Embed presentation
Downloaded 26 times


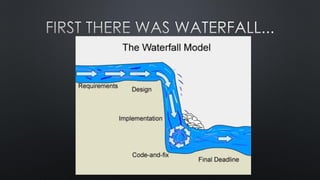




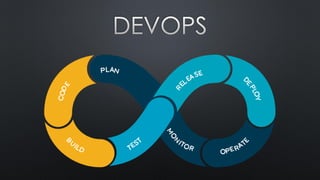


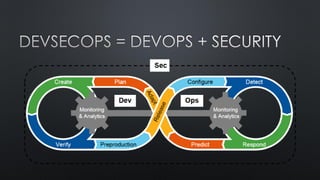
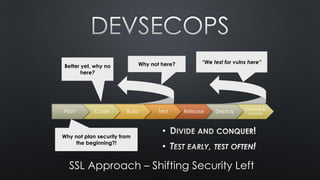

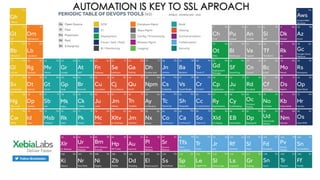


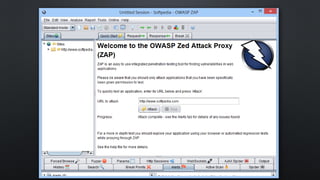





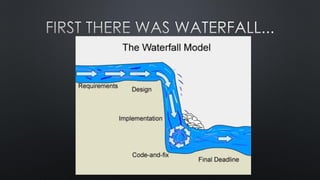
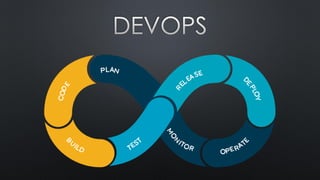
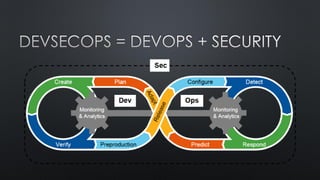
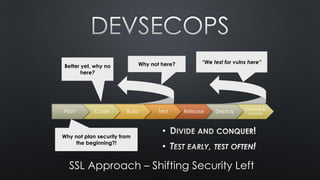
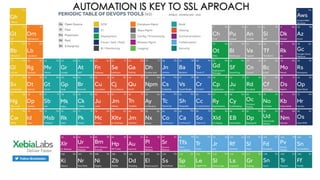
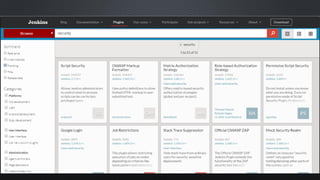
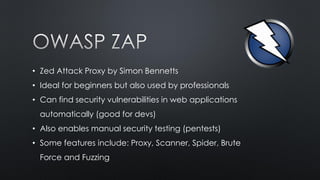
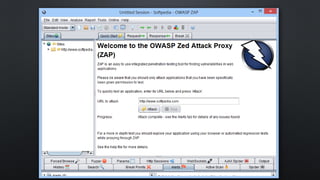
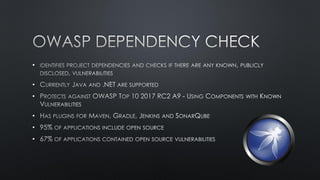
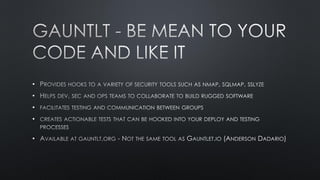
The document discusses shifting security left in the software development lifecycle using an agile approach and automation tools. It recommends planning security from the beginning of the development process. Automation is key to continuously test for vulnerabilities during integration and development. Tools mentioned include an open source CI server to detect errors, Zed Attack Proxy to automatically find web application vulnerabilities, and various resources on securing the DevOps pipeline.