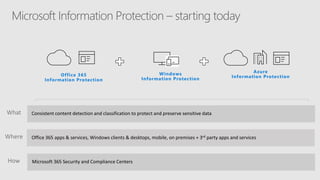
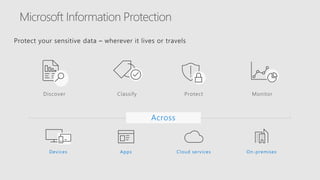
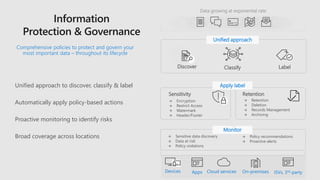
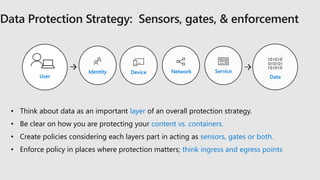
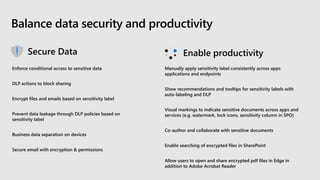
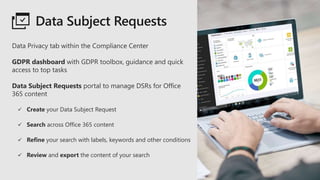
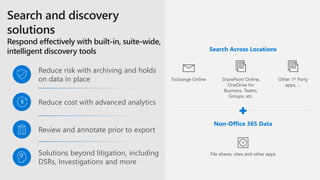
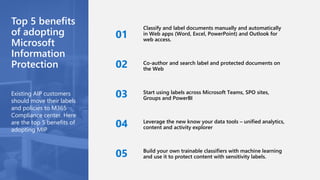
The Microsoft 365 Virtual Marathon, held on May 27-28, 2020, focused on topics such as Microsoft Information Protection and security compliance frameworks, featuring sessions led by industry experts. Attendees could engage in activities like raffles, vendor visits, and charity donations, with insights on protecting sensitive data across various platforms. The event highlighted the importance of comprehensive data protection policies and tools within the Microsoft 365 ecosystem to manage compliance and security challenges.