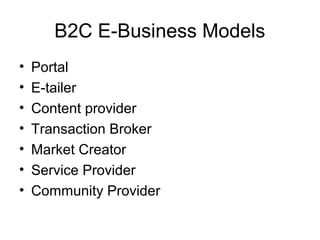
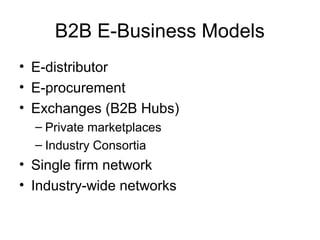
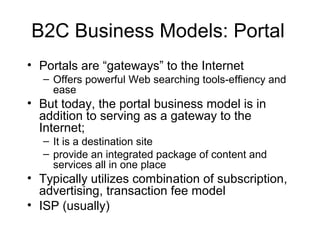
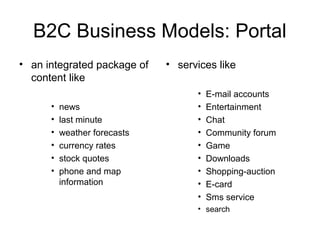
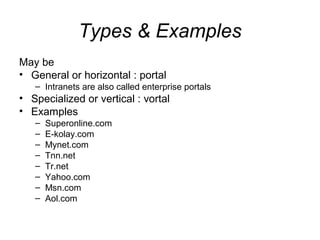
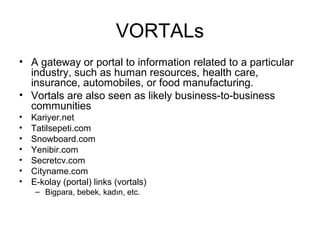
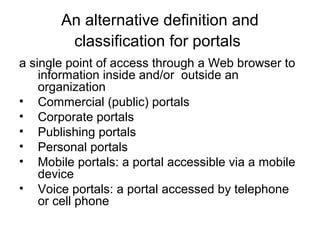
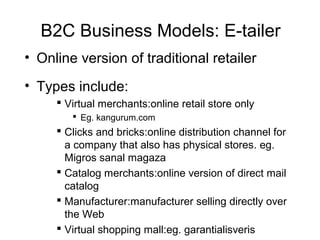
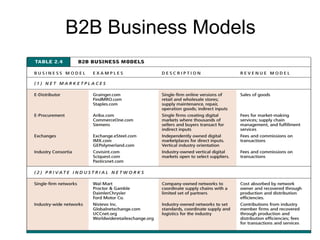
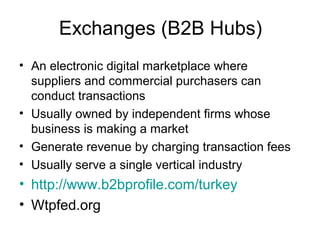
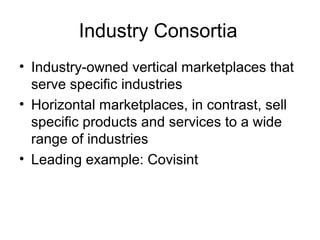
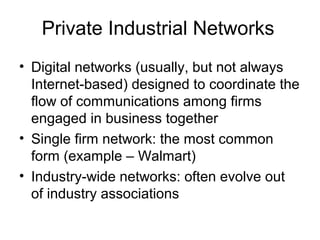
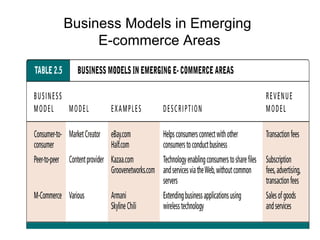
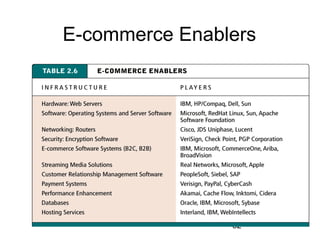
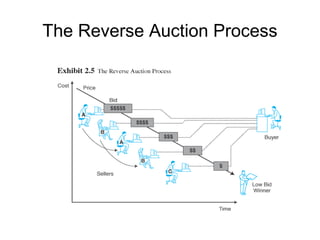
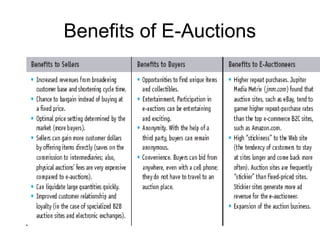
This document discusses various e-commerce business models, including B2C and B2B models. For B2C, it describes portal, e-tailer, content provider, transaction broker, market creator, service provider, and community provider models. For B2B, it discusses e-distributor, e-procurement, exchanges, and industry-wide networks. It also covers emerging models like C2C, P2P, and e-commerce enablers. Auctions are discussed as an online market mechanism where sellers offer goods and buyers bid until a final price is reached.