The document summarizes research on geographic routing and relay selection in wireless sensor networks. It discusses how geographic routing uses location information to route packets towards a destination but faces challenges around connectivity holes and optimal relay selection. The document reviews several existing approaches and their limitations. It then describes an alternative method called ALBA-R that was proposed to more efficiently route around holes while enhancing relay selection to maximize node lifetime. Simulation results showed ALBA-R outperformed other methods with respect to metrics like overhead and end-to-end delay.
![A major evolution in communication
technology has been the introduction of the
Global Positioning System (GPS) which
provides the location information and universal
timing of a node. The recent development of a
wireless sensor network has led to an innovative
use of small sensory nodes which operate with a
very low power in extreme environmental
conditions. A group of small sensory nodes are
randomly deployed in a sensor field. These
nodes have the ability to organize themselves
automatically and to detect the data content
accurately.
II. LITERATURE REVIEW
A New Contention-Based MAC Protocol for
Geographic Forwarding in Ad Hoc and
Sensor Networks [1]:
Michele Zorzi referred that Geographic
Random Forwarding (GeRaF) is based on the
assumption that sensor nodes have a means to
determine their location information, and that
the positions of the final destination and of the
transmitting node are explicitly included in each
message. GeRaF is designed to integrate MAC
message exchanges and the designation of the
most convenient relay (from a geographic point
of view). Thanks to awake/sleep cycles and to
this cross–layer design, it is very energy–
efficient. Moreover, it is simple and easy to
implement on real nodes. However, it has some
drawbacks, e.g., it cannot route around
connectivity holes, and thus may not be able to
deliver all messages in sparse networks
(because of the physical absence of nodes).
Also, it is not able to operate in dense traffic
scenario (when congestion builds up).
On the Effect of Localization Errors on
Geographic Face Routing in Sensor
Networks [2]:
The reason for geographic routing protocols
does not need to maintain per destination
information and only neighbor location
information is needed to route packets.
Geographic routing protocols are very attractive
choices for routing in sensor networks. Most
geographic routing protocols use greedy
forwarding for basic operations. Greedy
forwarding is based on next forwarding hop is
chosen to minimize the distance of the
destination. It fails in dead-ends. Most
geographic routing protocols use greedy
forwarding for basic operations. In order to
provide correct routing in the presence of dead
ends, face routing has been introduced. GPSR is
a geographic routing protocol for wireless
networks that combines greedy forwarding and
face routing. GPSR uses geographic hash table
(GHT) system that hashes keys into geographic
location and stores the key-value pair at the
sensor node closest to the hash of its key.GHT
uses mainly for geographic routing to the hash
location. The applications are data centric
storage and distributed indexing.
Locating and Bypassing Holes in Sensor
Networks [3]:
In routing, connectivity holes cause difficulties
in organizing the networks. Holes define the
“hot spots” regions created by traffic congestion
and sensor power shortage. A commonly used
assumption in studying sensor networks is that
sensors are uniformly densely distributed in the
plane. However in system deployment, this
assumption does not hold in general. Even if
sensors nodes are distributed randomly, there
are still regions with sensor density much lower
than others. In practice, sensor networks usually
have holes, i.e. regions without enough working
sensors. An example of a large number of dead
sensor nodes it creates a big hole in the
network. A packet is forwarded to a 1-hop
neighbor who is closer to the destination than
the current sensor node. This process is repeated
until the packet data reaches the destination, or
the packet is stuck at a node when there is no
neighbor to reach the destination. Here, holes
define to be simple regions enclosed by a
polygon cycle which contains all the nodes
where local minima can appear. The
information storage and Memory requirement
are based on boundary node. The applications
are avoiding network hot spots, supporting path
migration. The applications are avoiding
network hot spots, supporting path migration,
information storage mechanisms. It can able to
handle node failures, information storage and
memory requirement. It uses TENT rule and
BOUNDHOLE techniques to identify and build
around holes. TENT rule requires each node to
know its 1-hop neighbors locations. To help
packets get out of stuck nodes, BOUNDHOLE
to find the boundary of the hole.
Proceedings International Conference On Advances In Engineering And Technology
ISBN NO: 978 - 1503304048
www.iaetsd.in
International Association of Engineering & Technology for Skill Development
12](https://image.slidesharecdn.com/iaetsd-asurveyongeographicroutingrelayselectionin-150407215054-conversion-gate01/75/Iaetsd-a-survey-on-geographic-routing-relay-selection-in-2-2048.jpg)
![Efficient Non-Planar Routing around Dead
Ends in Sparse Topologies Using Random
Forwarding [4]:
Geographic forwarding in wireless sensor
networks (WSN) has long suffered from the
problem of bypassing "dead ends," i.e., those
areas in the network where no node can be
found in the direction of the data collection
point (the sink). However previous scheme
resolve these problems that rely on geometric
techniques leading to the planarization of the
network topology graph. In this paper, a
alternative method to planarization is proposed,
termed ALBA-R, which successfully routes
packets to the sink transparently to dead ends.
