The internship project report discusses the development and implementation of a Computer-Based Testing (CBT) platform, highlighting the limitations of traditional examination methods and the advantages of automation. It introduces TAO, an open-source e-assessment software that facilitates online testing with features like flexible timing, randomization of questions, and immediate feedback. The document includes installation procedures, system requirements, and contextual issues related to the use of computer-based assessments in educational settings.



![Internship Project Report
8
1.1 Motivation of the Project:
The paper and pen (manual) method of writing examination, which has been in existence for decades, may not be appealing for use because of the problems usually experienced including examination venue capacity constraints, lack of comfort for examination candidates, delay in the release of results, examination malpractices, cost implication of printing examination materials and human error. This brings about the need for automation of the examination system [1].
Over the years, there have been various automated examination systems that have been developed with one or more limitations. Some of these limitations include lack of
Flexible timing functionality to automatically log-off candidates upon expiration of allotted time as a challenge
Malpractice due to questions not randomly generated
Not well secured application domain in terms of data security and integrity.
An online assessment however, is expected to offer several advantages for the institution and the learner. These include
Time analysis of responses to the question level to better discriminate between candidates.
Including video in questions, particularly for scenarios in authentic assessment.
Question banks and randomization of questions and response orders to reduce cheating.
Automated analysis of results from entire candidate troops.
Immediate feedback can be given.
1.2 Background and Objective:
There have been a number of researches focusing on the development of automated examination systems and electronic learning information systems. Zhenming et al (2003) developed a novel online examination system based on a Browser/Server framework which carries out automatic grading for objective questions in computer related topics such as programming, Microsoft Windows operating systems and Microsoft Office applications. It was successfully applied to the distance evaluation of basic operating skills of students offering computer science in some Universities.
Lei (2006) presented a web-based educational assessment system by applying Bloom’s taxonomy to evaluate student learning outcomes and teacher instructional practices in real time. The system performance is rather encouraging with experimentation in science and mathematics courses of two local high schools. Emery & Abu (2006) developed an online website for tutoring and e-examination of economic courses.
This novel software tool was used for online examination and tutorial application of the syllabus of economic courses so as to ensure that students study all the concepts of economics. So, the proposed software is structured from two major modules, the first one was an online website to review and make self-test for all materials of economic course and the second part is an online examination using a large](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-8-2048.jpg)
![Internship Project Report
9
database bank of questions through it the level of students can be evaluated immediately and some statistical evaluations can be obtained. The developed software offers the following features:
Instructors could add any further questions to maximize the size of the bank of questions.
Different examinations for each student with randomly selected questions from the bank of questions can be done.
Different reports for the instructors, students, classes etc. can be obtained.
Several students can take their exams simultaneously without any problem inside and outside their campus. The proposed software has been designed to work based on the client server architecture.
1.3 Literature Survey: In its broadest sense, e-assessment is the use of information technology for any assessment- related activity. This definition embraces a wide range of student activity ranging from the use of a word processor to on-screen testing. Due to its obvious similarity to e-learning, the term e-assessment is becoming widely used as a generic term to describe the use of computers within the assessment process. Various terms are used to describe the use of a computer for assessment purposes [2]. These include:
Computer-Assisted Assessment or Computer-Aided Assessment (CAA) Computer-Mediated Assessment (CMA) Computer-Based Assessment (CBA) Online assessment.
1.3.1 Contextual Issue Related To CBT:
The implementation of CBT occurs within a context that both supports and limits its use. In this section, we briefly address several of the contextual factors that surround CBT including [3]:
a) The technological capacity of schools to support CBT
b) Universal design applied to CBT
c) Perceived advantages and disadvantages of CBT
a) Technological Capacity in Schools
Access to computers and Internet capabilities have for some time been a stumbling block for the push to widespread use of computer-based and online assessments. For example, Becker (2006) questioned ―digital equity‖ in computer access, computer use, and state-level technology policies. He used data from the National Assessment of Educational Progress to examine digital equity, and reported that ―students in rural schools or schools with high percentages of African American students were likely to have less access to computers‖ (p. 1). Becker did not examine whether having a disability had any impact on computer availability or use [4]
A nationally representative school-level survey on information technology conducted by the National Center for Education Statistics (Gray, Thomas, & Lewis, 2010) reported several findings about the availability and use of technology in schools in the fall of 2008. The results generally indicated that computers with Internet access were available for instruction, and that the ratio of instructional computers](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-9-2048.jpg)
![Internship Project Report
10
with Internet access was 3 to 1. The large majority of computers in public schools were used for instruction. Schools also reported using a district network or the Internet to provide assessment results for teachers to individualize instruction or to inform instructional planning; nearly three-fourths provided online student assessments. Full-time technology staff members were available in about one-third of low poverty schools and one-fourth of high poverty concentration schools. The survey did not ask about availability of computers to students with disabilities, or about the use of computers for statewide testing.
b) Universal Design Applied to CBT:
Universal design of assessment generally means an approach that involves developing assessments for the widest range of students from the beginning while maintaining the validity of results from the assessment. Universal design also sometimes refers to multiple means of representation, action/expression, and engagement [5].
