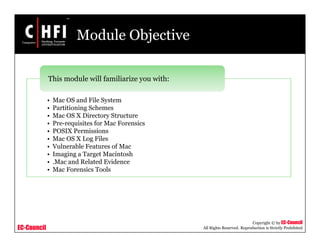
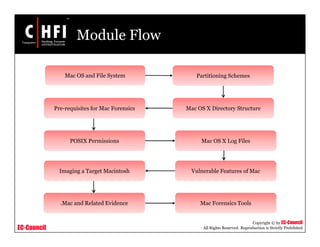
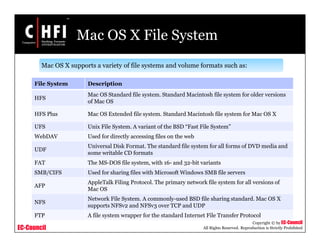
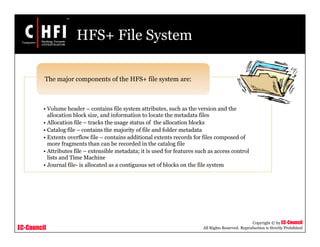
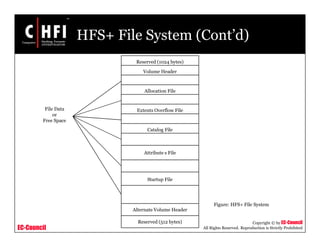
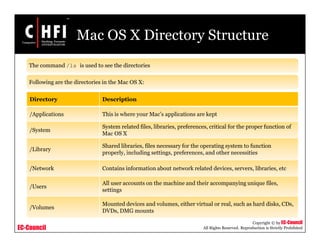
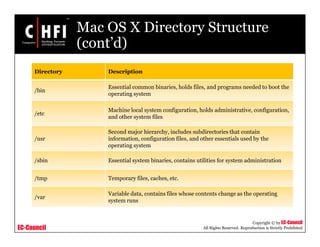
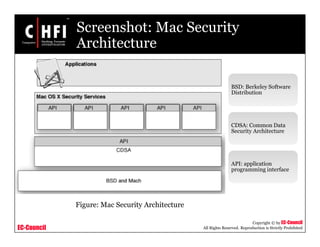
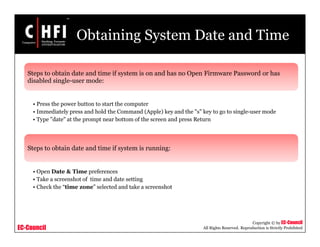
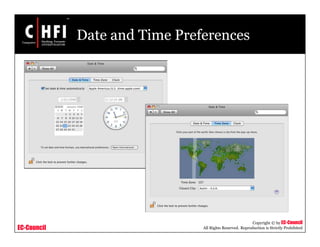
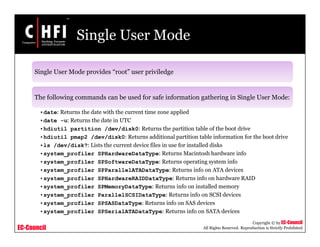
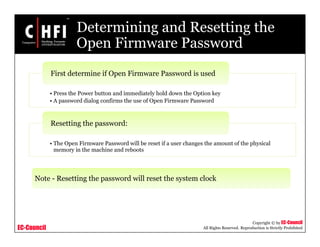
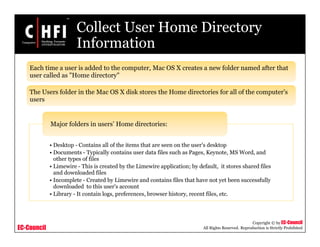
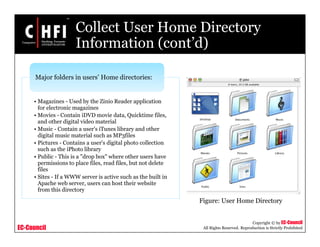
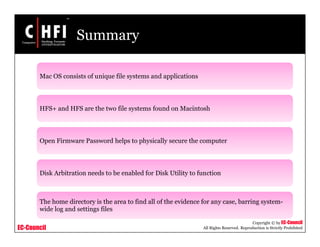
This document provides an overview of Mac forensics. It discusses the Mac OS file system and directory structure. It also outlines the prerequisites for performing Mac forensics, including how to obtain the system date and time either from single-user mode or from preferences. Specific commands that can be run in single-user mode for safely gathering information are also provided.