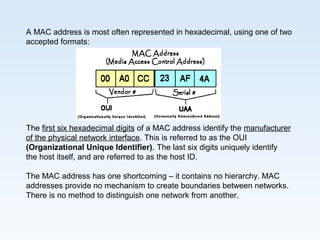
Hardware addressing uses MAC addresses at the data link layer to uniquely identify devices within a local network. MAC addresses are 48-bit identifiers hardcoded or dynamically assigned to network interfaces. While MAC addresses uniquely identify individual devices, they lack hierarchy and provide no means to separate different networks, posing scalability issues for large internetworks like the Internet. Logical addressing at higher layers solves this problem.