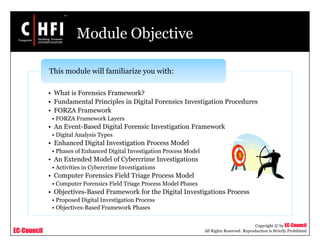
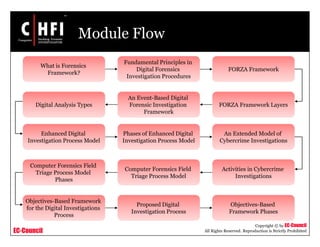
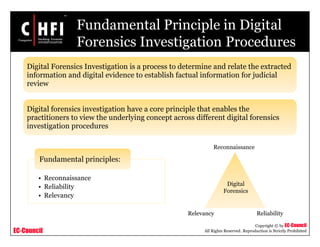
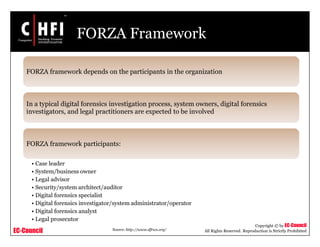
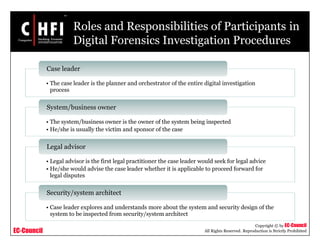
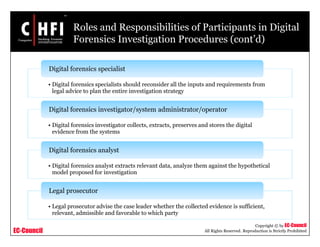
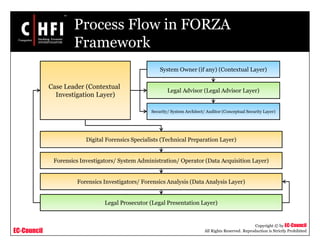
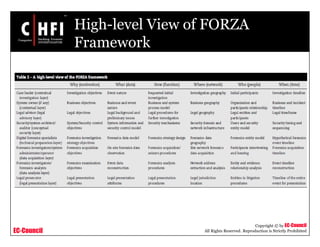
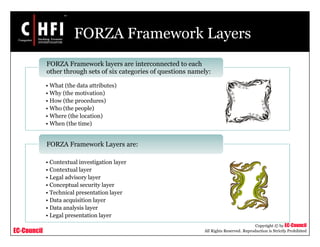
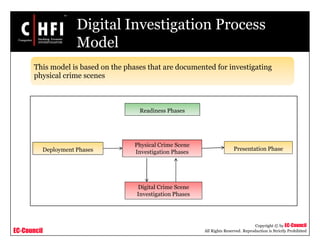
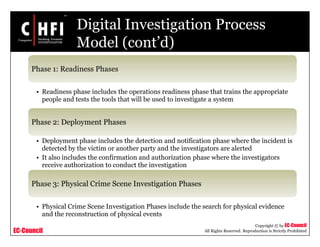
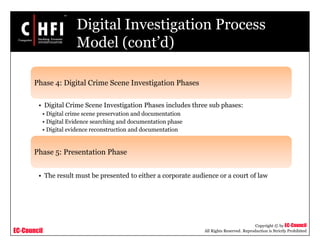
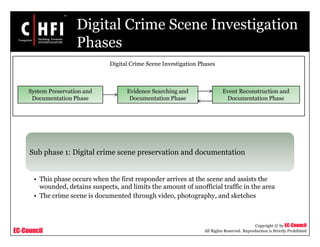
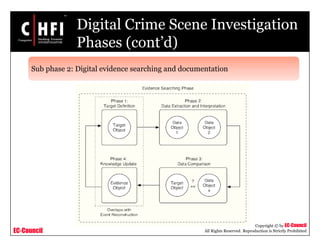
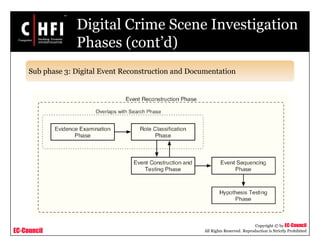
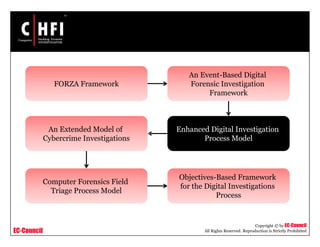
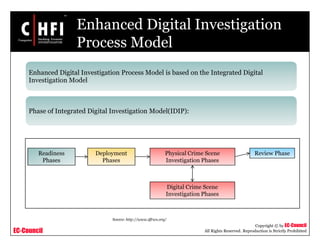
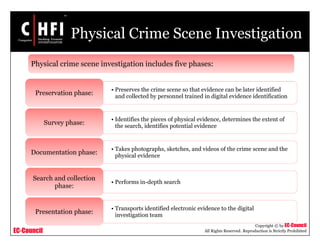
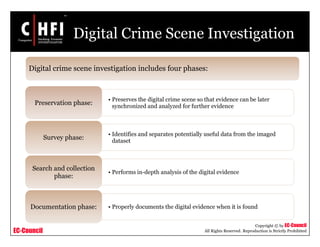
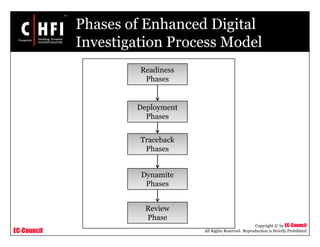
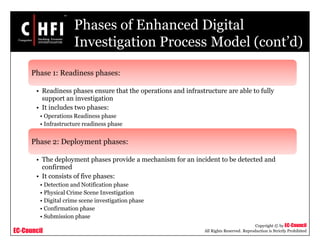
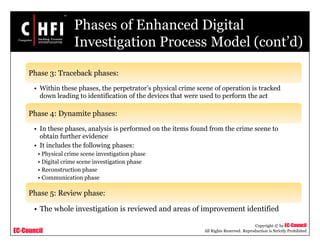
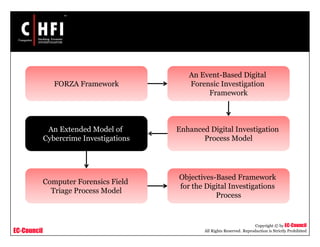
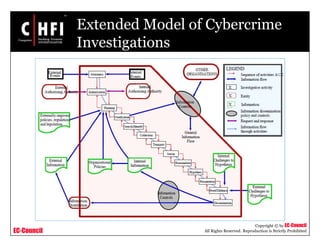
