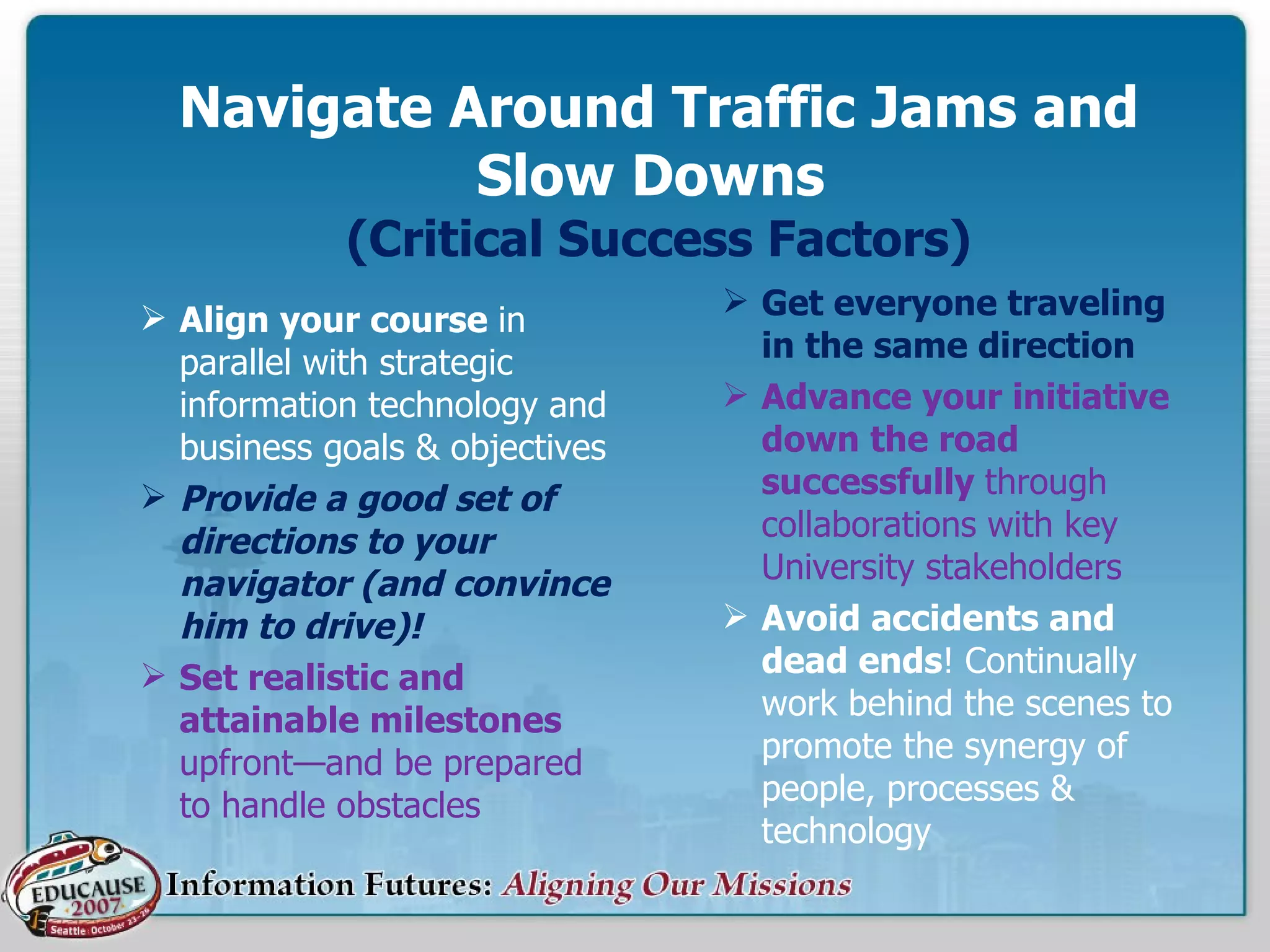
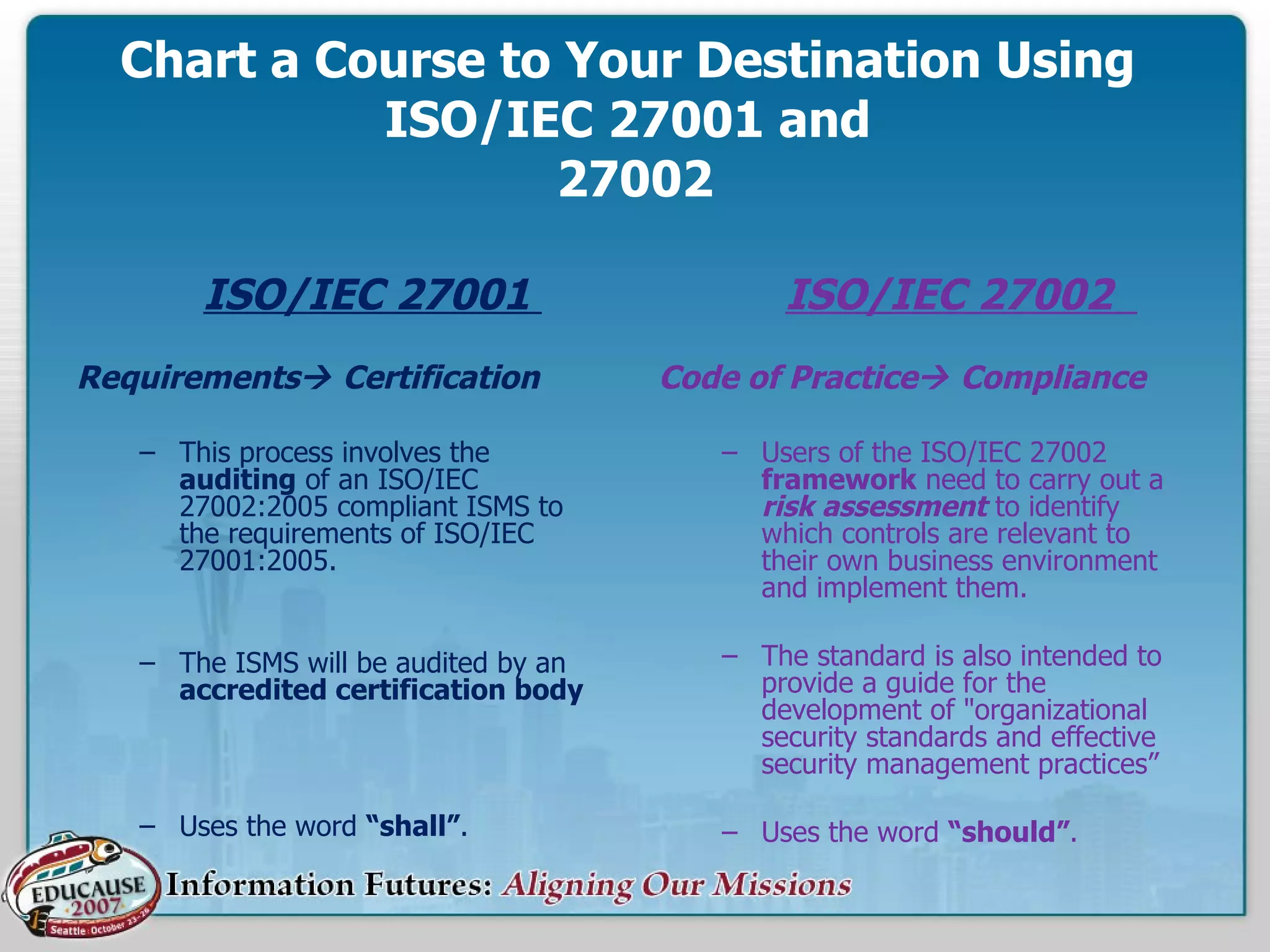
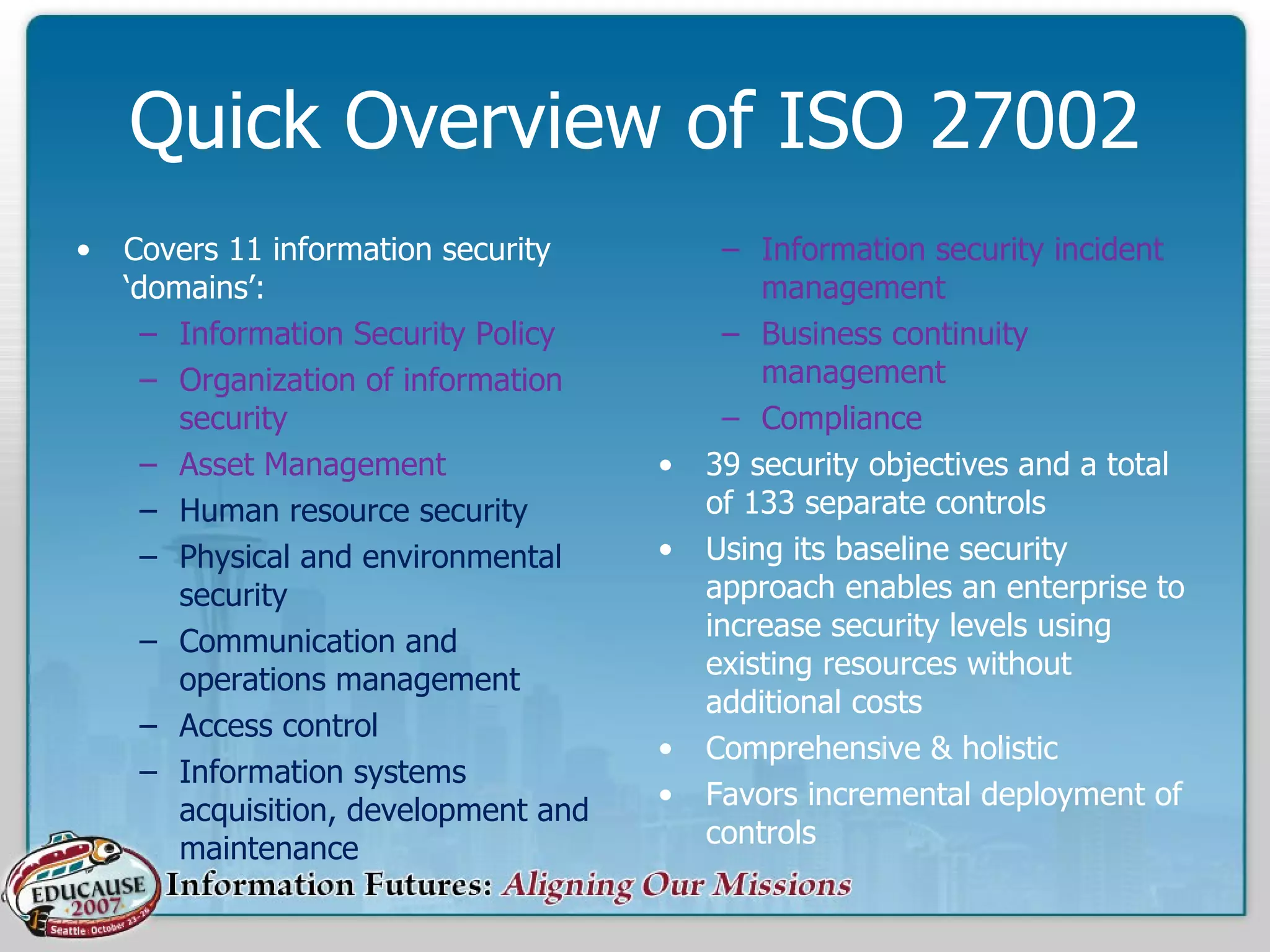
