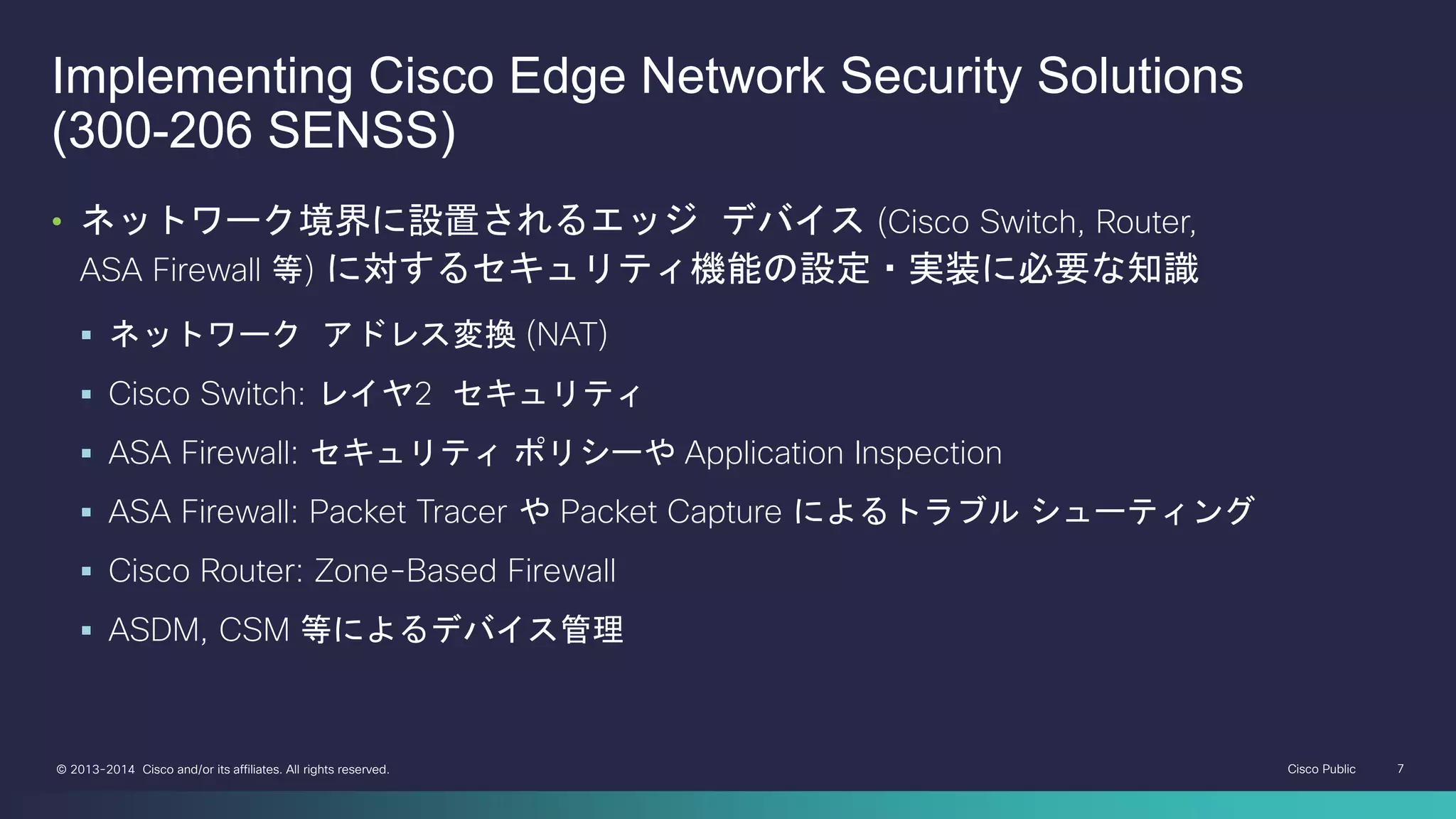
Implementing Cisco Edge Network Security Solutions
(300-206 SENSS)
• ネットワーク境界に設置されるエッジ デバイス (Cisco Switch, Router,
ASA Firewall 等) に対するセキュリティ機能の設定・実装に必要な知識
ネットワーク アドレス変換 (NAT)
Cisco Switch: レイヤ2 セキュリティ
ASA Firewall: セキュリティ ポリシーや Application Inspection
ASA Firewall: Packet Tracer や Packet Capture によるトラブル シューティング
Cisco Router: Zone-Based Firewall
ASDM, CSM 等によるデバイス管理
- 8.
Cisco Public 8©2013-2014 Cisco and/or its affiliates. All rights reserved.
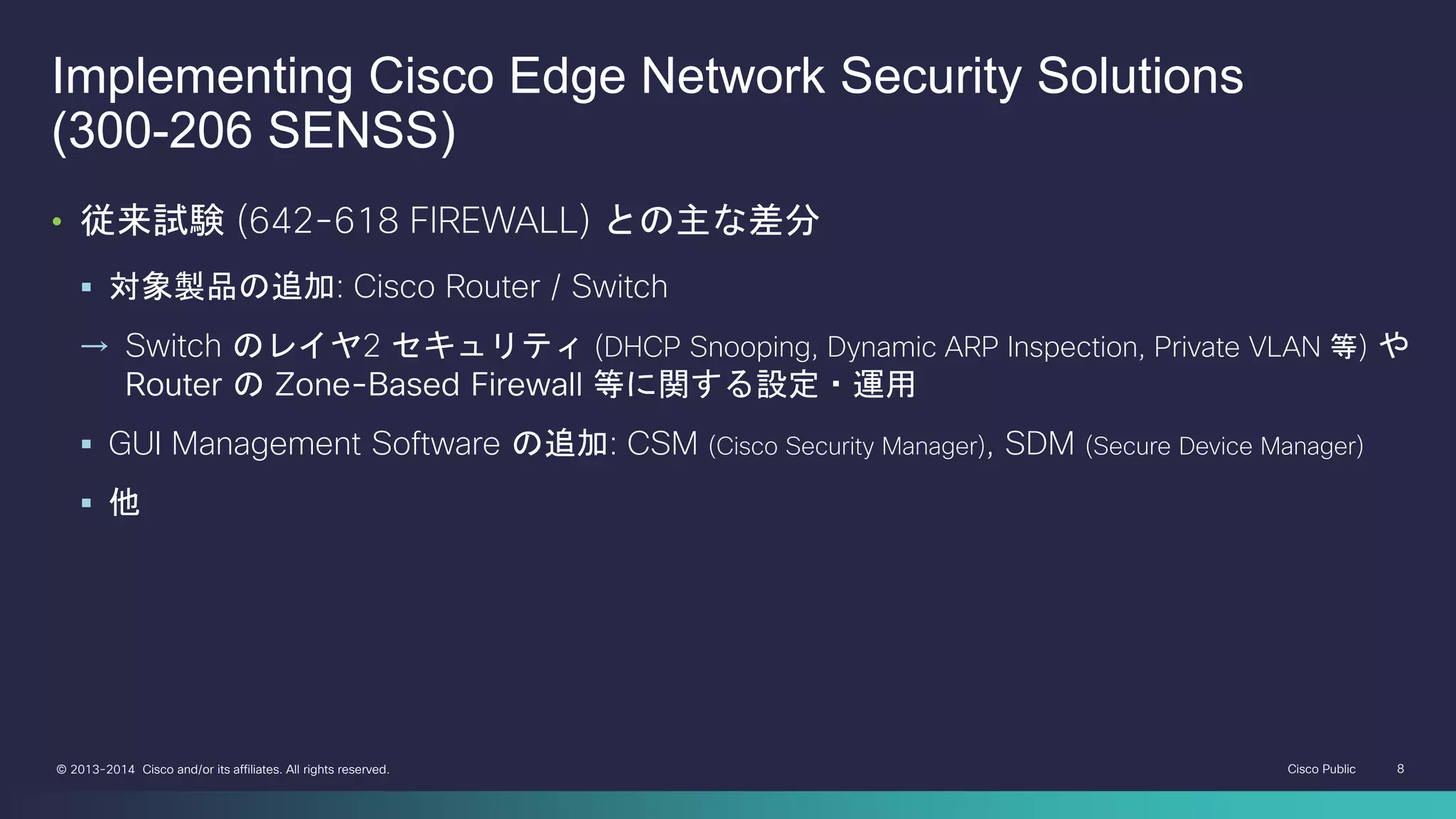
Implementing Cisco Edge Network Security Solutions
(300-206 SENSS)
• 従来試験 (642-618 FIREWALL) との主な差分
対象製品の追加: Cisco Router / Switch
→ Switch のレイヤ2 セキュリティ (DHCP Snooping, Dynamic ARP Inspection, Private VLAN 等) や
Router の Zone-Based Firewall 等に関する設定・運用
GUI Management Software の追加: CSM (Cisco Security Manager), SDM (Secure Device Manager)
