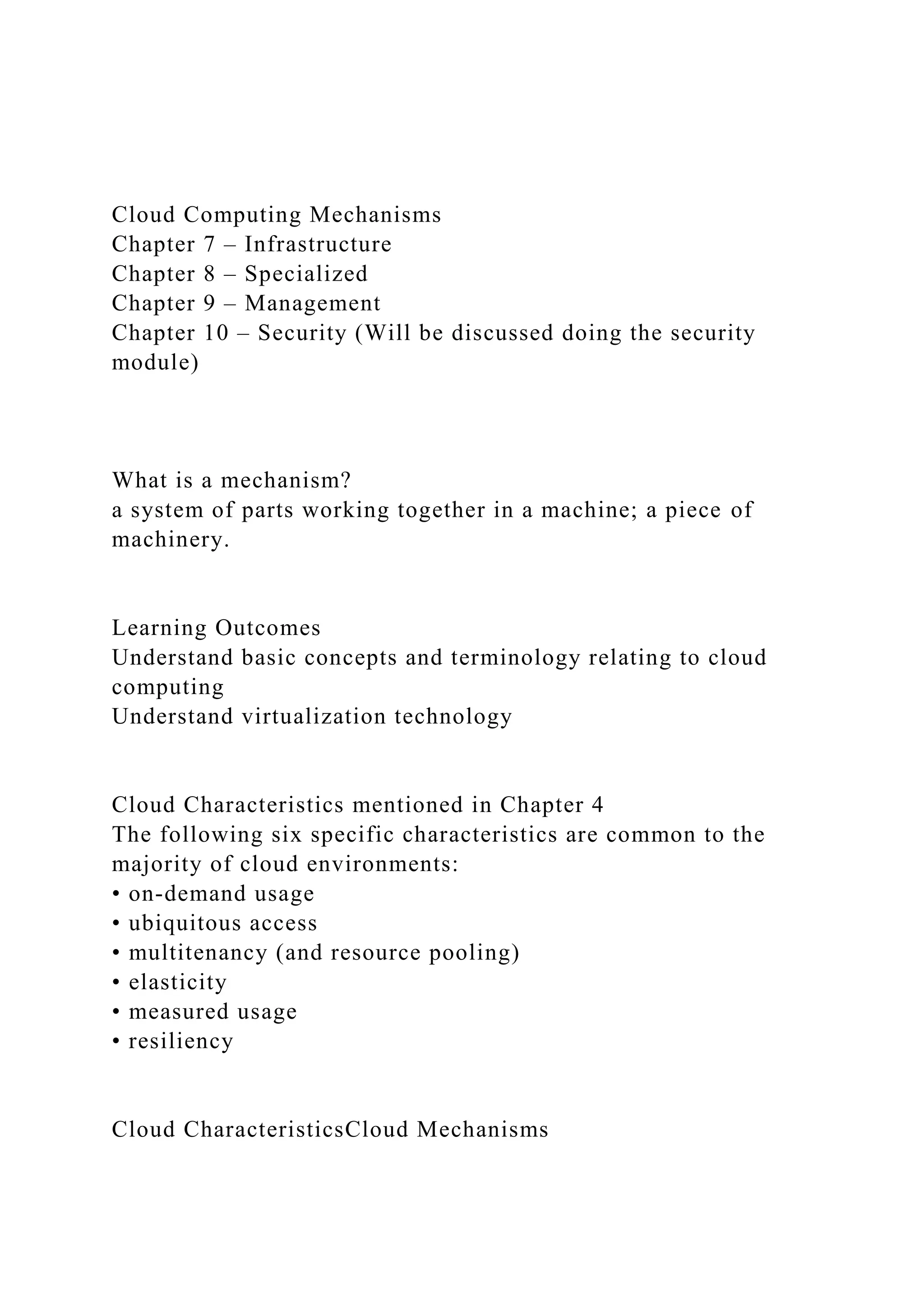
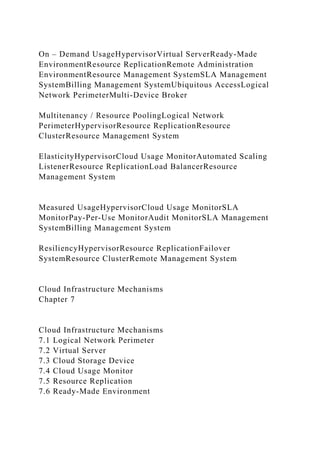
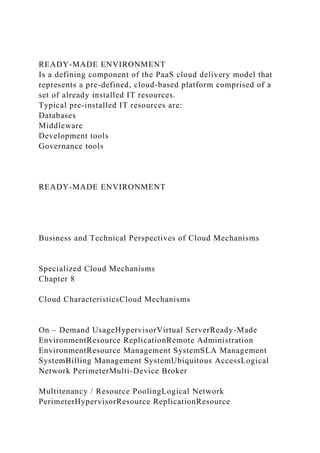
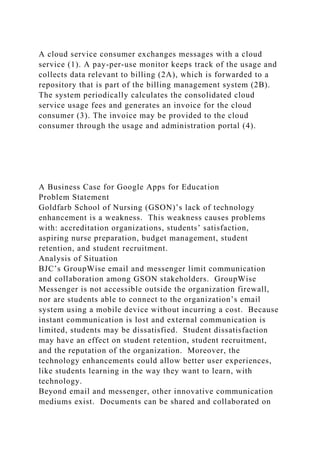
The document outlines the various mechanisms, characteristics, and management systems related to cloud computing, detailing infrastructure mechanisms such as virtual servers and resource replication. It highlights the importance of specialized cloud mechanisms for automated scaling, load balancing, and service level agreement (SLA) monitoring, along with the roles of remote administration and billing management systems. Additionally, it presents a business case for adopting Google Apps for Education to enhance operational efficiency and communication within a nursing school facing technological limitations.