The document discusses several key topics related to computer systems:
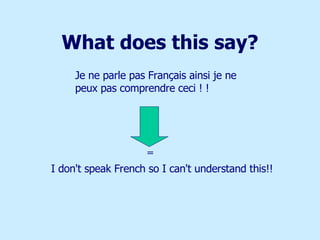
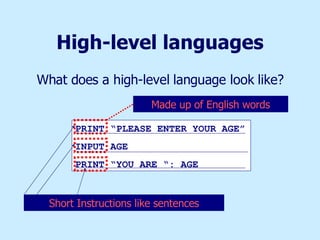
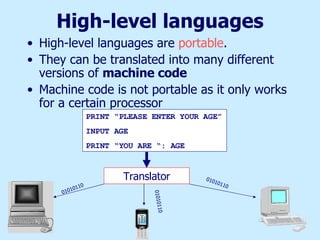
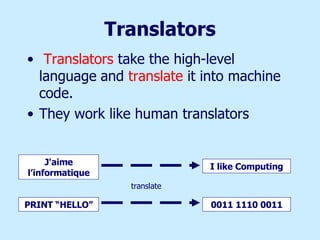
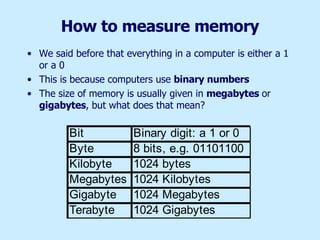
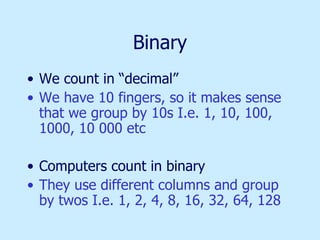
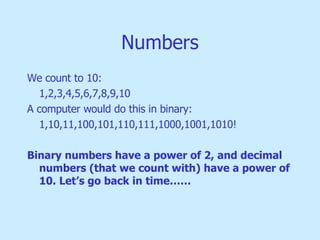
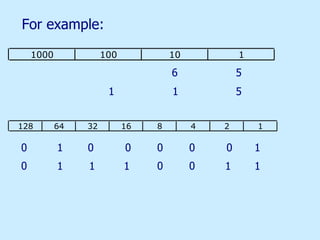
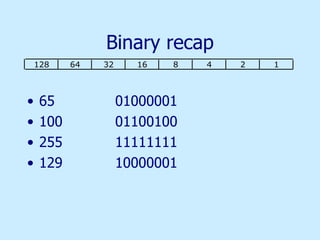
1. Computers only understand binary (1s and 0s) called machine code. Humans write programs in high-level languages that are translated into machine code.
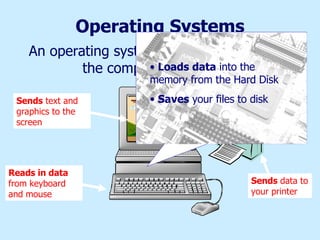
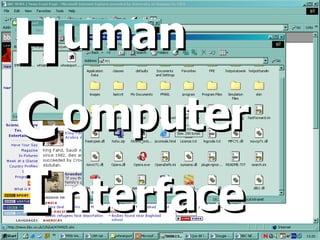
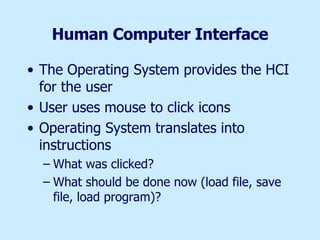
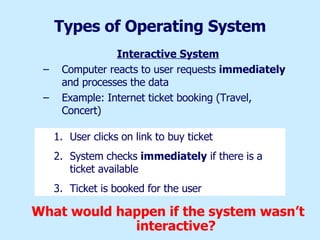
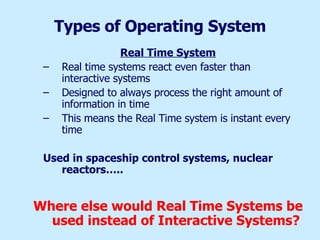
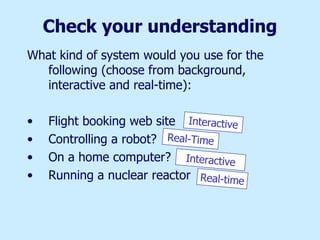
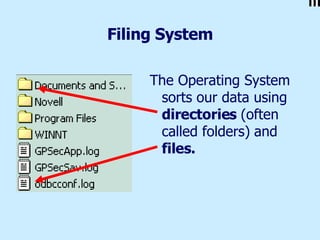
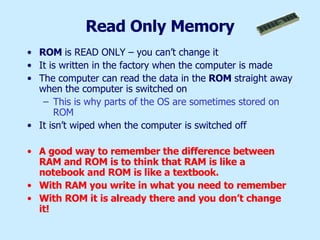
2. Operating systems control tasks like loading data, reading input/output, and saving files. They provide a human-computer interface (HCI).
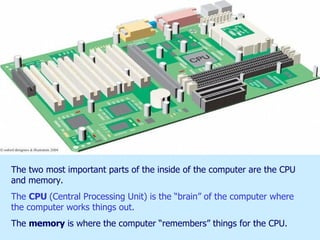
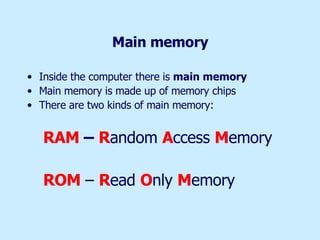
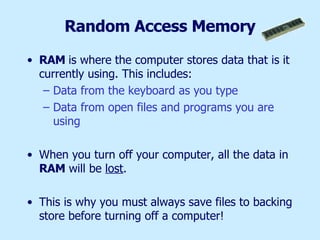
3. Files are either program files or data files used by programs. Memory stores active data (RAM) and permanent files (backing storage like hard disks).