他
- 9.
Cisco Public 9©2013-2014 Cisco and/or its affiliates. All rights reserved.
HQ-ASA
HQ-ISR
L3-Sw
HQ-Srv
Attacker
PC
Guest PC Employee
PC
DMZ
Management
Outside
Inside
Site-to-site
Partner-ISR
Branch-ISR
Partner-Srv
Branch-Srv
HQ-ISE
Admin
PC
HQ-CDA
HQ-ESA
HQ-
WSA
DMZ-Srv
HQ-ISRIPS/CX
SW Module
L3-Sw
Attacker
PC
Guest PC Employee
PC
SP-Srv
Internet-
RTR
Internet
Cisco SIO
ScanSafe
Implementing Cisco Edge Network Security Solutions
(300-206 SENSS)
- 10.
Cisco Public 10©2013-2014 Cisco and/or its affiliates. All rights reserved.
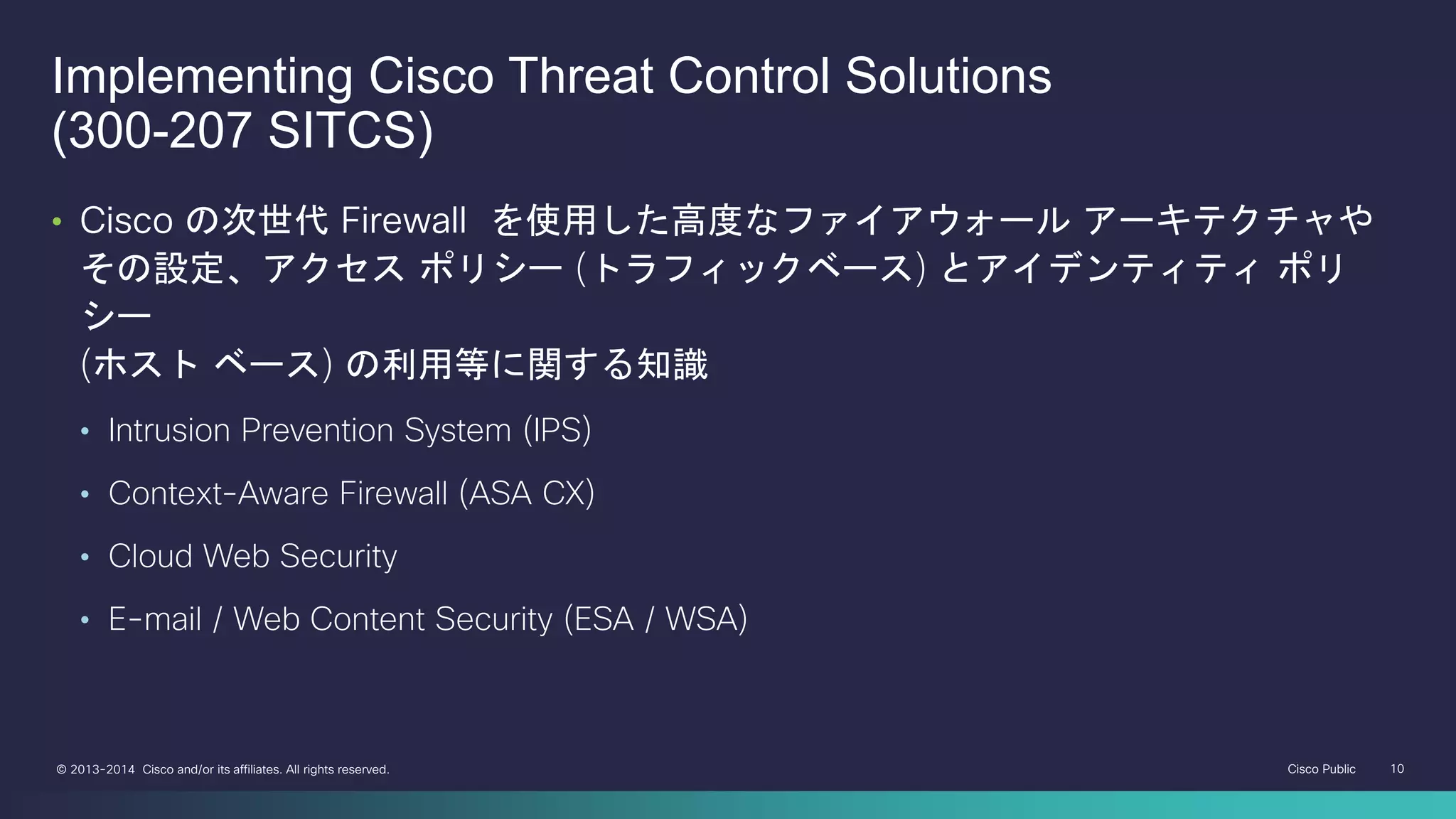
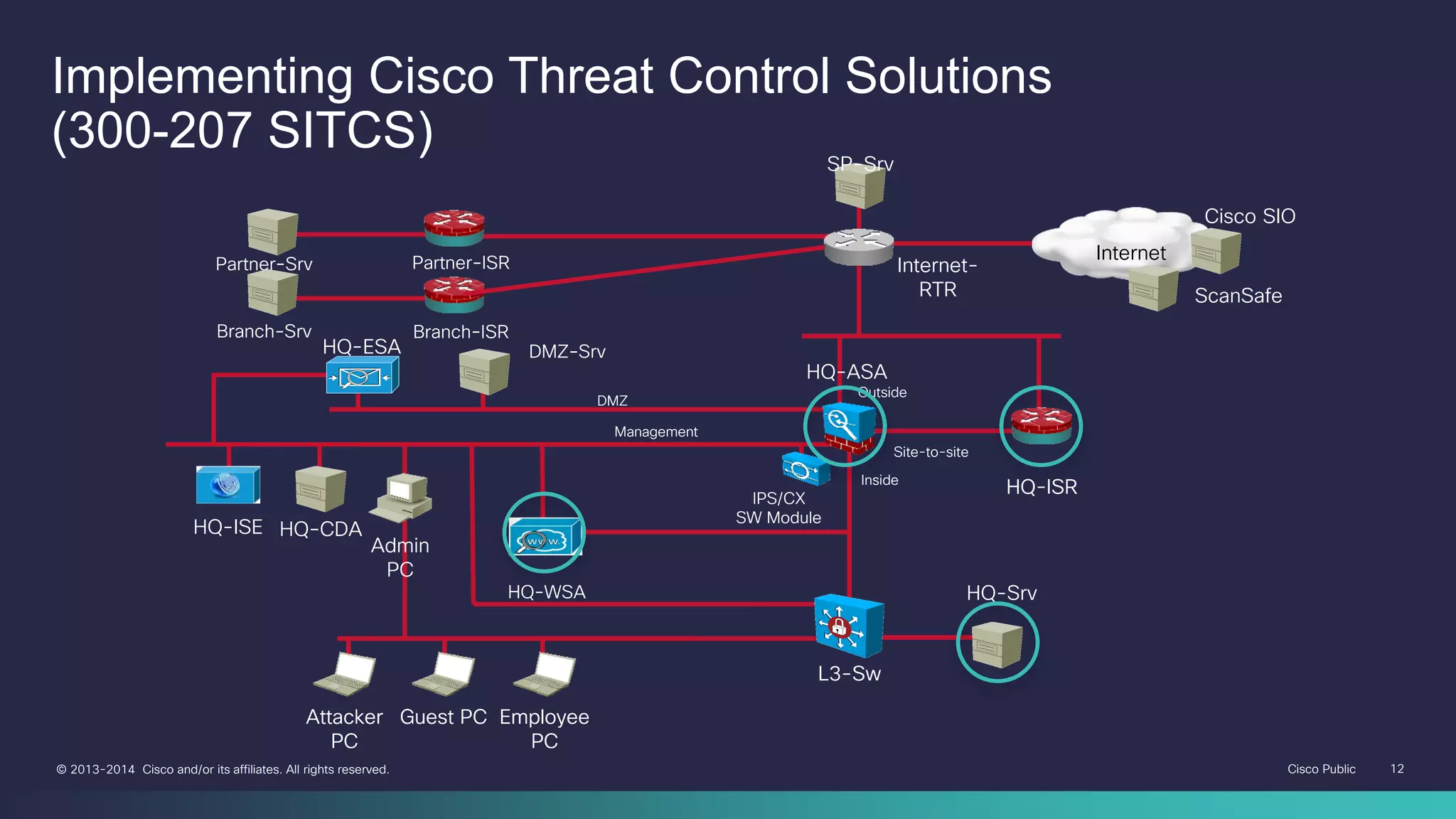
Implementing Cisco Threat Control Solutions
(300-207 SITCS)
• Cisco の次世代 Firewall を使用した高度なファイアウォール アーキテクチャや
その設定、アクセス ポリシー (トラフィックベース) とアイデンティティ ポリ
シー
(ホスト ベース) の利用等に関する知識
• Intrusion Prevention System (IPS)
• Context-Aware Firewall (ASA CX)
