Report
Share
Recommended
Image segmentation

Image segmentation - regional segmentation.
Regional Growing.
Region split & merging
Morphological Watersheds - use markers
Motion Segmentation.
Edge Detection algorithm and code

Basics, different types, different operators and results of algorithm and code of Edge Detection
Basics of edge detection and forier transform

These slides presents simple basics of edge detection and fourier transform in context of image processing
Recommended
Image segmentation

Image segmentation - regional segmentation.
Regional Growing.
Region split & merging
Morphological Watersheds - use markers
Motion Segmentation.
Edge Detection algorithm and code

Basics, different types, different operators and results of algorithm and code of Edge Detection
Basics of edge detection and forier transform

These slides presents simple basics of edge detection and fourier transform in context of image processing
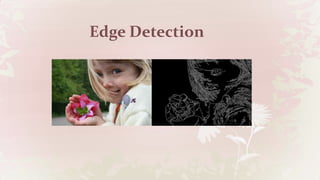
EDGE DETECTION

Edge detection is the name for a set of mathematical methods which aim at identifying points in a digital image at which the image brightness changes sharply or, more formally, has discontinuities.
IMAGE SEGMENTATION.

THIS PRESENTATION IS AN INTRODUCTORY APPROACH TO IMAGE SEGMENTATION.IT INCLUDES ITS APPLICATION,TECHNIQUES,ETC.
Image feature extraction

Image feature extraction and it's pipeline. Feature detection , description and matching. Image pre-processing.
Image Interpolation Techniques with Optical and Digital Zoom Concepts

re-sizing image by using interpolation methods
Image segmentation

Image segmentation is an important image processing step, and it is used everywhere if we want to analyze what is inside the image. Image segmentation, basically provide the meaningful objects of the image.
Active contour segmentation

Learn about Active contour segmentation in MATLAB.
A simple and lucid way to understand image segmentation using examples with MATLAB code.
Color image processing Presentation

Color Image Processing
Reference :Rafael C. Gonzalez and Richard E.
Wood, Digital Image Processing, 2nd Edition.
Edge Drawing - An Heuristic Approach to Robust Real-Time Edge Detection

Presentation of ED Algorithm.
Real time Canny edge detection

Seminar report for the fulfillment of B.Tech final year. Digital image processing subject seminar report.
More Related Content
What's hot
EDGE DETECTION

Edge detection is the name for a set of mathematical methods which aim at identifying points in a digital image at which the image brightness changes sharply or, more formally, has discontinuities.
IMAGE SEGMENTATION.

THIS PRESENTATION IS AN INTRODUCTORY APPROACH TO IMAGE SEGMENTATION.IT INCLUDES ITS APPLICATION,TECHNIQUES,ETC.
Image feature extraction

Image feature extraction and it's pipeline. Feature detection , description and matching. Image pre-processing.
Image Interpolation Techniques with Optical and Digital Zoom Concepts

re-sizing image by using interpolation methods
Image segmentation

Image segmentation is an important image processing step, and it is used everywhere if we want to analyze what is inside the image. Image segmentation, basically provide the meaningful objects of the image.
Active contour segmentation

Learn about Active contour segmentation in MATLAB.
A simple and lucid way to understand image segmentation using examples with MATLAB code.
Color image processing Presentation

Color Image Processing
Reference :Rafael C. Gonzalez and Richard E.
Wood, Digital Image Processing, 2nd Edition.
What's hot (20)
Image Interpolation Techniques with Optical and Digital Zoom Concepts

Image Interpolation Techniques with Optical and Digital Zoom Concepts
Similar to Edge Detection
Edge Drawing - An Heuristic Approach to Robust Real-Time Edge Detection

Presentation of ED Algorithm.
Real time Canny edge detection

Seminar report for the fulfillment of B.Tech final year. Digital image processing subject seminar report.
195706916 i journals-paper-template-2013

homework help,online homework help,online tutors,online tutoring,research paper help,do my homework,
https://www.homeworkping.com/
X-Ray Image Acquisition and Analysis

ABSTRACT
Medical images are pictures of distributions of physical attributes captured by an image acquisition system. Most of today’s images are digital. They may be post processed for analysis by a computer-assisted method. Edges are important features in an image. Edge detection extracts salient features from an image such as corners, lines and curves. These features are used by higher level computer vision algorithms. Segmentation plays a crucial role in extraction of useful information and attributes from medical images. Different edge detection methods are applied on dental images. It is implemented using MATLAB.
Keywords – Edge Detection, Dental Image, Canny
Edge detection iOS application

Edge detection is the name for a set of mathematical methods which aim at identifying points in a digital image at which the image brightness changes sharply or, more formally, has discontinuities.
Edge Detection and Segmentation

