Embed presentation
Downloaded 17 times
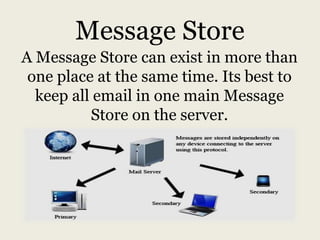
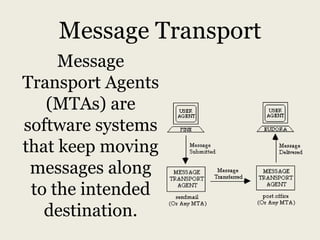
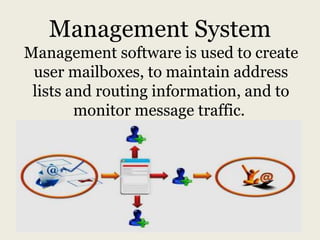
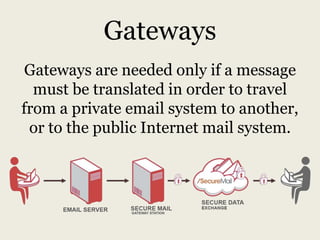

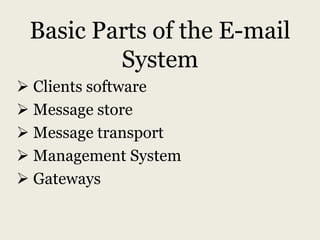
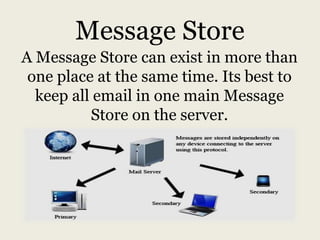
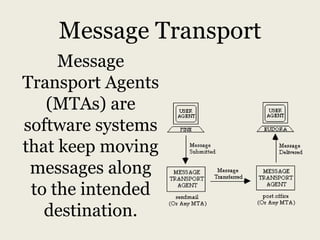
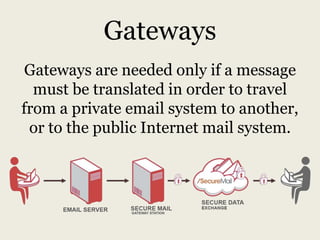
Email is the electronic transmission of messages over networks, functioning similarly to traditional mail but utilizing digital formats. The e-mail system consists of client software, message stores, message transport agents, management systems, and gateways for message delivery. Each component plays a crucial role in sending and receiving electronic messages efficiently.