• Cloud Web Security
• E-mail / Web Content Security (ESA / WSA)
- 11.
Cisco Public 11©2013-2014 Cisco and/or its affiliates. All rights reserved.
Implementing Cisco Threat Control Solutions
(300-207 SITCS)
• 従来試験 (642-627 IPS) との主な差分
• 対象製品の追加: ASA CX, Cloud Web Security, ESA / WSA
→ Web や E-mail の Contents を監視する製品群の機能・実装に関する知識が必要
• 他
- 12.
Cisco Public 12©2013-2014 Cisco and/or its affiliates. All rights reserved.
HQ-ASA
HQ-ISR
L3-Sw
HQ-Srv
Attacker
PC
Guest PC Employee
PC
DMZ
Management
Outside
Inside
Site-to-site
Partner-ISR
Branch-ISR
Partner-Srv
Branch-Srv
HQ-ISE
Admin
PC
HQ-CDA
HQ-ESA
HQ-WSA
DMZ-Srv
HQ-ISRIPS/CX
SW Module
L3-Sw
Attacker
PC
Guest PC Employee
PC
SP-Srv
Internet-
RTR
Internet
Cisco SIO
ScanSafe
Implementing Cisco Threat Control Solutions
(300-207 SITCS)
- 13.
Cisco Public 13©2013-2014 Cisco and/or its affiliates. All rights reserved.
