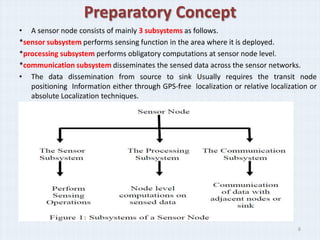
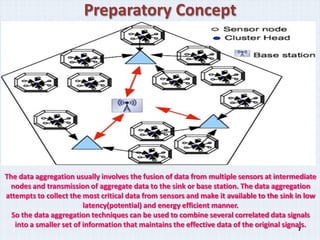
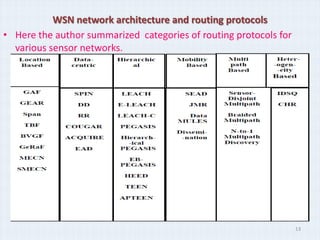
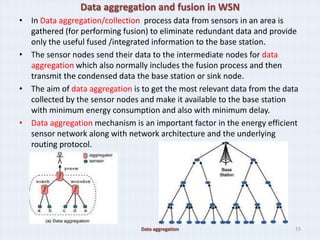
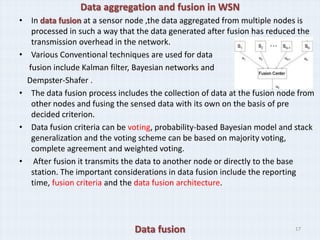
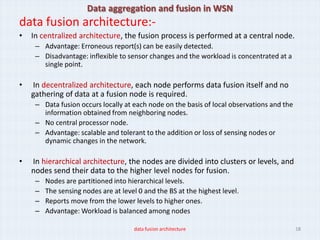
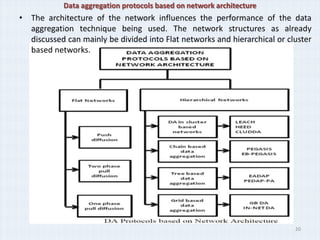
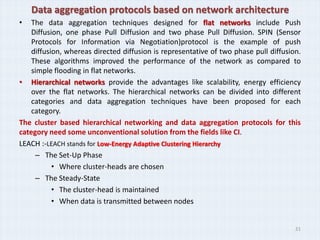
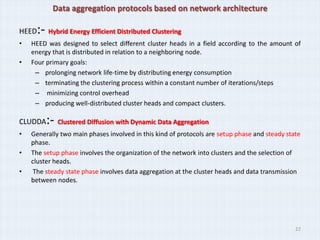
The document discusses computational intelligence based data aggregation techniques in wireless sensor networks. It begins by introducing the research intentions of integrating computational intelligence techniques with conventional data aggregation to improve efficiency. It then provides background on wireless sensor network architectures, routing protocols, and challenges with data aggregation. Finally, it proposes using techniques like neural networks, genetic algorithms, fuzzy logic, and particle swarm optimization to enable adaptive and distributed data aggregation and fusion in sensor networks.