More recently, attention has been paid to applying the principles of universal design in a technology-based environment. For example, Russell, Hoffman, and Higgins (2009a) demonstrated that the principles of universal design could be applied to computer-based test delivery. Technology also can be used to more seamlessly link instruction and assessment. For example, Salend (2009) specifically identified a variety of technology-based approaches that might be used for classroom assessments—for example, curriculum-based measurement (CBMs) assessment probes, digitalized observations and portfolios, and self-monitoring tools [6].
Dolan et al. (2009) prepared a set of guidelines specifically for computer-based assessments. The principles address test delivery considerations, item content and delivery considerations, and component content and delivery considerations. A variety of topics relevant to computer-based testing and universal design is addressed in the component content and delivery considerations section of the guidelines (e.g., text, images, audio, video), with each organized according to categories of processing that students apply during testing [7].
c) Perceived Advantages and Challenges of CBT:
Many of the perceived advantages and challenges of CBT have been addressed in the literature [8]. Yet, most are not focused on students with disabilities. In examining perceptions and research on CBT, we identified several categories or ―themes‖ that can be used to organize the advantages and challenges of CBT:
Economic: Factors that have cost implications.
Systems implementation: Logistical, test security, and other factors that affect the capacity of local education agencies and state education agencies to implement CBT.
Test administration/design: Factors that affect how students (and sometimes teachers) perceive and interact with the test.
Accessibility: Factors that affect how accessible a test is to a wide range of students.](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-10-2048.jpg)

![Internship Project Report
12
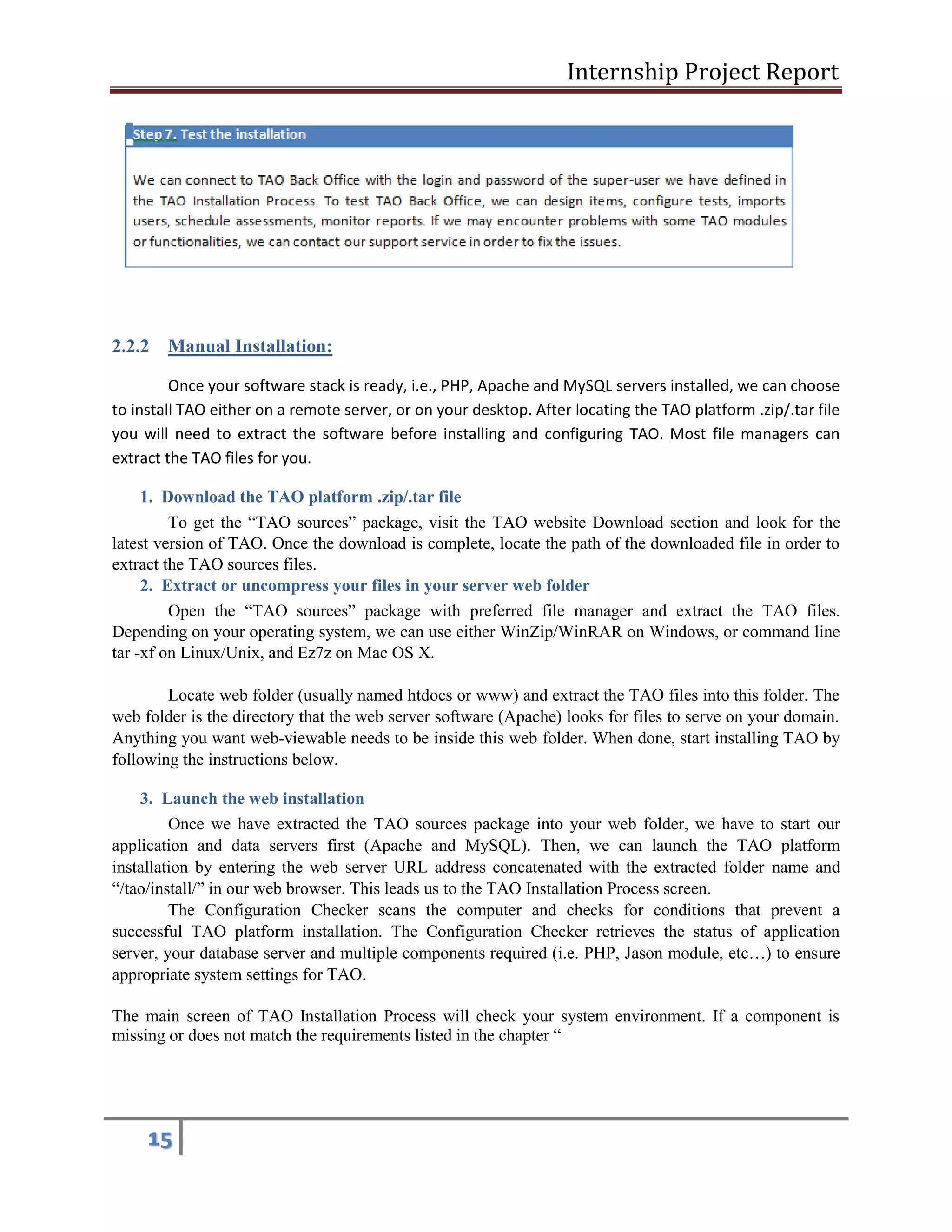
2.1 Things to know before installing TAO:
TAO is an open source e-Testing platform for building, delivering, and sharing innovative and engaging assessments online. The minimum system requirements for installing TAO are PHP 5.3 or higher, MySQL 5.0 or higher and an Apache server (recommended version: 2.2.9, other version should work).
2.2 Installation Modes:
Under all Windows operating systems, you will have the ability to install the TAO platform using the Automated Installation mode. This mode is recommended when installing TAO with just basic technical information [9].
Alternatively, you can perform a manual installation on your server or desktop. To do so, you need to download the ―TAO sources‖ package from the TAO website. The ―TAO sources‖ package contains the source codes and files of the TAO application. These source files need to be uploaded into the appropriate Apache server folder and set into MySQL workbench in order to run TAO.
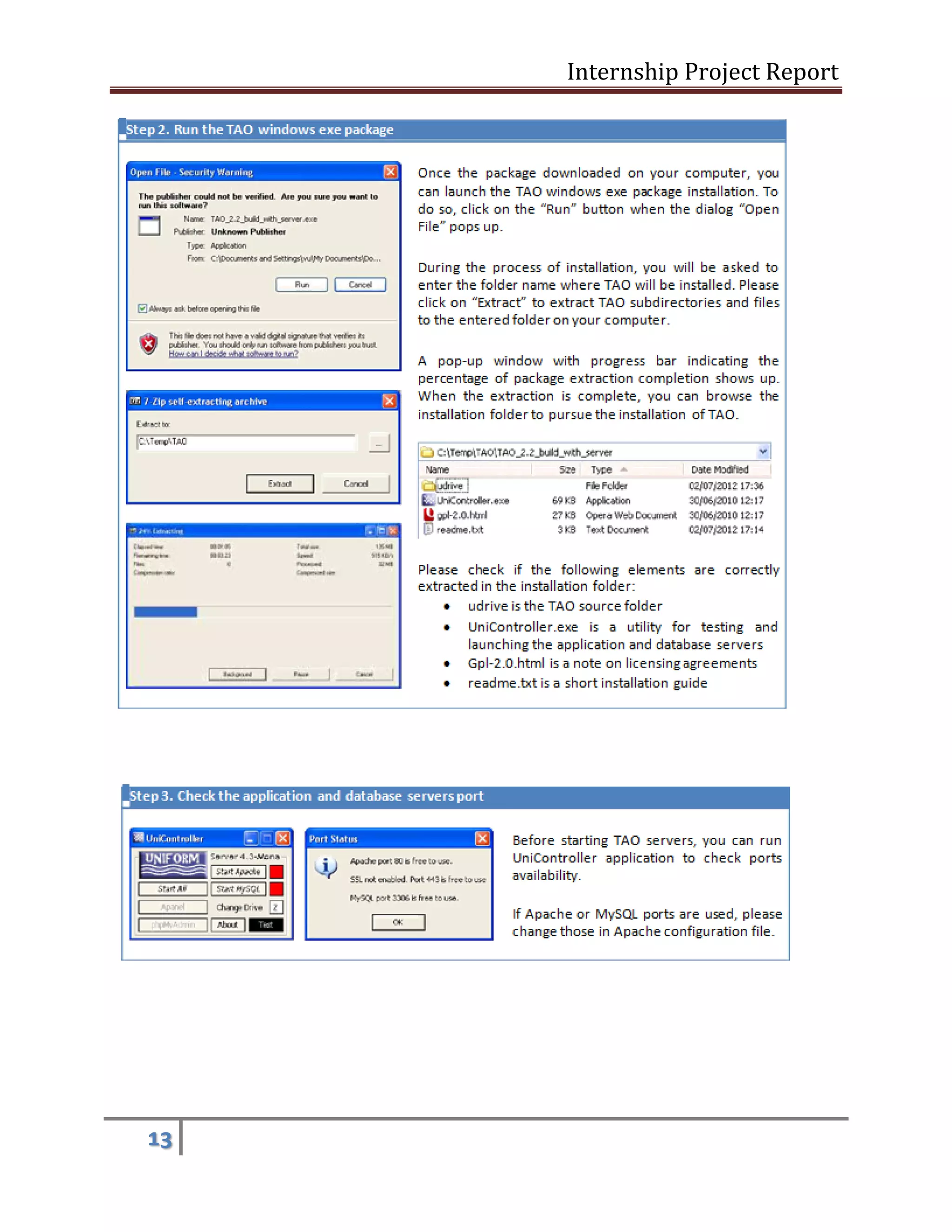
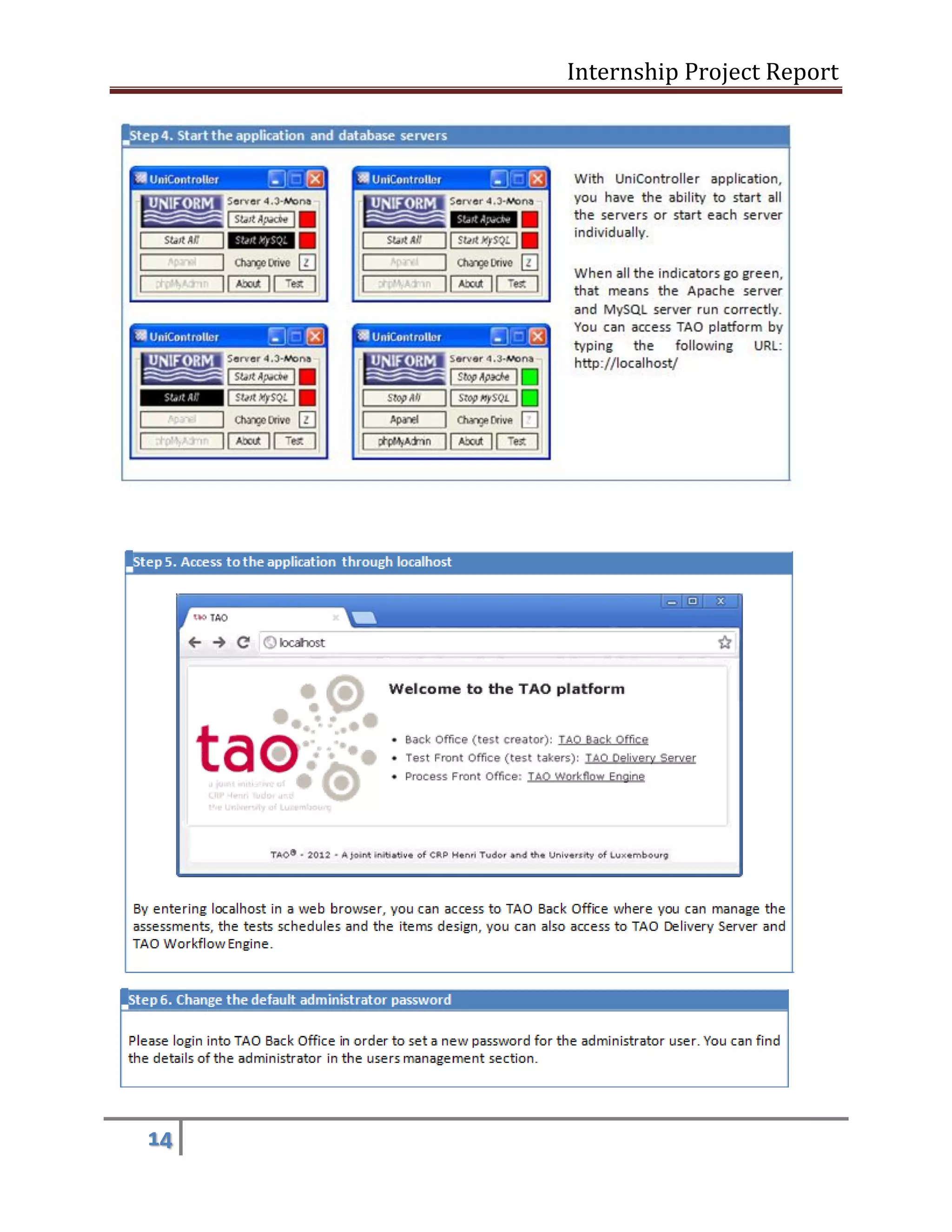
2.2.1 Automated Installation:
If your IT environment meets TAO’s system requirements, follow the instructions below. Please note that the TAO Automated Installation is only available for Microsoft Windows operating systems.
