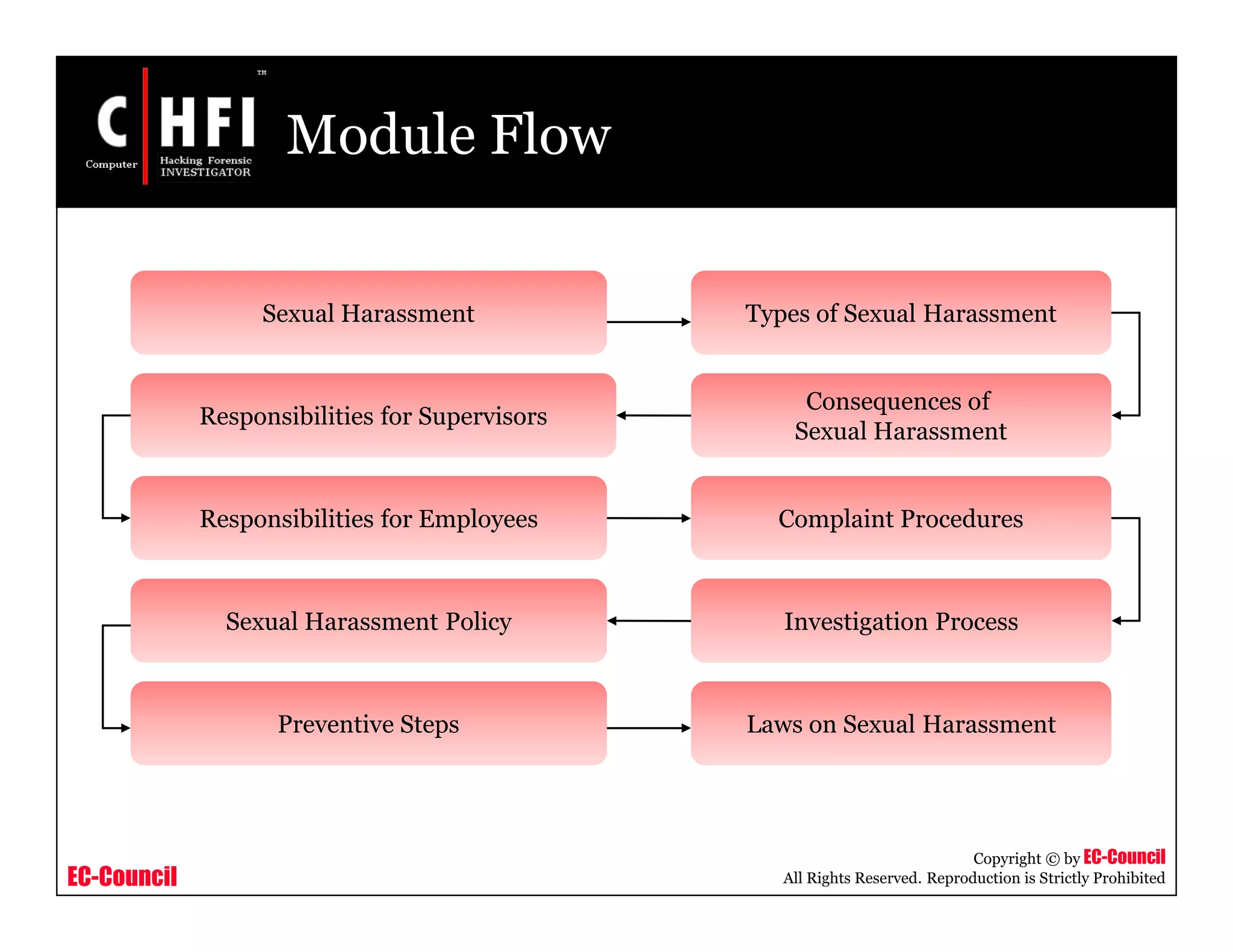
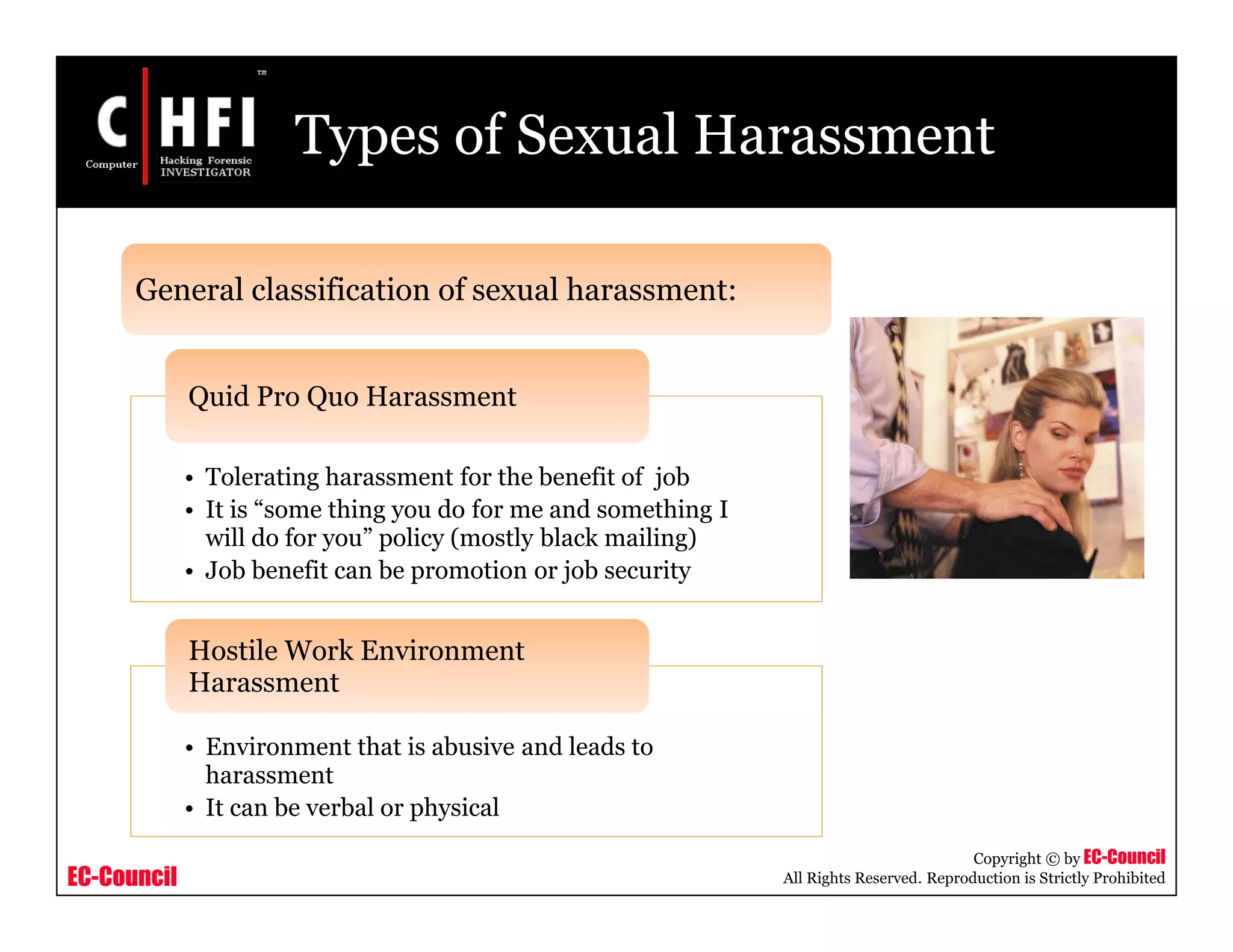
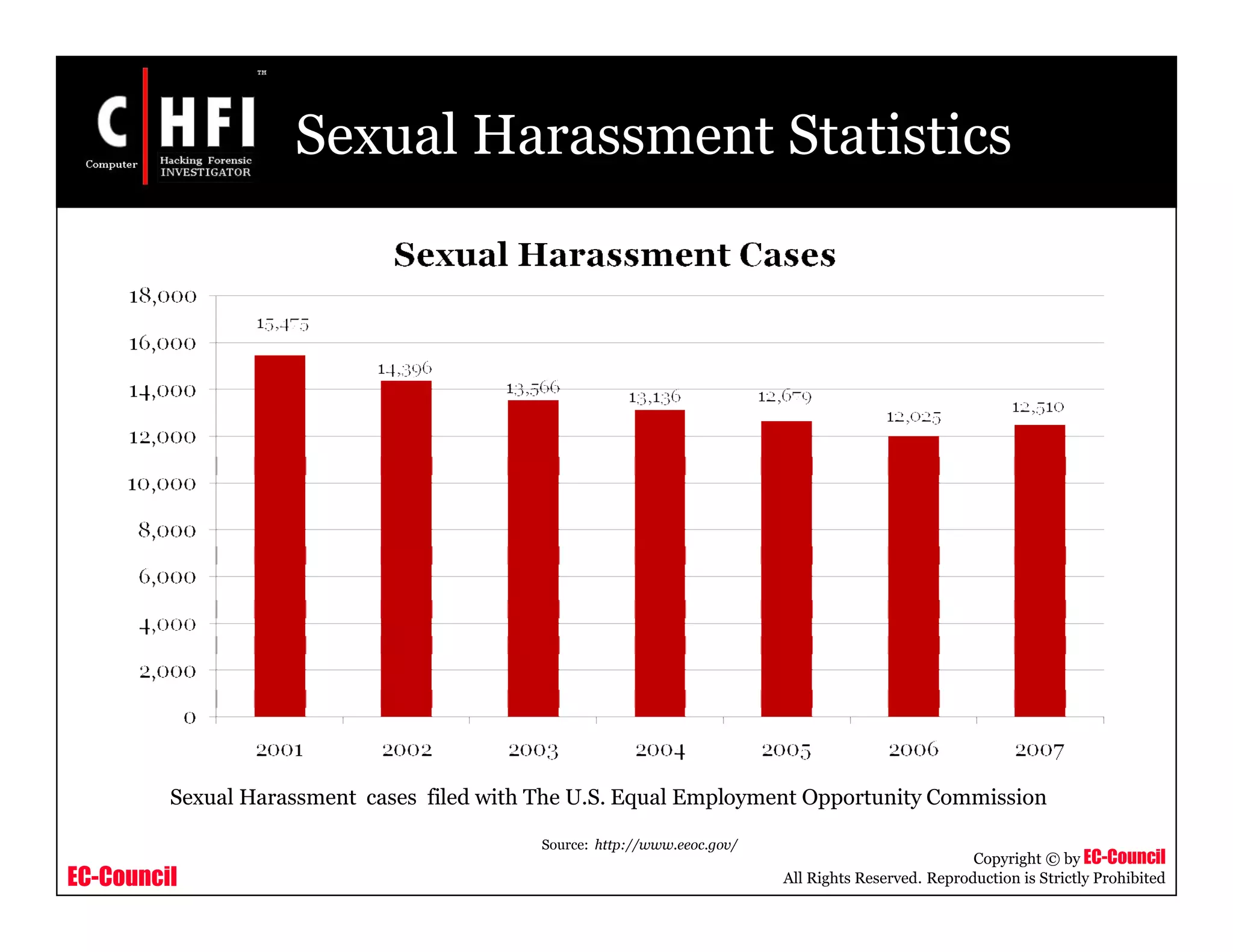
