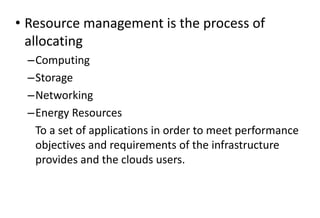
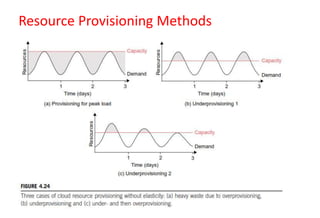
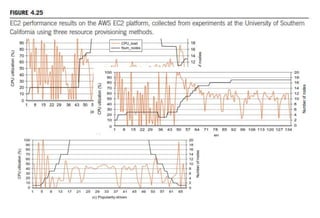
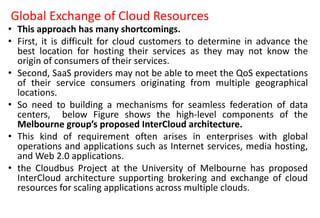
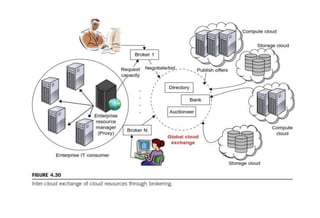
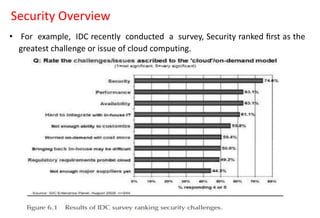
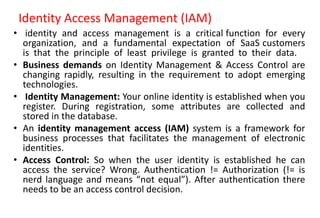
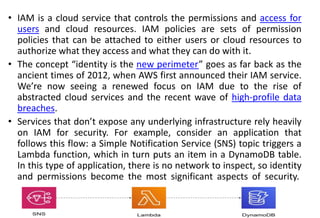
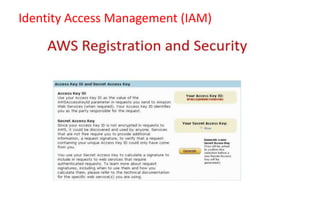
This document discusses resource management and security in cloud computing. It covers topics such as inter-cloud resource management, resource provisioning methods, global exchange of cloud resources, and security challenges in cloud computing. Specifically, it discusses demand-driven, event-driven and popularity-driven methods for resource provisioning in clouds. It also summarizes proposed architectures for global exchange of cloud resources across geographic locations. Finally, it outlines some key security concerns for cloud computing like data breaches and the shared responsibility model between cloud providers and customers for security.