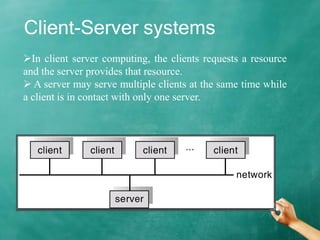
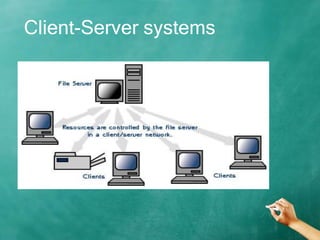
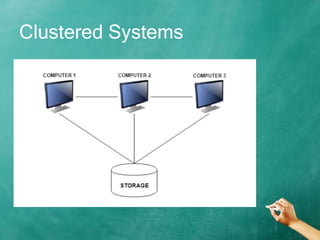
This document discusses distributed and clustered systems. It defines distributed systems as systems composed of independent computers that communicate over a network. Distributed systems can be client-server systems, where clients request resources from servers, or peer-to-peer systems, where users share resources directly. Clustered systems combine independent computers and shared storage to work together. They provide benefits like high performance, fault tolerance, and scalability.