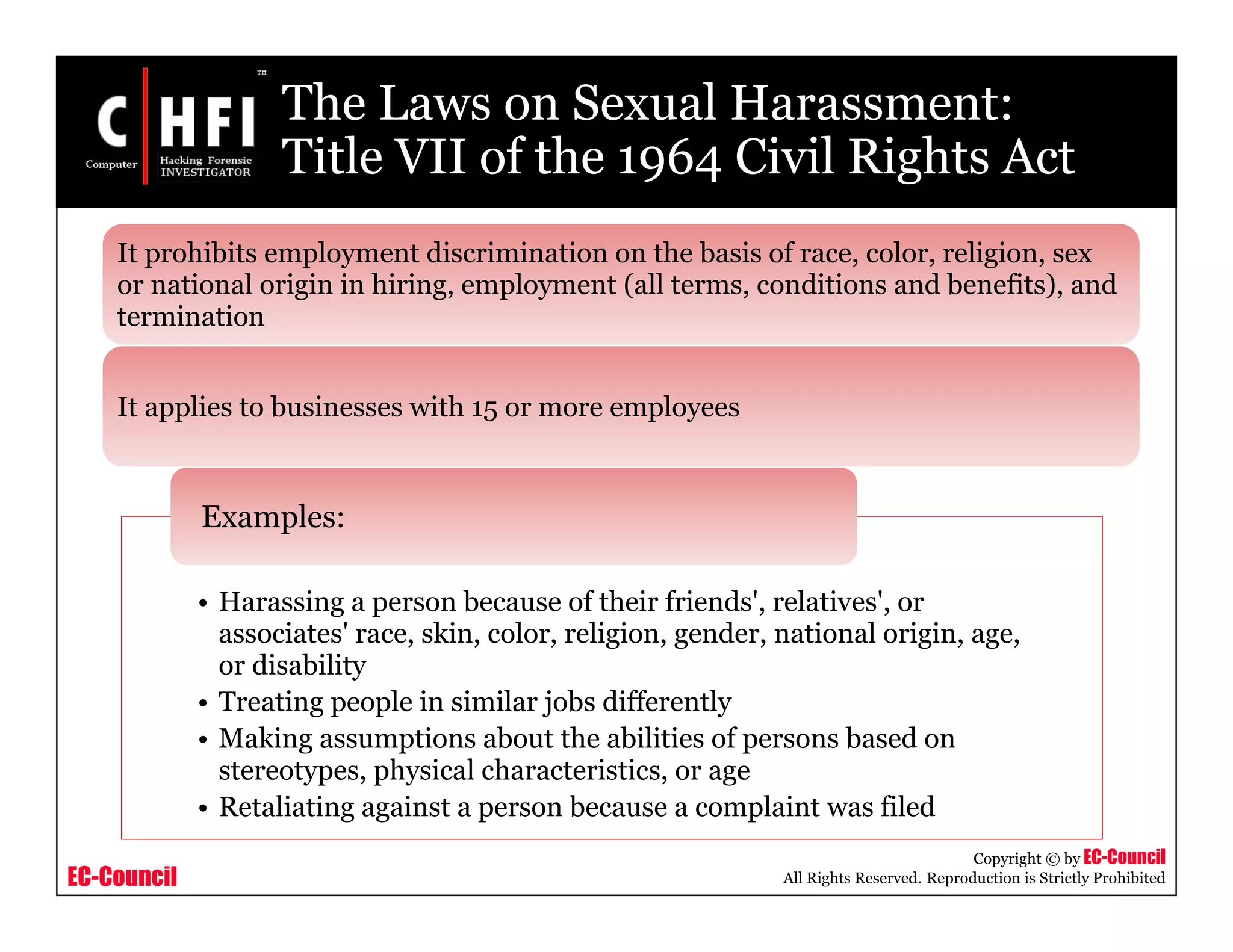
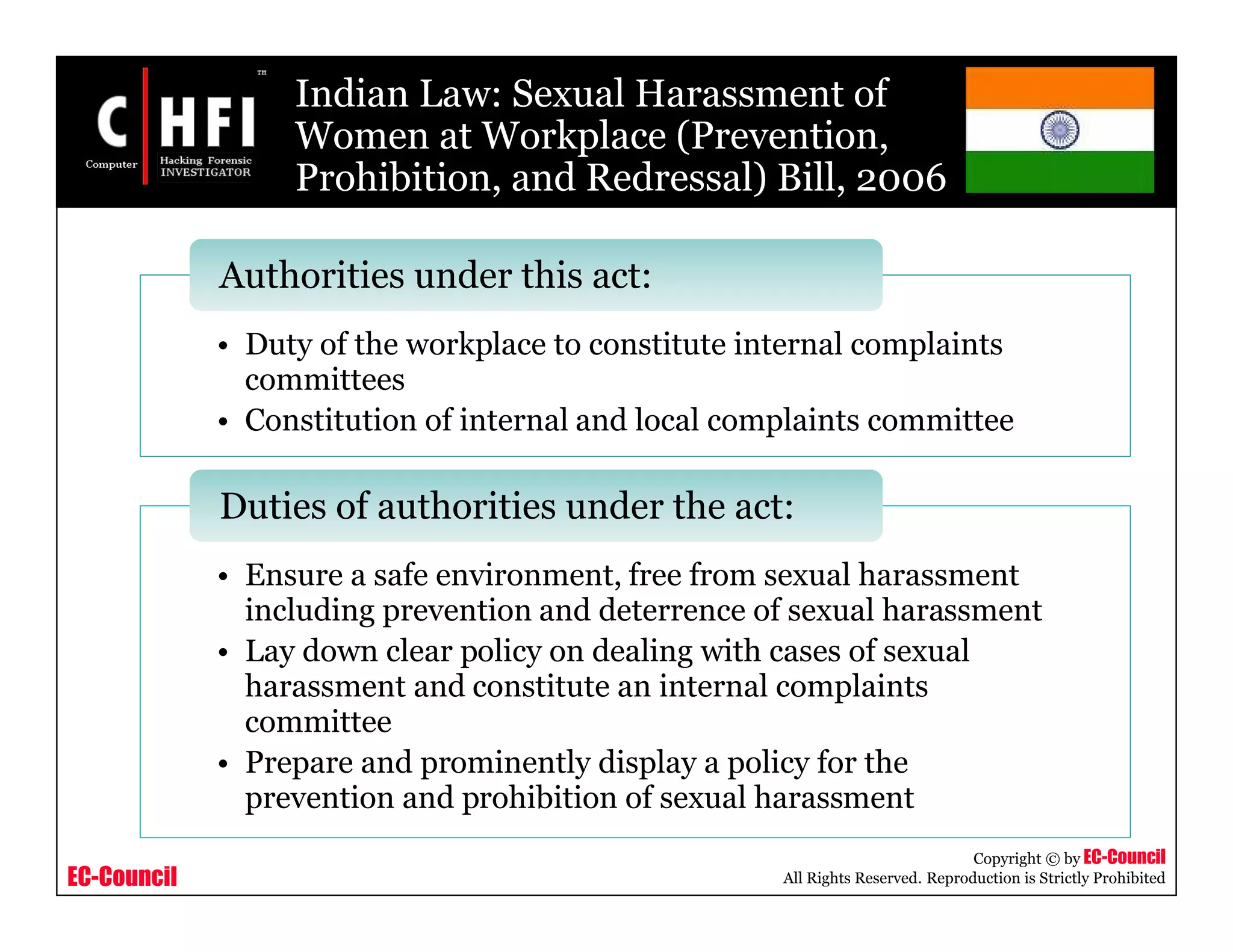
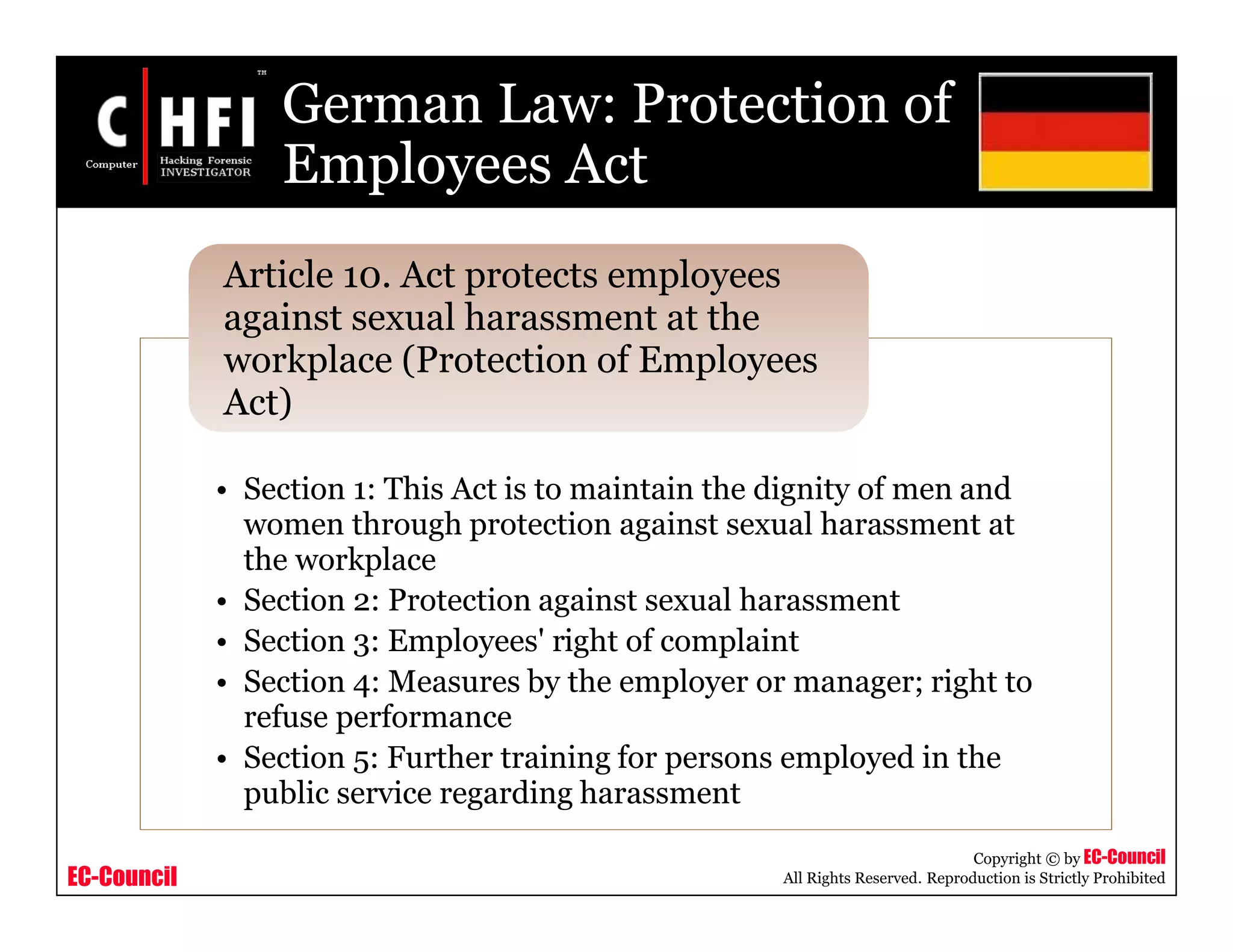
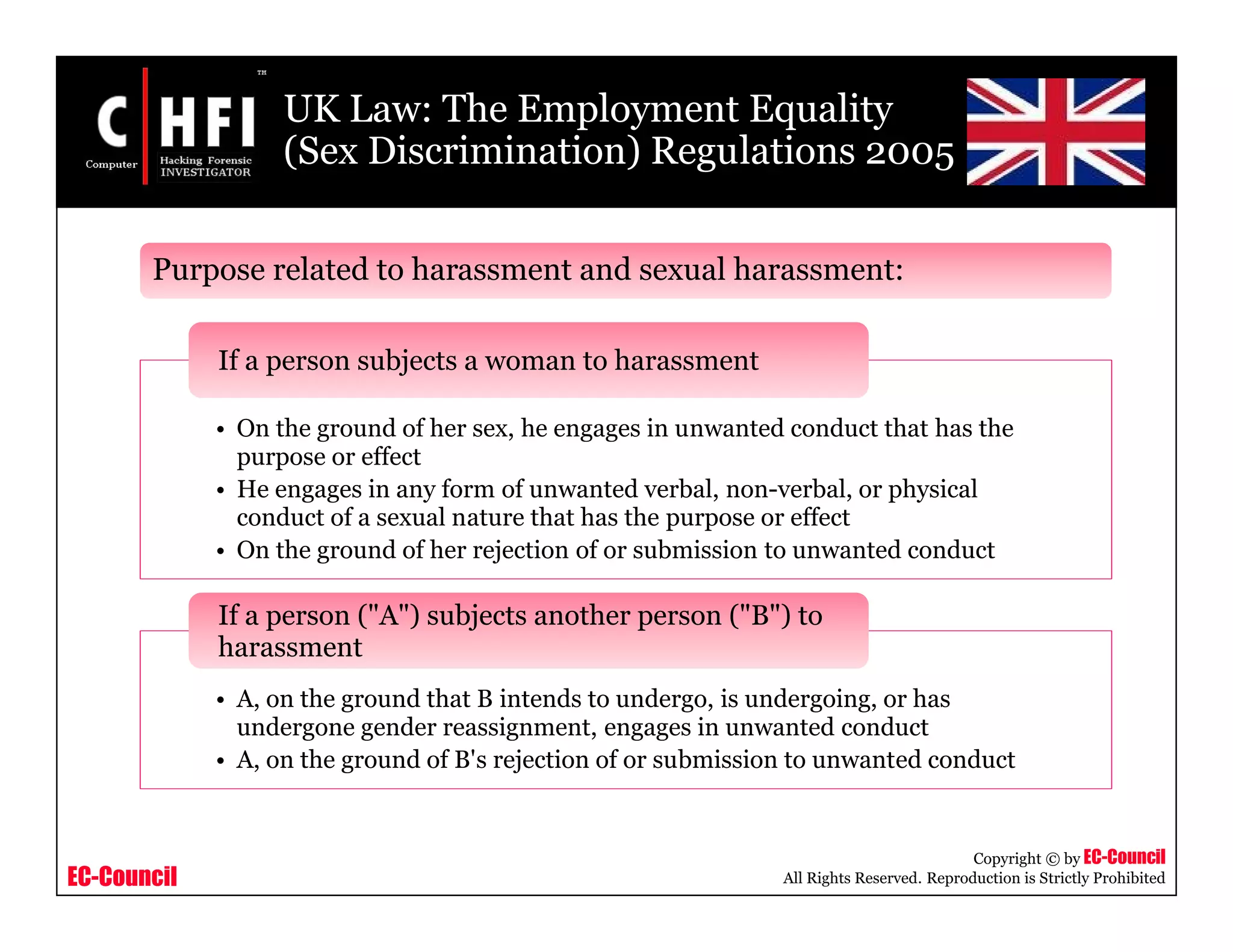
