The document outlines objectives for day 1 of a training on network security and hacking techniques, including hardening Linux and Windows 2000 systems, analyzing software vulnerabilities and attacking techniques, and discussing elements of network security like confidentiality, integrity, availability, and models for access control. It also provides details on installation and configuration of Linux operating systems for network security.









































![How to use RPM Commands
• To install a RPM package, use the command:
[root@testing /]# rpm -ivh foo-1.0-2.i386.rpm
• To uninstall a RPM package, use the command:
[root@testing /]# rpm -e foo
• To upgrade a RPM package, use the command:
[root@testing /]# rpm -Uvh foo-1.0-2.i386.rpm
• To query a RPM package, use the command:
[root@testing /]# rpm -q foo
• To check a RPM signature package, use the
command:
[root@testing /]# rpm --checksig foo
Network Security and Hacking Techniques – DAY1](https://image.slidesharecdn.com/day1-090721102657-phpapp02/85/Day1-43-320.jpg)
![Starting and stopping daemon services
• To start the httpd Web Server manually under Linux.
[root@testing /]# /etc/rc.d/init.d/httpd start
Starting httpd: [ OK ]
• To stop the httpd Web Server manually under Linux.
[root@testing /]# /etc/rc.d/init.d/httpd stop
Shutting down http: [ OK ]
• To restart the httpd Web Server manually under
Linux.
[root@testing /]# /etc/rc.d/init.d/httpd restart
Shutting down http: [ OK ]
Starting httpd: [ OK ]
Network Security and Hacking Techniques – DAY1](https://image.slidesharecdn.com/day1-090721102657-phpapp02/85/Day1-44-320.jpg)




























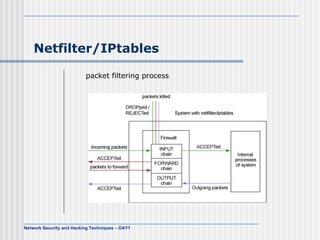
![Building rules and chains
Root# iptables [-t table] command [match] [target]
Tables: INPUT,OUTPUT,PREROUTING,POSTROUTING
Command: -A or –append
$ iptables -A INPUT -s 205.168.0.1 -j ACCEPT
-D or --delete
$ iptables -D INPUT --dport 80 -j DROP
-F or –flush
$ iptables -F
-L or --list
$ iptables -L
Network Security and Hacking Techniques – DAY1](https://image.slidesharecdn.com/day1-090721102657-phpapp02/85/Day1-77-320.jpg)