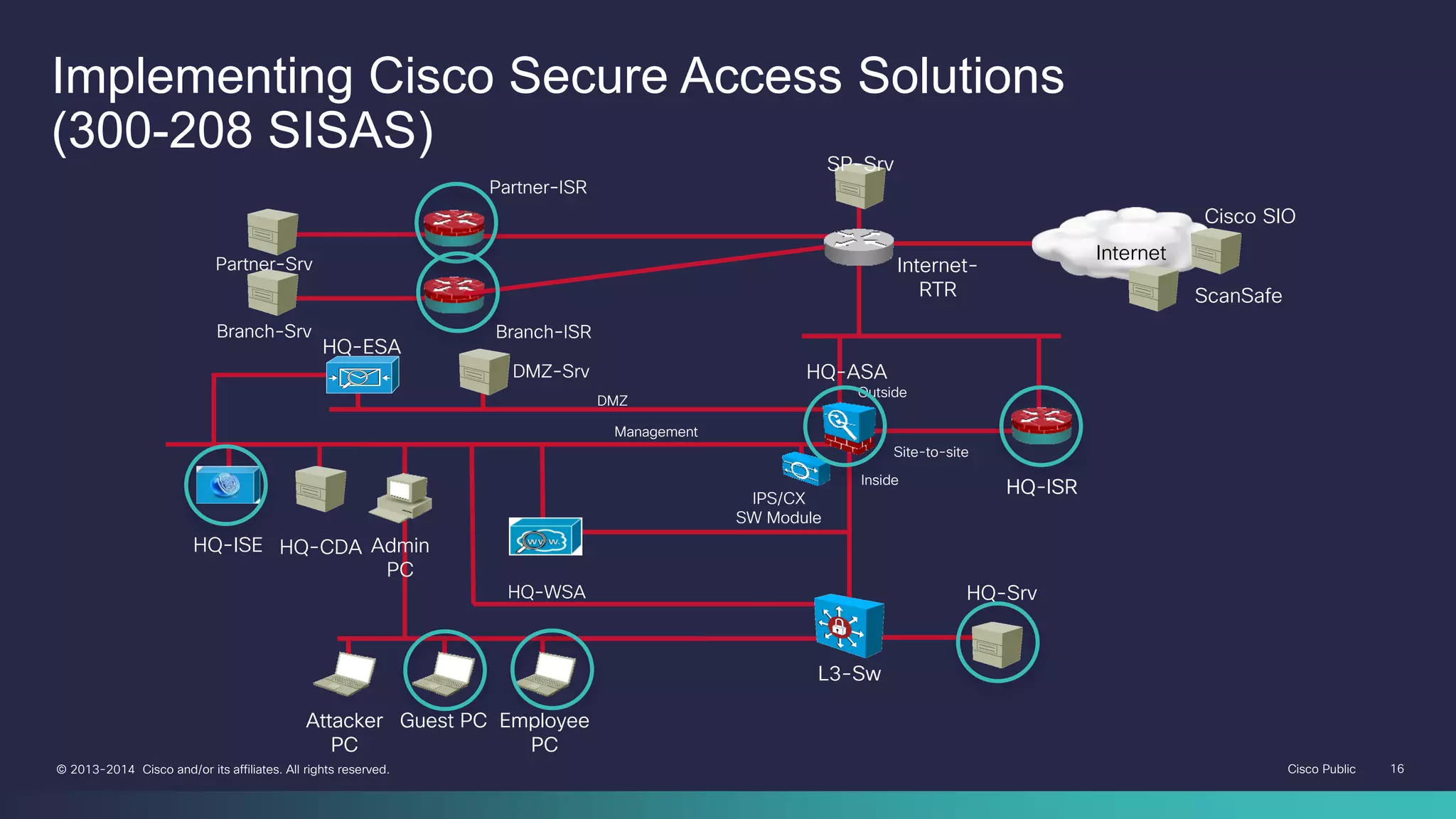
Implementing Cisco Secure Access Solutions
(300-208 SISAS)
• IEEE 802.1X や Cisco TrustSec を利用したセキュアなアクセスを実現するための
コンポーネントやアーキテクチャに関する知識
Cisco Identity Services Engine (ISE) の製品概要
ISE のポスチャ ポリシー・プロファイリング ポリシー等を利用した
Bring your own device (BYOD) の基本概念
AAA の基本プロトコル: RADIUS, TACACS+ 等
Identity Management: LDAP, Active Directory, PKI, ワンタイム パスワード等
Switch での認証: IEEE 802.1X, MAB (MAC Authentication Bypass), Web 認証等
- 14.
Cisco Public 14©2013-2014 Cisco and/or its affiliates. All rights reserved.
Implementing Cisco Secure Access Solutions
(300-208 SISAS)
• 従来試験 (642-637 SECURE) との主な差分
Cisco Identity Services Engine (ISE) を中心として大幅に刷新
(従来の内容の大半は SENSS へ)
AAA (Authentication, Authorization, Accounting) の運用に則した知識が必要
Switch と ISE を組み合わせた認証ソリューションとアーキテクチャ:
IEEE 802.1X, MAB (MAC Authentication Bypass), Web 認証等
他
- 15.
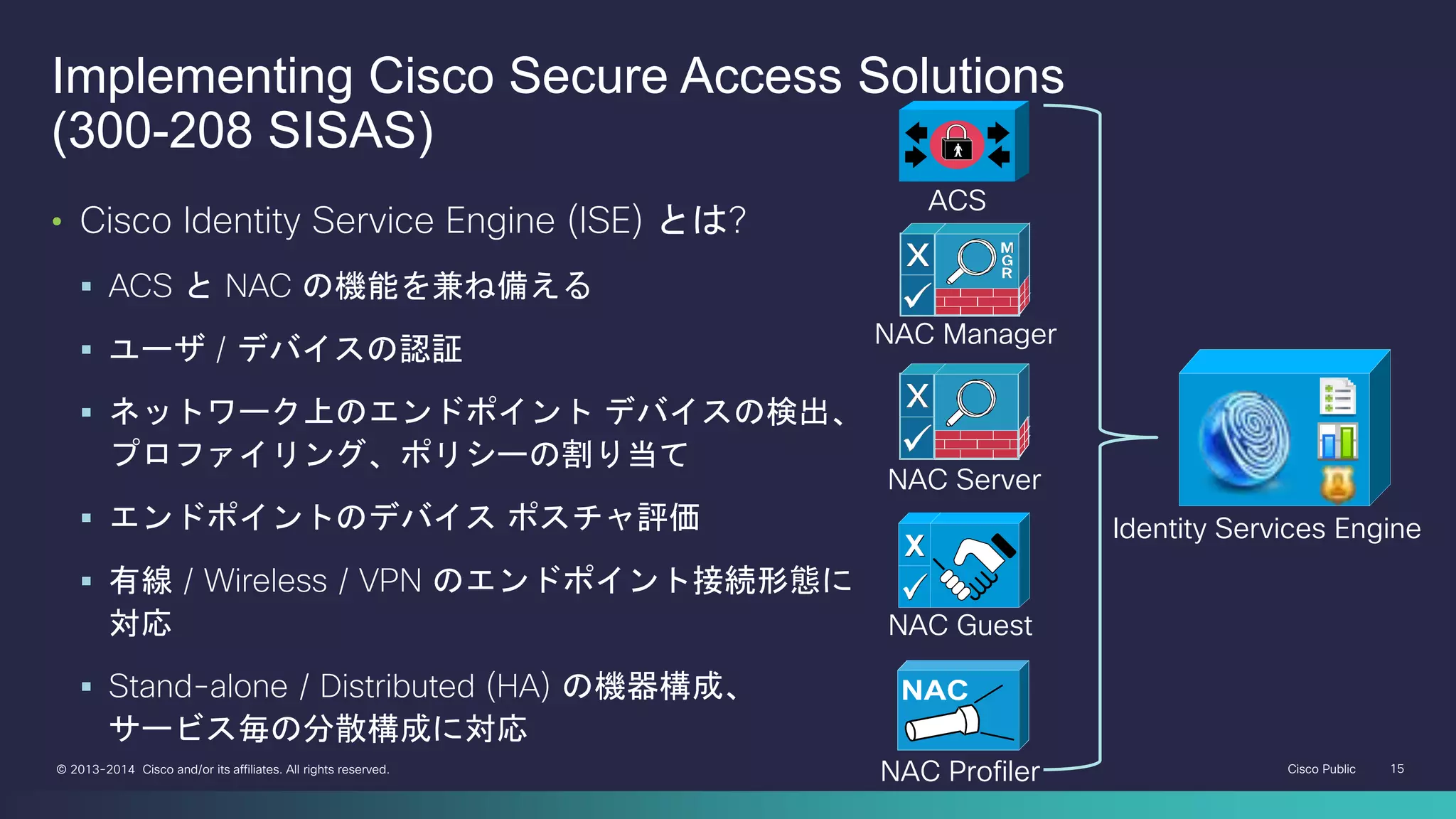
Cisco Public 15©2013-2014 Cisco and/or its affiliates. All rights reserved.