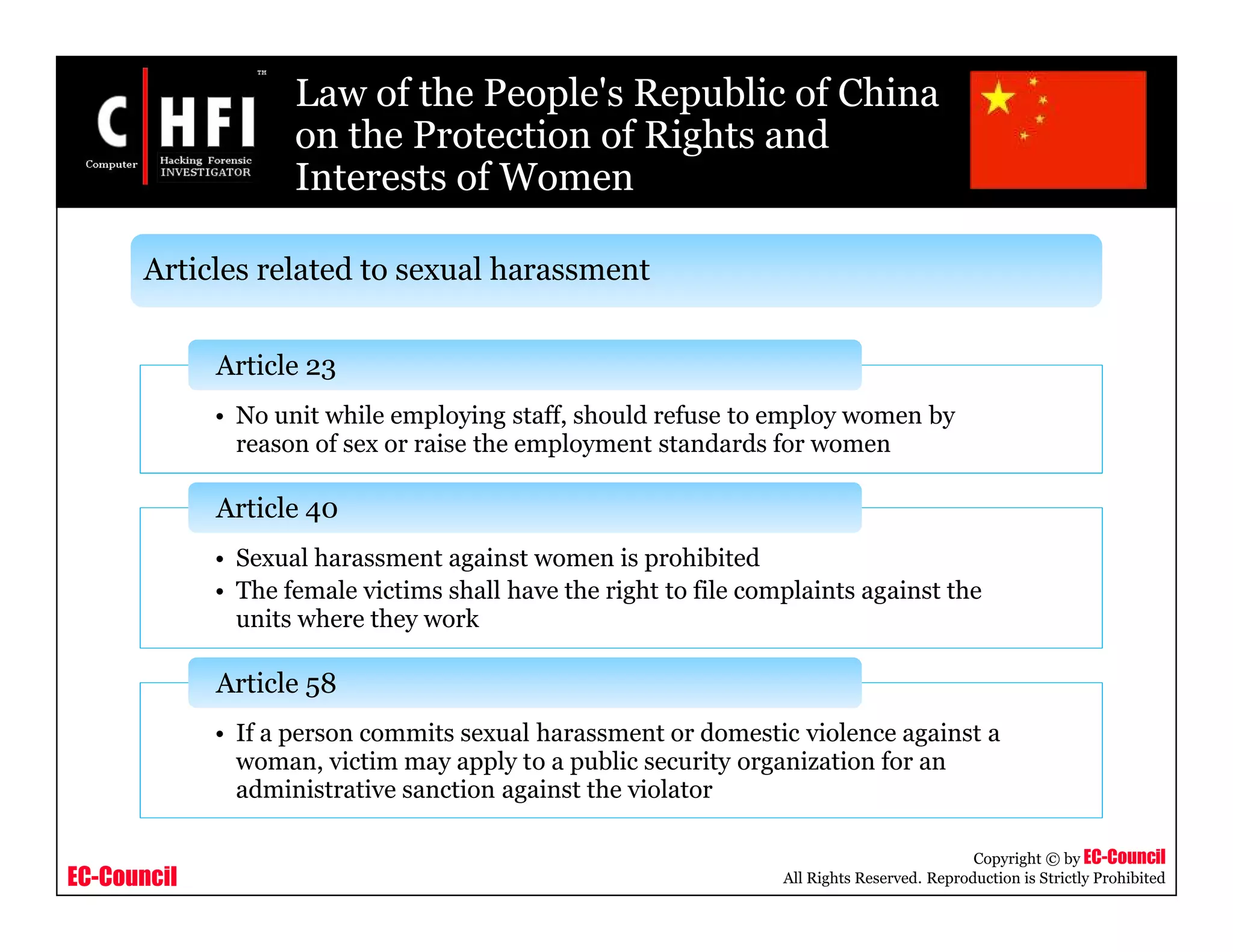
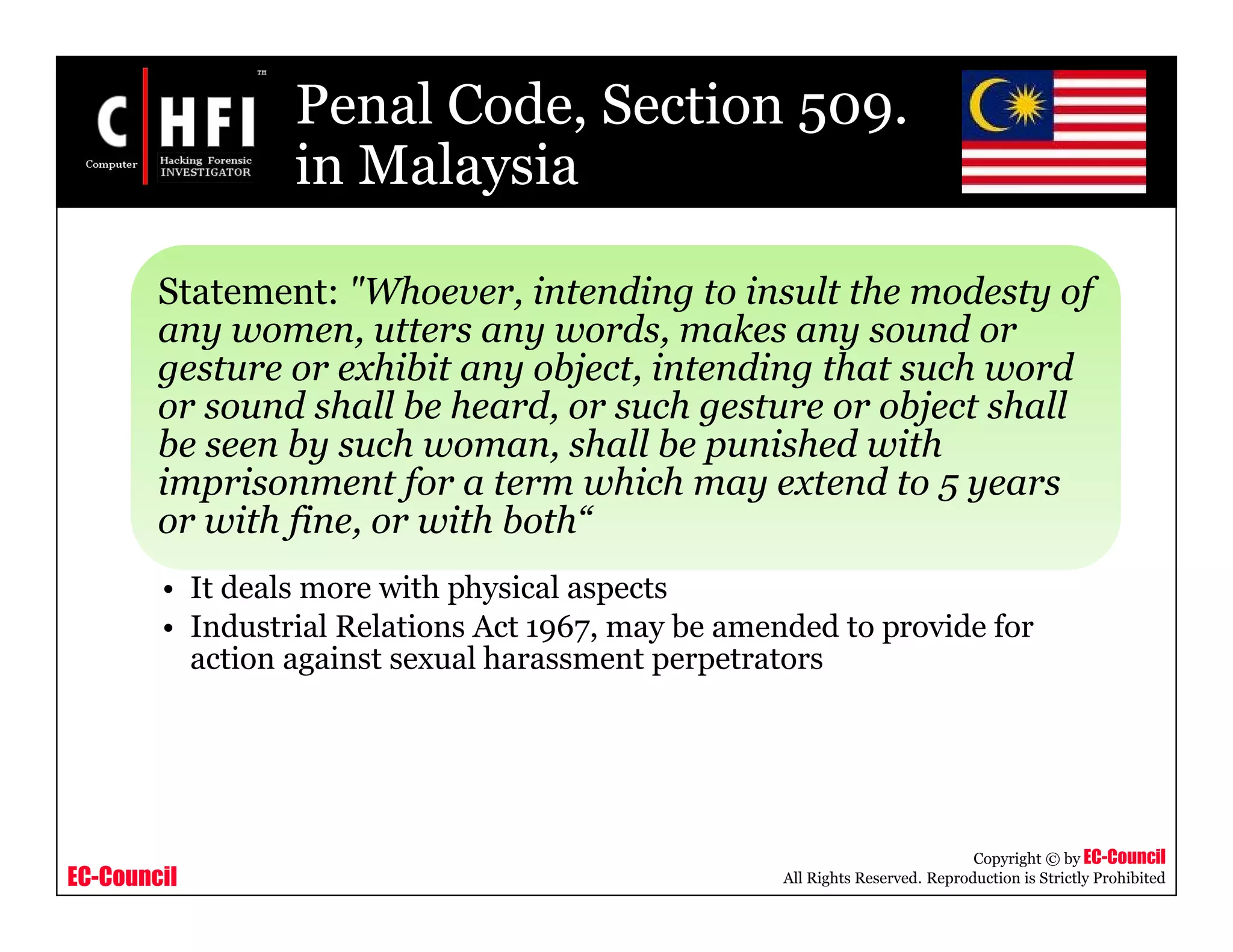
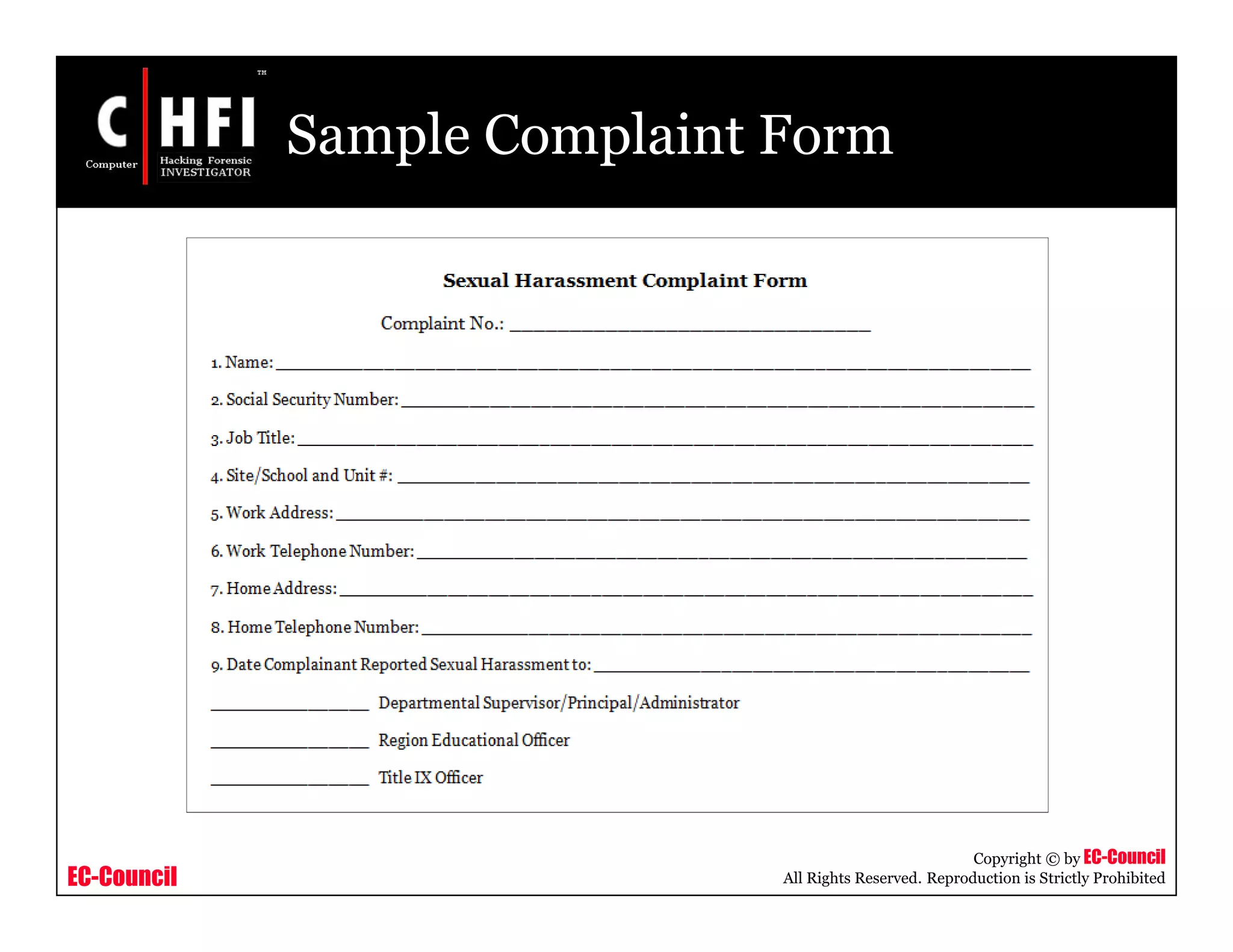