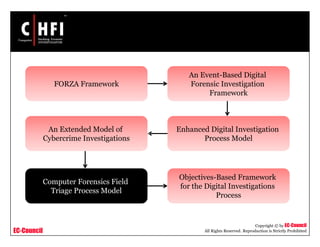
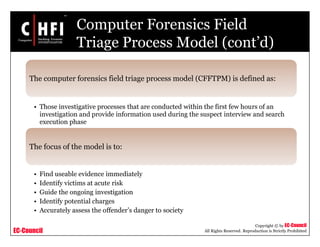
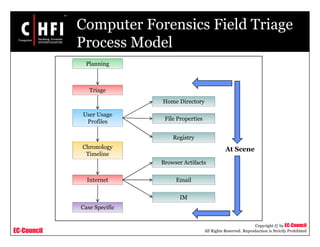
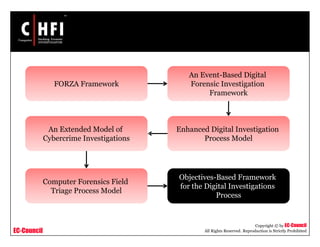
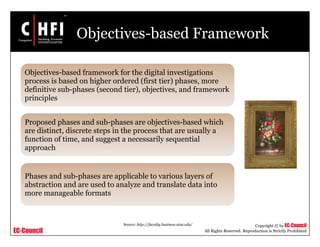
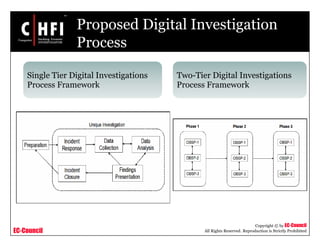
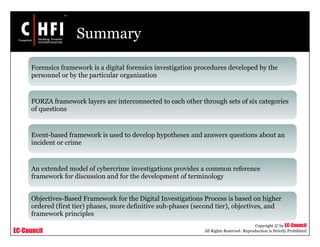
The document discusses several digital forensics frameworks that outline procedures for conducting digital investigations. It describes the FORZA framework in detail, which includes different layers representing contextual information, legal considerations, technical preparations, data acquisition, analysis, and legal presentation. Other frameworks covered include an enhanced digital investigation process model, an event-based digital forensic investigation framework, and a computer forensics field triage process model. Key phases of each framework, such as readiness, deployment, physical crime scene investigation, and digital crime scene investigation are also outlined.