Different edge detection and segmentation techniques are descibed here.
Study and Comparison of Various Image Edge Detection Techniques

Edges characterize boundaries and are therefore a problem of fundamental importance in image processing. Image Edge detection significantly reduces the amount of data and filters out useless information, while preserving the important structural properties in an image. Since edge detection is in the forefront of image processing for object detection, it is crucial to have a good understanding of edge detection algorithms. In this paper the comparative analysis of various Image Edge Detection techniques is presented. The software is developed using MATLAB 7.0. It has been shown that the Canny’s edge detection algorithm performs better than all these operators under almost all scenarios. Evaluation of the images showed that under noisy conditions Canny, LoG( Laplacian of Gaussian), Robert, Prewitt, Sobel exhibit better performance, respectively. . It has been observed that Canny’s edge detection algorithm is computationally more expensive compared to LoG( Laplacian of Gaussian), Sobel, Prewitt and Robert’s operator
Enhanced Optimization of Edge Detection for High Resolution Images Using Veri...

dge Detection plays a crucial role in Image Processing and Segmentation where a set of algorithms aims
to identify various portions of a digital image at which a sharpened image is observed in the output or
more formally has discontinuities. The contour of Edge Detection also helps in Object Detection and
Recognition. Image edges can be detected by using two attributes such as Gradient and Laplacian. In our
Paper, we proposed a system which utilizes Canny and Sobel Operators for Edge Detection which is a
Gradient First order derivative function for edge detection by using Verilog Hardware Description
Language and in turn compared with the results of the previous paper in Matlab. The process of edge
detection in Verilog significantly reduces the processing time and filters out unneeded information, while
preserving the important structural properties of an image. This edge detection can be used to detect
vehicles in Traffic Jam, Medical imaging system for analysing MRI, x-rays by using Xilinx ISE Design
Suite 14.2.
YCIS_Forensic_Image Enhancement and Edge detection.pptx

Forensic_Image Enhancement and Edge detection
ALGORITHM AND TECHNIQUE ON VARIOUS EDGE DETECTION: A SURVEY

An edge may be defined as a set of connected pixels that forms a boundary between two disjoints regions.
Edge detection is basically, a method of segmenting an image into regions of discontinuity. Edge detection
plays an important role in digital image processing and practical aspects of our life. .In this paper we
studied various edge detection techniques as Prewitt, Robert, Sobel, Marr Hildrith and Canny operators.
On comparing them we can see that canny edge detector performs better than all other edge detectors on
various aspects such as it is adaptive in nature, performs better for noisy image, gives sharp edges , low
probability of detecting false edges etc
Digital Image Processing

Fundamental concepts and basic techniques of digital image processing. Algorithms and recent research in image transformation, enhancement, restoration, encoding and description. Fundamentals and basic techniques of pattern recognition.
Comparative Analysis of Common Edge Detection Algorithms using Pre-processing...

Edge detection is the process of segmenting an image by detecting discontinuities in brightness. Several standard segmentation methods have been widely used for edge detection. However, due to inherent quality of images, these methods prove ineffective if they are applied without any preprocessing. In this paper, an image pre-processing approach has been adopted in order to get certain parameters that are useful to perform better edge detection with the standard edge detection methods. The proposed preprocessing approach involves median filtering to reduce the noise in image and then edge detection technique is carried out. Finally, Standard edge detection methods can be applied to the resultant pre-processing image and its Simulation results are show that our pre-processed approach when used with a standard edge detection method enhances its performance.
Fuzzy Logic Based Edge Detection

This Algorithm is better than canny by 0.7% but lacks the speed and optimization capability which can be changed by including Neural Network and PSO searching to the same.
This used dual FIS Optimization technique to find the high frequency or the edges in the images and neglect the lower frequencies.
Similar to Edge Detection (20)
Edge Drawing - An Heuristic Approach to Robust Real-Time Edge Detection

Edge Drawing - An Heuristic Approach to Robust Real-Time Edge Detection
Exploring Methods to Improve Edge Detection with Canny Algorithm

Exploring Methods to Improve Edge Detection with Canny Algorithm
Study and Comparison of Various Image Edge Detection Techniques

Study and Comparison of Various Image Edge Detection Techniques
Enhanced Optimization of Edge Detection for High Resolution Images Using Veri...

Enhanced Optimization of Edge Detection for High Resolution Images Using Veri...
YCIS_Forensic_Image Enhancement and Edge detection.pptx

YCIS_Forensic_Image Enhancement and Edge detection.pptx
Comparative study on image segmentation techniques

Comparative study on image segmentation techniques
ALGORITHM AND TECHNIQUE ON VARIOUS EDGE DETECTION: A SURVEY

ALGORITHM AND TECHNIQUE ON VARIOUS EDGE DETECTION: A SURVEY
Comparative Analysis of Common Edge Detection Algorithms using Pre-processing...

