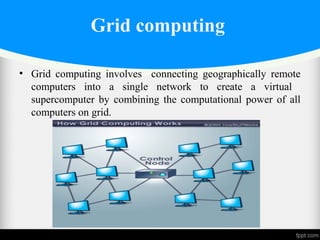
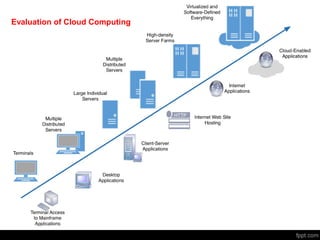
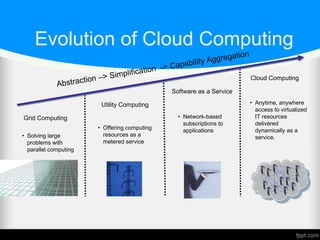
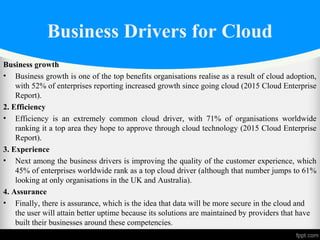
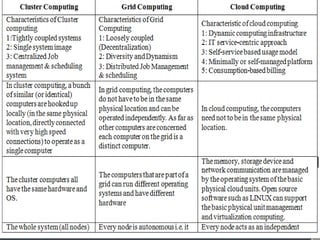
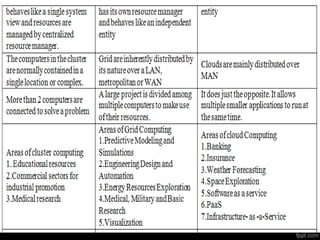
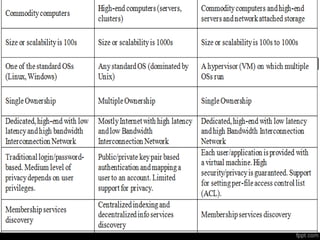
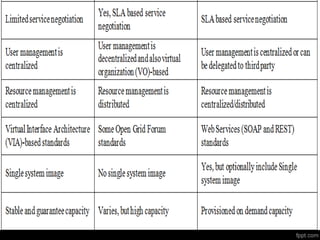
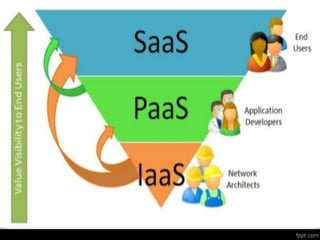
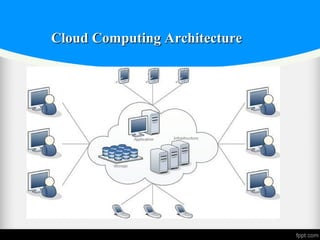
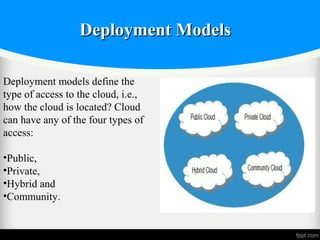
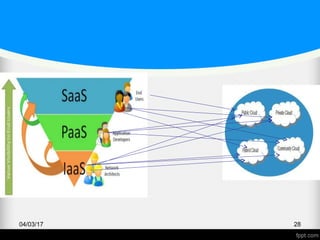
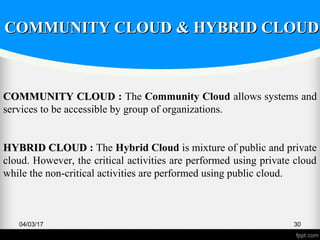
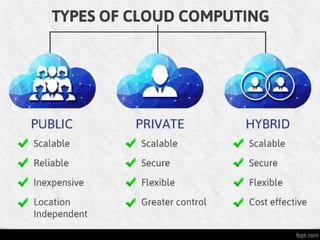
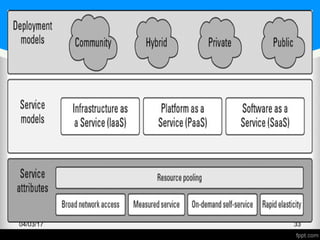
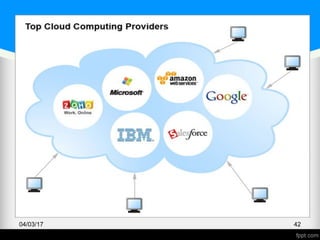
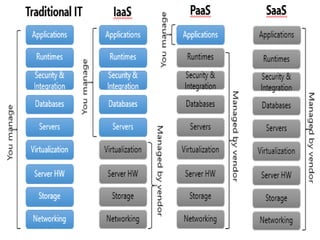
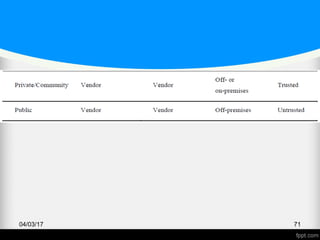
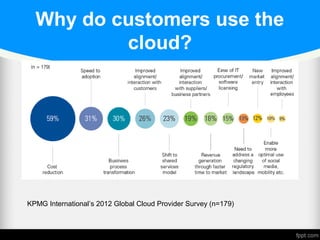
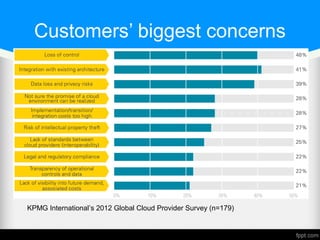
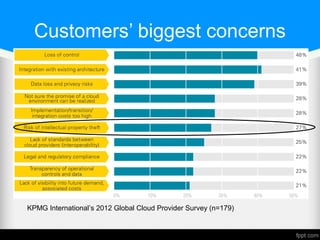
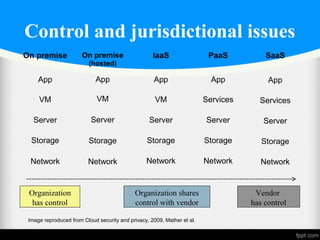
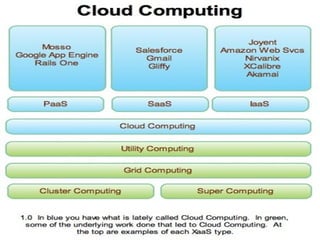
