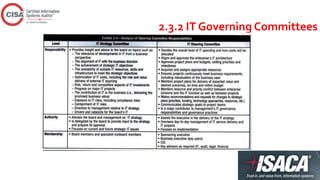
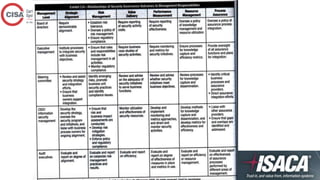
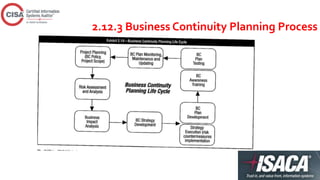
This document provides an overview of topics covered in a CISA review course, including IT governance, corporate governance, governance of enterprise IT, risk management, information security management practices, auditing IT governance structure and implementation, and business continuity planning. The document defines key concepts, best practices, standards, and approaches for each topic. It also outlines the roles and responsibilities of various committees, policies, procedures, and other elements involved in effectively governing enterprise IT.
![2016 CISA ® Review Course
Hafiz Sheikh Adnan Ahmed – CISA, COBIT 5, ISO 27001 LA
[PECB Certified Trainer]](https://image.slidesharecdn.com/chapter2cisa-training2016-160330195808/75/CISA-Training-Chapter-2-2016-1-2048.jpg)