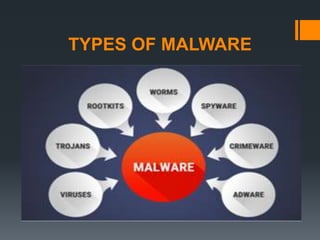
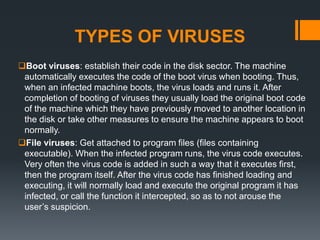
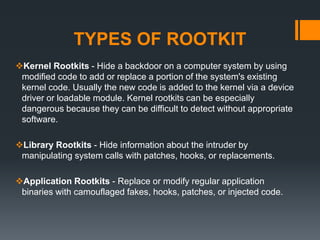
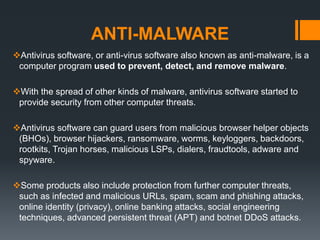
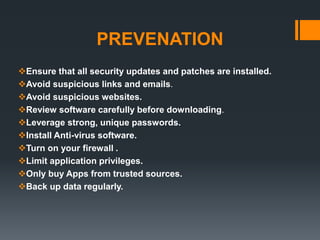
The document provides a comprehensive overview of malware, its various types including viruses, worms, trojans, spyware, adware, ransomware, and rootkits, explaining how each operates and the damage they can cause. It emphasizes the importance of anti-malware tools and outlines preventative measures individuals can take to protect their systems from these threats. Despite advancements in security measures, cyber criminals continue to evolve their tactics, making user vigilance crucial.