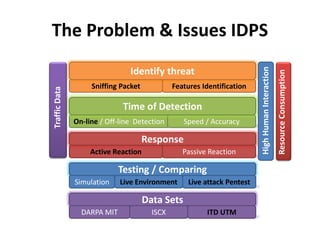
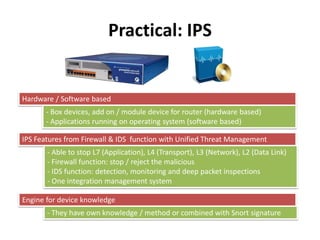
(1) The document discusses network attack and intrusion prevention systems. It describes how intrusion prevention systems (IPS) aim to detect and block threats in online traffic in real-time, beyond just detecting threats like intrusion detection systems (IDS).
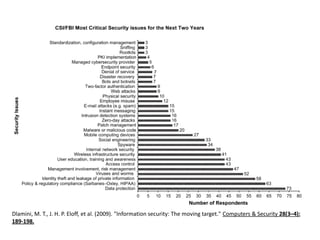
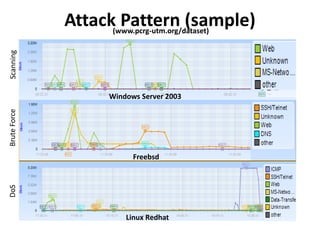
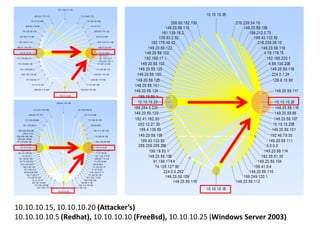
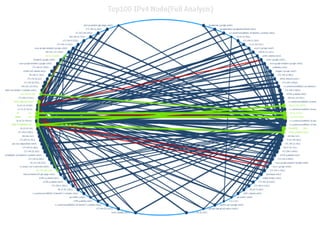
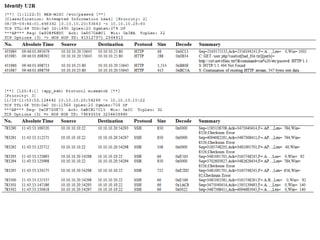
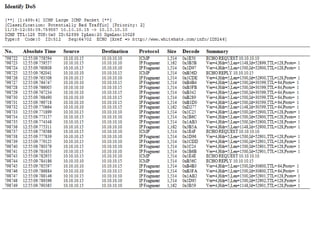
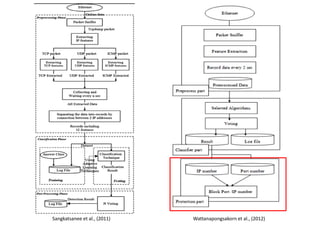
(2) Feature extraction from network traffic is important for IPS to analyze without being overwhelmed by raw data. The document examines relevant features to monitor and criteria for deciding what is important to track.
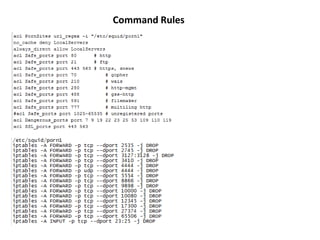
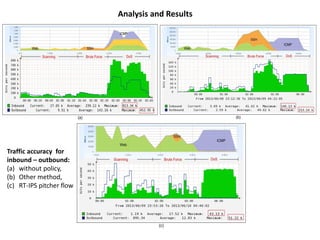
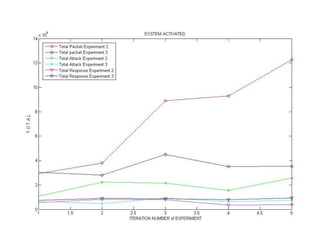
(3) Experimental testing is needed to evaluate IPS performance. The document outlines stages for training systems, testing methodsologies, and resuming test results. This helps IPS avoid unexpected outcomes and ensures continuous monitoring.