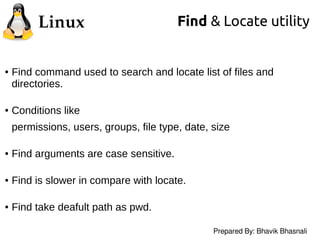
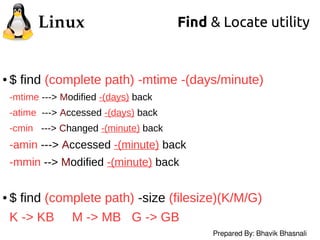
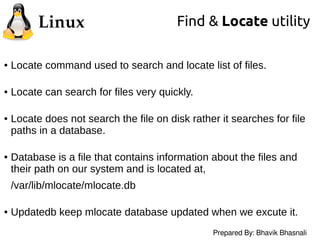
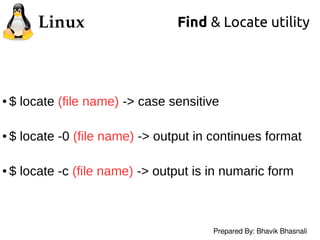
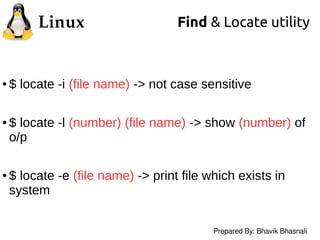
The document presents an overview of the 'find' and 'locate' commands used for searching files and directories in Linux. It outlines the functionalities, differences, and various arguments pertaining to both commands, emphasizing that 'find' is more thorough but slower, while 'locate' is faster as it references a prebuilt database. Additionally, the document provides examples of command usage and links to further references.