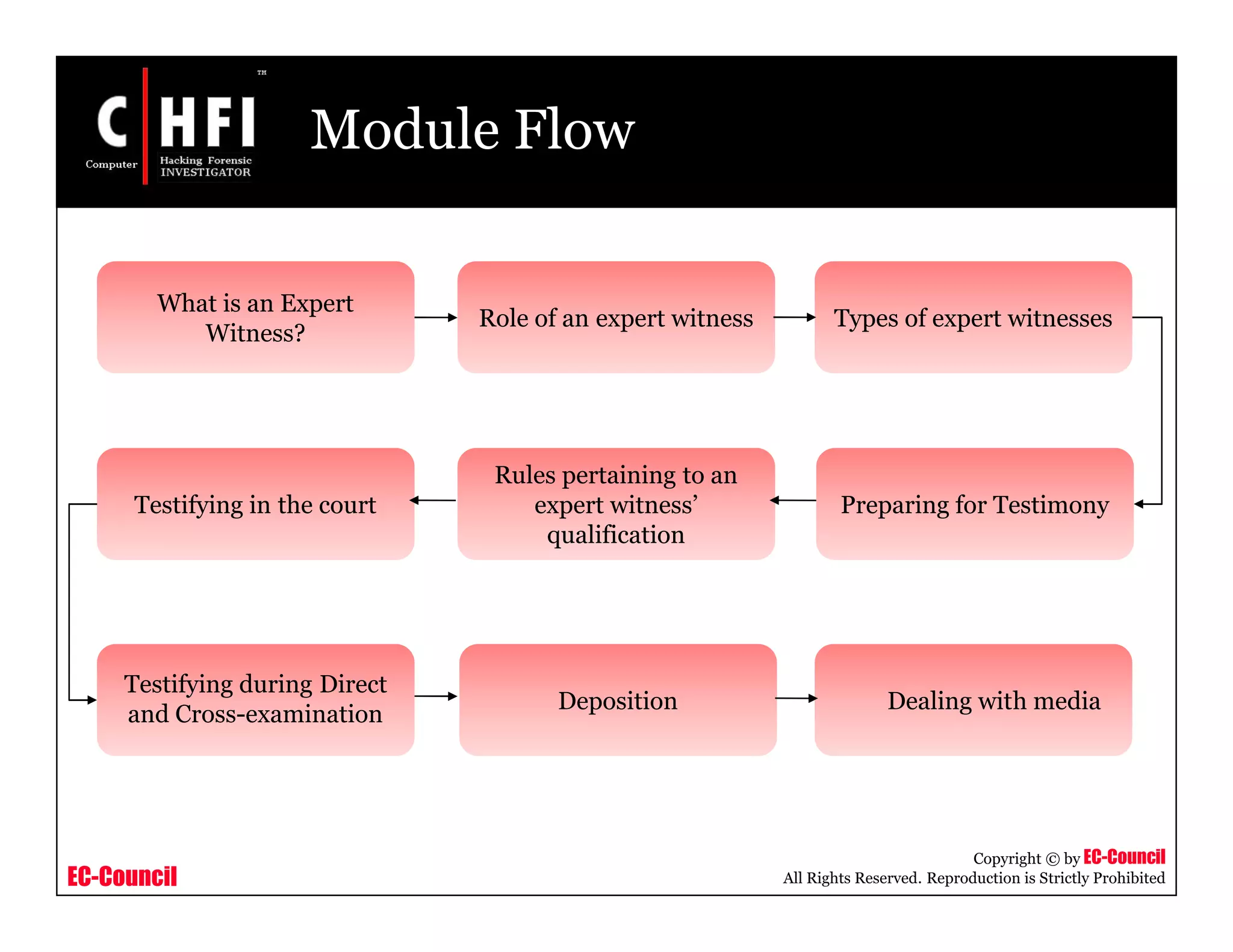
An expert witness testified in a court case involving a teacher accused of sexual relations with a student. The expert, a computer forensics officer, explained that activity seen on the teacher's computer was likely caused by automatic programs and weather programs, not tampering as the defense suggested. If the computer had been turned back on after seizure, there would have been evidence of that, but there was none. The document then discusses the role of expert witnesses and preparing for testimony in court cases.