Implementing Cisco Secure Access Solutions
(300-208 SISAS)
• Cisco Identity Service Engine (ISE) とは?
ACS と NAC の機能を兼ね備える
ユーザ / デバイスの認証
ネットワーク上のエンドポイント デバイスの検出、
プロファイリング、ポリシーの割り当て
エンドポイントのデバイス ポスチャ評価
有線 / Wireless / VPN のエンドポイント接続形態に
対応
Stand-alone / Distributed (HA) の機器構成、
サービス毎の分散構成に対応
ACS
NAC Guest
NAC Profiler
NAC Manager
NAC Server
Identity Services Engine
- 16.
Cisco Public 16©2013-2014 Cisco and/or its affiliates. All rights reserved.
HQ-ASA
HQ-ISR
L3-Sw
HQ-Srv
Attacker
PC
Guest PC Employee
PC
DMZ
Management
Outside
Inside
Site-to-site
Partner-ISR
Branch-ISR
Partner-Srv
Branch-Srv
HQ-ISE Admin
PC
HQ-CDA
HQ-ESA
HQ-WSA
DMZ-Srv
HQ-ISRIPS/CX
SW Module
L3-Sw
Attacker
PC
Guest PC Employee
PC
SP-Srv
Internet-
RTR
Internet
Cisco SIO
ScanSafe
Implementing Cisco Secure Access Solutions
(300-208 SISAS)
- 17.
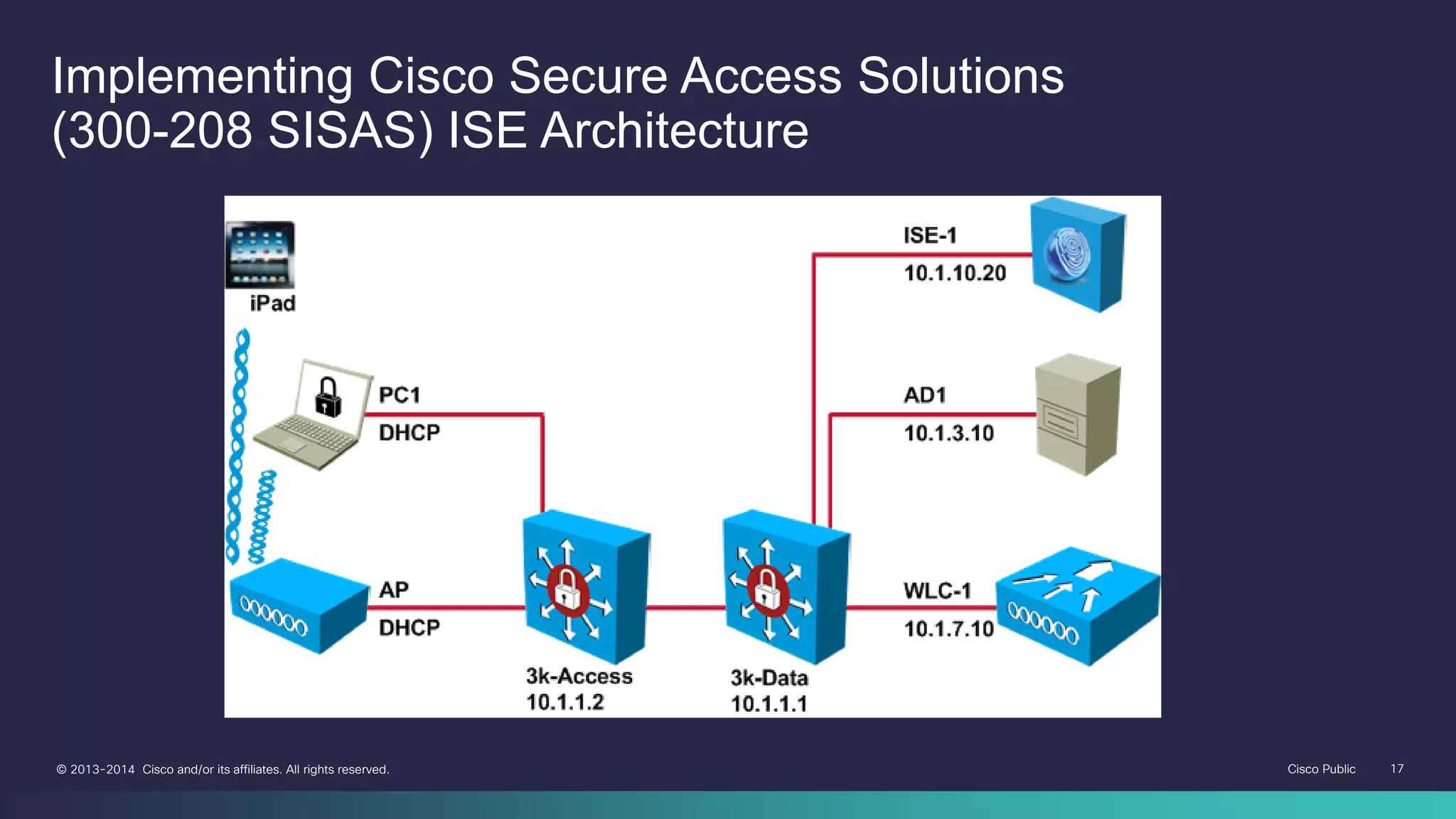
Cisco Public 17©2013-2014 Cisco and/or its affiliates. All rights reserved.