ALBA-R combines scheduling of awake or
asleep nodes, channel access and geographic.
By enhancing geographic routing along dead-
ends with a mechanism that is capable of
routing packets around connectivity holes.
Through simulations results, it demonstrates
that ALBA-R can provide insignificant
overhead, and outperforms similar solutions
with respect to all the metrics of interest
investigated, especially specifying the
benchmark for geographic routing protocols..
Localization Error-Resilient Geographic
Routing for Wireless Sensor Networks [5]:
This paper concerns the demonstration of the
resilience to localization errors of ALBA-R, a
protocol for geographic routing in wireless
sensor networks (WSNs). In particular, it shows
that a simple effective nodal coloring
mechanism for handling nodal connectivity
holes, ALBA-R achieves the further desirable
benefit of being totally resilient to localization
errors, which are unavoidable in WSNs.
Through ns2-based simulations it explains that
fundamental network parameters such as
network density, and also independently of
errors in nodal coordinate estimations as high as
the node transmission radius, ALBA-R is
successful in delivering all generated packets
while incurring reasonable degradation for
metrics such as route-length and end-to-end
latency and still remaining and energy efficient
protocol.
ALBA-R: Load-Balancing Geographic
Routing Around Connectivity Holes in
Wireless Sensor Networks [7]:
ALBA-R features the cross-layer integration of
geographic routing with contention-based MAC
for relay selection and load balancing (ALBA),
as well as a mechanism to detect and route
around connectivity holes (Rainbow). ALBA
and Rainbow (ALBA-R) together solve the
problem of routing around a dead end without
overhead-intensive techniques such as graph
planarization and face routing. The Rainbow
mechanism allows ALBA-R to efficiently route
packets out of and around dead ends. Rainbow
is resilient to localization errors and to channel
propagation impairments. It does not need the
network topology to be planar, unlike previous
routing protocols. It is, therefore, more general
than face routing-based solutions and is able to
guarantee packet delivery in realistic