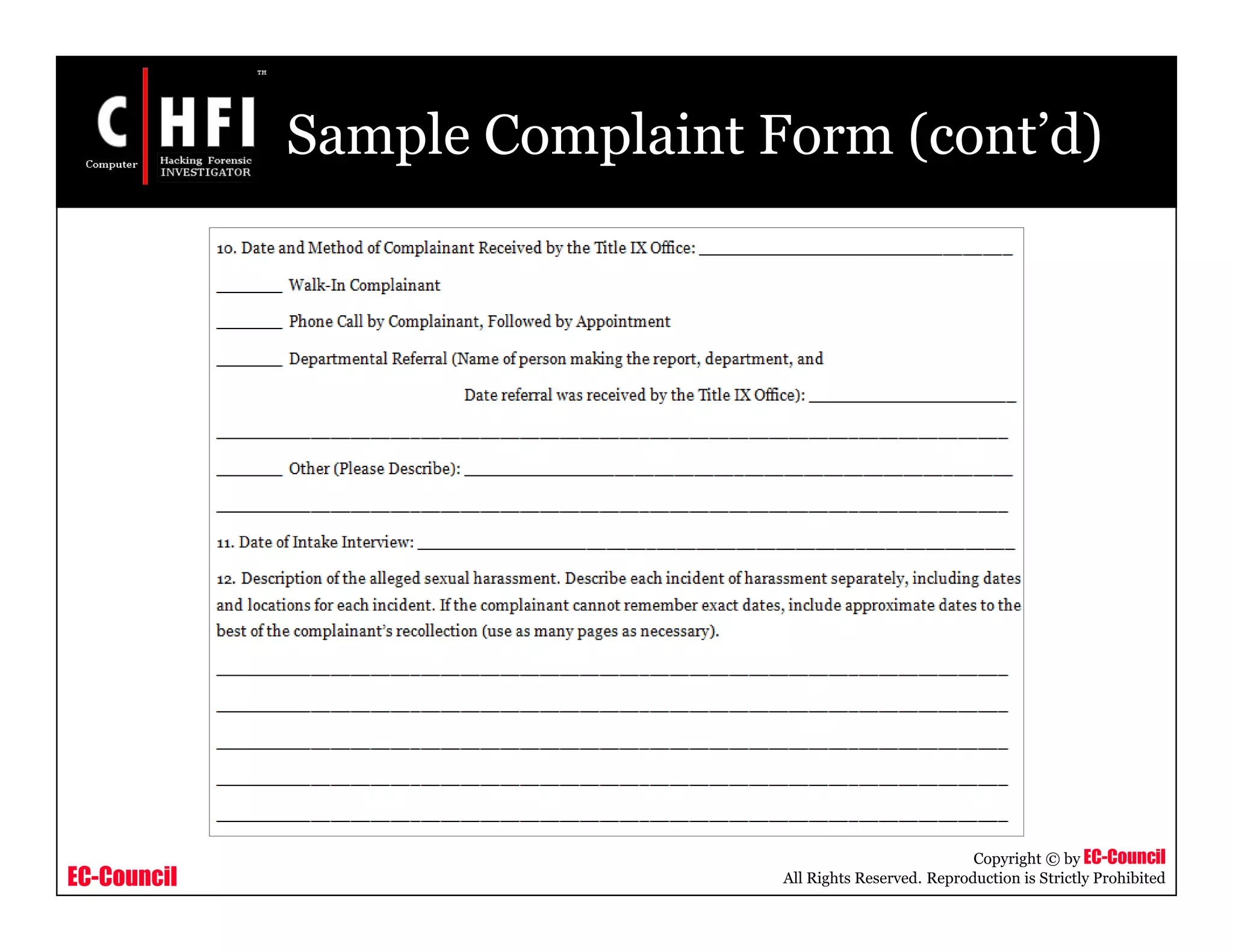
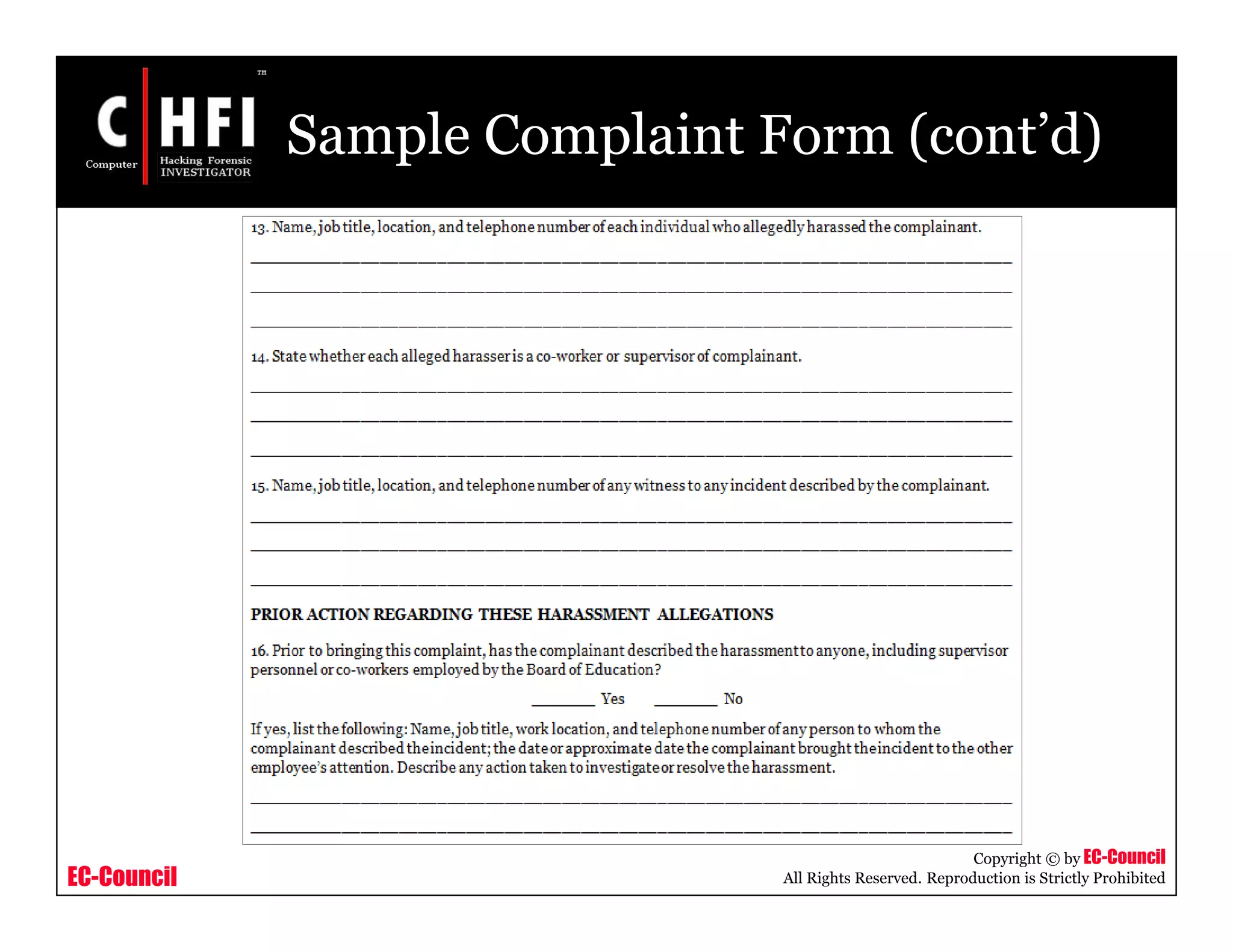
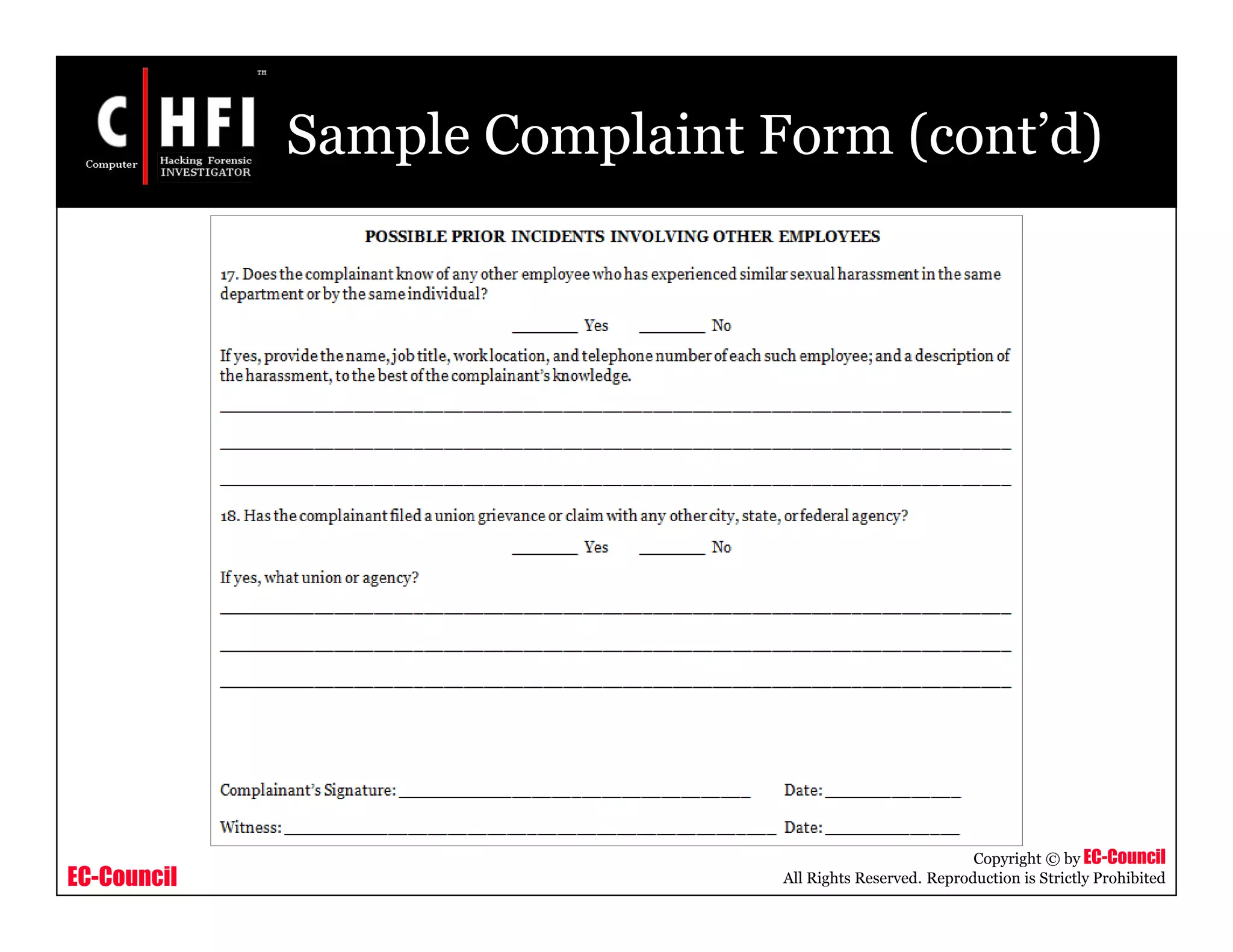
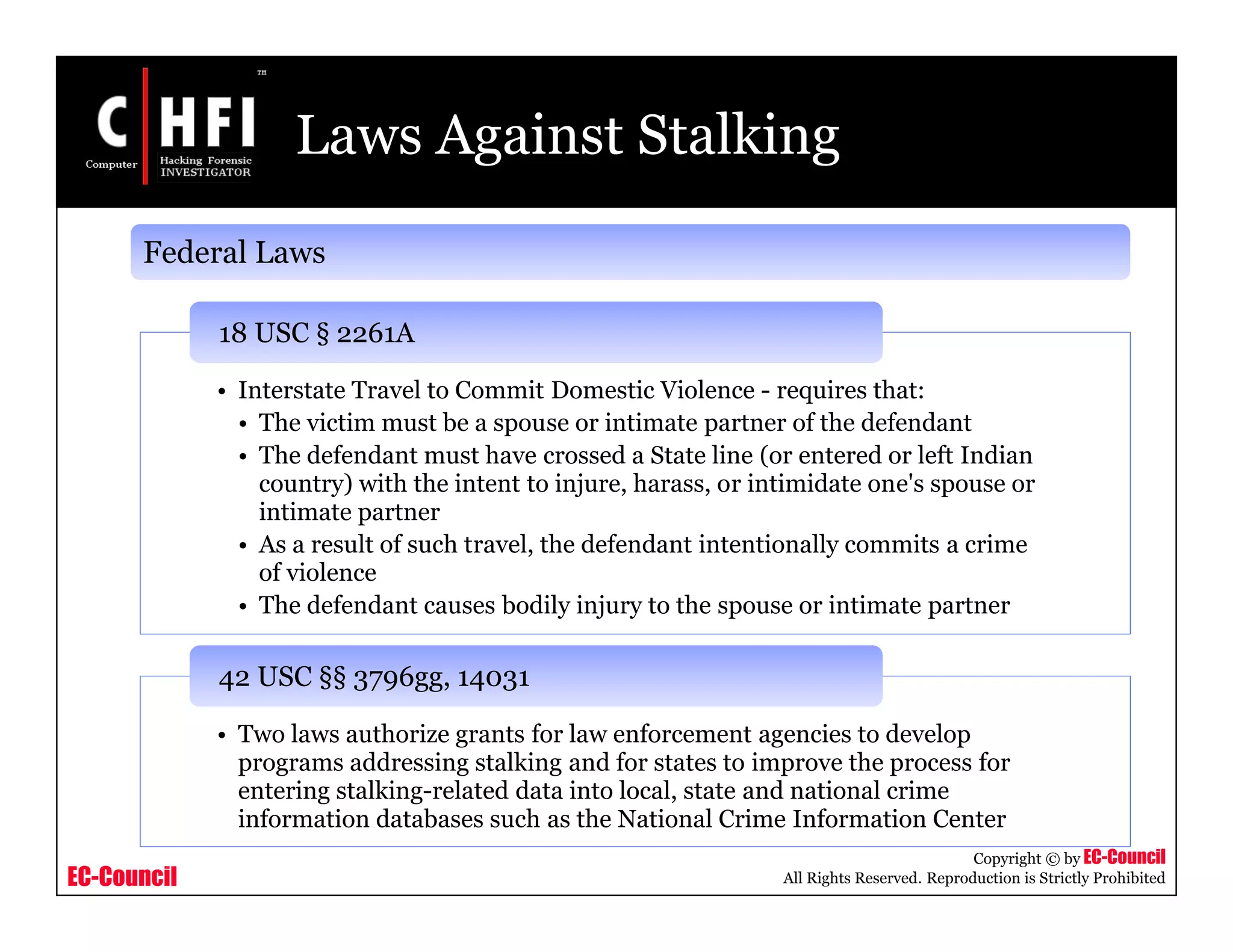
This document provides information on investigating sexual harassment incidents. It discusses types of sexual harassment like quid pro quo and hostile work environment harassment. It outlines the investigation process including interviewing witnesses and victims. Responsibilities of supervisors and employees are defined, such as supervisors addressing complaints and employees reporting issues. The document also discusses stalking behaviors and effects. Laws prohibiting sexual harassment are referenced, such as Title VII of the Civil Rights Act.