Implementing Cisco Secure Access Solutions
(300-208 SISAS) ISE Architecture
- 18.
Cisco Public 18©2013-2014 Cisco and/or its affiliates. All rights reserved.
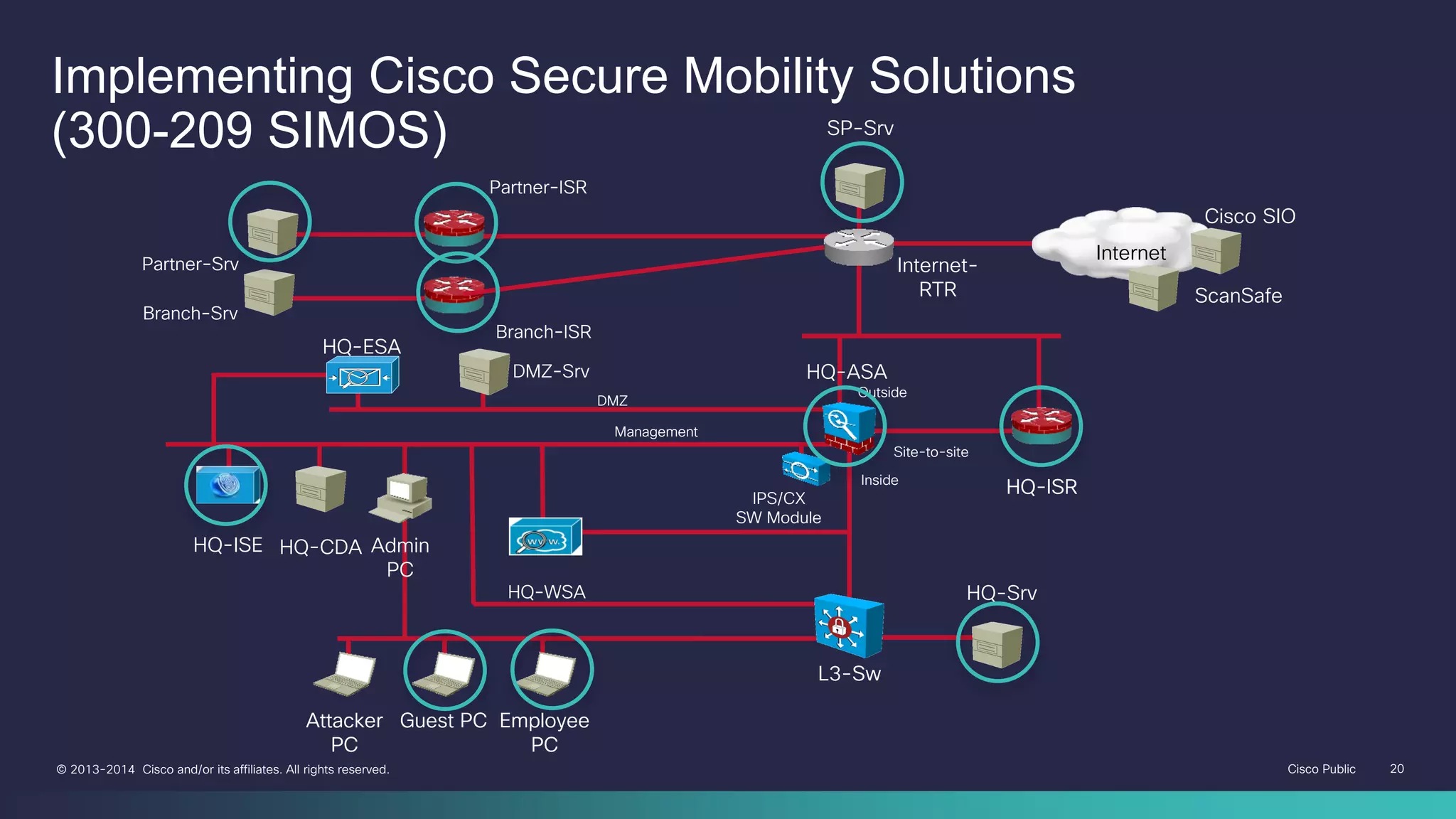
• Cisco ASA Firewall や Cisco IOS Software プラットフォーム (Cisco Router 等) で
利用可能な各種 VPN (Virtual Private Network) ソリューションにより
セキュアなリモート通信を適切に実装するのに必要な知識
リモート アクセス VPN:
Cisco AnyConnect Secure Mobility Client による IKEv2 / SSL VPN, Clientless SSL VPN
サイト間 (L2L) VPN:
GETVPN, DMVPN, FlexVPN 等の実装やソリューション、トラブル シューティング
Implementing Cisco Secure Mobility Solutions
(300-209 SIMOS)
- 19.
Cisco Public 19©2013-2014 Cisco and/or its affiliates. All rights reserved.
• 従来試験 (642-648 VPN) との主な差分
対象製品の追加: Cisco Router
→ IOS Software を利用した Router で構成可能な L2L VPN ソリューション:
GETVPN, DMVPN, FlexVPN 等の実装や設定に関する知識
他
Implementing Cisco Secure Mobility Solutions
(300-209 SIMOS)
- 20.
Cisco Public 20©2013-2014 Cisco and/or its affiliates. All rights reserved.
HQ-ASA
HQ-ISR
L3-Sw
HQ-Srv
Attacker
PC
Guest PC Employee
PC
DMZ
Management
Outside
Inside
Site-to-site
Partner-ISR
Branch-ISR
Partner-Srv
Branch-Srv
HQ-ISE Admin
PC
HQ-CDA
HQ-ESA
HQ-WSA
DMZ-Srv
HQ-ISRIPS/CX
SW Module
L3-Sw
Attacker
PC
Guest PC Employee
PC
SP-Srv
Internet-
RTR
Internet
Cisco SIO
ScanSafe
Implementing Cisco Secure Mobility Solutions
(300-209 SIMOS)
- 21.
Cisco Public 21©2013-2014 Cisco and/or its affiliates. All rights reserved.
