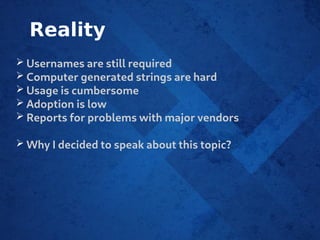
The document discusses the implementation of passkeys, which aim to enhance security by replacing traditional username and password combinations with unique cryptographically signed keys for each application. It outlines challenges such as low adoption rates, cumbersome usage, and issues with vendor controls over stored authentication keys. Various implementation aspects, including frontend and backend processes, as well as potential problems with passkeys, particularly related to hardware devices, are also detailed.