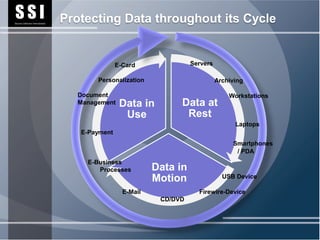
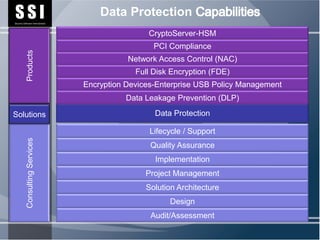
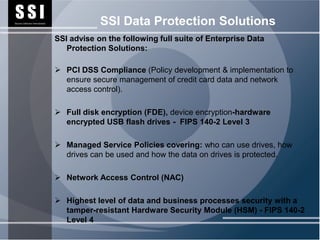
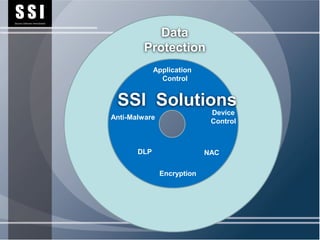
SSI provides data protection solutions to help organizations protect sensitive data throughout its lifecycle. SSI's solutions include consulting services, data leakage prevention, full disk encryption, network access control, encryption devices, and a hardware security module to provide the highest level of security. Implementing SSI's solutions can help organizations comply with privacy regulations and protect their reputation.