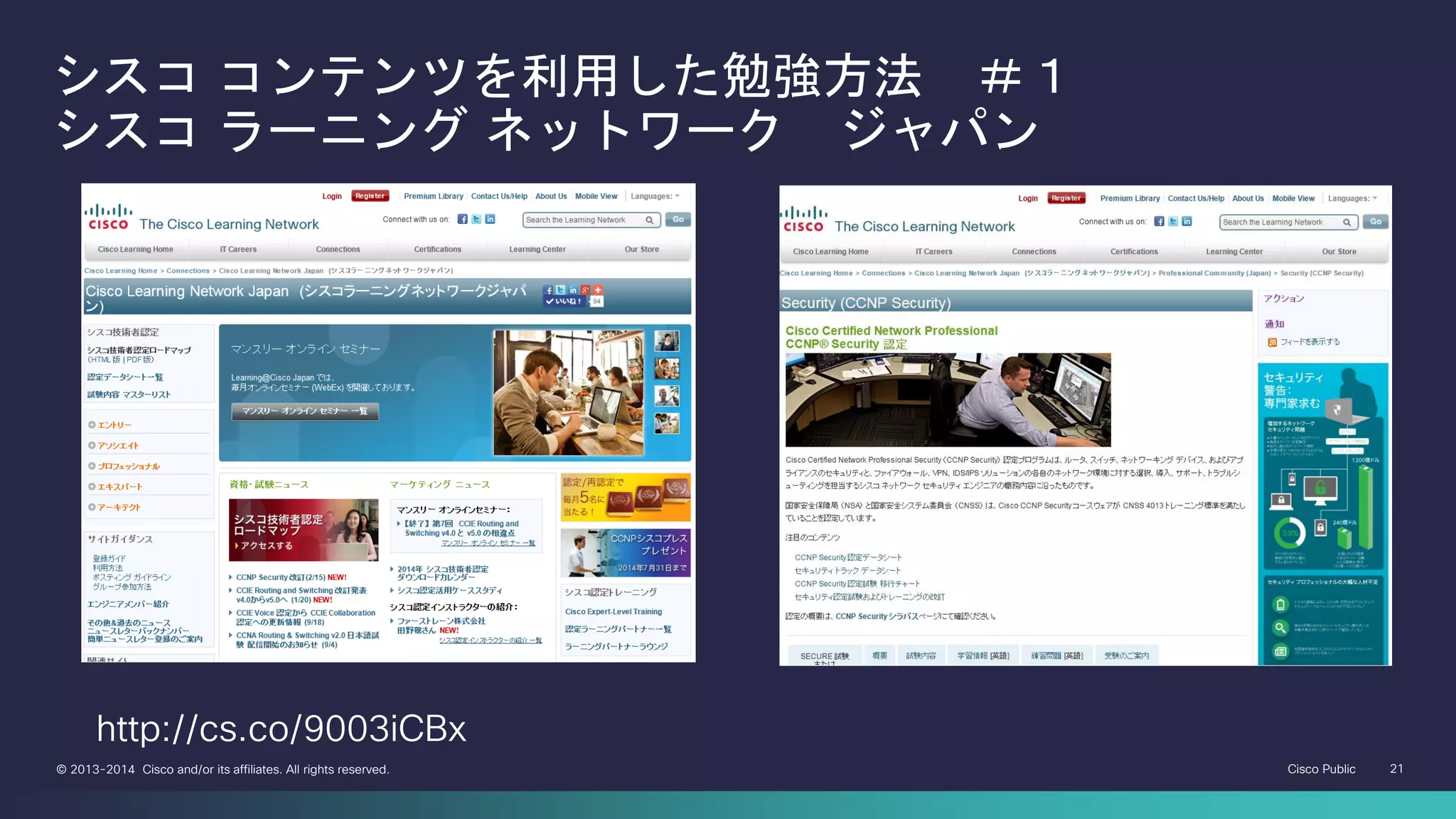
シスコ コンテンツを利用した勉強方法 #1
シスコ ラーニング ネットワーク ジャパン
http://cs.co/9003iCBx
- 22.
Cisco Public 22©2013-2014 Cisco and/or its affiliates. All rights reserved.
シスコ コンテンツを利用した勉強方法 #2
シスコ ラーニング ネットワーク US(英語)
http://cs.co/9003iCBx
- 23.
Cisco Public 23©2013-2014 Cisco and/or its affiliates. All rights reserved.
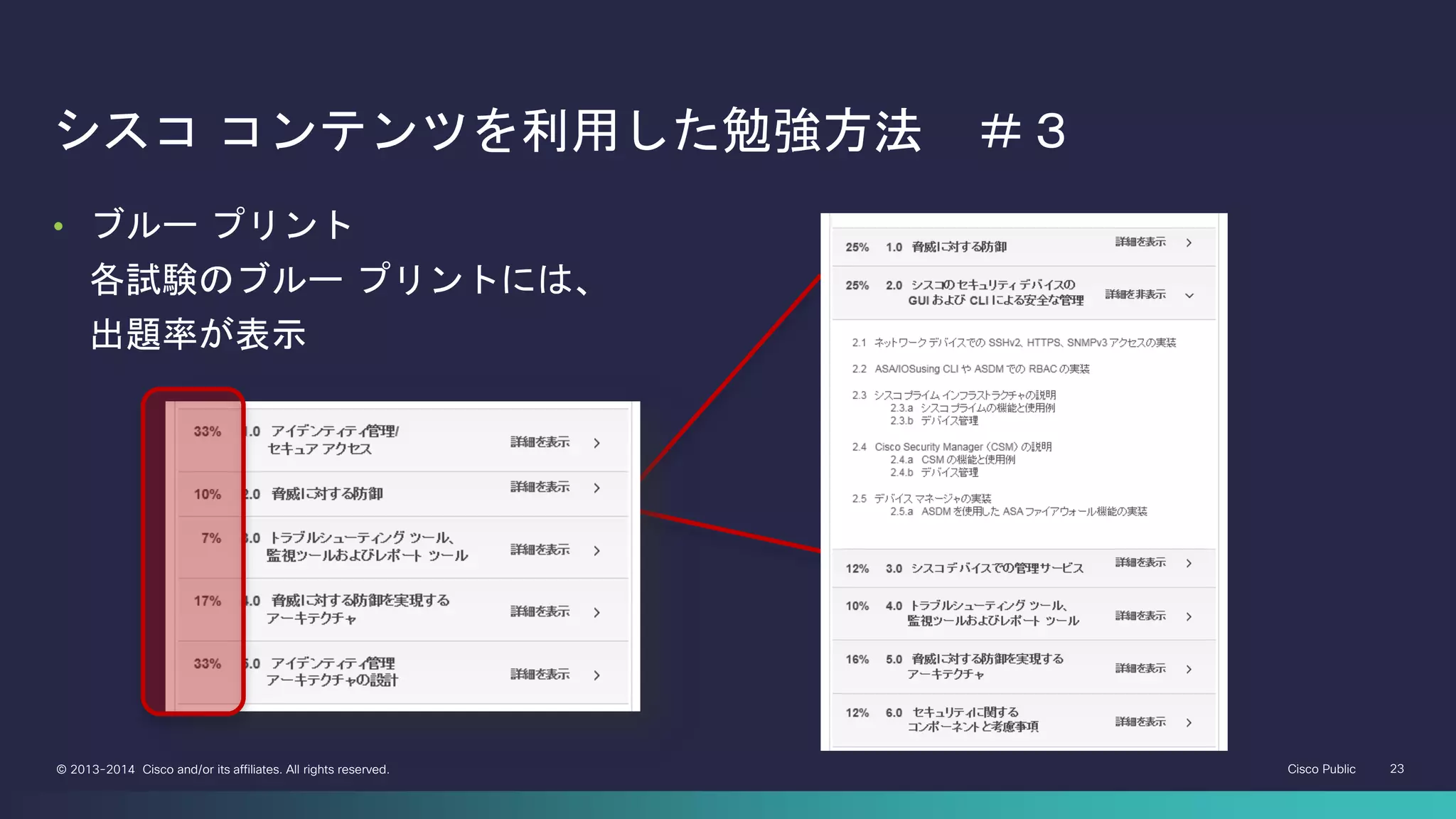
シスコ コンテンツを利用した勉強方法 #3
• ブルー プリント
各試験のブルー プリントには、
出題率が表示
- 24.