deployments.
III. PRELIMINARY
A. Routing in WSN
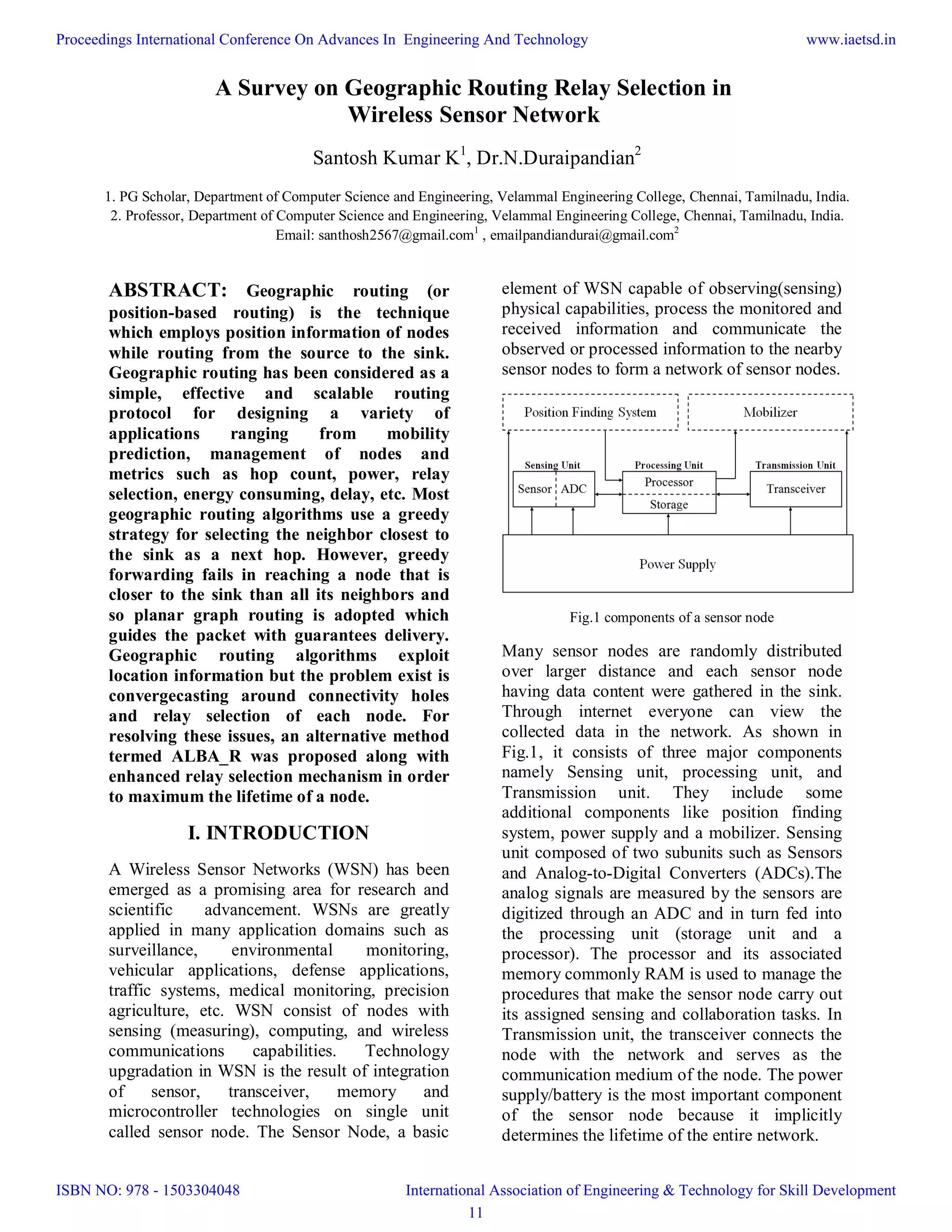
Routing is a process of determining a path
between source and destination regarding the
transmission of packet messages. When the
sink is far away from the source or not in the
range of source node, multi-hop technique is
followed. In order to moving a packet of data
from source to destination, intermediate sensor
nodes have to relay their packets efficiently. As
shown in Fig.2 depend on network structure,
routing protocol that perform an end-to-end
message delivery can be classified as flat-based
routing, hierarchical-based routing, and
geographic routing (location-based routing). In
flat-based routing, all the nodes are treated as
equal and ensure same roles or functionality. In
hierarchical-based routing, all the nodes are
assigned with differed roles and provide higher
energy nodes for transmission as well as lower
energy nodes for sensing. In location-based
routing, node’s positions are extracted to route
packet data i.e. Sensor nodes are addressed by
means of their locations and their location were
obtained by distance estimation, neighbor
discovery, GPS etc.
Proceedings International Conference On Advances In Engineering And Technology
ISBN NO: 978 - 1503304048
www.iaetsd.in
International Association of Engineering & Technology for Skill Development
13](https://image.slidesharecdn.com/iaetsd-asurveyongeographicroutingrelayselectionin-150407215054-conversion-gate01/75/Iaetsd-a-survey-on-geographic-routing-relay-selection-in-3-2048.jpg)
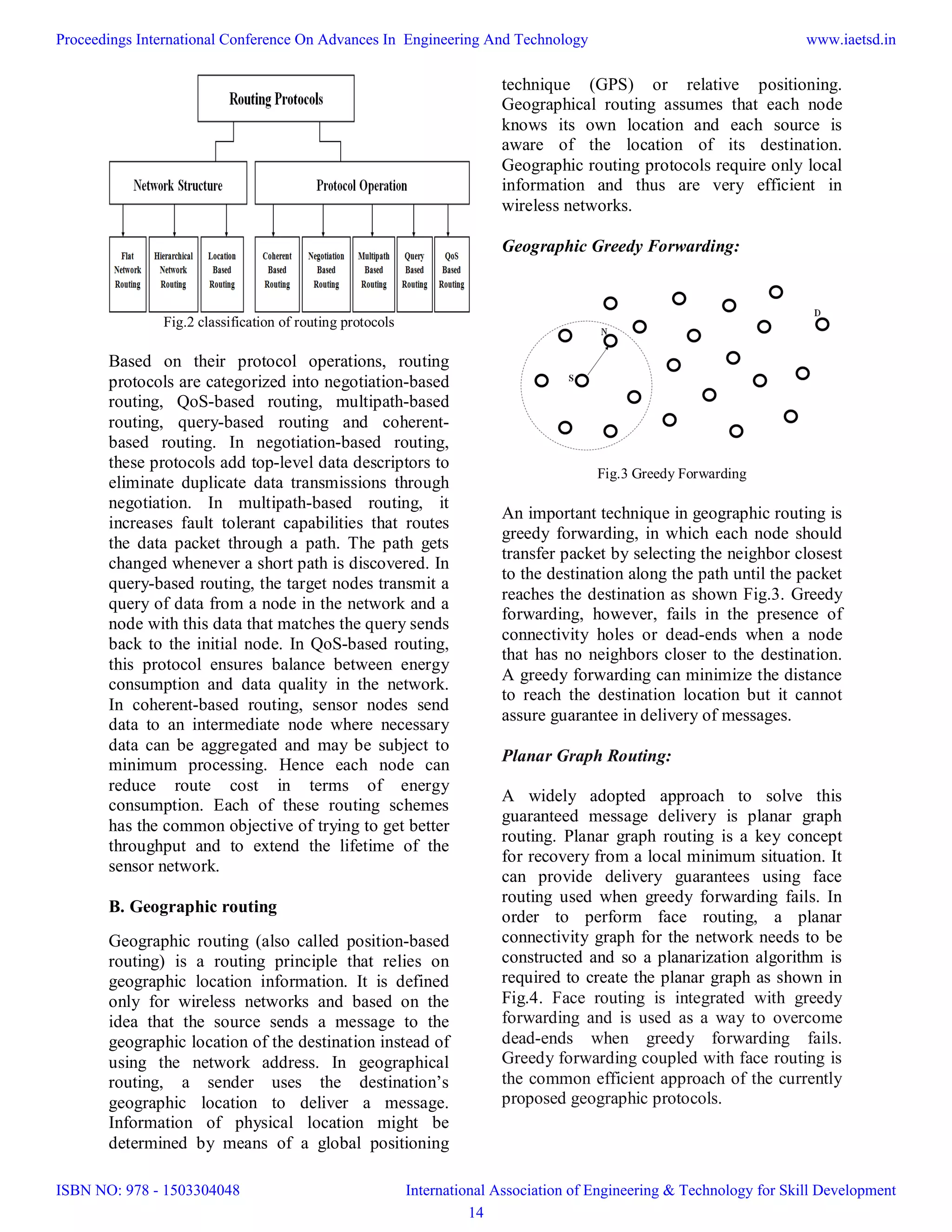
![Fig.4 Planar graph routing
C. Issues in geographic routing
Some of the following issues while designing
geographic routing schemes are
(a)Routing around dead ends,
(b) Flexibility to localization errors,
(c)Relay selection process.
IV. OVERVIEW
D. Relay Selection in Geographic routing
Adaptive load balancing algorithm improves a
convergecasting in WSNs that integrates
awake/asleep schedules, Medium access control
(MAC), load balancing, and back-to-back data
transmissions. While transmission, it is
necessary to ensure that a node which is awake
or asleep or else usage of energy can get
