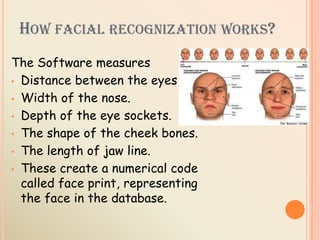
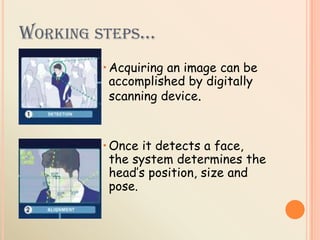
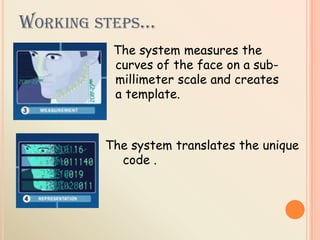
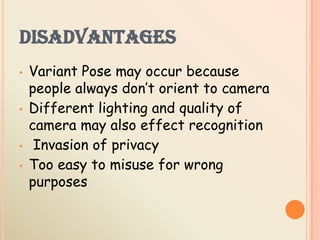
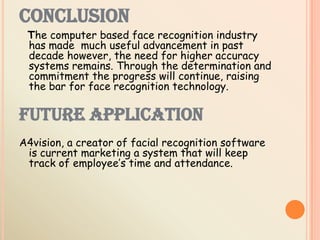
This document provides an overview of facial recognition technology. It discusses how facial recognition works by measuring distinguishing features of the face. It covers 2D and 3D facial recognition, with 3D providing more accuracy. The document outlines the basic steps 3D facial recognition systems use to verify identity, including acquiring an image, determining head position/size, measuring facial curves to create a template, and matching templates. It also discusses the technology's advantages in identification, current and future applications, and some disadvantages regarding variations in poses, lighting and privacy issues.