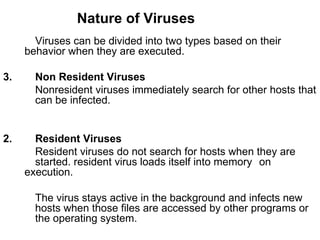
A computer virus is a malicious program that can copy itself and infect computers. It runs without the user's permission and can slow down computers or cause errors. Antivirus software uses virus signatures and heuristics to detect viruses and remove or quarantine infected files to disinfect computers. There are many types of viruses like boot, program, macro, and polymorphic viruses that infect different parts of a system. Antivirus software, system restore, reinstalling the operating system, and firewalls are some methods used for virus recovery and protection.