increases. A sensor node can forward packet
from source to destination by sending RTS
(Request-to-send) packet to all the neighbor
nodes in order to ensure their availability of
awake nodes. The sensor nodes which are
available will report with clear-to-send (CTS)
packet carrying information through which the
sender can choose the best relay. A ‘best
throughput’ can get performed through effective
relay selection. Every upcoming relay is
characterized by two parameters: the queue
priority index (QPI), and the geographic priority
index (GPI). The QPI is measured as, the
requested number of packets to be transmitted
in a burst is Nb, and the number of packets in
the queue of an eligible relay is Q. The potential
relay keeps a moving average M of the number
of packets it was able to transmit back-to-back,
without errors, in the last forwarding attempts.
The QPI is then defined as min (Q+Nb)/M,
Nq, where Nq is the maximum allowed QPI.
Rainbow is the mechanism used by ALBA_R to
deal with dead ends. An important feature for
avoiding dead ends is that of allowing the nodes
to forward packets away from the sink when a
relay selection toward the sink cannot be
found. To remember whether to search for
relays in the direction of the sink, each node is
labeled with different colors. Rainbow
mechanism discovers a specific color of each
node so that a possible route to the sink is
determined.
E. Enhanced Relay Selection Scheme
The relay selection scheme of ALBA_R [7] can
fail in two cases:
1. If no node with any QPI is found
2. If the contention among nodes with the
same QPI and GPI is not resolved within
a maximum number of attempts.
Both situations cause the sender to back off. It
will lead to end to end delay also.
To overcome that, we can send the RTS packets
to all the one hop neighbor nodes to collect the
QPI value as the reply instead of sending RTS
with particular QPI value. After receiving QPI
value, we can select the relay node based on the
QPI value in the increasing order. If there is a
tie, we can choose the relay node which is
having lowest GPI value as shown in Fig.5.
Thus the delay will be reduced by transmitting
the RTS packets again and again until find out
the node with particular QPI value.