The Automated Installation consists of the following steps:
Step 1: Download the TAO windows exe package on tao.lu
Step 2: Run the TAO window exe package
Step 3: Check the application and database servers’ port
Step 4: Start the application and database servers
Step 5: Access to the application through local host
Step 6: Change the default administrator password
Step 7: Test the Installation
Download the TAO windows exe package on tao.lu](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-12-2048.jpg)
![Internship Project Report
20
2.3 How to use TAO:
Generally six portions or tabs are there to use this software [10].
Items
Tests
Test-takers
Groups
Deliveries
Results
2.3.1 Items: Create, preview and organize individual items before including them in your tests. Choose from 17 different interaction types, including: Single choice Multiple choice Text entry Slider Hotspot Import & Export Items: Import any items that are compliant with the QTI (Question and Test Interoperability). Conversely, you can also export items from TAO and re-use them in other QTI-compliant tools. If your needs go beyond what the QTI standard allows, you can develop powerful and sophisticated item types using the TAO Open Web Item format. 2.3.2 Tests: In this section we Build and manage tests using items that you have previously created or imported. 2.3.3 Test-takers: In this section we Register our test-takers, manage their personal data, and assign them to groups. Default properties of the test-takers are their name and the language of the test interface. You can customize these records by adding any data you need, such as date of birth, gender, etc. In addition to](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-20-2048.jpg)
![Internship Project Report
22
References [1] https://www.google.com.pk/url?sa=t&rct=j&q=&esrc=s&source=web&cd=7&cad=rja&uact=8& sqi=2&ved=0CE4QFjAG&url=http%3A%2F%2Fwww.ijstr.org%2Ffinal- print%2Faug2013%2FComputer-based-Test-Cbt-System-For-University-Academic-Enterprise- Examination.pdf&ei=- d7RU4f1BoTC7AbqlIEw&usg=AFQjCNF9YOWtPIH03QP4IZTBvjFEjrNLhw&sig2=CT5lJAx
vzkytkXCxnSuHHg&bvm=bv.71667212,d.bGE[2] h ttp://en.wikipedia.org/wiki/E-assessment
[3] https://www.google.com.pk/url?sa=t&rct=j&q=&esrc=s&source=web&cd=2&cad=rja&uact=8& sqi=2&ved=0CCIQFjAB&url=http%3A%2F%2Fwww.cehd.umn.edu%2Fnceo%2Fonlinepubs% 2Fsynthesis78%2Fsynthesis78.pdf&ei=-d7RU4f1BoTC7AbqlIEw&usg=AFQjCNG- gCrLgnoVTuGuPItHNlMmwMnaRA&sig2=WyCw06_UrhshrTR0jfv08Q&bvm=bv.71667212,
d.bGE
[4] ww w.eed.state.ak.us/nclb/pdf/Statewide_System_of_Support.pdf - 2009-03-26
[5] h ttp://www.eed.state.ak.us/tls/assessment/FormativeAssessmentResources.htm
[6] h ttp://www.doe.k12.ga.us/ci_testing.aspx?PageReq=CI_TESTING_EOCT
[7] h ttp://www.doe.in.gov/eca/pdf/2009-10_ECA%20_Kick-off_Memo.pdf
[8] h ttp://en.wikipedia.org/wiki/E-assessment
[9] https://www.google.com.pk/webhp?tab=ww&ei=G768U_iXKdLT4QTau4HoAg&ved=0CBAQ1
S 4#q=tao+testing+manual&safe=active
[10] h ttp://127.0.0.1/TAO/tao/Main/index?structure=tests&ext=taoTests#](https://image.slidesharecdn.com/computerbasedonlinewrittentestsystem-141207092104-conversion-gate02/75/Computer-based-online-written-test-system-Tao-Software-22-2048.jpg)