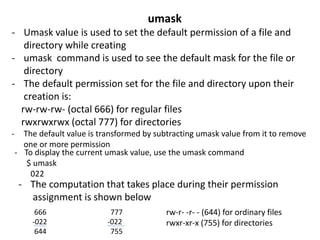
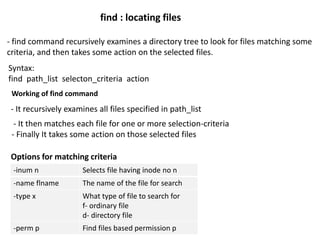
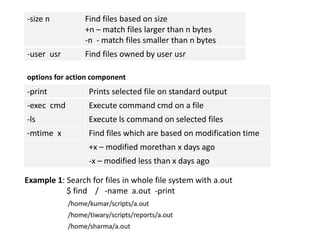
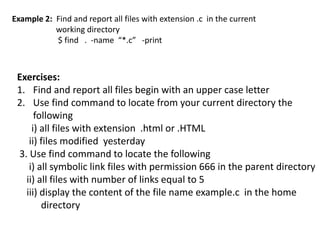
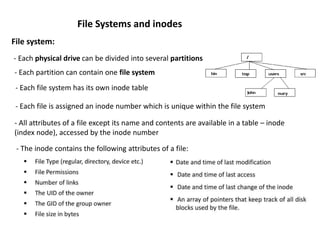
This document provides an introduction to Unix file systems and attributes. It discusses inodes, hard links created using the ln command, the umask command for setting default file permissions, and using the find command to search for files based on various criteria like name, size, permissions and more. Examples are given for using ln to create hard links, viewing inode numbers and link counts, setting umask, and searching with find. Exercises are included to practice using find to locate files based on attributes.
![ln – creating hard links
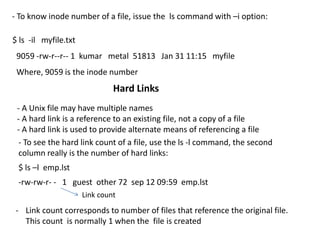
- A file is linked with the ln command which takes two filenames as
arguments
Syntax: ln [options] existing_filename new_filename
Example: link emp.lst with employee
$ ln emp.lst employee
- The –i option to ls shows that they have the same inode number, meaning
that they are actually one and the same file:
$ ls –li emp.lst employee
29518 -rwxr-xr-x 2 kumar metal 915 may 4 09:58 emp.lst
29518 -rwxr-xr-x 2 kumar metal 915 may 4 09:58 employee
- The link count, which is normally one for unlinked files, is shown to be two](https://image.slidesharecdn.com/filesystemsandinodes-200417131348/85/File-systems-and-inodes-5-320.jpg)