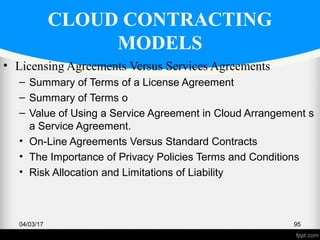
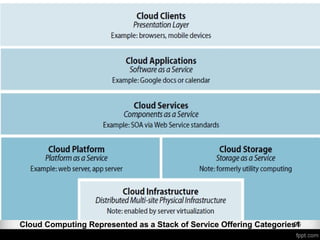
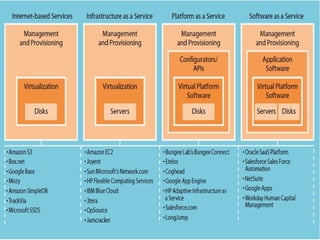
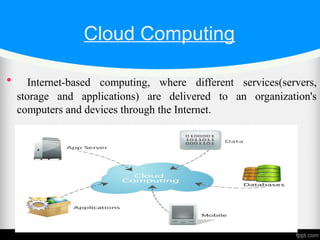
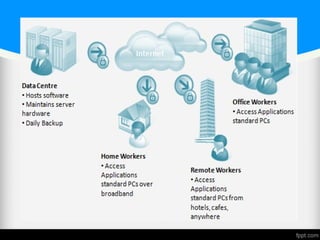
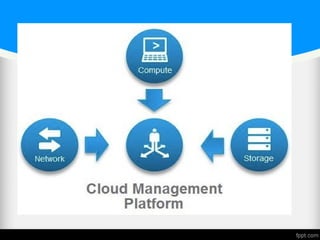
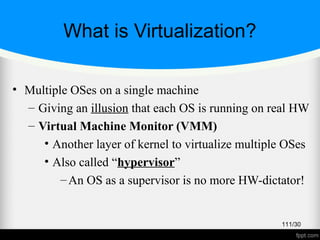
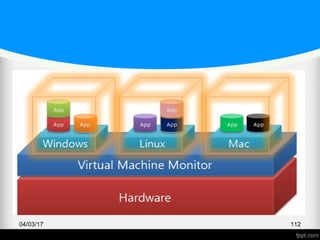
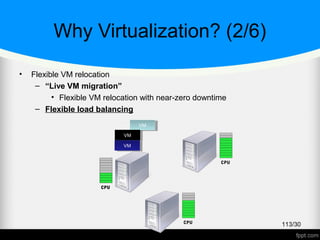
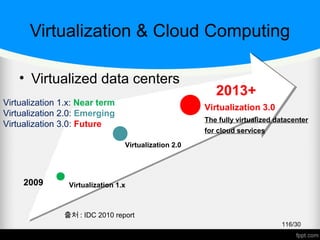
The document provides an overview of cloud computing, including its key concepts and components. It discusses the different deployment models (public, private, hybrid, community clouds), service models (IaaS, PaaS, SaaS), characteristics, benefits, history and evolution. Communication protocols used in cloud computing like HTTP, HTTPS and various RPC implementations are also mentioned. The role of open standards in cloud architecture including virtualization, SOA, open-source software and web services is assessed.