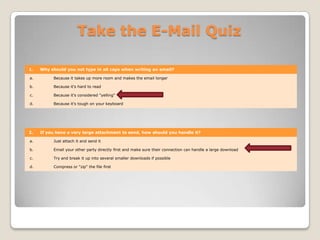
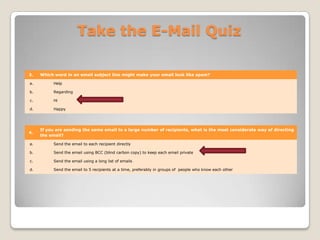
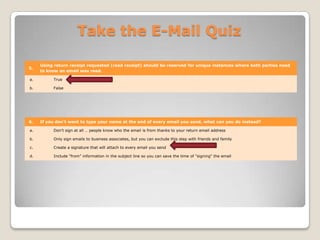
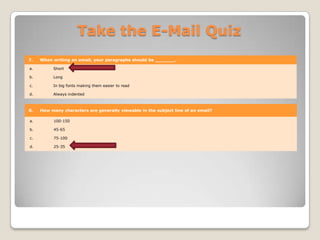
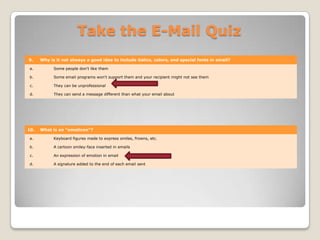
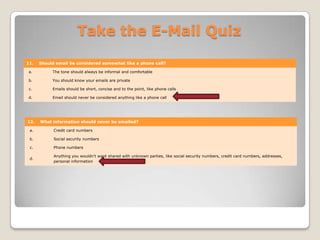
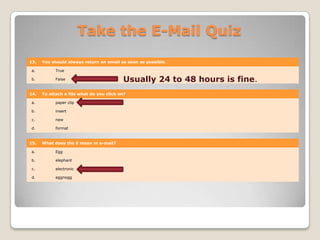
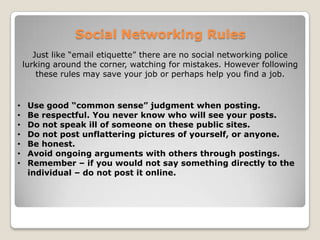
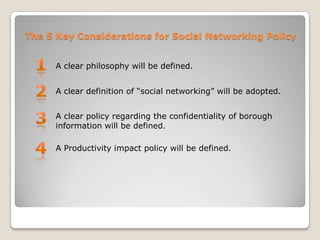
This document summarizes an information technology training session on email etiquette and social networks. It provides 18 rules of email etiquette, such as only discussing public matters, avoiding anger emails, and responding in a timely manner. It also discusses organizing emails and potentially moving email to the cloud for cost savings and security. Finally, it outlines rules for appropriate social media use, noting employers may check profiles, and indicates a borough social media policy is being developed addressing confidentiality and productivity.