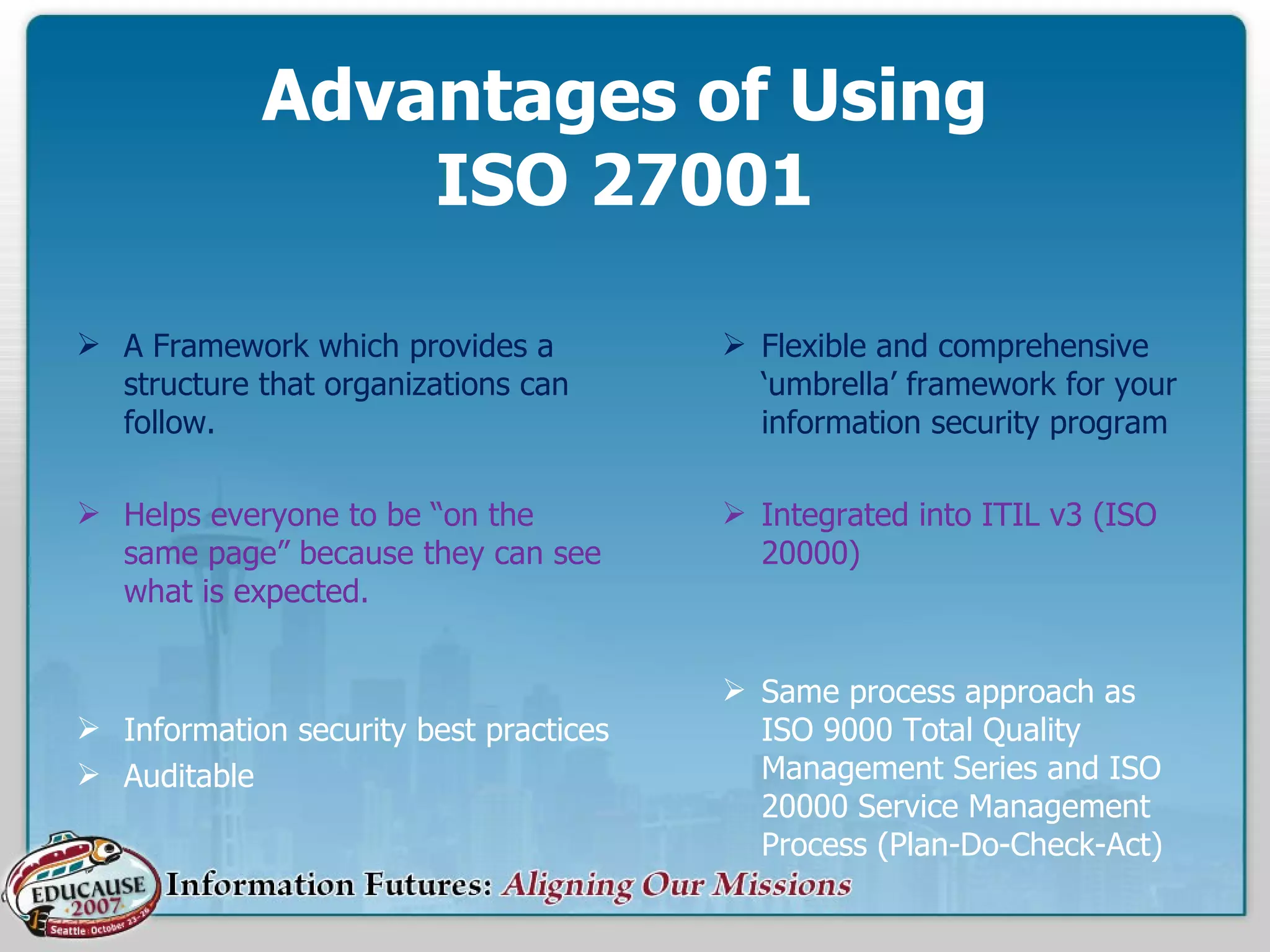
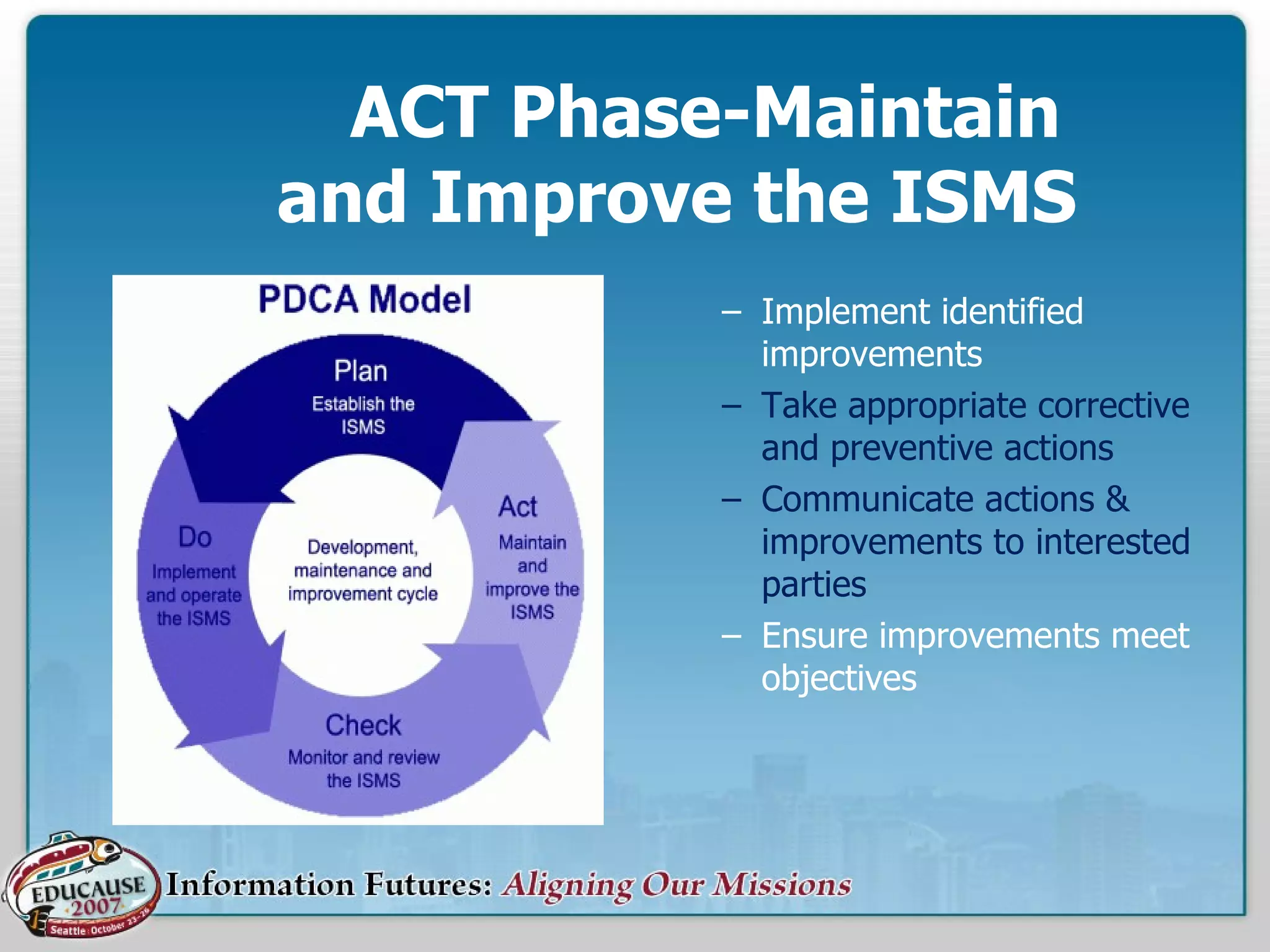
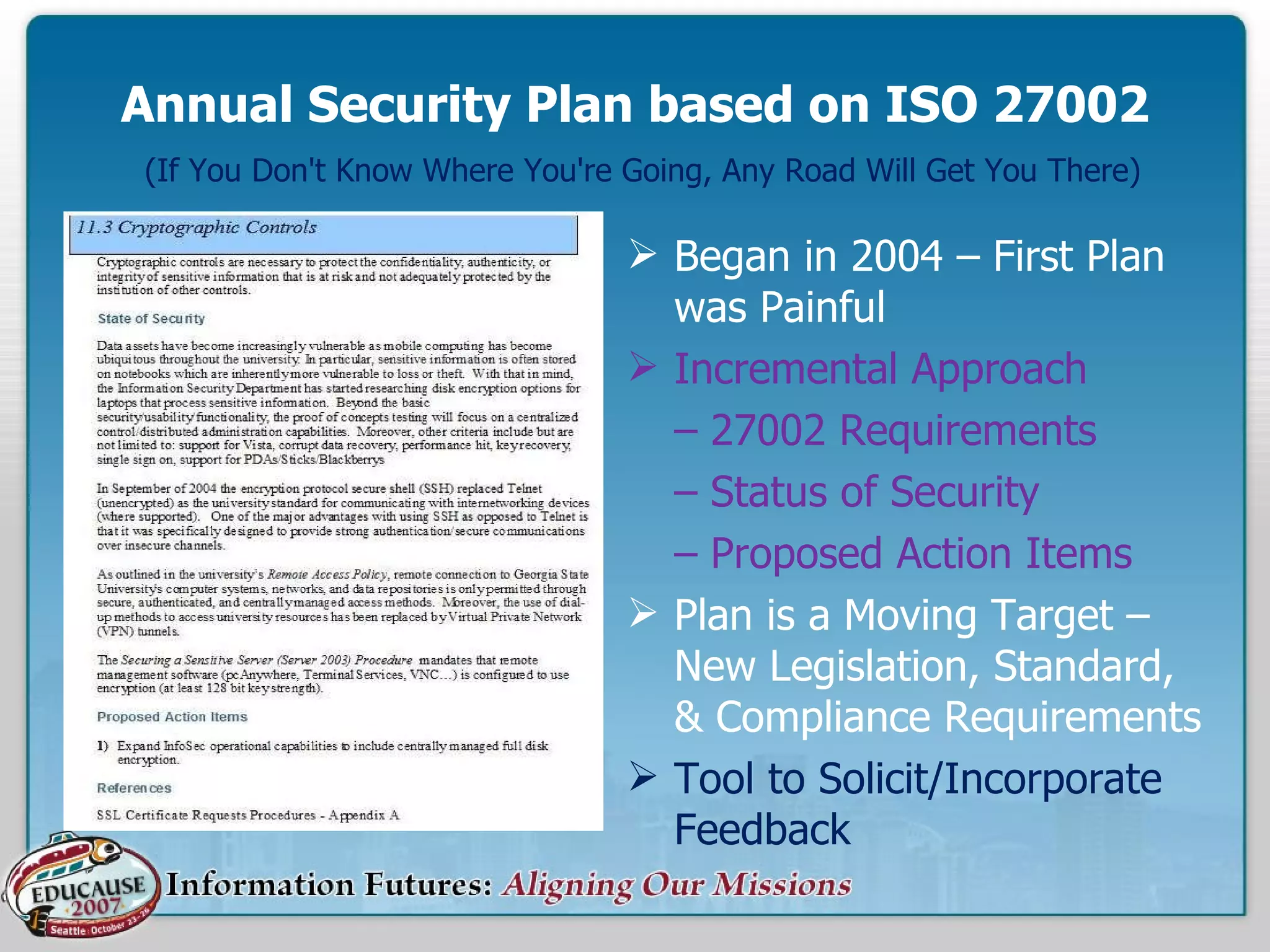