Fig.5 System architecture
Proceedings International Conference On Advances In Engineering And Technology
ISBN NO: 978 - 1503304048
www.iaetsd.in
International Association of Engineering & Technology for Skill Development
15](https://image.slidesharecdn.com/iaetsd-asurveyongeographicroutingrelayselectionin-150407215054-conversion-gate01/75/Iaetsd-a-survey-on-geographic-routing-relay-selection-in-5-2048.jpg)
![V. CONCLUSION
WSNs have seen tremendous developments in
design and applications over the recent years.
This speedy progress has resulted in the stress
towards solving the hurdles that this area has to
face. The area of WSN is thriving and every day
new ideas are emerging. The positive benefits
of this are quite obvious; such a technology will
achieve fine granularity tracking of what is
going on at far away and generally in
inaccessible locations. A wireless senor network
is the latest and fastest growing technology and
is expected to revolutionize a wide range of
applications in terms of its quality and
availability in the near future.
REFERENCES
[1]M. Zorzi, “A New Contention-Based MAC
Protocol for Geographic Forwarding in Ad Hoc
and Sensor Networks,” Proc. IEEE Int’l Conf.
Comm. (ICC ’04), vol. 6, pp. 3481-3485, June
2004.
[2]K. Seada, A. Helmy, and R. Govindan, “On
the Effect of Localization Errors on Geographic
Face Routing in Sensor Networks,” Proc.
IEEE/ACM Third Int’l Symp. Information
Processing in Sensor Networks (IPSN ’04), pp.
71-80, Apr. 2004.
[3]Q. Fang, J. Gao, and L.J. Guibas, “Locating
and Bypassing Holes in Sensor Networks,”
ACM Mobile Networks and Applications, vol.
11, no. 2, pp. 187-200, Apr. 2006.
[4]P. Casari, M. Nati, C. Petrioli, and M. Zorzi,
“Efficient Non-Planar Routing around Dead
Ends in Sparse Topologies Using Random
Forwarding,” Proc. IEEE Int’l Conf. Comm.
(ICC ’07), pp. 3122-3129, June 2007.
[5]S. Basagni, M. Nati, and C. Petrioli,
“Localization Error-Resilient Geographic
Routing for Wireless Sensor Networks,” Proc.
IEEE GLOBECOM, pp. 1-6, Nov./Dec. 2008.
[6]A. Camillo, M. Nati, C. Petrioli, M. Rossi,
and M. Zorzi, “IRIS: Integrated Data Gathering
and Interest Dissemination System for Wireless
Sensor Networks,” Ad Hoc Networks, Special
Issue on Cross-Layer Design in Ad Hoc and
Sensor Networks, vol. 11, no. 2, pp. 654-671,
Mar. 2013.
[7]C.Petrioli, P.Casari, M.Zorzi, M.Nati, and
S.Basagni, “ALBA-R: Load-Balancing
Geographic Routing Around Connectivity
Holes in Wireless Sensor Networks” IEEE
Transactions on parallel and distributed
systems, vol.25, no.3, March 2014.
[8]S. Ru¨ hrup and I. Stojmenovic, “Optimizing
Communication Overhead while Reducing Path
Length in Beaconless Georouting with
Guaranteed Delivery for Wireless Sensor
Networks,” IEEE Trans. Computers, vol. 62,
no. 12, pp. 2240-2253, Dec. 2013.
[9] H. Frey, S. Ru¨ hrup, and I. Stojmenovic,
“Routing in Wireless Sensor Networks,” Guide
to Wireless Sensor Networks, S. Misra, I.
Woungang, and S. C. Misra, eds., ch. 4, pp. 81-
112, Springer-Verlag, May 2009.
[10] Fraser Cadger, Member, Kevin Curran,
IEEE, Jose Santos and Sandra Moffett “A
Survey of Geographical Routing in Wireless
Ad- Hoc Networks “, IEEE Communications
Surveys and Tutorials, Vol. PP, No. 99, pp: 1-
33, 2012.
[11] Rama Sundari Battula, O. S. Khanna
“Geographic Routing Protocols for Wireless
Sensor Networks: A Review”, International
Journal of Engineering and Innovative
Technology (IJEIT) Volume 2, Issue 12, June
2013
Proceedings International Conference On Advances In Engineering And Technology
ISBN NO: 978 - 1503304048
www.iaetsd.in
International Association of Engineering & Technology for Skill Development
16](https://image.slidesharecdn.com/iaetsd-asurveyongeographicroutingrelayselectionin-150407215054-conversion-gate01/75/Iaetsd-a-survey-on-geographic-routing-relay-selection-in-6-2048.jpg)