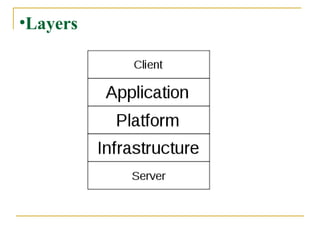
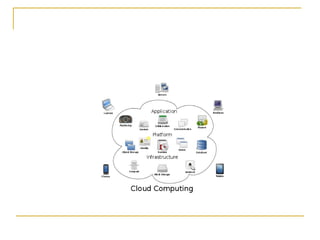
Cloud computing allows for location-independent computing resources that can be accessed on demand. It has evolved from earlier technologies like utility computing and now commonly uses a client-server model. The key features of cloud computing include agility, cost savings, scalability, and reliability, though privacy and security concerns still need to be addressed.