Cisco Public 24©2013-2014 Cisco and/or its affiliates. All rights reserved.
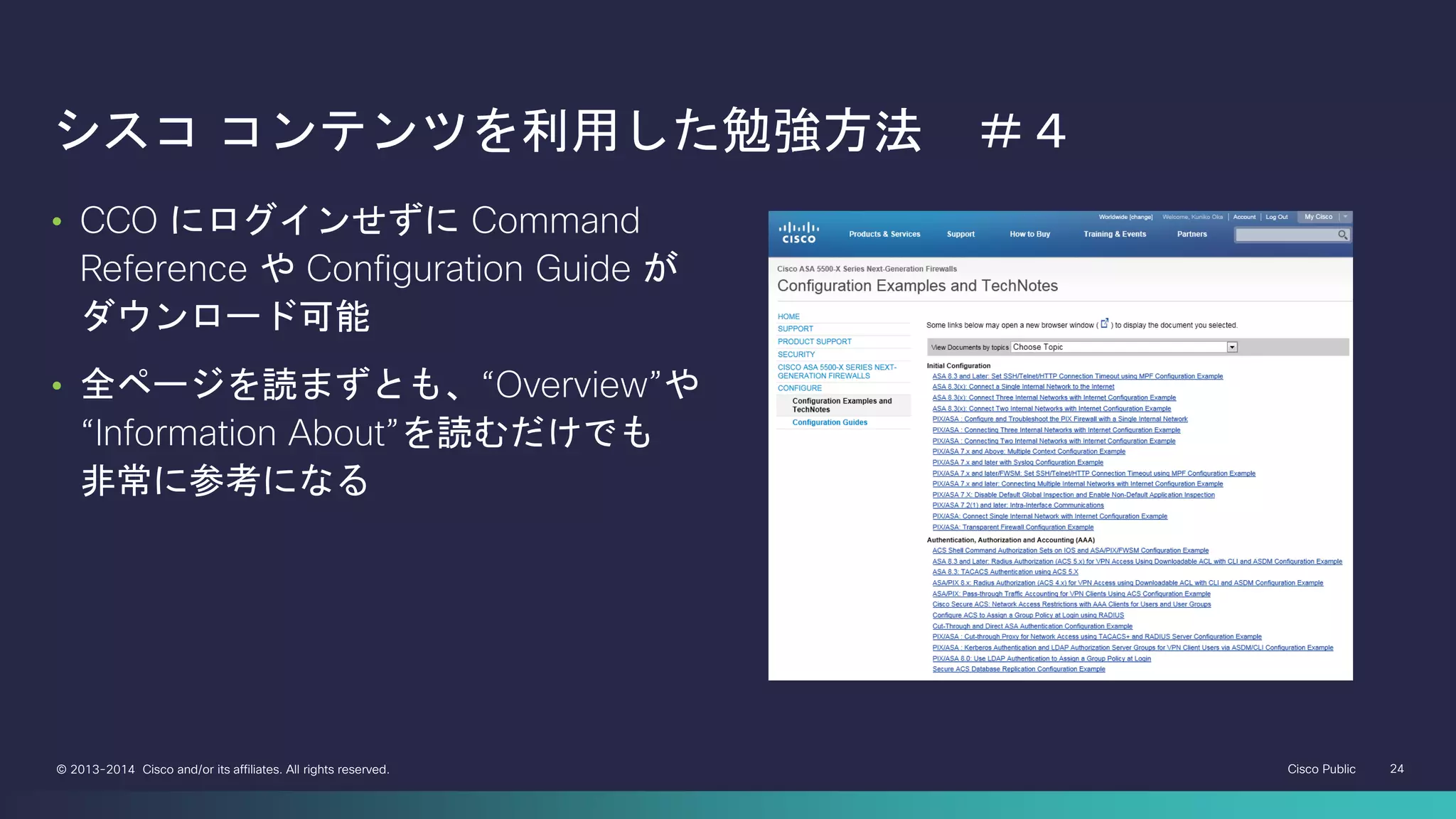
シスコ コンテンツを利用した勉強方法 #4
• CCO にログインせずに Command
Reference や Configuration Guide が
ダウンロード可能
• 全ページを読まずとも、“Overview”や
“Information About”を読むだけでも
非常に参考になる
- 25.
Cisco Public 25©2013-2014 Cisco and/or its affiliates. All rights reserved.
シスコ サポート コミュニティ
https://supportforums.cisco.com/community/5036/csc-japan
- 26.
Cisco Public 26©2013-2014 Cisco and/or its affiliates. All rights reserved.
シスコシステムズ 認定試験情報&お問合せ先
• シスコシステムズ認定トレーニング / 認定資格
• www.cisco.com/jp/go/training/
• シスコ ラーニング ネットワーク ジャパン
• www.cisco.com/go/learningnetwork/jp
• シスコ技術者認定 Facebook
• http://www.facebook.com/Cisco.Learning.Japan
• シスコ技術者認定 Twitter
• https://twitter.com/#!/CiscoCertJapan
• 認定試験関連問合せ先 1: 試験内容、受験方法、トラッキング システムなど
• http://ciscocert.force.com/japan
• 認定試験関連問合せ先 2:マーケティング活動:イベント、セミナーなど
• certification-japan@cisco.com
- 27.