Comparative Analysis of Common Edge Detection Algorithms using Pre-processing...
IJCER (www.ijceronline.com) International Journal of computational Engineerin...

IJCER (www.ijceronline.com) International Journal of computational Engineerin...
Recently uploaded
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Recently uploaded (20)
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Edge Detection
- 2. What is Edge Detection? Identifying points/Edges in a digital image at which the image brightness changes sharply or has discontinuities. - Edges are significant local changes of intensity in an image. - Edges typically occur on the boundary between two different regions in an image.
- 3. Goal of edge detection Edge detection is extensively used in image segmentation when we want to divide the image into areas corresponding to different objects. If we need to extract different object from an image, we need Edge Detection Using Edge Detection, we can: - Produce a line drawing of a scene from an image of that scene. - Important features can be extracted from the edges of an image (e.g., corners, lines, curves). - These features are used by higher-level computer vision algorithms (e.g., recognition, Image comparizon ). Unaccepted object can be remove.
- 4. Process of Edge Detection Most of edge detection algorithm are based on one of two basic properties of intensity values: Discontinuity and similarity. Typically, there are three steps to perform edge detection: 1. Noise reduction 2. Edge enhancement 3. Edge localization
- 5. Process of Edge Detection (...) Noise reduction where we try to suppress as much noise as possible, without smoothing away the meaningful edges. Original Image After Nois Reduction
- 6. Process of Edge Detection (...) Edge enhancement where we apply some kind of filter that responds strongly at edges and weakly elsewhere, so that the edges may be identified as local maxima in the filter’s output . One suggestion is to use some kind of high pass filter.
- 7. Process of Edge Detection (...) Edge localization where we decide which of the local maxima output by the filter are meaningful edges and which are caused by noise
- 8. Process of Edge Detection (...) There are many algorithm for Edge Detection. Some are: Robert's edge detector Prewitt edge detector Sobel edge detector Frie Chen edge detector Canny edge detector Canny edge detector is giving best output, I am going to explain Canny edge detector.
- 9. Canny Edge Detector Canny Edge Detector is complex and uses a multi-stage algorithm to detect a wide range of edges in images. It is most commonly implemented edge detection algorithm. It has three basic objectives: Low error rate Edge points should be well localized Single edge point response
- 10. Canny Edge Detector As I mention before, canny edge detector have multiple algorithm. It have 5 steps, those are: Image Smoothing Gradient Operation Nonmaxima Suppression Hysteresis Thresholding Connectivity Analysis
- 11. Canny Edge Detector Image Smoothing Reduce image noise by smoothing with a Gaussian The choice of σ depends on desired behavior large σ detects large scale edges small σ detects fine features The larger the width of the Gaussian mask, the lower is the detector's sensitivity to noise.
- 13. Canny Edge Detector Nonmaxima Suppression Nonmaxima Suppression reduce thick edge strength responses around true edges select the single maximum point across the width of an edge. is used to trace along the edge in the edge direction and suppress any pixel value (sets it equal to 0) that is not considered to be an edge. This will give a thin line in the output image.
- 14. Canny Edge Detector Hysteresis Thresholding Large intensity gradients are more likely to correspond to edges than small intensity gradients. It is in most cases impossible to specify a threshold at which a given intensity gradient switches from corresponding to an edge into not doing so. Therefore Canny uses thresholding with hysteresis. Thresholding with hysteresis requires two thresholds – high and low. Select two thresholds TH and TL such that 0 6 TL < TH 6 255 Create two new binary 2-D arrays • gNH(x; y) = gN(x y) > TH • gNL(x; y) = gN(x y) > TL Eliminate from gNL(x; y) all the nonzero pixels from gNH(x y) After this operation • gNH(x y) will contain only the strong edge points • gNL(x y) will contain only the weak edge points • They will not contain common points Ratio of TH to TL should be 2 : 1 or 3 : 1
- 15. Canny Edge Detector Connectivity Analysis After step #4, gNH(x y) will contain the strong edge pixels { thus are valid edge pixels. However, there will be discontinuity in the edges. Longer edges are formed using the following procedure: 1 Add all the edge pixels in gNH(x y) to a list L 2 Do until there are more edge pixels in L • Locate the next unvisited edge pixel, p • Mark as valid edge pixels all the weak pixels in gNL(x y) that are connected to p (8 neighbors) • Remove p from L 3 Set to zero all pixels in gNL(x y) that were not marked as valid edge pixels 4 Combine all nonzero pixels in gNH(x y) and gNL(x y ) to find the final edge pixels Analysis
- 16. Canny Edge Detector Visually all steps
- 17. ?
- 18. Thank you! Jakir Hossain. ID: CSE-24th Batch. Southeast University.
