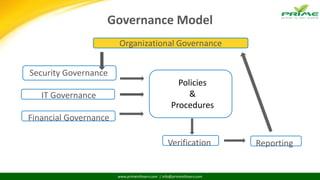
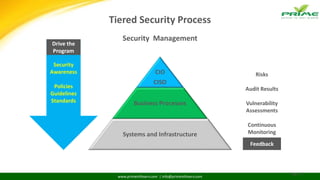
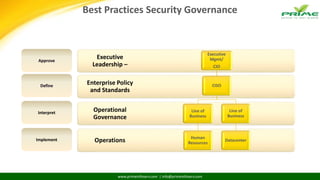
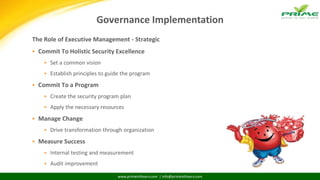
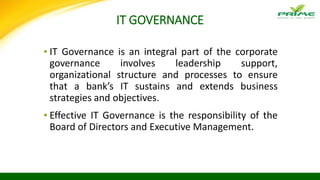
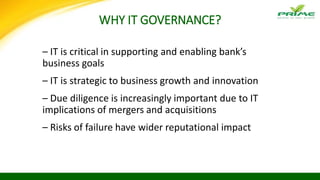
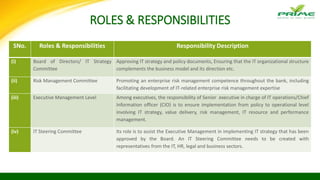
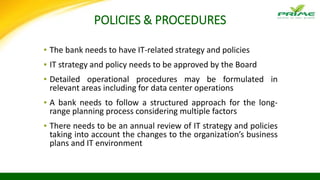
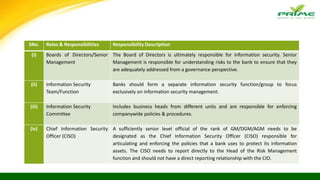
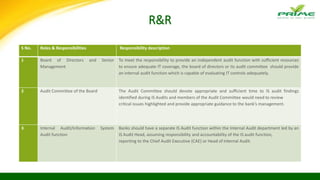
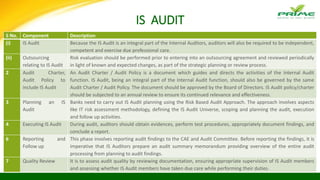
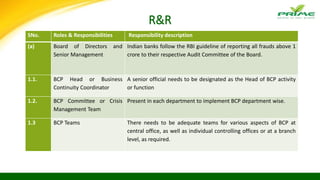
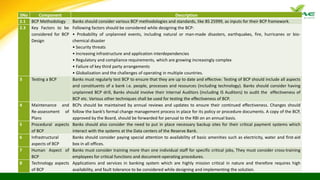
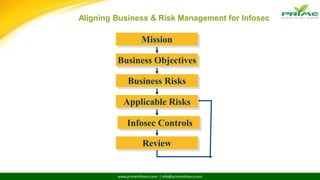
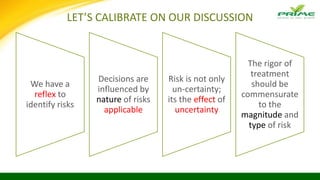
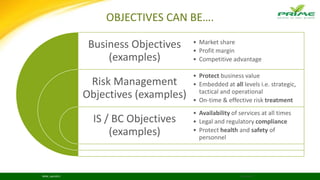
This document discusses information security governance and business continuity planning for organizations. It emphasizes that information security is a business issue that requires strategic management from the board and senior leadership. It outlines key roles and responsibilities for governance bodies like the board, executive management, information security team, and risk committees. It also discusses developing policies, procedures, risk management processes, information security audits, and testing business continuity plans to ensure effective governance. Regular reviews and updates are needed to account for a changing threat landscape and business environment.












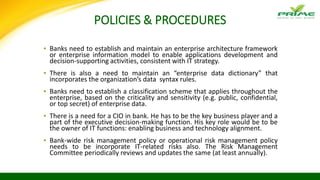


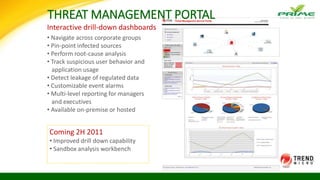
![RISK - DEFINITION
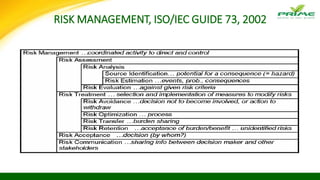
Source Definition
ISO/IEC Guide 73:2002 ‘Combination of the probability of an event and its consequence.’
AS/NZS 4360:2004 ‘Chance of something happening that will have an impact on objectives.’
COSO (2004) ERM - Integrated
Framework
‘Events with a negative impact represent risks, which can prevent value
creation or erode existing value. Events with positive impact may offset
negative impacts or represent opportunities.’
Lars Oxelheim and Clas
Wihlborg (2008) Corporate
Decision-Making with
Macroeconomic Uncertainty
‘The concept of risk refers in general to the magnitude and likelihood of
unanticipated changes that have an impact on a firm’s cash flows, value or
profitability. […] Risk has a negative connotation, but uncertainty can be a
source of opportunities as well as costs.’
BRiSK_April2015 22/04/2016](https://image.slidesharecdn.com/infocon-prime3-160422060705/85/Infocon-Bangladesh-2016-57-320.jpg)


















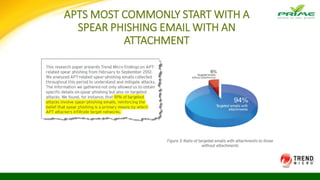




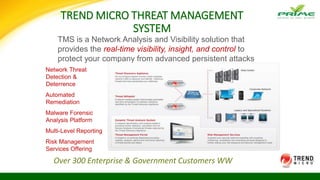
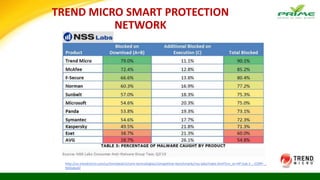
!["While traditional antivirus [vendors] may be able to spot and deflect many kinds of
attacks, they're not well-equipped to handle targeted attacks. But there are
technologies able to detect such attacks, if not entirely prevent them."](https://image.slidesharecdn.com/infocon-prime3-160422060705/85/Infocon-Bangladesh-2016-118-320.jpg)