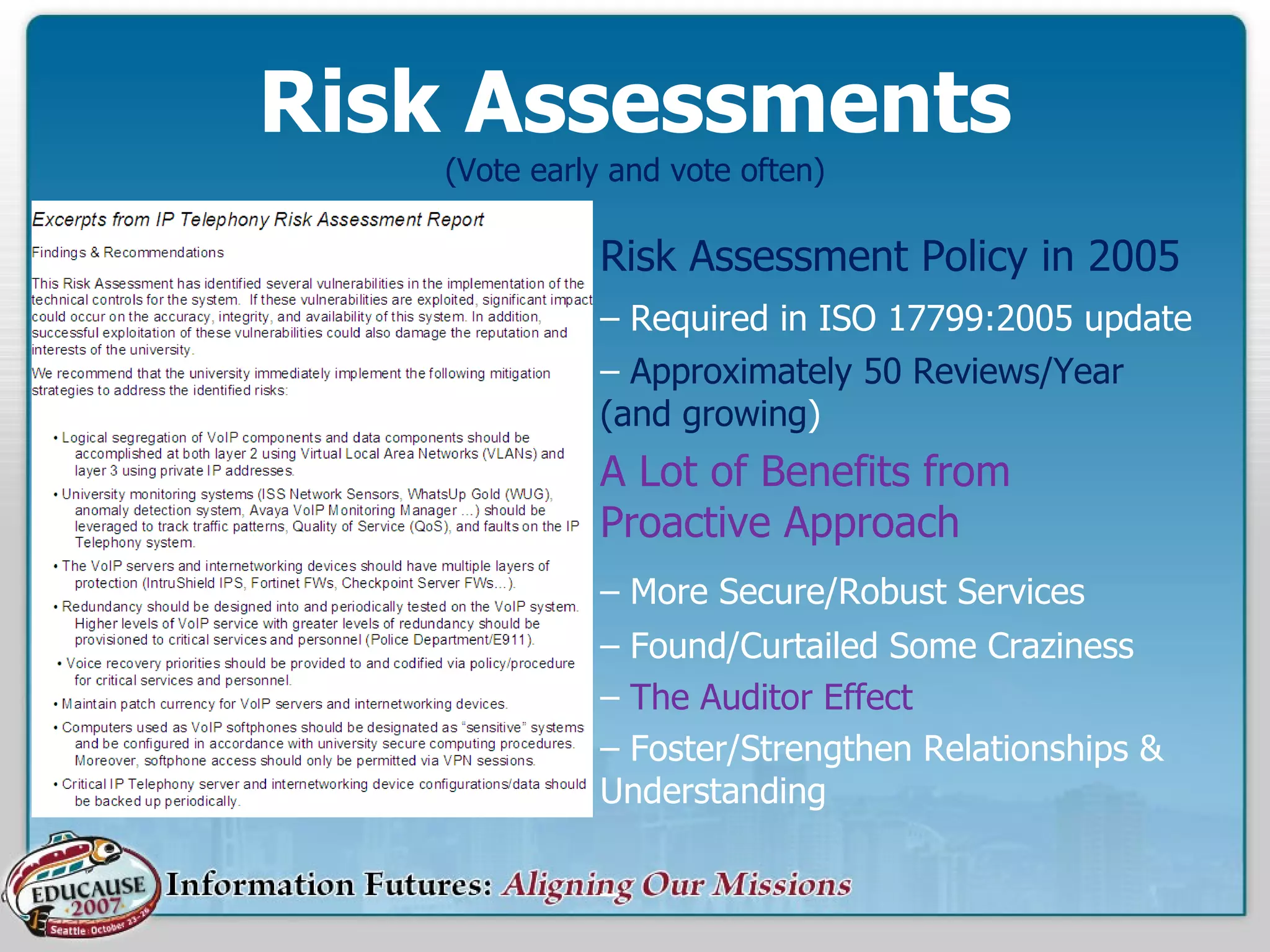
GSU is developing an Information Security Management System (ISMS) based on the ISO/IEC 27001 standard to protect the university's reputation, ensure security and availability of information, and reduce risks. The roadmap involves strategic planning, continuous reviews and improvements, and incremental implementation of controls. It will align information security with business goals and provide comprehensive, auditable best practices for managing risks through plans, implementation, monitoring, and improvements.