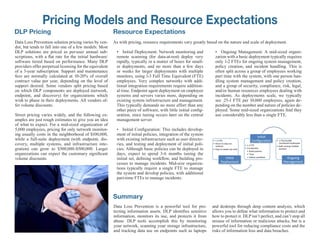
The document provides an overview of Data Loss Prevention (DLP) technologies designed to safeguard sensitive information while minimizing disruption to business processes. It outlines the importance of DLP in protecting digital assets, justifying investments based on risk reduction, policy enforcement, cost savings, compliance support, and security management. Additionally, it discusses the architecture of DLP systems, the deployment process, and key features that enable organizations to monitor and protect sensitive data effectively.