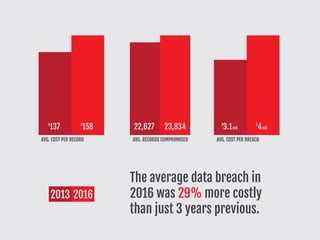
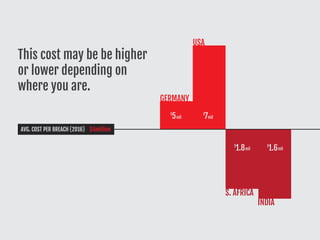
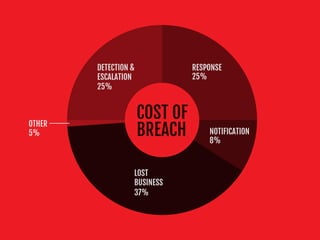
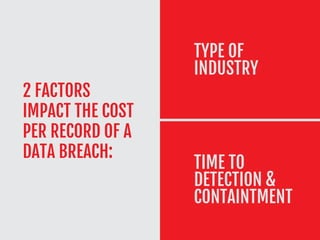
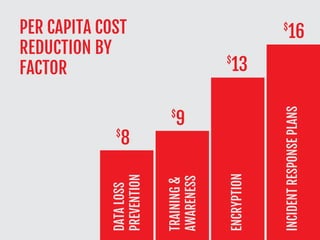
This document assesses the costs associated with data breaches, highlighting an average global cost of $4 million. It details the factors impacting these costs, such as the type of industry and time to detection, and outlines components of breach costs including detection, notification, and lost business. The document also emphasizes the importance of training IT teams and implementing security measures to significantly reduce the costs of breaches.